SAP Message Server Vulnerability: Full System Takeover #shorts
Show transcript [en]
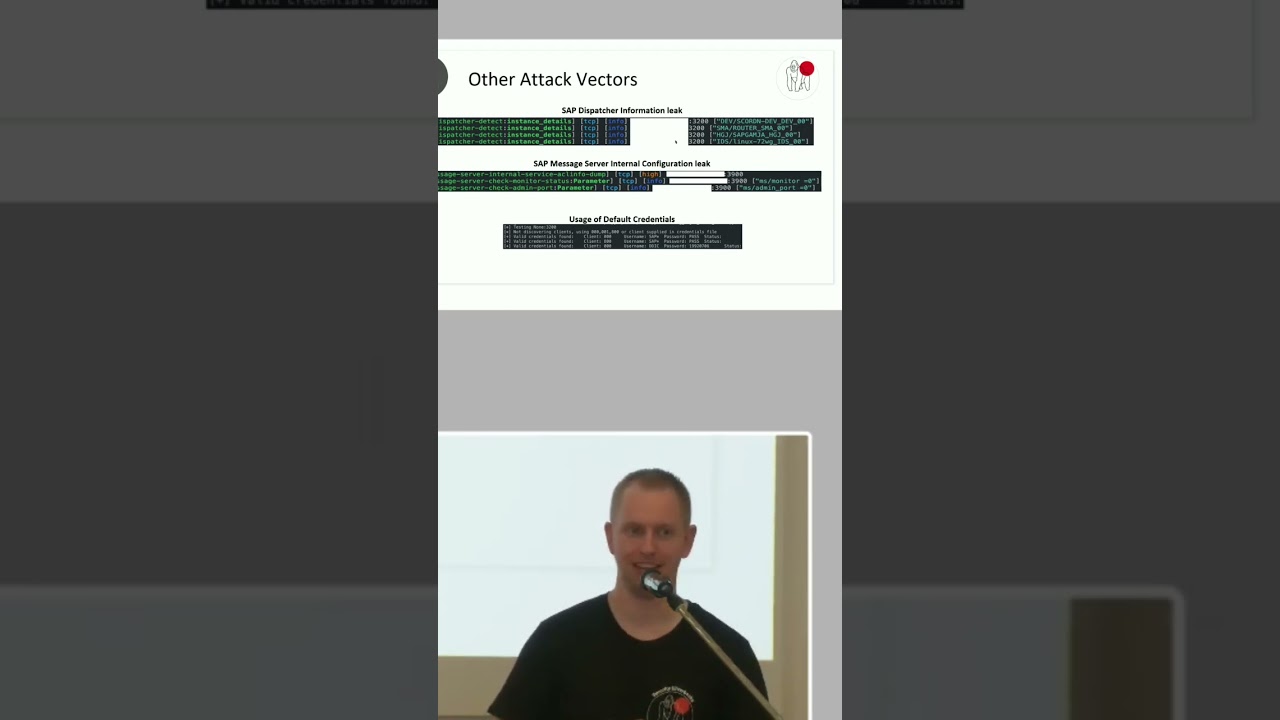
Another one is, well, one of my favorites, so SAP, it's big, thousands of users running against it, so you need load balancing. SAP has a message server. Let me introduce you to that servers. And the message server has the cool feature to you connect to it and it will say go to server X, you get redirected basically and then can log into that machine. It has two ports. Well, yeah, it has two ports dynamic generate an internal and an external. With that gateway to heaven, we also spoke about that internal port. Again, lack of authentic authentication and that internal allows you to change parameters. And also dump parameters. And what you see here for example that MS monitor,
that's basically you can enable that. It's a monitoring service. So, zero means only the instance self can see each other and see which services are there and how the load is. It's to one, external can connect from wherever and change stuff. And if you then see like that MS admin port, that's why I included that. Connect to that port. Congratulations, you now can change whatever configuration parameter an SAP system has, you can change it and switch it. When it is dynamically, that means for example enable hardcoded user passwords and credentials. So, you basically have taken over that system.





