Getting On The Same Level: What I Learned Building A Security Table Top Exercise
Show transcript [en]
Um uh after the last speech, do not go home and go straight to your cars. Instead, go to the UC center to do the last ceremony. And they have a couple as well. That's around um 4:45, I mean 4:55. And then um quick introduction that we're going to do here. Again, we've been here all day. So, of course, welcome to Bside San Antonio. Before we begin, want to give a quick shout out to our diamond sponsors, USA and St. Mary's. And then also we are also grateful for the support of Island as well. And we are going to be turning over the mic to Dwayne McDaniels and he will be discussing on the same level
what I learned building security tabletop exercises. All right. Well, give a round of applause to Dwayne. Thank you. I don't know what's going on in my intro music, so we're just going to skip it. Uh for those of you who have paper copies of the schedule, you'll realize that this is not the talk that is in the paper copy of the schedule. That's because they couldn't make it and I was asked to step in last minute to fill in with the talk. One of the other talks I submitted for this conference and that's what this is. So if you're like, "No, I don't want to hear this." Not your chance. And I won't take any
offense. Nobody walks out. I have no problem. Literally no problem. This will like springing on you. Um, but if you came in here because you saw the storage got switched online. Thank you. It means something to me. Who said I see me speak earlier today? Yeah. Okay. Um, this is what security looks like to me. This is what good security looks like to me. This is a family playing Monopoly. Now, I love Monopoly a lot and this is an impossible game. Like, no kid that age has that many hotels. It doesn't happen. like it must have just the dad's dominating this game. It never is too happy for them to like be that. So, but I love games because they give you a
practical way to experience things. This is why kids learn through play. This is why people make games. We can have non uh we can do conflict resolution. We can have complex conversations like cellan teaches resource management in a way that very few other games or anything can aside economic theory. But when we think of things we do in computer science, things we think we do in security, typically we think of screens, we think of being behind a keyboard. The way you use your machine is not the same way everyone else uses their machines. You don't believe me? You let someone else use your laptop and then cringe that they don't know how to use it. Literally, it's or touch someone
else's machine and watch them their same reaction. Like the fact that no one knows all the hot keys for Caden live bothers me. Uh it's an editing software, but every time I've ever seen any else do anything, they go through the menus like how are you that slow? Because the way they use their machines is not the way you use your machines. The their machine might look like this. This is not your machine. Why is that important? Because we make a lot of assumptions that people in our world that we're securing are on our level with at least some base concepts, at least some ideas out there. And they're really not. Even people in this
room are on a bunch of different levels. And that's awesome because that means we're on the same journey together. Stairs are different levels. There's nothing wrong with being three stairs up in front of somebody or three stairs down from someone else if you're all going to the same place. No, you just got there in a time based thing. Like we we live in time space. That means here and when are the same thing like conceptually I'm Dwayne. Obviously I think about this stuff too much. I live in Chicago. I came down here for this. Very very proud to be here. First time in San Antonio. Saw the Alamo yesterday. I saw some punk rock last
night. You have a really cool city here. Be proud of that. I host the security repo podcast. Check it out. I ain't got a lot of time. I got 20 minutes to get through about 60 slides. So, we're just going to go my company, GitG Guardian. They'll come up later. We put out this report every year, state of secret or uh voice practitioner. We're working on the next iteration of this right now. It'll come out sometime in August, I think. Uh don't hold me to that. So, this is the one from last year. We asked over a thousand IT professionals, hey, a bunch of questions. And 27% of people that wrote back said, "We're relying on
manual code reviews to get over this problem of hard-coded credentials." And I took that personally. I said, "Look, there's got to be a better way to do that." And we were getting ready to go to Absse Village uh RSA uh when the 2024 report came out. And Absac Village, if you don't know, who's ever been to Defcon? Should all go to Defcon. If you come to Defcon this year, come to Absac Village. I'm one of the organizers. Uh, full disclosure, I love that place. But back then, I wasn't. This is before I got involved and did that. Actually, this was the first year I got to help like volunteer organize. But I built a game called Spot Secrets.
Finding secrets through your environments by Git Garden. That's the thing. Uh, you can actually go look at the um rule set for this at the labs there. But this is what it looked like. It was a card-based game. We sat around a table. I got people to run through it as fast as possible. You can see I use that same stat on my explainer board and it looks like this. We have four stacks of things uh commit samples, log files, uh samples, slack message samples, and Jira commit samples because those are all places secrets commonly show up. And I ask people like, "All right, do you think there is a secret on this?" A secret being something that grants
access to another system. This one's easy. Yes, it says access right there. That is a real key. There are so many forms of secrets that it's really hard. So the way the game worked is if there was a secret had an S on it in invisible link uh UV light and if it had a V that means it was valid. I brought a copy of this to to San Antonio and it's in my hotel room. So I apologize. I didn't realize I left it at home until literally they tap me on the shoulder and say hey can you do this talk? Sorry about that. If anybody wants a version of this, let me know. I will
get it for you. Very quick. My game, my exercise wouldn't exist without these uh back doors and breaches. They have it over there. They've been doing demos all day. If you don't have a copy of B back doors and breaches, do not leave this event without one. If you've never heard of Chronicopia, it's cuz it's one of the 300,000 things that OASP does, and it get buried along the way. But it's a paperbased skills game they built. Really good to learn. Uh, you can even order it from the website. It's on the OAS project. Look it up. OS Cornucopia in the wrong secrets. Uh, that's where all my code samples came from. It's a OAS project on how to not do secret
security correctly. It's it's a goat. It's literally this is how you don't do it. You want to test your tools against a really insecure thing. This is bug free at least if you don't count bug. Anyway, 562 people gave us email addresses. More than that came through when I talked to them. But what did I learn? Well, the biggest thing is there's no one path in security. Holy crap. Defcon brings everybody to the table. Literally everybody. Doesn't matter what you look like. Doesn't matter what you smell like, especially not what you smell like. You can come to Absac Village. You've been to Defcon. If you've never been to Defcon, there's a 321 rule. You have to sleep at least 3
hours a night. You need to eat at least twice a day and shower at least once. And this is 110 degree desert weather. But if you want it, if you want to go down the path of security, you can get on the road wherever you're at. And all roads lead to security eventually. You can be a lead hacker doing this for 20 years. You can be a mid-career blue teamer who's only ever kept databases safe. Thank you for your service. You be entry level thinking, "All right, I I want to learn how about all of this and I'm just excited to be here." You're all welcome at Defcon. You're all welcome at ABSAC Village. and I talked to the the
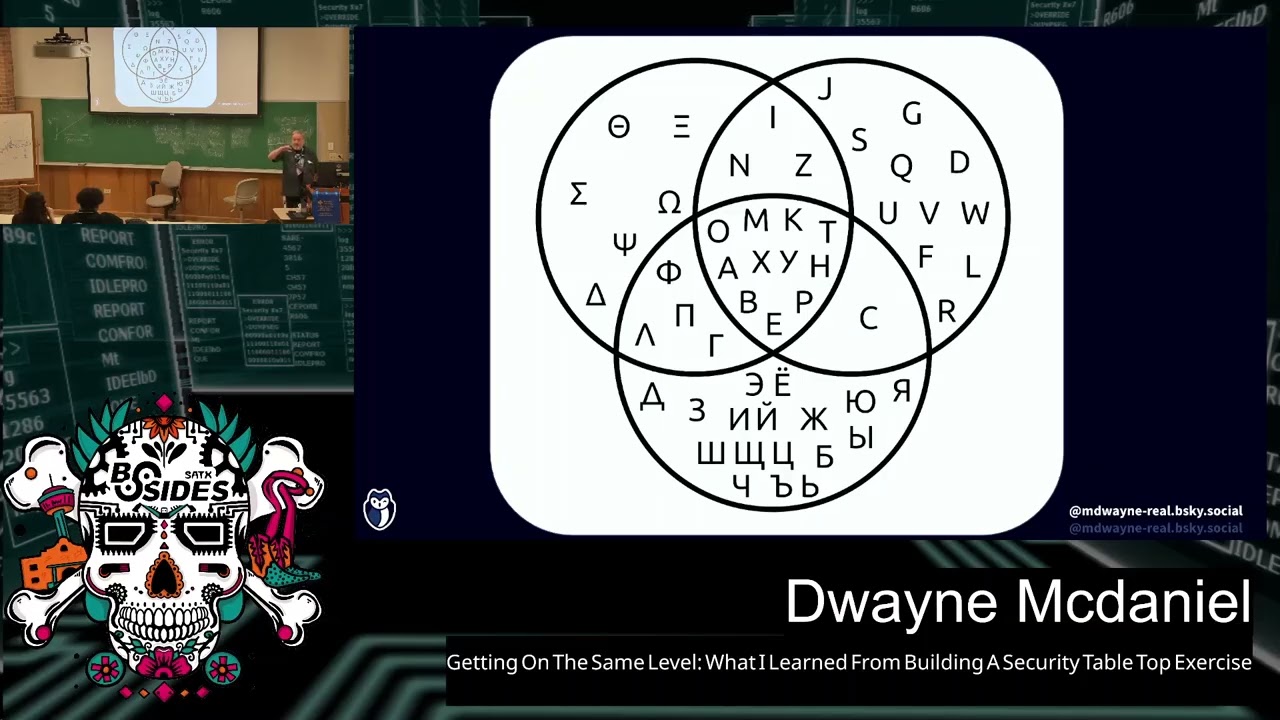
whole gamut. Turns out in security we don't even speak the same language all the time. We all use our own uh phrase. I just went to Identiverse this year, the the AM conference and like talk to people that write the protocols for like open IB connect and uh like are on the boards for things like Whimsy and and Spice and new things coming out of the IETF and a bunch of other standards bodies. Pixie is something you should all never mind. We no time to get into all the the craziness, but they all use their own shortorthhand and jargon. And the IM's people do not talk like redteamers and redteamers do not talk like midyear or
mid-career like application architects that specialize in security systems. They should we meet in the middle. We do have a common vocabulary somewhat in security. But when we step back and realize that we are security and we have this problem of communication, it kind of makes sense that security is seen as an over there an us versus them problem by pretty much everyone else in the world because our view of the world is keep it safe. Their world is get it done fast and that shows up nowhere more than than development. I'm an OASP member. I love OASP. I will promote OASP until I don't know like something goes horribly wrong in my life or their world. I don't know. Uh but the
whole world of o OASP ex worldview exists around the application itself. Like why do you have a network to run an application? Why do you have machinery to run applications? Why do you have users? Because you have an application application center the world. And I know I make a lot of assumptions when I'm talking about red team uh to redteamers when I go through pentesting classes when I'm I'm studying like the IM world. I make a lot of assumptions like you know what I know and people are like no no I don't but I think we naturally do. It's the bias of I had to learn this or everyone else match had to know this too
because everybody else knows a little more than I do don't they? Maybe not. That's why I like vin diagrams so much. We know what we know. They know what they know. And our roads overcross sometimes, but I'm not going to ask anyone to ask like maintain or tell me the rules of accounting and like how you can qualify to be a CPA in this country. I don't expect anyone in the room to know that. If you do, that's cool. I just don't expect you to know that. But we people assume like we need to put multiffactor authentication on your device. We assume they understand what that is and why. We got to stop making assumptions. So, the three big things
that I walked away with after asking people a bunch of questions, me and my team sat down afterward and said, "Hey, what did we ask? What did we learn?" And I wrote a whole blog post about this. Uh, Defcon 32 is uh the blog and it goes into all that, but it really is three things. People had just this profound confusion that I honestly took me by surprise. At least a couple of these did, but I I lumped in these buckets. I work in the world of secret security, so I just assumed everybody knew what I knew. Note, I've been doing uh environment variables as the way to do production since 2013. And turns out the rest of the world
didn't catch that memo. I don't know why. I didn't know how, but we just kind of didn't. Uh gets confusing, and I'll explain why. And developer workflows are really hard. All right. Secret security. How do I tell if something is a secret? Well, sometimes it just says secret equals um but this is how you can tell contextually it's used in such a manner to grant access to another system. That's kind of it. Uh now how do you define contextually give access? Well, there's a lot of ways to validate that. Uh a secret can take the form of a long live credential. If you saw my talk earlier today, um I went into great detail about all of this
stuff. The one thing I want you to remember about secrets though, don't ever see them in plain text. If you see a secret in plain text, something has gone wrong somewhere. Tell security like, "Hey security, I found a plain text credential." And they will be like, "Cool, we got to fix that. Let's open a ticket." Unfortunately, this problem is getting worse, not better. And I wish my company would go out of business. And I I mean this because we focus on this problem as the core of what we look at in the world, our our worldview. So every year we put out a report, state secret sprawl report. And uh we do this by looking at
every commit that hits GitHub public. You can too. It's event api.github.com/events. It's the feed. You can go out just ingest the whole thing. We look for uh commits and we look for uh is public. So something becomes public that was private and say, "Hey, it's got a secret. If it does, we email the committer right then and there. Uh say this is where you did this in public. Please don't do this. And then we take a fingerprint of that secret. Uh it's a hash that we don't it only goes one way. Uh and then we like can match that with future hashes. And we can do that for business stuff, not to get into what we
sell, but we put out this report every year, state of secret sprawl. And last year, drum roll, I don't have enough time to play a game about this today. Uh that's how many secrets we found on GitHub just added in the year 2024. That's not cumulative. That's just added from the beginning of 2024 to the end of 2024. 4.16 4.16 ah 4.61% of all repos that were touched last year. It's 25% increase over the previous year. 15% of all authors. And you might be like, well, why did you only send 1.9 mill messages? We've been blacklisted for uh I should say disallowed listed um excuse me uh disallowed listed uh and banned on certain by certain people like oh well
we don't trust your data. It's like you signed a public commit that has an API key in it. Stop blocking us. Also a lot of people sign their email or sign their commits with bad emails. If you're in the room and you do that, please stop. There are people that really really really want to tell you you put the world in danger and we can't if it bounces so please don't. Um oh that horrifying 70%. So we've been doing this for years and back in 2022 we uh we found a lot of secrets and we validated the ones we can validate. Do can we do a non-intrusive call to the system and say does this actually work?
So we took a sampling of 11,000 of the ones that we found valid in 2022 and said are these still valid? I sent this email after this much times surely they rotated them and January of this year it was 70% still worked still had valid yeah rotation's hard so please adopt continual secret scanning I have a favorite on this list I don't really care which one you use personally I know this is being recorded maybe it's not I don't care uh I have a favorite but if you use nothing right now you're doing it wrong if you're using GP you're going to run into a world of self-maintaining problems uh open source is noisy Nothing wrong with that. Sometimes
that's a good thing. Depends on what your needs are. That's it. Secret security. We can have a whole discussion about that after this. I'm happy to go out to drinks if anybody wants to buy me a drink, talk about any of this stuff. So, get the most common question I got which shocked me to my core is what is what is commit? I have worked for two companies in my career that have git the title. Get kraken which makes desktop git tool. uh desktop cop git guey uh git for git integration for Jira and uh gitlints the most popular VS code plugin of all time I been teach I've taught well over a thousand people git in my lifetime um
like in classes and workshops so this like baffled me I was like security people just not understand git and then I remembered oh yeah git's one of the hardest things to learn isn't it because it's the concept of intergalactic time tra inter interdimensional time travel to store documents. It's weird. It's a really weird concept. Nothing else in the world works like this. And developers who have to use it day in and day out, nobody ever comes to you as a developer and says you have to learn Git today. What they do is we need you to make a PR by X date. In fact, no, they don't even say that. They say do project by date or
AI will take your job. Don't believe me? Go talk to Microsoft who's laying off people. Go talk to Amazon who's laying people off. Like it's developers right now are getting eaten alive because we got to move faster. We got to move faster and I got to move faster. At no point is anyone in that conversation saying, "Oh, by by the way, learn first principles on these base technologies so we can be fundamentally safer as a community. Everybody comes to get their own way." It's one of the weirdest things we ever learned. Like everybody learns JavaScript pretty much the same way. Everybody learns PHP pretty much the same way. Everybody learns how to do Drupal development.
That's a wall. But you learn it the same way. You power through it. Uh you learn open source tools the same general way. Git because it's so weird. Nobody sits down and read Who here ever doesn't even know who here even knows there's a Git book. Yeah, it's awesome. It's free. You can just go to get SCM git-m and read the book. It's a little dated at this point. They haven't updated a while. But you know what? The core concepts are never going to change. Most people know eight commands, maybe eight. Add commit push rebase, which scares everybody, clone, uh, a few others. Cherry pick. I hope you know cherry pick. That's a really useful one. And then there's the people
that use goies. And I got nothing against, but they don't teach anything. It's just automagical. I'm gonna go real quick through this part because I promised I would go real quick through this part to make this a 25m minute talk. Here's how git works. Git just takes a snapshot at a moment in time of the file system. It takes a time stamp, makes a list of exactly what happened and compresses down the actual files themselves into things called blobs. So when you do a git add, it takes the things that have been modified in your working directory, your present working directory that git is watching, that gets aware of. So that's when you do a
get init. That's you're saying, "Hey, watch this in every subdirectory under me." If you change something, it says, "All right, I'm going to make a binary log object out of that thing you just modified, which it collapses down using uh crap zib um collapses it down into really, really, really small compression. And then it throws that into a file called the index, which is a text file that contains binary files. And then you say get add and it turns that into a binary file that's ready to commit. And then you write on the outside of that envelope what you want to have on the outside of that envelope your commit message and say get commit. And now that
is a permanent record in a chain. If you're like that kind of sounds like blockchain. Yeah, this is where blockchain came from. This is cited in the Bitcoin or yeah Bitcoin original paper. This is Satashi took this and said we can make money with this. Lionus said that we could build Linux with this. Uh if you don't know, uh Git turned 20 this year, uh April 7th, it was Lion's wrote the first email that said, "Here are the patch here's this, uh scripts I use to manage patches for uh Linux. I don't think it's ever going to become a full source control management system." 3 months later, they rename it git. Those patches are still
commit zero. Why is this important to community security? Well, once it's in the commit history, it's there forever unless you surgically remove it. And if you're working completely independently by yourself, that's easy. It's just rewrite your history. You can already rewrite anything in history of Git. It's just lists. It's just list files and timestamps and compressions. It's all it is. But you can jump between those compressions like at the line level. It's crazy. Uh but once it's in there, it's in there forever. If it's a shared repo, good luck. If you've ever pushed it anywhere, there is a cache of it. I guarantee you. I just explained earlier how we read every commit that hits
the uh public GitHub. Have you ever heard of storing out decrypt later? You heard of this? This is what quantum computing is waiting on. >> Yeah. I was going to say, isn't it just like like bad actor as much information as possible? Yeah. coming out like like clouds that you could >> I yes that is the short good explanation of it uh bad actors there are nation states doing this and I don't want to call a nation state a bad actor publicly uh just just in case the drones are listening um anyway if anybody wants to go further and get oh so why is this important if you put a secret in a git repo by accident and you
push it out there you have to consider that secret is gone you just need to rotate it right Even if you cover it up with the next commit, that last commit's still there. If you did an RM on your machine and you fixed your branch and you tried to push that force that up to the server, guess what? There's a shadow cache on Git on GitHub that you can just go reach. All of those orphan commits, where do they go? Oh, they just hang out. There is a huge never turns off cache on GitHub you can hit for like 90 days after a push and just get anything back. If you ever push it publicly, you need to get rid of
it. I had so many people say, "Well, can I just overwrite that commit?" I had so many people like insecurity ask me these questions. So, if anybody here needs to help learn Git. I love teaching people Git. Last one. People really do manual code reviews to find this stuff. Yeah. 27%. Who here has ever, and this is going to sound accusatory, and I'm sorry, I was really angry when I originally wrote this, and I've backed off a lot um from some of the physicians uh crazy stuff I said. Apologies if you saw this talk at Wild West Hackingfest. Um, who here has ever deployed anything to production? Who here has ever written code, pushed it through a pipeline that went into a
public internetfacing application that users you will never meet that way outnumber their Dunar number will touch and manipulate that system. That's what developers do day in day out. That's their job. They make dev happen through the DevOps cycle. DevOps people build the infrastructure to make that happen. And I'm not saying that to accuse you of anything. That's what developers are under the gun for when you say, "Why don't you do this in cure way?" It's like, "Cuz I got told I was going to get fired if this didn't hit production by Friday." That's the world they're living in. I'm a developer advocate. I'm going to advocate for the developer until I don't have this job at all. I'm going to have
this job until I don't work any day now. Lottery. But this is the world they're living. Where security fit in that? That's answerable, sir. But uh yeah, but that's the point. That's why dev sec ops became a thing where we'll put security around everything. Oh, but wow. Wow. This is the actual world of production life. So when I say they don't know what we know and we don't know what they know, it's like can you explain the entire tool chain that your developer uses to get to production right now? If the answer is no, that's not your job to know. The more you know that, the more you can say, how do we secure this piece? Hey, do you realize
there's a really, really, really easier alternative to what you're doing that makes your life better and my life better and everybody's life better and you're more secure? I can't tell you what those things are right. I have no idea what your developer is doing. But if you're like, I don't know what my developers doing either. You know who you could ask? Your developers. You know what developers love? Food. I know humans love food. If you get them food, throw them a security party. Throw them like, "Hey, let's help you out with your scripts party and buy them a pizza. Buy them jelly beans. Buy them some food. But don't just stop at developers. This is everybody in your company. We're in a
world now where shadow it and vibe coding I when I wrote this vibe coding wasn't a concept but vibe coding is real and it's that stuff's getting production because I'm watching it in real time and it's nuts but the shadow IT problem is never going away either hey it was too hard to do through proper channels so I got out a credit card now there's a server under my desk I use chat GPT that I pay for myself on with company not data because I'm I work tech marketing so my blogs go through it but they're going to go public anyway What we need to do, and this is I know I'm over time, but this is the end. We
got to get everybody on the same team and realize that we have more in common together. If we work together as a team, we come together and stop seeing security over here, you over there. The only way we can do this is getting on the same level with them. And how we do that is we embed ourselves with them and don't expect them to come to us. This is the inverse of the model that has been more prevalent. Hey, we're sit here and we look for anomalies and we go punish people that do anomalies. Humans are humans. We're going to screw up. That's humans, especially under pressure. What if you could get in the room when the
whiteboard's out? What if you get in the room when they're like, "Hey, we're going to plan this scrum for the week. What if you could get in the room and they trusted you?" I'm not saying that's going to be easy. I am not saying that might even be possible where you're at in your life. I'm saying this is how we get from fighting all the time and people don't like us and don't trust us in security to oh wow you make my life better. I have a problem. Hey, we're going to have a meeting plan to plan this out. Who on the team your team can come over and have this conversation with us to make
sure that 3 months from now everybody's happy and have them seek you out. That's the goal with that. So here's your call to action. Go ask team members outside of security about their preferred coding, DevOps, or business automation workflows. Anybody that you're in charge of securing, anybody that you might be able to write an email to and said, "You did it wrong." Set time with them, 15 minutes, 20 minutes to be like, "Hey, I'm just trying to understand your workflow. I'm not going to judge you. I'm literally just there." And then just be a human with them. At the end of the day, security is about humans. Humans do all this stuff for now. I
don't care about AI. Find out where the bottlenecks are. Figure out how to help them with that. If you can make their job easier and make the easy path the safe path, they're going to use it. Developers are inherently lazy and that's a virtue. They will automate their way out of any problem if they can. And if you can say, "Here's the safest way to do that and the easiest," they're going to take it every time. Who here knows how to write a bash script? I dream of a day when I'm on a bid and every hand goes up. It doesn't have to bash. You could use PowerShell. For those of you who didn't raise your hand,
do you know PowerShell? Everybody should know PowerShell a little bit. I hate it, but we should all learn it. GitHub actions is just Git and Git hooks are just just scripts. Use Bash. It's universal. It's on most machines you'll ever touch. Come to Defcon next year. Last year was a blast. I learned a lot. Teach people to silly the game. If you want a copy of this, literally hit me up and I will mail one to you. I literally just forgot them because we're all on the same journey together. >> Not just the people in this room, not just people in security. We're all just trying to get through the end of the day because I just want to go and play board
games with people that I love. I want to make sure that it's not 3 in the morning and I have to get out of bed and leave the house for a week because wow, we had an incident. I want to protect these people. I want everybody on my team to have this experience. Let's go on the same level. Oh yeah, don't make people read 100 cards if you build a card game. It's that was too many. I put it down to 20. That's the last point. I'm Dwayne. I live in Chicago. Came down here to do this. Uh and we are way over time, but I work for this company. Um that don't you worry about the QR code. That just goes
for our blog. I don't really care about the stats on it. Um but we help people with anti-governance, secret security stuff, and honey tokens and some other fun stuff. And you want these slides that we saw today, it's up there. Um, tiny world.com says you can even read it. Okay. Thank you. >> Thanks, Mike. We got five minutes before they're got to do a closing ceremony. So, talk to me on the walk over.