BSides Vancouver 2015 - Irfahn Khimji & Ken Westin - I am The Insider Threat
Show transcript [en]
all right our next speakers are are faon and Ken and they're going to be talking to us about The Insider threat please welcome Ron and Ken thank you uh yes my name is Ken Weston this is zon kimg so we're both with tripwire and uh we're going to be talking about Insider threat today um and we're going to do it a little bit differently than you probably heard about it before we're going to do a little bit of a good cop bad cop um I get to be the bad cop um and eron's gonna be the good cop so um I have a lot of experience um actually setting traps for people I'll talk a little bit about
that um and nuron has a lot of experience actually on the defensive side and actually working with companies to set up uh defenses and security policies um and things like that particularly around Insider threat so uh we'll kind of be switching off here and there um I think it's really important to uh to kind of look at from from both perspectives um you know you have to be able to understand um the the malicious Insider um and sometimes you have to think like them and think about um especially as a privileged user you know what damage could I cause to my organization um I even think about like what if I went rogue you know if what if
I had to come up with a bunch of money or somehow I was comprom we don't want you go Rogue so um yeah so I um I have a background um um these this is what I call my Wall of Shame um these are actual cases I've been involved with where I've actually U put people in jail um I developed a lot of different tools um sort of friendly Trojans if you will um that would actually um trick a like a USB flash drive into compromising a computer uh send information out about um where that device is who has it um I then also built tools for um uh covering stolen laptops so uh utilizing the
built-in web camera getting location off Wi-Fi networks um and then other tools too that we're dealing more with grabbing serial numbers off of um images that are posted online um I have a bunch of recovery stories that are like that so I have a lot of experiencing uh sort of develop ing these traps um and I'll talk a little bit about that how we can use traps like this to catch the malicious Insider um and also use um some of the the rules for the correlation of you know different log formats and things like that and how that information can be used to identify suspicious person so so you want take so key thing here is
in any organization the the greatest asset is also its greatest threat right the people you guys um really key here because an organization is not going to run unless it's got good people and good organizations always have good people now what happens if those good people turn Rogue and that's that's really key so I had a um for another company I work for we actually had a case where um I was um managing the web servers and the systems and I got a call around 3:00 in the morning uh getting alerts that the web server was down um I I went in to try to figure out what was going on at the time we had open source version
of Trip Bar so I could actually to go through and identify pretty quickly what had happened um we actually had an admin who was in charge we had actually hired a contractor to go in and help with security hardening um come to find out there was actually a disagreement with management about being um him being paid he was actually o over billing um and the management wasn't um paying the full amount so he decided he was going to show us so he logged into the main web server and decided to bring it down um it was a really bad thing for him we were able to provide this information to them um and the server was actually
being used for law enforcement purposes um so he was actually um interfering with an active investigation which is also a felony um and uh the thing here though is that if management would have notified me or other admins that there was a problem with this particular contractor we could have de-escalated his privileges um they weren't aware that he still had access at the time there wasn't any sort of notification that went out to the rest of the IT staff that his work was done or that there was his particular issue so some interesting stats here right um 38% of organizations with a thousand or more employees have experienced one or more Insider threat incidents uh I'm sure that's gone up
over the last couple years that's a couple years old um 58% of information security incidents attributed to Insider threats um now one of the questions we always like to ask is you know what makes somebody go Rogue um so I throw this question out there you know feel free to shout out an answer I can't really see hands with the lights but um what do you think what would make an Insider go Rogue any takers sorry sorry money there you go okay money anything anything else evil bosses that's a common one sorry General disgruntlement yeah something could have happened so if we take a look at those stats I mean we got a whole bunch here so fraud is is a big
one this is from the US CT um IP theft Espionage it sabot sabotage um a couple of the key ones were uh some of the the recent ones that I noticed were around uh competitors and competition competition's been heating up lately again this stats uh think about a year old or so but as competition comes up um people are trying to recruit others from from their company and hey if we're going to recruit you across from a competitor bring over some information we'll throw you an extra bonus when you when you log up so money was a big one uh bosses was another one I heard out there I don't know who that was but uh don't worry I
won't tell your boss um and really if you're not happy and you're and if you're not happy with where you work you're going to be looking for other employment and if a competitor wants to recruit you uh they might give you a little bit of incentive to take something out along the way yeah so you guys are familiar with killchain when it comes to hacking but um the FBI actually developed um one specifically for insiders um it's a little bit different when you're dealing with an Insider threat because um they're not stealing credentials and doing unauthorized things they actually have authorized credentials and they're doing unauthorized things so um the first is sort of the recruiting or the
Tipping Point um and this is sort of where they decide that they're going to go Rogue they're either they have that bad boss and they're going to show them they're going to damage the server um they're going to steal data um or um whatever the motivation is um the next thing they're going to do is they're going to go through and they're going to be um doing search and Recon they're going to identify what do I have access to what information do I have access to through Salesforce uh cloud services um or other file shares I might have access to for some of this information or you know how can they escalate my privileges or get someone else to get that
information for me as well and then they move into the acquisition phase where they actually start doing the acquisition of the data or they may actually start causing damage to the systems um and then of course the exfiltration of that data um and uh or damaging the server U bringing it down and that's where we actually have the damage within the organization and sort of through these phases we have different ways we have prevention detection and response and it's not always a technical thing right um we we hear a lot about um particularly with HR and legal um they have to play a really key role when they're dealing with Insider threats when this comes down to
recruitment um doing things like background checks making sure that um these these folks they don't have criminal uh Records or um have done anything illegal um but there's usually going to be non-technical indicators and this also requires that um these departments work very closely with it departments um a lot of times these organizations are very siloed um it sometimes doesn't talk to um HR doesn't talk to iht and the legal department isn't involved um what's really interesting is if you actually have a very strict security policy um that basically says you're allowed to monitor what they do on the computer even if you're not necessarily doing it it does have a pretty significant impact on
people's behavior it's sort of like the if you put a a surveillance camera if it's fake um people are going to behave a little bit better in that environment than they would um otherwise if they don't think they're being monitored um they're they're going to be a little more on the Rogue side um and then of course we have the technical indicators which we'll talk about a little bit more here so what what are some indicators of human risk right how do I know that uh you know from a non-technical perspective that there could be a chance that you know one of my co-workers or somebody who reports to me or even one of my bosses um could be an indicator of
risk or could could uh become an Insider threat so some of the things we look at up here is is you know are they consistently the first and last out of the office um has this person actually had time to uh review or share their work some a lot of times if they're the first and last out of the office great they're fantastic IC employee do you for a bonus do you for a raise right not always um there's a lot of cases where they're just trying to have people not look at their work maybe they're coming early in the morning try to find something where uh try to find some time where others aren't in the office yet to
access some systems that they may not be they may they may should not be accessing um they might be you know staying a little bit late to close off some stuff or to set set a job to run at night um to have it start up in the morning or have it run overnight and uh shut it off in the morning before anybody gets in there um 12 plus months without taking a vacation how many people here like to take vacations anybody yep almost everybody this guy up here he's just does not I'd watch out for him um but if they haven't taken a vacation in a while have they actually shared any of their work with with any
of their co-workers right has anybody had a chance to be backup for them uh there may be somebody that's a backup on paper but are they actually getting a chance to look at that person's work and review their work uh if they're not getting chance to do that um and they're in the office the whole time and and segmented might be a chance that they're looking at something else um of course these individually may not be that suspicious but when you kind of pile things in together um they tend to add up right um Life Changes right somebody shouted out earlier just disgruntled in general right something happened in their life they could just be hey I got
nothing to lose I might as well steal some money or steal some sensitive information that I can sell um things like giving notice or being laid off right if I give two weeks notice you better start de escalating my privileges because you don't know what I'm going to take on the way out right it's not necessarily private information it could be customer data could be things that hey if you know if I'm in sales for example I might want to take my customer list so I move on to the next job and I already have a customer list I don't have to start from scratch um that's things that that happen in that two weeks notice so a lot of these types of
things to to take a look for um so how do we how do we detect and prevent some of these things right um so we look at background checks we we look at the threat modeling uh we look at um periodic security awareness training you know a lot of a lot of individuals may take information with them unknowingly it might they might not know that it's against company policy they might not know it's illegal um awareness has really been key and and we we heard a lot about that yesterday uh from some of the other talks and it's really getting that awareness out there and getting people to know that hey this stuff's against policy um you know periodic uh
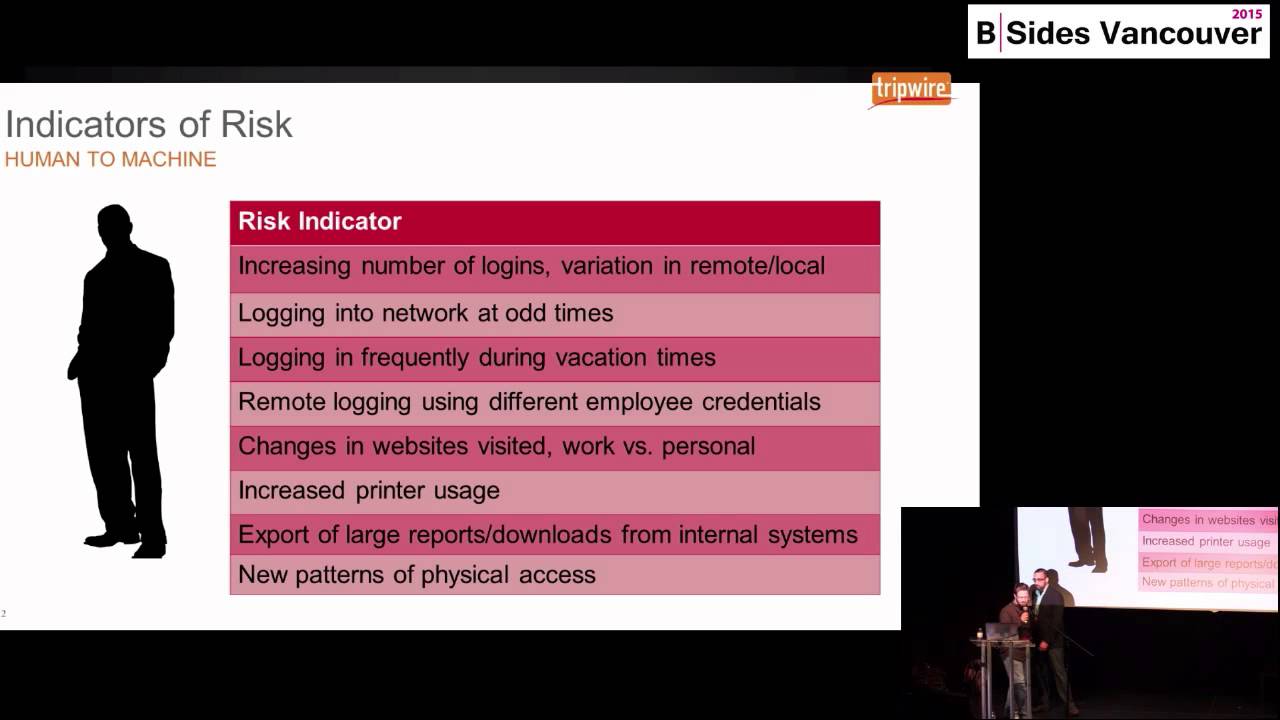
or monitoring for suspicious Behavior again that goes into more technical things which we'll get into uh um as well as you know establishing clear clear lines of communication you may have a disgruntled employee an employee may not be happy with their boss but they might like their boss's boss they're one up um and having those clear lines of communications where you can actually talk about these things and and build a better working environment really helps um to deter people from from become from going rogue yeah so uh so now we're going to get more into the the technical side so um indicators of risk when it comes to humans to machines um so as people interact with the
devices on the network um you know you can see things like an increasing number of logins A variation of remote versus local um and we'll talk about some correlation rules for this and our our log intelligence or our Sim tools um but these are things that you can start to monitor for um you should have this hooked into active directory so you're able to get some of this information um you start to see that they're logging into a network at odd times uh sometimes at midnight or 2 o' and that may not be an indicator that they're a rogue employee but it could be something that someone else is using their credentials as well so those are things we want to
watch for um logging in frequently during vacation times um again that's might be an indicator that someone else has has their credentials and is using it not necessarily that they're actually logging in from their on their vacation but someone else may have access to to their logins um remote logging yeah so changes in websites visited work versus personal you start to see that they're using LinkedIn a little bit more often um maybe spending a lot more time on Facebook um usually you know you don't want to go and invade their privacy you start to see that um they're on that for four hours a day that could be an indicator as well that there might be a
problem um yeah you see an increase in printer usage um you know still a very easy way to exfiltrate data um a lot of times organizations still don't they don't monitor what's being printed um and they should um you're going to see export of large uh reports or downloads from internal systems or external um how many people in your organization are using Salesforce how many of you actually have audit logs of what your salespeople are downloading right so there's actually something you can do there are uh logs that you can go in you can get access to some of that information unnecessarily that large reports are being created U but you can access and get some uh it's almost it's
in a CSV file format and you can put that into your sim or your log intelligence tool as well just something to consider um also if you see a large file share that's actually being created somewhere on a server or on a computer that might be another indicator that someone is downloading that information from somewhere they shouldn't you also start to see new patterns of physical access if um Simone's using their key card to get into a server room or to go in a different part of the building that they usually wouldn't be um that's another thing that we want to monitor um so when we want to talk about um uh DET Tech prevent we want to
implement strong password and account policies uh we want to enforce separation of Duties lease privilege and data classification these are things that we should be doing anyway of course but this also applies to Insider threat as well um so we want to do extra caution with systems administrators and Technical or privilege users I think this is one of the biggest things um you know um using DLP services or tools are great for dealing with you know your sales people or people doing regular business activities but when you're talking about privilege users in particular um there needs to be additional um reporting additional logging that goes into um all their activities as well um or using temporary
passwords things like that is a good idea as well um you want to implement system change controls and approved process uh you want to deactivate uh computer access following termination uh we'll even show you some examples here of actual companies where this was a major issue not only in deactivating those accounts but also monitoring what other accounts did that administrator create so uh maybe you deactivated their account but they had created Five other admin accounts that you didn't know about um and so they're going to be able to use those to get into the system um and then of course we want to log uh Monitor and audit employee network activities so uh so what do we want to log and
monitor I get this asked a lot the first things um you know if you're just getting started with logging uh make sure you have firewalls uh unsuccessful login attempts that's a really good for Insider um unauthorized changes to systems uh so if you're looking at like file Integrity monitoring um or uh security configuration monitoring as well uh modit or any sort of configuration file changes antivirus alerts uh physical access so um we'll talk a little bit about that in some examples a lot of people don't realize that the the hi devices that have the rfed chips they actually generate logs large majority of them do and um and that's actually something good that you can bring into your sim to monitor you
know where someone actually is within the building it helps U with um evidence if you have to actually put them in front of a computer for example physically um and then intrusion detection systems of course and then your web proxy logs ah I got a lot here um so you know when we we look at um log data in particular uh you know you can call it machine data um but it's really important that you realize just how uh Rich that information is a lot of times when this information it's out there it's um we we store it on the systems or we archive it but we don't actually make use of it um there
animation builds out so we want to look at um how the the information gets correlated um and then you want to be able to create dashboards from that as well so we talked you know a little bit about threat models when we talk about Insider threat uh we want to identify what are the Poss ways that they would go in and actually you know access confidential information what would be the steps and what would be the the trip wires that would indicate that they're actually up to something so we want to be able to um take all this log data and we want to create what's called actionable intelligence information that we can actually use it can either be through
alerts um it can actually activate scripts um if you see that someone is um trying to um access a server they shouldn't maybe fire off an email saying hey you've just been tagged here uh just to let you know that's a warning or you can even um automate some other um other things as well um and then also Integrations with other systems so if you have a SIM or if you have um some sort of HR System as well um you can do an integration here as well and then you want to get into analytics forensics and compliance and that's not necessarily so much in real time but being able to have an archive of all of your log data all
that activity that happened on that Network um it's really helpful if you have to terminate someone this is where we start getting into the legal aspects right if you terminate someone for doing something like this you better have the log data to back that up um there can be potential lawsuits or if that it does turn into a criminal case um you're going to need that information I talk a lot with the FBI and one of the things that they always come in the first thing they ask for when there is an incident is what where are your logs that's the first thing they usually ask for when there's been an incident and a lot of
times they don't have it I've seen a lot of companies they don't even have basic log collection um and that's a real challenge when they're dealing with Insider threats or you know any sort of security issue in general yeah just to add to that a lot of things we're we're seeing lately with um with various vendors and within the security Community is is that a lot of these tools that you guys use um on a day-to-day basis Now integrate with each other or are working towards integration so um if you don't if you haven't already looked at how some of your your tools can work together um it's a great idea to to go back to your vendors and
say hey you know what are you doing to integrate with the rest of my security ecosystem um how can I automate a lot of things that I have to do manually you know instead of me having to take this alert and go over here to this next system and look up something else how can I just have that automated um vendor Community is trying to get better at it so it'd be great um if you go back to them and say hey these are the things that that we we' like to see so interesting case study we had not too long ago um without getting too specifics it was a power company in the US there's plenty of those so hopefully
that doesn't narrow it down too far um there was a system administrator who was who was terminated and obviously if you get fired I wouldn't be very happy if I got fired I don't know many of you who will anybody would be happy if they got fired no the guy who didn't like his boss yeah okay um so of course you know didn't have a good process didn't have a good procedure didn't have anything going on at that company so they left their credentials they left that guy's credentials in there um how do you know that uh he shouldn't be accessing that right so what did he do middle of the night logged in um logged on to uh
disabled logging on a firewall uh um and that's kind of things that we found so how did we find that right um if he's logging in at an odd time you can create a log in your sim like how would you find that rather um was there a successful log on after hours so basically if you've got a a log collection tool right if you're seeing something that uh you know somebody logging in at an odd time you can create just a simple rule that says hey if I'm logging in outside of regular business hours right something sketchy in there unless of course you know there's a change window and things like that but that's typically something um I want to
be looking at um second piece in there is was there a successful log on um to a high value Asset from an unauthorized system so yes okay it might have been within a change window that this person was accessing the system um but if it's from outside of outside of our Network or somewhere that shouldn't be logging in from this is something else that that we can fire off so these are just two simple rules you can create in in your login Sim to be able to detect um unauthorized access from somebody who was who was fired um of course better practice really is to disable their account so they can't get in uh but in
the event somebody forgets um here's a way to pick it up so uh another fun thing to do uh just to experiment with is doing um Insider uh honeypots um so utilizing these tools um it can provide you some indicators of maybe people who are poking around the network in in the systems um um it's also good for um if a hacker does get in for example this can also be u a defense for that as well Gathering some additional intelligence around their intentions um one thing to note is IDs systems they should not only be deployed on your perimeter but also inside the network a lot of times people will think you know we're just going to use this
protect the perimeter but actually the IDS systems like snort or bro um they're really powerful when you're using them within your network um how many people actually use ids's inside their Network as well any two small handful anyone in particular like snort or bro or snort good good so it's um so this is kind of what an alert looks like if someone's actually running end map um against snort um if they're not quite sure what they're doing they're running an initial scan this is what it would look like um and this is something you want to ask if someone in marketing downloads and map and starts scanning your network um you want to be able to have some observation
as to why they're doing that um and uh and be able to provide those reports next so this was just something fun I did with eron here um so uh you can actually create these honey document files there used to be a site called honey files or honey docs or something like that um it's no longer active but um you can kind of create your own uh last time I buy you a flight to to a conference yeah well I just sent this to Fon I'm like hey can you open this up and see if it works these are not real credit card numbers so those have you taken pictures except for Fons that's that's
real so um you can throw an image bug here so if you look down here I have a web server um and then um for example I just want to name this campaign eron kimg honey do um and then I save that as a just a dooc file and then you can put it on a file share uh somewhere on the network and then if you go to the next slide sorry just simple thing like this didn't even pick up on anything I opened up on my laptop no antivirus no nothing didn't didn't pick up anything at all so uh yeah so here's what it looked like I have one for credit executive salaries nuclear launch codes you know
whatever someone that you know know that is a malicious Insider maybe they won't have access to um salaries is always a good one um but then here's what the log files on my server look like um when he he pinged this I was able to get a few of them um and uh it was it worked pretty quickly and seamlessly and I'm able to get the IP address and maybe it's an internal IP but um I can also if he's he's at home and he's connecting I can correlate that with VPN logs um and I I identify like the employes home IP address as well and see that this was actually open from their home
network next so second case study we had now that he successfully exploited me um was was a tire company so this was a large uh us Tire retailer again not naming names um and what happened was an employee created a back door for remote access so hey you know it takes too long to VPN and Citrix and I don't know what and what you have to do nowadays to to work from home why don't I just create a back door um well again the employee was terminated but the back door was never closed so you know a couple of days later uh I'm pretty disgruntled I got fired from my job uh let me try to log
in and and see what uh see if my back door is still there cuz I'm not going my VPN may have been disabled but my back door's still open fantastic um so now I can try to siphon information um out of the organization so again simple log rule to be able to detect that is was there a successful log on to a high value Asset from somewhere that that shouldn't be there right uh very simple rule that you can create in your in your login Sim um and then of course an example because that unfortunately didn't go detected but in the event we were to detect something this I created uh sort of a demo of how you can so we we have a
a file here that we got a user to download it was how to get a huge raise. pdf. exe so you know if I want to get a huge raise I got to open the PDF right but it's not a PDF um and what that did is is open up uh a new firewall Ru so just a quick difference in terms of of what the firewall looked like before and after so over here we notice we had uh a new rule that came in called open sesame um opening Port 1337 with my file how to get a huge raise. pdf. exe so now all of a sudden I've got my back door open and here you can see just uh before and
after that now we're listening on that on that Port uh good so I want to talk a little bit more about physical access and actually talk about a case study let build it out here so um I uh I had built a tool a long time ago that uh basically was called USB hacks I was really interested in USB USB based Trojans and actually turned it into a product um and uh we actually had a guy who had a flash drive stolen and it had this agent that was installed on his Drive um and so um his 32 gigabyte flash drive was a college professor had a bunch of research on it um so he really wanted to get that back
um and we're able to see that um it connected from a particular uh University and a computer lab um but that wasn't a lot of enough information really for law enforcement um IP address if you guys want to talk about attribution IP address is not enough to put someone in front of the computer which is a big challenge um so we needed more information and I was uh talking to the uh campus security and they found that well actually the they require a student ID card I'm like okay well there's logs data log data there right yeah and then oh yeah come to find out they um also had a bunch of computers that were stolen out of that
lab about a year ago so they actually installed uh security cameras and what I found too is that those also generate log files so so if you look at uh sort of non-traditional approaches to identifying physical access so if you look at you know student ID card swipes RFID those all generate log files um as well as any sort of uh video surveillance those also generate log files and you can bring those into a Sim or your log intelligence tool and correlate that as well so here's what uh looks like um in our our log product where we actually bring in some of these these HS we're able to see the name of the person and then we also have this
tied into active directory so it's really nice being being able to follow people physically around the building as well as um you know virtually when they're logged into the network good so um so some sample log detection rules that can be created um you know log on attempt from a terminated employee or contractor um you know odd remote login patterns uh from the employees on a watch list um if you have that communication with HR um they can they can either um add names to that watch list or uh work with it to to add those names um again you see you start seeing logons from employees at weird times high value assets from unauthorized systems uh creation and
deletion of a user within a certain interval um add and delete user so these are all just some examples of various rules that you can create and correlate that correlate them with other um systems go on the next so here we're going to do an example so uh let's say we have an employee um whose Behavior it's looks a little suspicious um let's monitor and see if he's connecting to organizations outside um C actually did a bunch of U sort of attack vectors and they found that this was a very common one where someone would actually uh SSH into a remote server and they would upload information you know if you're going to steal data that's probably the easiest
way so uh what we're going to do is we're going to setep rules to watch and alert on connections from outgoing ports after hours um and we're going to look at these particular ports so if we can go ahead and go to the next slide there sorry it's kind of tiny but this is a it's in SEF format which is a common expression format or and uh so this can actually be um imported into most log intelligence or Sim tools um arite Splunk they all will support this um but here you have a suspicious Connection by risky employee that's going to be the name and the alert that will get fired off um you can establish your uh time
ranges and then um you know the the name of the user um the IP address and other information then we want to identify and monitor any sort of ports here so this is good for the technical guys but then what about HR right how are they going to be able to identify this you can uh EAS easily create dashboards so they don't have to uh mess with the technical aspects of it so here's a dashboard that we created for HR um you know I talked about the HR watch list well this is tied into active directory so we can easily watch those particular users and watch their behavior um and also look for any um anything else that's
suspicious so any of those correlation rules that we talked about earlier for the malicious Insider those can be easily brought into a dashboard here so if you're using like our product our our log product or you're using Splunk or arite all this is possible so really just to kind of tie that all together is is you really got to look at your logs um a lot of the data breach reports and all these things that come out they say well hey you know you could have detected this if you were monitoring your logs well that's fantastic but what are some of the challenges that we have right there's a lot of volume there's a lot of logs uh
if you're logging everything you're logging everything there's a there's a lot to look at there so really how do you know uh you have to be able to identify certain rules and certain certain criteria to take those lots of logs and really look at the things that are important um so really determining um what you have and what you're going to do with it um policies and procedures right um You got to make sure you have legal consult for this because if you're monitoring everything and logging everything um for your staff at all times um you got to make sure there's legal contracts and things like that in place and and you consult your legal
department um false positives are always a big a big problem right if you're if you're creating all these rules and you have all these things blocking automatically or detecting and sending emails you don't want to get flooded with a thousand emails or you know a bunch of calls at 4 in the morning um so you got to make sure that you you tune and you work um to to identify and and streamline all these logs to things that are important um and then establish a baseline right so what is normal um and everybody's normal is a little bit different right every organization's going to be um a little bit different than than the next organization so so
there's no real out of the box that works out of the box um it's going to require some tuning and it's going to require some work um so you got to be willing to put in that work so you're able to to tune and remove those um and then um accessing the information right so who needs it so like Ken was talking about just now the technical folks are going to need their technical stuff um HR is going to need to see HR things compliance for people are going to need to see compliance stuff so really being able to access the information and provide the appropriate reports to the appropriate people um is really key uh and being able to identify
that so you're not just throwing information at people but you're you're working with them to tune them and get the appropriate information that they need so once you get all those logs well we need to respond to them so you need to be able to automate and and action these things that happen so if you were detect an Insider threat or any other threat um you need to be able to um take the appropriate actions um if something gets happened something gets compromised you need to have secure backup and Recovery um you need to be able to quickly audit a user's behavior for for forensic purposes to see where they went did they only um look at this one server
or this one firewall or where they spread out across the network um you need to be able to identify that um and then develop an Insider incident response plan so in the event we see such and such happen you know we see Joe or Jack or Paul or whoever um infiltrating our systems or something like that you need to have a response pen in place and it's not just the IT team it's not just the business team it requires um several people throughout the company to be able to do that so to sum it all up right The Insider kill chain is going to be a little bit different than than your average breach or your average hacker
because it's coming from the inside um there are human indicators um and machine indicators of uh of Insider threats um there is um instrument and gain Telemetry of indicators um and you want to ensure that you have rapid response and Recovery plans in place anything else you want to add oh I think that's it all right so uh if you guys want to reach out to us we're pretty easy to get a hold of um and if anybody has any any questions please go
ahead yeah so in this case the the examples that we pulled um is not necessarily around DLP and most organizations I've seen unfortunately don't have DLP in place it's usually uh an added bonus if they do um majority of organizations have things like uh vulnerability Solutions they've got uh login Sim is usually the first thing that anybody does in a security program um so just being able to use existing tools is really where the focus is um the other thing with DLP is that um if you if you're siphoning out information a lot of times if it's an authorized user um of that tool um they'll be able to get past that so this is just looking
at at different ways of doing it and of course DLP does work as well in that case any other questions all right thanks great thank you everybody





