Allow myself to encrypt...myself!
Show transcript [en]
so uh I have been uh working on the AV rig I I go around to conferences and and do AV and uh so that you guys can enjoy it afterwards and hear stuff and listen to things and so my laptop was tied up doing that and I had to borrow my buddy Tom so uh hopefully everything will work because I have not had chance to run through the slides on his laptop but uh a little bit about myself um so this talk anybody was here last year uh besides uh Charleston last year show hands repeat attendees that's good that we got a few of you I wish you know got a lot of uh new face which is even better um so this
talk hopefully will make some sense because it's a follow on to a talk that I gave last year it was called Dungeons and Dragons Siege Warfare and Fantasy Defense and depth so any of you from last year remember we uh like sacrificed the Black Knight called admin dude um you know like we we played this little game called Fantasy Defense in depth and uh and pretty much showed us how like Warfare and and other things like eventually lead to this futility of Defense right so I'm going to try and give us a little quick recap for those of you that weren't here and and I chose an Austin pow theme because um most of you are are are trying to stay awake at
this moment um anybody any hangovers only seriously what kind of con is this um I guess it's out of college so we can't actively uh promote overc consumption of alcoholic beverages but uh um later tonight there will be a party somewhere that I'm sure you will be able to do that and so uh last year we talked about dude um and so what this concept was is the progression of warfare so we got a lot I know we're in Charleston here we got a lot of military type of uh contractors and things like that progression of warfare anybody understand what that concept is it's a I build you know man makes spear I get Shield I take woman you know all those
types of things you know this progression of now we have the castle and we and so Siege Warfare right well the idea was is that we as Security Professionals are still in the dark ages of Defense because we're still very much focused around putting up a perimeter defense that we want to try to make impregnable and so this this leads into this concept and I'm going to highlight a couple of key Concepts before we get into what this is but one of the things that I ran into last year was I I wasn't able to share as much of the presentation as I originally wanted to and it was because I presented It bides Las Vegas and out of that I was going to
share this framework or concept um that I called presentation layer or six and a half and I'm giving the presentation and we walk out and this dude from a very big company walks up he's like you can't talk about this anymore like why can't I talk about it he's like this is patentable somebody will steal this like you are presenting a framework and you don't even realize what you have and so when I got to besides Charleston like two months later I I pretty much was like locked up with a couple of lawyers trying to figure out like do we have something that we really need to protect if we you know because my intent was to
hey as Security Professionals let's open source something let's like come up with a collabor means of of trying to fix an issue that we have and so here we are now and I can actually share a little bit about this and and uh and and why because uh some lawyers helped us protect it from patent Trolls but uh so as we talked about the history of this and and defense like at first when we first started like you remember back in the day when you got your little Nokia phone you wanted connectivity right so I'm going to talk about these are two major Concepts we need to have this understanding of is connectivity versus connected
and so connectivity was this concept that you know oh my God I can have a phone with me anywhere I go holy cow that's amazing you know oh I can have a tablet that I can carry my stuff with and then that quickly shifted right you didn't just want your iPad with you everywhere you want you wanted all the files that were at home on your laptop the files are in the computer um I'm going to use some very vague and obscure movie references and if you don't like Austin Powers 's something wrong with you but um so key concept right like it shifts from access to inform or access to services to availability of information and so as
we think about like what does this really mean uh there's a concept called pervasive ubiquity and what pervasive ubiquity is about is about the future of connectedness and you know in the future in the future I'm gonna use some like nobody's launched anything at me yet um I I I have a very dry sense of humor so I'm I'm going to be digging for like you might have to catch up anyways um so pervasive ubiquity which is this concept of like you know borderless networks right anybody heard of borderless networks what does that even mean nobody really knows software defined networking software defined networking people here okay or like as I like to call it the uh
like you know it's a big freaking memory Hub you know like networking hubs anybody we're in college anybody know what a hub is um you know so so what pervasive ubiquity is about is like this concept of like self- routing data devices being aware of each other your your freaking you know milk carton telling your refrigerator when it's out of milk and things like that you know so that you can make your shopping list and and uh you know somebody can deliver it to you or whatever and so some of what these what these these concepts are is that we are pushing responsibilities of networking interconnectivity into different layers of the application stack and so when we when we talk about
why that's important and and we're going to show you why encryption and the implementation and the mechanism that we use for encryption and and other things is is busted and why we can't we don't think we can trust encryption like how many of you really trust encryption a couple of hands you yeah okay yay encryption encryption is a great thing um is encryption busted we'll talk about that here in a minute but the IDE is that what is a network what is a um you know what is an application even what is a file system okay how many of you use dropbox like where's your fi you know where are your files is it on your hard
drive or is it in the cloud or is it both um you know how do you leverage devices so this this concept of like virtualizing even file systems becomes a little bit more obscured as to what um like where that perimeter is now and so we're going to take a moment here and reflect Mr riddlesworth so the idea that and I talked about this a little bit last year is that security and kind of our methodology for doing things now is we Harden devices we deploy products uh you know we monitor them and things like that it keeps bad guys out you know so we draw that Line in the Sand this is mine and that is
yours and that if we keep bad guys out of the systems that have the the stuff that's important to us that you know that we can win well how many of you um are successful in keeping the bad guys out 100% of the time joance I'm I'm audience participation here right I am victorious I don't monitor anything so I always win right I always love that one um so then you uh like but the reality is and what we as Security Professionals try to teach people in our organizations that it's it's really about minimizing data exposure encrypting data okay some of you may or may not be doing that protecting devices because you're not going to keep them off of them right
they're going to get your iPhone you're going to plug it into the uh you know how many of you have the uh the the USB condoms anybody know what a USB condom is all right sweet um real quick USB condom for those that aren't aware is a uh it it more or less strips out it takes it down to only two pens so that when you're charging your device at like an airport that the Chinese can't like you know I love that like I always love the uh I heard Jason's talk at uh Derby con and uh and absolutely love it because uh you know it is it's hilarious I I actually do a lot of work uh in my
day in my full-time job explaining to people how like the Chinese are often the least of their concerns um but and then preparing for an inevitable breach how many of you prepare for breaches in your organization like very few people and so what what that is that's proactiveness so as I'm looking around at these things I'm looking at Technologies I'm and I actually was on the fence a minute ago Jason about which talk to give because I gave a talk at Scott oon and hacker halted about how to hack the emergency alert system and uh and that one's a lot of fun and I take over a radio station and do a bunch of fun stuff like on
stage and uh and Jason made me like really think okay let's let's show about like how hackers are actually helping fix things so we're going to we're going to apply our our mcgyver principal here and uh no you don't want to use duct tape that's all I got to say um bad idea so so last year I talked about this briefly but this concept of that security is 3D and so as we we and we realize this right like I can encrypt all my data and put it on Dropbox but what's the problem I can't view it on my iPhone anymore right unless I have an app on my iPhone that can decrypt the data and blah blah so all of these
things start to compete with each other so to be completely secure like to get all these things green like you kind of get hopefully you understand this concept of like TR you have to protect in transmission storage and processing but then you have the basic concepts of confidentiality integrity and availability and then all of these are impacted or touched by technology ology policy and practice anybody do that here anybody policy and practice people uh and then the human element so so what is this look like kind of right now well and what this is showing is that any of these things can be negated by a weakness in the other area and so it's kind of warped I'm going to skip over
this because I don't have time for you to fully absorb what this is talking about but like this is this is reality if it'll go back fail a it's up sucks sucks to be me um you know this is kind of reality of what we really face but like how can we get it as close to this as possible because in my mind unlike McCumber who created this this concept and this is called the McCumber Cube so this is not something I created um so that means that instantly it has a level of intellectual capability that is far beyond my own uh ability uh so the reality is like from the human element you're never going to get it
100% anytime humans interact with at some point we're going to fail in some area that's going to cause security to be lapsed so when we talk about uh so I started to attack this problem like wanted to understand encryption and how encryption was vulnerable and how security and data and Transit and all these other things how do we get as close to that green as possible and I being from primarily a network background wanted to think about things from an an aspect of the stack and so when I started to look at this you know you have a couple of different competing models uh not really competing kind of the same and and I'm going to introduce
something that I call the software developer model and uh this is in no any software developers in the room okay I I want to open your eyes to something this is in no way meant to be like I had one guy come up after this talk at another con and he was like you know that was kind of insulting and it's like no it's not meant to be insulting it's about how you view this is like so you know as a networking guy we view seven layers then as you get into a uh you know a troubleshooting perspective you're kind of looking at it from you know the dcpip model or the dod model or
whatever but then when it comes to software development it's what device am I going to put this software on what application package am I going to use to develop it and what services does it provide me so like Apache or JBoss or Java or something like that I want my application I want to write it one time and I want it to work on as many devices as possible Right hello how many of you like writing tons and tons and tons of code for every single other little device no nobody wants to they want to write one app and it work everywhere so that's what this concept is so what ultimately like a lot of these
application Frameworks do is they provide a set of Base services and an application framework or API stack to develop on and there's where your application lives and so what we're kind of getting towards is that more and more frequently here where we're using interpreted languages and Python and all these other types of things it's to make all of this stuff at the bottom ubiquitous it's to make sure that like code works everywhere and it's right across and your data is available everywhere you go and all this other type of stuff and so ah this is the slide that's jacked up um so I'm going to ask a question here real quick where does encryption live in this
stack and I don't have a gift like here but like there's a giveaway as part of this whoever guesses this qu or whoever answers this question will get whatever goodie everywhere it exists at one layer and I'm gonna I'm going to so we're going to we're going to look at so we're going to look at it from this perspective okay anybody heard of these standards or these these different Technologies okay so so would you agree that this this is winning that this works right so I'm G to I'm going to click back here real quick and hopefully winning will not pop up but if it does I'm sorry um so where do you think encryption is supposed to be it's it's
it's in one layer even with all of these protocols encryption is at one layer appliation a presentation presentation okay now what is that makes perfect sense and whoever who guessed it it somebody be honest right all right right there so if I get a giveaway it's you um so wh why does this make sense okay so let's think about like jpeg or an image file right so the image file isn't the application the the image file when you en code it like jpeg or PNG or whatever it's a representation of data in a certain format that's intended to be visualized in a certain way make sense okay so how does where does encryption fit in that
it's it's exactly the same right you take you know you take um plain text you render it to Cipher text and then back it's a present you know it's a a change of format which is what the presentation layer is about and so when you when you look at these other things and people say well what about all these other different areas it's like there is an application stack on all of those in each of these implementations that takes it up to the presentation layer and brings it back when you run your data through an IPC tunnel on a Cisco firewall or switch or router or whatever you're running it through it's going from Layer Two up to it's taking all the
layer two traffic running it up to an application stack and bringing it back down and sending it back out does that make sense okay so it's supposed to be at the presentation layer so when we get it why is this stuff um like why is this stuff attacked it's because we're taking data and bringing it down into lower levels of the applica of the tcpip stack and it gets exposed to vulnerabilities at all those different levels right so like why does you know like a layer two encryption I'm taking data that if it's going to be encrypted should be encrypted at layer six right but now it's going all the way down to layer two before it gets
encrypted and then it goes back you know anybody see some flaws in this logic okay now I'm not knocking those encryption mechanisms those are great things and the reason they were done were for compromises performance you know uh maybe we trust things maybe it'll break other things you there's all sorts of reasons to do this but because there's all of these you know different standards in it it it kind of starts to Jack things up so let's look at like once we get into that big fat layer that application layer so we've got session presentation and application and what all exists there and how does encryption exist in these different places you know there's there's all sorts of stuff
that's here to do this and why is that not going so when we look at like how encryption is attacked like how often I mean how many of you heard like AES 256 is vulnerable anybody agree that it's a vulnerable protocol okay it's still the like DOD standard AES 256 right there's nothing wrong with AES 256 so then we had like web right rc4 everybody's talked about you know rc4 is vulnerable think it's a bad algorithm no rc4 is a great algorithm for what it was intended to do and so what I like to what I want to talk about here real quick is that hopefully I'm doing okay on time I have no idea how
much time I've spent um oh okay yeah I'm all right so I'm gonna my apparently the notes didn't come up here so I'm like uh kind of Flying Flying Blind because I didn't change the let me see if I can add notes here because that would be nice to have my notes yay let me okay so when we talk about attacking encryption we're not talking about attacking algorithms okay we're talking about attacking implementations and the reason I say that is and we hear some people how many of you've heard that I know in the dod world people like to talk about that a little bit like they're not really attacking the encryption and the reason is because aes256 is an algorithm
right it's a it's a method for taking plain text and rendering it into Cipher text so how many of you DOD people like you have a safe right or a skiff or whatever if you ever look at like a vault door or even if you buy a fire safe right you go to a Home Depot and you buy a fire safe how do they rate those rate them in hours have you ever lo I mean anybody ever looked like how many hours is this device going to survive certain levels of heat and things like that before the stuff that's inside of it turns into a crispy cracker you know that's how these things are rated and encryption is exactly the same
way it's not meant to be unbreakable it's meant to make sure that the by the time that somebody takes the effort to do you know to break it that it's not worth anything anymore okay so ases 256 isn't meant to take Cipher text and render it unreadable forever no it's meant that if somebody intercepts it and we don't want them to how long is it going to take them to get the information that's in it and if they do is it worth anything anymore let that kind of sync in for a little bit it's a very different like for some reason that's like for a lot of security profession that's a very odd thing for them to grasp and and I I can
understand why but like if you go to if any of you work on base somewhere and you work in like a skiff and you go up to these like crazy Vault doors I guarantee you somewhere on it you will find a number of like man hours okay how many man hours is it going to take for somebody to break into that why because if somebody is determined enough and can get to that door they're going to get through it okay why do we have do people never break into banks no they break into Banks all the time the intent is is can we prevent them from getting in Long enough so that we can get the resources
there to stop them okay and that's what encryption is about so why is aes256 so easily broken you know when we're using it on our SSL websites and everything well the reason is is because all they have to do and the reason that uh heart bed and other ones were so effective was is that we we destroyed a session level service that had a vulnerability in it and because data came down past the session or the applic or I'm sorry past the presentation layer unencrypted it was visible to the services operating at that level following me nod heads all right do the hokey pokei turn yourself around you guys are like putting me to sleep um so what's
happening here is we're not attacking encryption algorithms we're not attack we're attacking implementations and we're attacking poor security architecture and design that is allowing these very in advanced standards and very appropriately applied and designed standards and allowing us to like apply so what happens when we take something from the application Level like in a web browser and send it down to our Apache server is the Apache server takes that clear text Data puts it through a library at the presentation layer brings it back down and sends it down the stack and because of that we can see it unencrypted above that layer so what's the issue with TLS you know with layer 2 encryption anywhere above Layer Two I
can see it unencrypted why did it ever go below the presentation layer in the first place we're going to talk about that so what we what we kind of as I'm sitting here looking at this going why in the world is this happening the reality is is that there were a lot of compromises that were made and a lot of us like to reuse code I'm not going to talk about code reuse or apis or any of other type stuff because that's a dead horse that just doesn't really have a whole lot of value but we we literally we apply we like to reuse sessions services and interfaces and those exist at the session layer um one of the
things that I didn't call much attention to um and I and I want to real quick before we uh go in uh go too far is the services that exist in this layer um so some of the things that a lot of us think is uh like AAA and all that type of stuff those exist like all of those terminate at the session layer okay so there's no protection for user information beyond that so once I get to there that's and we we all see this like bypassing UAC vulnerabilities and other things like so anything I can get to past that like anything above that there is no none of no control for that stuff
in in modern operating systems or applications okay just going to throw that out there because it's important maybe you'll learn something from that developers um like control sandbox your stuff appropriately and apply it not just so like I I say that because like I hear sandboxing all the time and people wonder like how do I get into other sandboxes from stuff it's like well if I tack it at this level and then go up um it's yeah so so what do we have this is how how we do application development right hopefully it'll stay there for a minute so we have in libraries and other things and Os libraries and other stuff that we access
at a presentation layer that we call through our software and yeah we have like we're going to trust that these those defenses all those other things work okay we're just going to for purposes of the rest of this conversation we're going to say that we can't do anything about those protection mechanisms we're going we're going to trust them all right because they do provide us some measure of protection user account control uh dep aslr all those things they provide us a measure of protection and uh and so ultimately the issue isn't those things getting compromised that's causing unencrypted data to be compromised it's you know a failure to implement it correctly and so what if we just like made a standard way
for us to access encryption what if we put something there that was standard that said application developers this is not an API that you use as part of JBoss or your Java development thing your flash package that you're developing your web apps for or your C libraries for net or anything else what if we made a standard methodology across operating systems in a standard way like so that's that's ultimately what this issue is right as a software developer you use those libraries that are provided with the platform that you're developing on and you trust that they're going to to provide you security and the reality is we've we've seen like yeah there are vulnerability in them and everything
else but so what if we kind of this is where this application layer 6 and a half comes from is you know we're not creating anything new what if we just provided a library that provided a standard mechanism for us to interact and get data and encrypt data so we more less bring things out of a Sandbox and instead of taking them down to a lower level we run that data as part of the uh you know our application process through the library it provides us you know we don't block access to the encryption libraries El right because tons of other applications are using them for encrypting application layer stuff and everything else but we take user
generated data run it through an application library before we present it to a service anybody following me yes thank you thank you for that my one true friend so anybody see how like something like this standardizing this method like providing something standard could possibly provide us a little bit layer security so preparations a through G work total failures um so this this is a pretty complicated issue so we we get into some things like uh so like when we talk about access control and data control and other things like that um implementing multiple models of access and data protection and other things like this like anybody have I mean y'all are familiar with these concepts of role-based access versus
mandatory access for all these things like none of this really it all gets kind of crazy right and it creates this this massive I don't know orgy of Vin diagram or something up here um but uh so I'm gonna GNA think about the best way to to broach the rest of this issue and and skip over things because I'm gonna have to move quickly um what if we could like take some of the best of these things and merge them together and take you know instead of just so we have user protection okay which is like AAA services and things like that then we have some things like data protection like where we have metadata and file
system journaling and other things we provide Access Control to those types of things how do we take those things and put them together and like the holy grail for for like data and systems protection for quite a while has been like how do we take things like location based data like you know you never take your cell phone to to usbekistan like how are you like accessing you know your Gmail from usbekistan or something like that and then apply that you know how do we merge all this data together to create you know real time Access Control right that's we've been trying to do some of this stuff for a while so what the concept for this patent and and and the
concept for this technology came from was like how do we not create anything how about we use we've got all these different standards and all these different things that are out there I'm not going to read all these off but I'm going to scroll them across the screen like how do we take all the the latest and greatest stuff that's out there and all the work that all these people are doing and how do we how do we make this magical cocktail of stuff that can give us a higher level of protection okay how do we Implement cryptography how do we use encryption in a you know the right way or a way that everybody can use that would you know
not mean that they're not going to get hacked but it means that we have a lot better mechanism for everybody to interact everybody's playing from the same Playbook okay and so so when I started looking around and doing some research on this I found there's like a buttload of crap out there and all of it's completely independent and it's probably really hard to read but there there are more rfc's how many of you like reading rfc's okay yay do your happy dance you know I E and Oasis and all these people have all this crazy stuff for like you know Geo zacal blah blah blah XML with this type of stuff it's like so there's there's tons
of stuff that's out there but I will put it this way every single one of these different little standards is in a silo like there is a working group that is developing that in the context of just them and they generate an RFC from it so it it gets a bit challenging to like try to take any of that and put it together and like and you wonder why web developers aren't implementing you know xml-based you know like geolocation information standard formats like why everybody has to do it differently is because reading those fraking rfc's makes you feel like Billy Madison over here you know with the little lost puppy that could so um so what I presented last year and what
we kind of came up with and I'm going to zip through this and then show you some diagrams of what this patent type of stuff is really about is scalable perile pki encryption for ubiquitous Computing with decentralized active Access Control file management Data Destruction through certificate revocation or archiving and revocation WTF okay what it pretty much means that's the one sentence deal is like we as users we use applications how many of you use applications all right those applications now because of certificate Penning and other things they get digitally signed right you know it's been a kind of a standard thing developers have to sign their code by with a you know a key that says that
they are them so you know they use that private key to do that and we load those devices on the or load load those applications on these and we interact with a user account right or an identity that we interact with devices with and then hence those applications and users a lot of times have public private keys so what if we made sure that every user had a public private key and then we use those applications and we generate data okay so what if we took this so now once you generate this data and you save it to the hard drive or whatever it gets synced with Dropbox and everything else and it's in the clear everywhere it goes
and now Facebook owns it with their terms of service that you know like legally castrated you and um but what if we you know so then we had this thing this massive thing called called uh pgp like so I create an identity and I have a private key and I encrypt my data and then but if I want to share it with anybody I have to know their public key and so it's kind of a pain in the butt right and you got to share keys and you got to do explicit trust and web of trust and everything else when I say it's a pain in the butt it's fraking awesome it's one of the coolest fraking
security Technologies ever but it just didn't scale very well and that's why we haven't seen here we are however 20 years later and don't have mass adoption of it so one of the things that does work really well though are domains and domain trusts and other things and certificate trusts through uh like by getting a domain right like SSL and certificate revocation lists and things like that they work pretty well right when you visit google.com or you visit Amazon you get the little green check mark up there right anybody F me yes all right feedback thank you because I'm gonna like sit here in awkward silence from now on until you answer my questions uh you can ask Chris Sanders
where was it of course he remembers that one where I just like Issa nobody would talk nobody would respond and so I was just like I'm going to sit here and make you feel
awkward anyways um so you know when we interact with data now like we we use SSL and stuff like that and so and it pretty much equates to we use their public key right to send them data but what if we took that data and our identity gets validated right we're M of the domain we have access to it what if we use that uh that that magic merger of stuff that that VIN diagram and we used a thing called context based Access Control what if we created something really cool and we use context based access control and it takes that data in and we've appended metadata and all this other type of stuff that applications
and everything put on it and we send that through our file server and the file server takes it and we have things like DLP how many of you have data loss prevention Technologies in your organization you know that do you have social security numbers in there and you have all these other things and blah blah blah and so now I've you know not just you know better than SSL like I've encrypted with the public key of a domain right so only that domain can open it right it's not even a man INE middle thing with a session it's once an application gets it that knows what to do with it so now I take this data and I
analyze it and I you know then I make a a decision like okay I'm going to store this in a certain way so then we have you know some basic concepts of like you know identity to role-based access control we have context and metadata we have files and settings that we can do like you know we're trying to give it some some greater level of detail of like authentication access control but what if instead of just like right now what if it's just users and device like users that have public private key sets right what if we gave a policy a private key what if we gave a you know some of these other things private keys and what
if they could encrypt data that is specific based on the domain and what the domain thinks that it should be doing you know based on domain policy that uh not just that social security numbers should be um protected but that they're protected with their own private key and that even if a user gets the file that the data inside of it now is is protected with a domain owned private key for example maybe not registering yet like what that could open up but um so now I take that and I generate another file that that then gets sent out to Dropbox with the public key of Dropbox but now Dropbox doesn't really have anything that they can use right like they might
have stuff that's unencrypted in there that I don't care about through my policy or whatever but for the most part they'd have to have the private keys of the rest of this data to actually read it anybody following me okay okay we're going to go into a little bit better detail but um so you know then what I have is this this idea of like that files can have encrypted data like maybe I encrypted something in there that's just for me and I don't want anybody else to see so what's different about this uh and this is this was literally the one thing why why I had no clue why this could possibly be patentable was
literally just the what if I gave public private keys to ju not just users what if I gave encryption keys to policies or to data structur or any number of other things right we're kind of doing this with data loss protection technology or prevention Technologies and other things sort of you know they have roles or they have identities or something like that that they belong to that that you have to be a part of but it's all pretty much still like we deploy public private Keys based on roles and and mainly users so what if the keys were disposable so when data gets compromised or something like that we just destroy the keys and the data is dead right
isn't that what happens with pgp when you forget where you stored your keychain anybody ever have that happen like and crap I suck um and you know so I've got a ton of encrypted email that I will never read again um you know there's that kind of concept so what if but we we'll keep going here all right so Dr Evil this is this is the patent and it's I know it's impossible we're going to break it out in a minute so it's a process it's not a bullet it's a silver bullet or anything like that it's a process so what if we take take that standard set of encryption hello that standard set of encryption libraries and
actually make it applicable now we give you a means in which to do this so now as software developers it's not just an issue of having a framework that does it for me like yeah although this would eventually it would ideally be applied this way right but what if everything applied a standard framework that doesn't you know that's open source I you know we'd all be playing on the same field we wouldn't have to pentest every single little implementation of how we do encryption because we're all doing it the same so I'm going to introduce two different well one of the things oh too far no don't do this to me do this let's go back here real
quick so one of the things that I want to want to identify here is like so we have two different base Concepts right now trust domains anybody know what a trust domain is it's users devices applications uh role based stuff blah blah blah domain stuff all the stuff that your domain Pro policy provides well we're starting to get away from devices and applications being inside of that right because you know they're being produced all over the place so what if I use uh you know like users applications or I'm sorry users domains uh devices then we have data domains right and a data domain would be where we take things like you know where we organize and
aggregate data into meaningful things to our organization or things that we want to protect but the problem is is that right now data loss prent is focused on users accessing things in context to this and we then rely on even though we have data prevention technologies that are monitoring these things they can't do anything to protect them outside of the trust domain they're all based around whether or not the trust domain actually allows them outside of it so like what happens when snow everybody's perfect example Snowden right he walks out of the building did the data loss prevention technology do anything for them no because there doesn't I didn't install that stupid piece of software
that's running anymore so it doesn't do anything um so let's let's talk about how we can like bridge data and Trust domains and so my big Mantra last year was Data protection not data loss prevention now I'm not talking about like touring machine code and things like that like Adobe PDF and what it was supposed to be where you have like self-protecting data and things like that no this is way more simple than that you don't have to install an application it's a process right data never leaves before it's encrypted and even when it does leave it's encrypted with a private key that you may not have and so if you don't have that private
key you can't open the data theoretically right all right so what we have happen is users generate data in context of devices and applications we have user identities when it's in the context of a domain those users get authenticated with a process pipe and a AAA process pipe and so the idea of the framework is not to exclude anything the idea behind a process pipe in this process is to allow you to use Noel if you freaking want to or to use open El app or active directory or you know I don't know smoke signals or something I I don't know um but you generate data and and can we make this sense that like in these verticals data
doesn't necessarily need to be shared horizontally okay it can be but the application doesn't necessarily need to see what the user is generating like when you generate a Word document how much of that word document is the text that you enter in and how much of the rest of it is how word processes and format stuff does word need to see that data to make your document work I can tell you it doesn't because I've actually screwed around with encrypting pieces of stuff in there now does it know what to do with it no but it can make it bold um you know so uh so we're going to that's just an idea to throw out there but then we run down
through this process you know as the process runs down we generate data data gets aggregated the file gets created right we the user digitally sign in cpit because it's the owner in a domain concept right or in a domain context the user is the the owner of a file right following me generate a Word document look at the owner people um you know then we domain user gets validated and crypts and forwards the data onto the domain for storage onto a file system somewhere right so now we enter into this data domain concept and so we have concepts of like you know what is a field you know so we have some abstract concept of what a field might be so it
might be like uh you know the you know the first three of a social security number right so you know everybody always can see like even the guys at Verizon can see the last four year Social Security remember to evaluate you as a user right so we may have to divide those down into different fields but then then you have data types which is like all three sets the the N how many seven nine numbers whatever is for a social security number that equals a Social Security number so that's a type and then you aggregate those into like an object model which would be like your identity so a social security number plus a phone number plus all these other
things and then you put those into a data model and you know so then what happens well DP we have this policy decision Point process and DP and some of these other things they actually have policies on like how data you know how to identify data and how to you know when do I alert if a certain level of user has touched it and things like that anybody following me all right this is academic so I have to make sure that that I'm not uh putting everybody to sleep so what if we extended this schema and like instead of just having like a policy decision Point added context to that and what if each of those context
so we have like key in certificate management I see J my buddy Jason over there from ways away um I remember certificate management right that was a big deal like how do we rapidly deploy keys and certificate and other things I can't talk about why I know anyways sorry j you can go ask him about a cool project that he was working on years ago um but uh like what if we extended this schema and gave public private keys to like I said applications data types file system tags of all things right like OSX what if we could restrict access an encrypt based on an OS system tag that'd be kind of cool right like I don't even
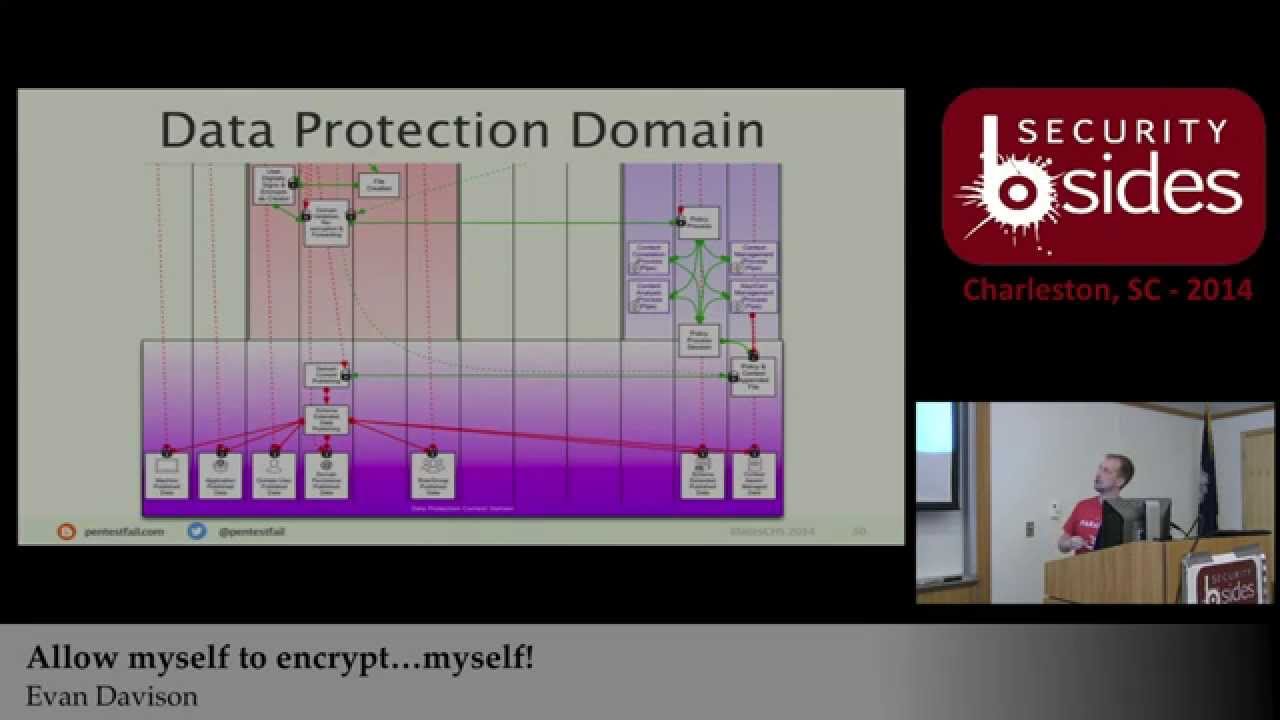
have to like move I don't care where the file is I apply a tag to it and boom it gets encrypted with the Pol you know with the rules that I set for that data tag or something so uh you you extend that stuff out and then how do we put all this stuff together well data protection domain is is kind of the the methodology by which you do this and so I'm kind of zooming in here to show you how this stuff kind of links together and then I'm going to zoom in real quick because I'm probably going to run out of time or they're going to hook me off the stage and and
I'm not Jason uh street so they will probably like just C me in the knee or something and I'll have to crawl off here um but a protection domain is so it's it's the bridge between trust domains and data domains and so what I what I want to do is you know add context add policy you and then create a means to generate policy around this and so we have things that that we do this with all the time right like uis application developers you know use a URI and things like that that are like you know abstract you know identifiers for purposes of you know aggregating certain types of data so it's faster to
you know call it or whatever so what if we use some of those types of basic concepts and we in this data protection domain when data comes in we inventory it at the PDP we allow different process pipes and I think it was on this oh yeah it's still right there so as the data data comes into to the policy decision point and the policy process opens it up I can't read that I don't know how in the world you guys can um you have you know content correlation processes all right so processes that are saying like when these pieces of data exists together then this then I want to do this with them and then you have other
things like uh content analysis okay so that's that's your data loss prevention technology that exists now right so we're not creating any new technology we're not pissing on the vendors we're not in them out of anything like they did to us we're not creating anything we're saying this is a process you want to have your latest AAA you know actor directory I'm not saying you can't use it you need to do it here and then once data comes out it needs to come out this certain way and so once it comes out like we can we can you know key insert management I'm not this this patent does not cover those things that's not the
intent there's a lot of great technology and great development that's being done in those areas we just want to provide a standard way for these Technologies to interact and to play nice with each other and so that way if I want to have my open source pgp type of file encryption deal that I can do it so then policy process you know so then that session ends and it spits out data and that data might be encrypted like we showed before where like a a a role has access to certain pieces of data inside of it it's encrypted with that so but it but it comes out after all those determinations are made so policy is
created context depended to the file and then it's forwarded back to the domain for storage and so once that do once that data comes back and I my mouse doesn't work so I can't like Circle it I should add like a laser pointer or something H sharks with freaking laser beams um there's an Austin Powers reference um so we have now what I call uh schema extended data publishing okay and what does this mean it means it's stored somewhere file systems you know virtual memory I I don't know wherever data gets stored for this particular piece of um you know uh meme meme wonderful goodness of you know that that you've generated that uh you're text file or whatever and
so uh so you have data that's published with the private key or or with you know that's encrypted for the machine you have data that's encrypted with the private key of the application so only that application or developer can open it for example um so we're still talking in verticals here at the same time so I'm not exposing data left and right to you know a user data to the application that doesn't need to be exposed I'm not exposing data to other things that that doesn't need it and then the data gets published back and so you know and then what this allows though is is that because data is owned in the context of
a domain unlike pgp if I want to share with 10 different users accessing it on a file share you know how do they access it right well they don't anybody following me like you know you you have to have the private keys of that or the public keys of that user to send them the encrypted data and once they do it you don't have any control over what they do with the data because they now own it anybody follow me weaknesses in existing technology um you know or limitations in it but the difference now is that we've encrypted it with a private key of a domain or of a policy decision point and it may be an organizational domain it
may be something that you own yourself because the idea behind this is open source so we want to create you know ideally we're going to in the future create your own you know policy decision point that you can have for your data that you generate in the context of your user identities and other things uh your email domains and so forth and uh and so once you do that we we then kind of um so let me go back because I'm already jumped ahead of myself so I just want to make sure before I stop I'm rambling and I'm going very fast because I've got a lot of data cover am I making any sense anybody this kind of changing
anybody's mindset say again not really um so there's this thing called A Beautiful Mind and uh no um I don't have one uh so uh if you really could read everything that's going on in my mind it starts with like F this so um but so one of the things that I call attention to and the difference in this framework as opposed to a lot of other open source Frameworks and why a lot of Open Source Frameworks in my opinion are rejected by Major organizations is because they feel like it prevents them from having access to to do something or to make money off of it and that kind of was and I know everybody like you know they want to
think that oh that's evil or whatever but no like some vendors like a lot of vendors they provide a legitimate value for something they answer a question or a problem that an organization or an individual has and and they're they're developing something to make your life easier hopefully right so like what value do you have by locking them out of it well then you lock yourself into a proprietary solution so there's a couple of companies that are trying to do this type of stuff like encryption throughout the pipeline and protection and where you have keys and things like that and role based like how do I share a file with you know put a file on a file share
that multiple users can access simultaneously but maintain it encrypt it all the time you know these types of things the problem is is that they most of those Technologies because they're afraid of people stealing them or whatever are closed they don't want to allow people into them so what if we don't close this off let's add a process pipe for all these different services and obviously we have to do it for future proofing right like I have no idea what awesome new data something something technology is going to exist in 10 years I have no idea you know TCP TCP version 6 may actually work right and we might do something cool with it um just saying
I I don't know so the intention of this is to allow some level of future proofing to allow new technology to enter the process and to do it in a in a controlled way and to have that access that they need to do it so some of the things that the pro that this technology or that this this process framework stays away from is like identity and access management you know there's just way there's so much stuff out in that space open off and all these other things that work well and do what they need to do but problem like problems with them are usually like we said they're not attacking open off necessarily it may have a vulner ility
but like when it attacks encryption tied to open off it's probably because it's not implemented at the right layer right we kind of starting to see how like some of the vulnerabilities and some of these things you know probably would be thwarted if we encrypted it at the right place and it never went below a certain layer in the stack unencrypted maybe um certificate management there's lots of cool tools out there that do that data storage and transport ultimately doesn't matter anymore right because it's going to be stored it's not going to go down to a session layer protocol and get transferred anywhere without being encrypted right so maybe that stuff is dead maybe TLS doesn't need to exist
anymore I don't know um so uh the reality is is like is this without its potential problems you know no but so I talked about like active access control and what that means is is like so I have a policy decision point that when you know Jason Street wants to read a file and his thing or you know you know James over here wants to read his or Jason over there wants to read that they have to come back they they may have the file but it's encrypted right and it's encrypted with private keys that they don't they may not necessarily have locally to them so what they do is they take that file and they send it to the
domain they they send a request to The Domain and they send a journal of it a journal of that file and the file gets verified that yes it is that file and the domain says this is what I have and oh yeah you are authenticated and I validate you and you have access to these different things because you're part of these roles or what whatever and then it takes the keys that it has and it un encrypts them with the private keys that it has in store then it re-encrypts them with your public key so now I have attribution right I now can see like and so then when you submit the file but you make your changes and you
submit it back I've got journaling right kind of seeing how this chain starts to go back around and how this use case starts to continue so I can't I don't have much time like I got like five minutes left so I can't really go into all of how that works so my goal is hopefully in showing you this is that it's it opens up a big you know opportunity to change the Paradigm in which we share information and do it in a free and open source way so some of the things that like so when your key gets compromised what what happens well who cares I revoke your key you have that data and uh and and maybe
they can you know unencrypt whoever has the files and has the private key can encrypt data to that specific private key right but theoretically there may be eight or n or 10 or 30 or 50,000 different private Keys encrypting different portions of that document so they'd have to work pretty hard to compromise a lot of them but also all I got to do is revoke the certificate because when they try to open the rest of it they got to go to The Domain to request it the domain says that certificate's bad I'm not going to allow you access to it anymore and the domain can make a decision does it want to destroy the data now that that private
key is done and totally trash it and delete that private key and everything that was ever encrypted with it die or do I want to take everything in my journal that was encrypted with that open it back up reencrypt it with a new private key and then destroy it make sense okay so now I've got either complete Data Destruction to the extent that I you know that they don't have all of the keys you know so you you get into this trust based thing right like now I have a means to establish trust in users like how many times have their keys been compromised how many times have they reported them and so forth um you know but it requires
compromising more than just an identity and that's really important because identity Facebook blah blah blah they get compromised all the time so what we're talking about here though is now we have limited data exposure so um again another kind of small slide what does some of these things provide asymmetric encryption provides as confidentiality man- in the- Middle protection so even if I man- in the middle list with SSL I'm not going to get anything because I have to have those keys as well and they're encrypted with public keys that have private keys that I have to compromise both private keys to get and da da da so I get Integrity one of the things that you we
do not have in our current stuff is non-repudiation I know exact who modified that file and what they did to it for example and with pki if you implement it in a certain way it requires online access control to do certificate revocation and to request those keys so metadata gives us tagging support for multiple Access Control mechanisms attribute based stuff and blah blah blah we get journaling which is you know obviously makes sense supports trust models you know I can actually see every machine that opened that file and if that file was in you know blah blah blah well okay so a compromised machine had that file stored on it for some period of time we're
private Keys ever on that on that machine that could have you know that could have exposed certain portions of data in that document you start anyways I'm getting a little bit out there maybe now for some of you um so then we have some stuff like how do we do search within encryption uh that's where you get into this machine based ontology like how do you search for in data inside encrypted files and things like that like that's a little bit beyond the scope of this but I'll talk about that later um some of the things that don't change with this key storage you have to protect the keys but we do provide what this type of
framework would provide is like a means to revoke them and limit exposure to data which you we don't have any means to control right now um and it gives us a trust and repute model some of the things that are a little bit not so practical with this are like you know I'm streaming uh uh you something or you know streaming video files okay I'm stream I'm streaming Yan cat you know to all of you right now um go to this website um you know so some of those types are a little bit impractical right because they're time sensitive or whatever so me encrypting every little thing is there but we actually solved that issue and that's a
whole other um patent uh but uh how to use public private keys and uh um onetime use SSL tokens and other things to exchange them but that will be open source too coming in the future um processing Network overhead um it might be a little bit you know more intensive right but theoretically it may be a hell of a lot less intensive because we're not encrypting at all these other layers and sending data back up and down and things like that so to be determined right um so attacking the framework yeah somebody's going to attack it the biggest thing that I get is like what happens if my policy decision Point what happens if my domain gets dossed or
whatever what happens when your domain gets Doss now thank you very much um the biggest thing that we saw and that we did not realize this uh in 20 you know last year was that uh and was patent trolls and and people coming in and theoretically trying to take something like I said we didn't really see this idea as patentable this is really a big what if um you know but then yeah there's some some real ways that this could be done you could attack rules on policy you can attack the the implementation of how you do it like poor policy implementation could definitely allow unauthorized use and things like that um you know you can
attack libraries you know but the idea is that if you open source the libraries and you make the you know make the process standard just like you know yeah open SSL got hacked right but why did open SSL get hacked it really wasn't op SSL that got hacked as much as it was like poor implementations in certain types of web servers that were using op SSL and the data was unencrypted when it got to the Apache server you know that's just an example um but of course race condition attacks like we have issues where like can I retrieve the file or retrieve a key so like if I steal a bunch of data and I get a private key
can I do it before you revoke it like how much data can I unencrypt before you revoke those keys and I'm no longer able to revoke them so those types of things still exist um I'm going to quote a line so uh um the best way to predict the future is to create it and that was kind of the model for this and just like um you know we are the calvary and some of the you know and irona and all those other ones like if we actually want to make this H this happen um pgp didn't create itself encryption didn't create itself uh we have to do something with it and so the we're not creating
anything new here you did not hear me Pitch some new technology of something this is just a means of using existing stuff to use it in a more constructive way that benefits somebody not a corporation making a ton of money and that's not to say that Ben that companies can't do this like I said we applied technology you know like there are process pipes there are things you as your company can Implement a a framework like this and still get paid to have the stuff in there um the idea of it is is that you can you know that we're providing a standard means to do this and and hopefully some people will will understand the value of it and
catch on some of the ways that we've tested this um I the my I'm not a developer and so my developers uh my developers are uh like for some reason they like Java and uh and I hate Java I call it unicorn poop um so you know some things like aimal and Geo aimal uh and what those are is these are XML formats like ways to format uh ex uh Geo information and other things for embedding and web pages and other stuff you know like so how do I create policy based off of those things so we want to use standards right so that we're not the ones saying that this is how it needs to be formatted and it's arbitrary
and you know no you use the standards that are out there uh and so what we did uh back in January January of this year we received a provisional patent protection so that I could come and show you these slides and come and show you this stuff for not having fear of somebody from some Corporation going out there and racing me to a condition to patent certain things and so um you know is this a complete deal is this a done deal no it's not it's still in development it started as an idea that literally I drew on a bathroom mirror um one day and I I kid you not um like there pictures of me and underwear
snapping pictures with the iPhone of like where I was drawing crazy things all over a mirror and uh and it was that was how the idea came to us and so the same thing is going to happen with you when you have that great crazy idea that you think that everybody I literally everybody that that saw it all they were like why are you in your underwear um like I was in my hotel room um why is there a beer on the thing well at least it wasn't Coke um so uh you know anyway I love that slide um this is how you can get in touch with me um the slides and some of the other stuff are
on pentest fail.com uh you'll also find like all the videos from this weekend I'll start tweeting them out once I start getting them done um so uh just like uh my buddy Iron geek he and I do a lot of conferences together and uh and so we'll start tweeting them out he usually reposts them as well so you can usually find him on iron geek and stuff as well but they'll be on a be on a YouTube page for um for bsides Charleston but that's how you can get in touch with you have questions on the framework or anything like that um I'll probably bore the living piss out of you um and and there's a lot of really cool stuff that
goes along with this framework but it is it is open source like the the slides for this the diagrams and other things are there um and uh and it's still vulnerable in the aspect that you know people could come in and steal stuff but I'm at the point now where I'm like well we have a base protection the more people that we tell about it the better if you're a cryptographer if you're a developer any of those things you know and you're interested in contributing some time or effort to the project we'd love to see we it's right now it's just me and a couple of guys that make unicorn poop so uh thank you very much
you