The Ladybird Book Of Quantum: Everything You Will Ever Need To Know
Show transcript [en]
take away fantastic thank you very much and welcome every than you with me the last person just talked about how um if you can explain something really complicated in really simple words um or if you can't do that then you don't know well enough and that feels like quite a lot of pressure to start this off with um so very briefly um I'm Frey um I my background is I did a PhD in um Quantum cryptography type stuff related stuff and then I realized I needed one of those you know job things and I spent a lot of time then in cyber security so um I worked at clarinet for a bit some of you will be familiar um as a
pentester um and then I went freelance and that was so that I could spend a bit of time building up and supporting um some of the research that I did on my PhD and turning that into a company um we just got investment for that actually yesterday it got signed off which is very exciting um but um because we weren't sure where that was going to be you know I'm here in my own capacity anything I say is you know views of my own that kind of thing um but but more on that later and so this is the lady book ladybird book of all things content and we are going to talk a little bit about I'm not going to
assume that you know anything so we'll do an introduction to cryptography we'll talk a little bit about quantum physics and how that relates to quantum computers um don't worry it's not going to be messy there's a good chance that you won't understand all of it but my goal is that if you come away from here knowing just a little bit more than you did when you walked in then that works for me um we're then going to talk about some of the problems that cause this for us and uh the kind of possible solutions to that as well so if you're all sitting comfortably then so craphy if you have two friends who want to send us a
message to each other and uh they want to do that in secret then they use cryptography and a sender can scramble up a message and the method that they use to do that is called a cipher and if the receiver knows what those steps are they can undo the steps to get the scrambled message uh into text that they can read read the original message and small variations in those steps make it harder for some else to work out so the exact combination of seeps you might use um is called the key effectively so um and the the whole process of scrambling the message that is encryption right some people get the words encryption and and key
distribution cryptography all kind of muddled up but they actually have specific meanings so this is an example of a cipher this is a Caesar Cipher you have the alphabet across the top and you want to scramble up the letters by shifting them by a number of spaces down the alphabet so this a is shifted down to D um so it's shifted three spaces along the alphabet so for this Caesar Cipher we are going to say that the key is shift by three it could be by one well could be by one it could be by 25 there's there's 26 25 different options you've got there and what you'd have is this C here would go to an f and the r would go
down to a u and so on and so forth cool okay so that is a Caesar Cipher the number of positions that you're shifting it along by is the key and if both friends are using the same key to scramble up their message and then unscramble the message your Cipher allows you to do that that is called symmetric cryptography um and there are some ciphers which use keys that are different they're public key and private key but they are related to each other and that is something called asymmetric cryptography we'll we'll talk about that later um and both friends have to agree what key and Cypher is they're going to use before sending those secret messages
um and distributing that key between the two people is key distribution so very briefly done a lot of a lot of big words here but cryptography is sending secret messages encryption is when you scramble up a message aes256 that's an example of um a cipher that's used to encrypt stuff um said Cipher key is kind of the the input that you put into that Cipher the the specific variation on steps that you use to scramble it up symmetric is when you use the same key on both sides an asymmetric is when you have different Keys usually public key and private key um but they are related fantastic there we go okay so now want this as a quantum computer it's
not because I used AI to try and generate some images this is actually a quantum computer um so actually it's massive it's you know about the size of a person but the actual bit that does the stuff is right at the very bottom here the rest of the stuff is just fibers for the lasers and stuff to keep it cool and and all kinds of other things like that and it solves new types of math problems and they are math problems that normal computers cannot Sol solve and it is very very big and it can only at the moment do very very simple tasks so think 1950 is computer size of the room and doesn't really do very much
you can do some maybe basic know multiplication if you're lucky um and it uses quantum physics so if you take anything away from this talk anything at all is that the word Quantum is often really really badly misused and all it really means is the smallest possible finite amount of stuff and it's it's misused all the time so this is apparently a Quantum of cake pan the smallest possible finite amount of cake pan and um I would guess that you could probably make one well not very well but with a lot of difficulty that's like a layer of atoms thick then it would probably be a Quant of cake pan um it would be wouldn't be very useful
to cook things in there this is a the smallest possible finite and we to dry um I'm not sure that's what the marketing people at sha were intending when they uh when they did this scientists make the smallest possible finite amount of leap towards a secure new kind of Internet that one's actually believable I think um and finally smallest possible fite amount of soft um what do you really want from your toilet paper Okay so so when we look at normal matter that's you know big it's very easy to guess what it it'll do if I have a ball and I throw it there are lots of uh equations that we can use to predict how that is
going to go where it's going to land we can we can predict that very very well but when we are looking at things that are the very smallest finite amount it's very very hard to figure out what it is they're going to do and they do some really strange things because it can't go small smaller than it already is so it can behave as though it's bouncing like a ball and Rippling like water at the same time it's bit of a weird concept to get your head around um and what we see really really depends on how we choose to look at it depends on our perspective and that is really really important so um let's imagine we've got
two quantums or Quant here uh and minute we're looking at them from like the top down perspective okay and we see them as two separate blobs but if we want to look at it from the other dimension and we spin those around very quickly all of a sudden as we are looking through we see both of them kind of superimposed of each other and that is something called superposition where they're both kind of um they're not necessarily operating as independent things uh anymore and they're doing some kind of weird stuff and and again this is all because we've changed our perspective so Quantum things as well like I said they're the smallest it can possibly get and that means that you
sometimes have related properties so if you imagine you got ball um and the ball you can't take any material away from it or add any material to it you can squash it and now as you squash it in One Direction this stuff has to go somewhere so it goes out in the other direction it's easy to think about it and in terms of physical dimensions um but it also uh applies to other kinds of related Dimensions as well so energy and time position and momentum and the better we try and get at measuring it in One Direction the more kind of floby and blurry it gets in the other dimension um and that is something called the uncertainty
principle um so if you look at it in that direction you can squish it down but it spreads out in the other way and if we were to then go right okay we'll Shu around and we'll look at it that way and then it spreads out in the opposite direction instead so um when we are looking at something in One Direction we can't really control what it's doing in the other one and with that we can only guess How likely it is to do certain things and we can do that by doing lots and lots and lots of experiments we take hundred of them and we see what the chances are that it does certain things
um and these properties are really really strange but we can harness them to do new and exciting things um so for example searching problems so when we're not looking at particular dimension of quantum object it actually tries to do all of the different things at once and it only decides what it's done when you look at it in that particular Dimension sounds a bit strange strange um and it's more likely to behave in the way that's easiest but it could do any of them so if I have a hundred things and I've let's say I've got 100 Balls they're all Quantum balls and I've swashed them all down I've measured them in that way and
I've not looked at them from the sideways Dimension not looked at them yet and then I choose one by one to look at them sideways Dimension some of them were look like squash to one side some of them squash to the other some of them will be in the middle and whichever one is the most energetically preferential the easiest one is the one that it's most likely to have done but some of them will have done all of them um so yeah if we do this just once it will pick one way at random but they will statistically add up to bring a pattern towards the end of it that shows the easiest uh the easiest position so
um we're looking at it down like that then we're looking at it at the side this way so it could be that both of them are quite close together or it could be the both of them are quite far apart some some of the times we'll measure this this one blob and uh it look like it's quite quite close together and sometimes it look like it's quite far apart and that will be governed by some probability so we can use this to our advantage if you imagine an object that is going through a maze as a Quantum object and if you're not looking at it it's going to try and go through all of the roots
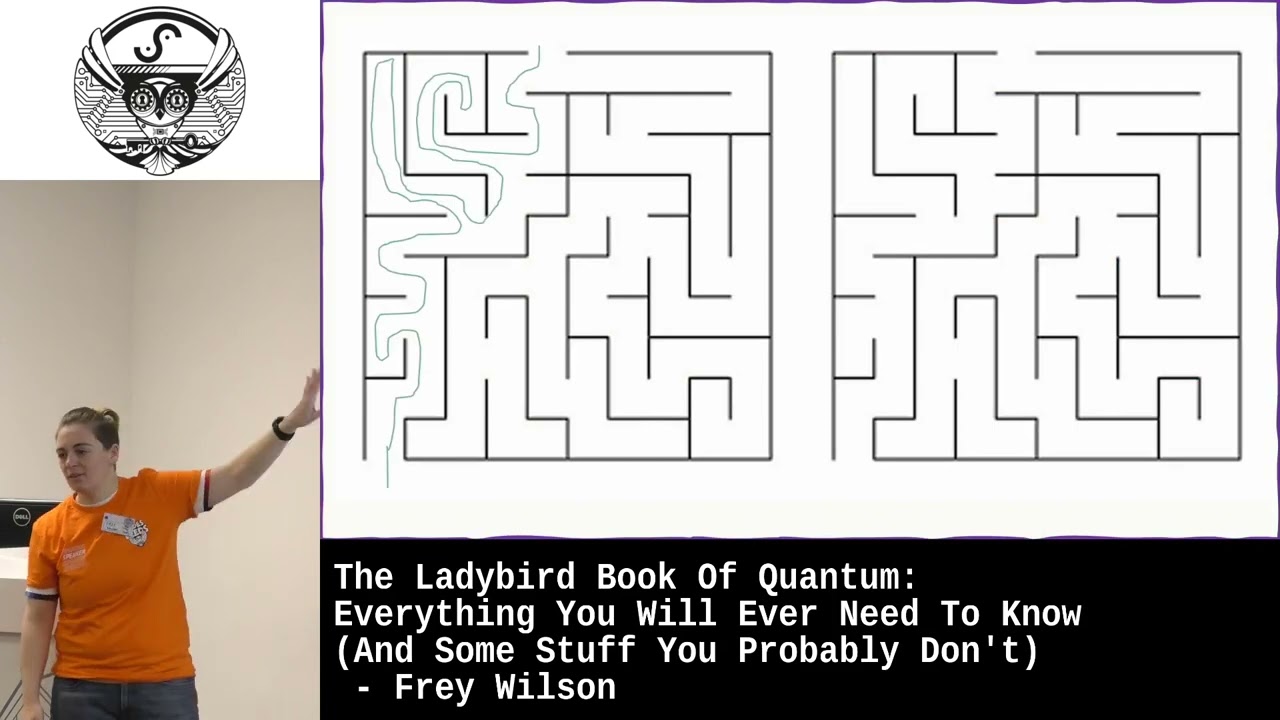
at once and if you can kind of you know suspend reality for a moment and imagine that you can measure it after it's been through the maze it'll show you if you do it lots of times over lots of them it'll show you that it goes through the easiest route the most often Okay so we've got two Maes here this one is a classical object please excuse my terrible struggles um and if you are a classical computer the only way you can solve this is try all of the different Roots yeah no it's not that one let's try let's go up here etc etc I didn't bother drawing in all the other all the others but you get the point and
eventually you're like okay no I know I know it's this way but if you've got a Quantum object you sound through that maze it'll go through all of the ones at once and then when you want to measure at the end it'll decide which route it went through and um if you do it with lots and lots of objects you can build up a position uh build up an understanding of which route was the easiest because that's the one that I've done most often so if you've got some Quantum siiz things then it's very easy to find the best route compared with normal classical computers and there are some Mass problems that look like this Con
searching problems some of them are very famous one of those particularly famous ones and and interesting ones for us is something called prime factorization basically you can take a mass problem and turn it into some kind of search of space you know we're searching to find the easiest route through this some of you might have heard of the traveling salesman problem that's another searching problem um even just a simple binary search actually you know it takes quite a long time to search through an entire database of stuff um so prime factorization then you think of a number and then you try and find the two or however many smallest possible numbers that multiply together to make that big number so if I give you
the number 21 have a think the two numbers that multiply to make 21 and they don't go any smaller because they don't multiply by any more things prime numbers are going to be three and seven you were probably able to do that in your head but for a normal computer they've got to try all basically all the different possible combinations they can they can simplify it a little bit but it's still quite the trick of and that means that if the number is very very big gets exponentially more difficult to do um so if I gave you the number 5105 that's probably very difficult to do but if I tell you one of those numbers is one 21 suddenly becomes a lot
easier and uh you can figure out that um the other number is five so we what we can do is we can kind of make this like a public key so I'm going to give you the big number but you can't figure out what my private key is my two small numbers are unless you already know what one of them are so my private key is a little bit like five and the 1021 I've greatly oversimplified this it's a lot more complex in practice um but basically the public key and the private key are linked together by a difficult Mass problem like that and the public key is kind of like the instructions for someone to encrypt the
message um and you can only undo it if you've got the private key um they can do other things as well with asymmetric cryptography do digital signing and that's where you guarantee set the message and you can also do symmetric key distribution so that is how we share our keys to do symmetric cryptography with something like a26 um and that is commonly an algorithm called ecdh elliptic per helment some of you are familiar with it um which is better asymmetric or symmetric well asymmetric methods that it's quite slow to do um but it's quite easy to kind of share the keys because you've just got public one share with everybody symmetric methods of encryption are are
very fast which is great but it's it's quite hard to get the keys to people in the first place so um there we have a problem and also we now have the problem that quantum computers not just yet but we're currently at quantum computers of the equivalent of normal computers in 50 60s um then those keys aren't going to be safe anymore and we need some ideas so they're usually one of two different things you can find a new hard to solve Mass problem um which is an asymmetric method or we can use the weirdness of quantum physics that gave us that before to uh try and find another way to share information and that's kind of a new
approach and that makes aetric keys so let's look at the math problem one then um this approach is called postquantum cryptography or pqc and it's the one that you probably heard most about in the news I would imagine and lots of the math problems that these people have come up with are very very difficult to set up they need computers that have quite a lot of memory um the keys are sometimes enormous um on the order of um like a gigabit gigabyte and um they need computers with lots of processing power as well to be form formulate those as well um that the gigabit isn't isn't true for all um types of key generation in this sense but it is for some of them
um it's also very very difficult to prove that they are secure especially secure against quantum computers because if you can um change the problem into a search problem then it might be something that can be solved um so it kind of means that can I break at any time just don't really know um n in the USA they ran a competition to find the best one and they were only able to find one that they thought might work it's called Kiva um they they've recommended it but tentatively um there was um about a couple of months ago there's a that came out by a guy called yelli Chen and uh he basically was like I've been able
to WR K with a Quant computer and everybody pic it was absolute chaos in you know all of the forums you can imagine all of the um stress and excitement about it um it turns out there was a bug in the code but and so it didn't work it wasn't a a real Attack um but it just demonstrates the the actual the fragility of this really it's based on lates um I don't have loads of time so I'll be very quick with this and if I lose any of you I'm sorry um but we'll come back later um so a Lattis basically you've got a starting point and you've got a number of points kind
of on some axes a little bit like you know graphs um and they're described by some vectors and then each point is kind of described by some number of vectors um so I've actually got this one this is 4 a so one two three four along and two points up so far so good um but you can make that a little bit more complicated so those vectors that you use or necessarily they don't just have to be the shortest possible ones they could be kind of long or they could be really really really long go all the way up and all the way along um and then that same point is described in a different
way um which is all well and good and then you can use that to formulate these really difficult problems so there's lots of different problems this one you get given a starting point you get given a point on that on that lattice that has some combination of of vectors you don't know what those vectors look like um and then you get given a random point you have to figure out which one of these dots is closest to that random point you can look at that and be like oh yeah I'm pretty sure it's that one but you don't have a lce so now what are you going to do and this becomes really really difficult when you have your L is in
multile Dimensions so it's going out the page AG it's also got you know another 50 or so other dimensions as well so another alternative that we have to finding a new high to solv mass problem um is using quantum physics and we can use weird Quantum effects to share secret Keys um and that's called Quantum key distribusion again something they might have heard of it's usually done in there's two different ways to do it I'm going to describe them briefly um but one of those ways uses entanglement um so that is when you've got a pair of quantum particles like the ones we saw earlier that if they have been linked together by by some way so
maybe you're looking at those two particles through one particular Dimension you then link them together and that means if one if you give those particles each one to a different person um if one person changes their Quantum the other one also has to change in response so what do I mean by that so we got this image again again we're looking at it through that that Dimension into the page um so the person that has a yellow one squashes it down then the other ones got to squat down in response as well because this has a finite amount of stuff which kind of means that it's all got to act in the same place um I
don't have a lot of time so I'm going to speak very quickly um is very difficult to detect uh when someone is using this which makes it very difficult for someone to break in um um which is good and bad uh it means that it's a lot more secure but it's very easy to just stop it from working it's basically very easy dos um there are some other systems that use the uncertainty principle um I am actually going to skip this very briefly because I don't have a lot of time um but basically you you squash it in one way or the other way and then you encode some ones and zeros and then you send it
over to the other person and they randomly choose are they going to measure it that way or that way um and if they are the same then they get the number out at the end which is great if they choose different dimensions then this now has to decide which way it's going to be and it'll be a zero or be in coded that way 50% of the time and that way the other 50% of the time and um they can have a discussion with each other afterwards and say which way did we measure it and they can get rid of all of these ones when they realiz that they didn't measure it in the same
way so it's quite secure do using Quantum key distribution still possible for a third person or you to come along and destroy it um it's also really really difficult to make these things so they only really work in special conditions short distances that kind of thing so we're very unlikely to use them in practice um so what are we going to do because because these are so difficult to make the goal really for a lot of people is to take kaiber and roll it out into as many things as possible um but there are obviously lots of people who are very worried it's actually not all that secure and it might be better it might
not even be better than what we have already um so lots of people are recommending hybrid so you roll this out in conjunction with the existing cryptography so that you kind of have a backup there if you like so that the two methods are used together ideally we have better solution um so I said that I spent some time doing research I'm going to talk about this again very briefly because I don't have a lot of time um but we came up with an alternative to that and it's nearly Quantum key distribution so it's kind of the same stuff as key Quantum key distribution but without any of the physical hardware and it's using that
probability theory side of it and not of the actual quantum physics so we can replicate that probability theory in a purely software based method and we didn't really understand why it worked until very very recently but it's a way of doing symmetric key um and uh I think I've got a few minutes so I I will go through it so basically you have one person they start off with a lot of random numbers so this person Alice they flipped a coin got 50/50 heads and tails and then what she's going to do bit weird she's not going to tell anybody she's going to make some deliberate mistakes in those numbers so uh she flipped some of these coins here
she's not going to tell anybody where she's done that um but she's going to keep that quiet and we've we've kept it red here so that uh you can see which ones were the ones that she flipped she sends that over publicly to uh Bob he goes okay thank you very much and he also makes some deliberate mistakes at random he's also not going to tell anybody where he's done his mistakes and in some places that's just he's just introduced a new mistake and in other places Alice still has her mistakes there are some places Alice has made a mistake and then Bob has undone it again and he has a head here and she has a head here but
publicly all you could see was a tail and nobody else that's seeing this communication has any idea where those mistakes been made and so what you've got here is purely by probability you've introduced some completely secret numbers um there's another set that you need to do so we'll have some mistakes are still left in there um and so what we can do is we can break those numbers up into blocks so the example I've used here is two and then we can share some kind of summary information that doesn't disclose the specifics of what's in there but just a summary so for example the par that's you know is it an even number of heads
or an odd number of heads and if they have the same parity they can go there's really good chance we've got a match here um and we we definitely made a mistake if it's the wrong par so we'll get rid of those ones they have to repeat this process a few times um because you have some like this first example here where it's just they just managed just by chance to to make two mistakes um but so you have to repeat it a few times what you what you end up with um is a list of completely matching keys and as long as you've got some of those purple ones in there um that were kind of a mistake
that Alice made and then Bob and did it and then you've got some secrety final thing to do is perform a hash you don't know what a hash is basically you kind of multiply every number in here by every other number in there which means that you need to know all of the numbers to be able to figure out what that end bit is there so that secrecy is kind of distributed along that number so know they have some matching Keys which is great so this might be the next step towards a Quantum safe world we certainly hope so this is what AI thinks that is going to look like um if any of you are developers um or if any of you
are particularly Massy and kind of interested in knowing more how this works come and speak to me um because we are um since we got investment yesterday now looking to do our um like more stuff with this so if anyone's interested in kind of testing that out let me know and just to summarize we started off at the start understanding a little bit about costom stuff um and traditional cryptography um then we learn a little bit about Quantum which is the smallest finite amount stuff possible we showed how you can use that to solve new Mass problems with the computer including Prim factorization um which breaks existing cryptography um so we talked about how people have come up with new Mass
problems uh such as um well such as the ltis problems to create postquantum cryptography um and we heard about how n have put on a competition for that and how kyber is the current leader um and we've also talked about Quantum key distribution which is another method of doing that it's just very difficult to do uh and finally um a potential new alternative to that as well so thank you all very very much





