Chris Dorman - Open Source and Leaked Malware
Show transcript [en]
so my name is Chris I'm going to talk about open-source malware and leak malware really it's a really generic title and lets me talk about a couple of different malware stories it's the first one yeah anybody recognize this video clip you can follow Club me if you want it as well no what's that this is a Ukrainian TV station is about the Christmas 2015 attacks so there are a bunch of power stations near Kiev they were attacked people lost power about quarter of a million people on Christmas Eve so that was pretty bad the way they did it this is a video of the attackers interacting with some scarlet consoles so someone working on the substation has recorded
this on their iPhone and they can see them manually flicking through the console and then turning off top of the circuit breakers so that was the manual part but saying up the attack they use a few different tools and the reason I'm talking about those attackers because some of us open-source is part of a growing trend so had some custom stuff us published something on the year before this attack saying they had a exploit for general educator consoles there's also something else where they invent exploiting my office too so I cite who call these guys sound wear and poppers and stuff about them particular to this attack I use black energy which the malware these guys are really known
for some people call me on them after that like ng itself is the interesting piece of malware a while ago you could buy some earlier versions it was shared amongst a few people these guys customized it which is kind of stuff that they built themselves kind of stuff that they also to support commercially I suppose be cool team doing RDP guess not really commercial malware better something along those lines what's really nice either these guys are really big fans of open source particularly recently so they've got some nice stuff where them do TCP over HTTP I'm sure those your pen test but we recognize most these tools got some pretty good web shells its Lister off github another SSH backdoor
nice to let your on on side drives on Windows so whenever they need something just go and lift it off because they can't build everything they just haven't got that much time and they user as as they go through and it is part of the growing trends as a talker Kaspersky SAS this year on some other groups they've been using some open source malware sometimes in place of things have really built themselves because the open source stuff is better and doing more effective attacks that way so after they did these attacks and people have lost their power on Christmas Eve people start to notice there on their networks turns out that you take out the power for the last
public country people notice and but they came back to regain access and those networks as a post by ESET looking at some their new Maur in this point rather than using black energy which is something they've been using for years going back for ages they're now using gcapp which is really nice little tool straight off github and they just use it in place they kept using the same macro in stores they're using for so people could tie it to the same guys but now they're using something just straight off of github and the guy that wrote this on get happy notice as well they were using this tool he was a little bit upset about it understandably he didn't
really want responsible for this kind of stuff and it's Fe not his fault but someone have used that but if you put something out there obviously you can't control who's gonna be using it if this is a really extreme case of when that happens and extreme cases make really bad rules this is some idiot who at some point things is our Qaeda other point things is Isis and he posts all these YouTube and Facebook videos but how you can use these open-source tools a hack into people and YouTube and Facebook take down this video straight away within a couple of hours into the archives still hosting them after couple of years so again the information is still out there it's all
about like a proliferation of ideas and all this stuff so fast forward one year later this is a another bit of research this one was by ESA again and they found the same attackers coming back this time into financial networks in Ukraine but rather than using gee cat that gmail backed all they had I said they're using something probably inspired by it now it's using telegram for command to control but otherwise it's very much like the stuff on that Gmail it also upgraded to so some of those open source tools they're using before the previous year they replaced their own so the one on the on the left there that's actually how they're doing G's to be a base to be now
upgraded that killed his software to two had one thing that would absolutely destroy all the machines on the network made it hard to recover may the trends a bit more tricky as well there in these initial attacks cover the power quite quickly and then this is another talk with one of those scary pits of the anonymous masks in there looking very terrifying they came back a year later less successful that time and then more recently yeah that worked well recently there's been a lot talk about pet sure or not Petra ex-pet sure and who that might be linked to I haven't seen anything solid there a couple of people saying that maybe it's linked to these guys Sam them again
maybe here Ukraine plus destructive often is these people I don't know but that tour was an interesting mix of definitely sourced malware so in there there's some open source stuff at the mini cats which was pretty successful about hoping the spread around networks then there's a stole and exploits return on blue which is everywhere these days there's some source code taken from the original patio - and the author of that mal I wasn't sure just where that come from whether it's store and all been sold on that kind of thing I know they've written some that code themselves - so pets kind of interesting example of how he can bind all that different things together something bad
can happen this slide doesn't really have much reference to this talk but in an earlier version for I hope I deleted it this morning has taken up too much time as there's a group of wynn NCI quite a messy group of armed hackers loosely tied together they use a lot of open source tools recently the news github from our control and they use some of the open source tools for command control to get up so it's kind of a meta open source thing going on there is a post by Trend Micro and one of their developers it turns out is a part-time pig farmer and in a day he farms picks in the evening he writes
malware and this is his profile picture and the reason it's in this talk is cuz it just makes you wonder what's going on because I mean the pigs in his bed and I know it's not very nice to post pictures about developers personal lives but in the case of this one oh it's funny enough to justify it samurai another one that Evan will have heard of Internet of Things botnet web cam is that kind of stuff and use of DDoS people the guy that wrote this to prove how bad and powerful his botnet was he hid prying Brian crepes and it's quite an impressive feat to master crabs off of his DDoS control servers after that enforcement rostrum what's
surfing there police and stuff for interest in he was his response he polished the code on to hack forums so anyone can use it all the scripts then run it I'm sure you've all seen it now there are tons of my partners out there so particularly shortly after Mirai everyone seemed to have the roamer ID bottner you weren't great if you didn't have your own one and lots of people were affected there's even an improved version someone later did with Symantec wrote up which went around patching some of the flaws and the I just letting people know about the issues with Mariah in that case it was a full rewrite based on that knew what they were doing when the first
people don't to do that anyone remember my doom yeah I didn't actually remember I was looking into a couple days ago back in 2004 at one point worm functionality of a zit worm where is responsible about 10% of email traffic in the world which is crazy was a really successful damaging worm going back to Martin from Taos has taught this morning about worms and how they've been changing now back in the 2001 was a pretty common this is one of the worst ones it was ddosing ska Linux if you remember that and also Microsoft so they offered a quarter million bucks to anyone who's willing to adopt this guy in and tell them who it was so Microsoft a pretty
good at chasing people down probably because of that the author gave it away and then they got the heat off his back at that point then it was a hardest fight it was cuz then again all the script kiddies were writing their own girls am i doing living somewhere and still going today yeah this this one if anyone here is a fan of a fixed win I found out this week that he wrote a track about my doom called W 32 but dot my doom it's not one is best it's from the album and the Lord I think that's how you pronounce it don't try that one might be something like that and there's some other tracks there too so BBS
that's something and if you'd like your music a bit more generic PW stealer as well my favorites see hidden tear it's a really well-known piece around somewhere I look at me talking about because it's seen so often it's not that great it's just a couple hundred lines of visual basic and a guy could good cou I think I'm pronouncing his name right he's from Turkey he released a couple years ago when he was at university he said the reason was to educate people about how ransom I work so they could learn to better defend it I think most people know how ransomware works but fair enough maybe he just did it to get his name out
there he want to get into the industry yeah that's that's what lager Purdue has a sense of humor this is the ransomware message which comes with it you down that's true github and you've run it this is what you get he says that he likes the Babs yeah he likes Cobalt it doesn't like being drunk and please send them some bitcoins say you know and if we don't encrypt files and stir and folding our desktop there's only one line change of code then to make encryption hold disk but by default do I do that there's got a lot of attention on reddit there was a thread talking about it they picked up on some crypto fails in there there a
lot I'm not really equipped oh guy so I didn't understand looks today one of the most obvious ones though is that the run key generation there please encrypt the files it's based on environment account so in that system time 32-bit integer potentially some issues there someone else suggested to you that maybe to add a back door into hiddens here so it gets a it was fast back he declined the suggestion on the on the repository on github but it's a good idea and of course in take long but always being seen in the wild so this is from a website in Paraguay I think it's some local utility some like that you download some form off there you get
this malware as one the first ones be running in here and then Trend Micro ever a post on there saying good idea you know just give it away let's what's ransomware here's what it's dangerous people being affected okuu he was called the Turkish security group OpCo which is spending his name wrong I'm said you know what maybe I can help out here let me know what the file is and we can see what they do I did actually decrypt it so the people who read it had a pretty good idea he followed their advice and he brute forces they're the key so for one thing system time 32-bit integer 2 billion maybe values my maths not great but I
think my kyria that's where it was and also you know that at the time the interest starts as well because you look for the first files on the disk and then that gives you kind of a hint and they just brute force as either side and here you can see I think they're about 40,000 guesses before you got it right and this idea was actually taken from BitDefender who did this with Linux encoder malware which had a similar kind of issue there but in the case of BitDefender so in the case of linux encoded a bit the vendor didn't write the malware it encrypts the your disk three four times it goes to continuously because really badly room
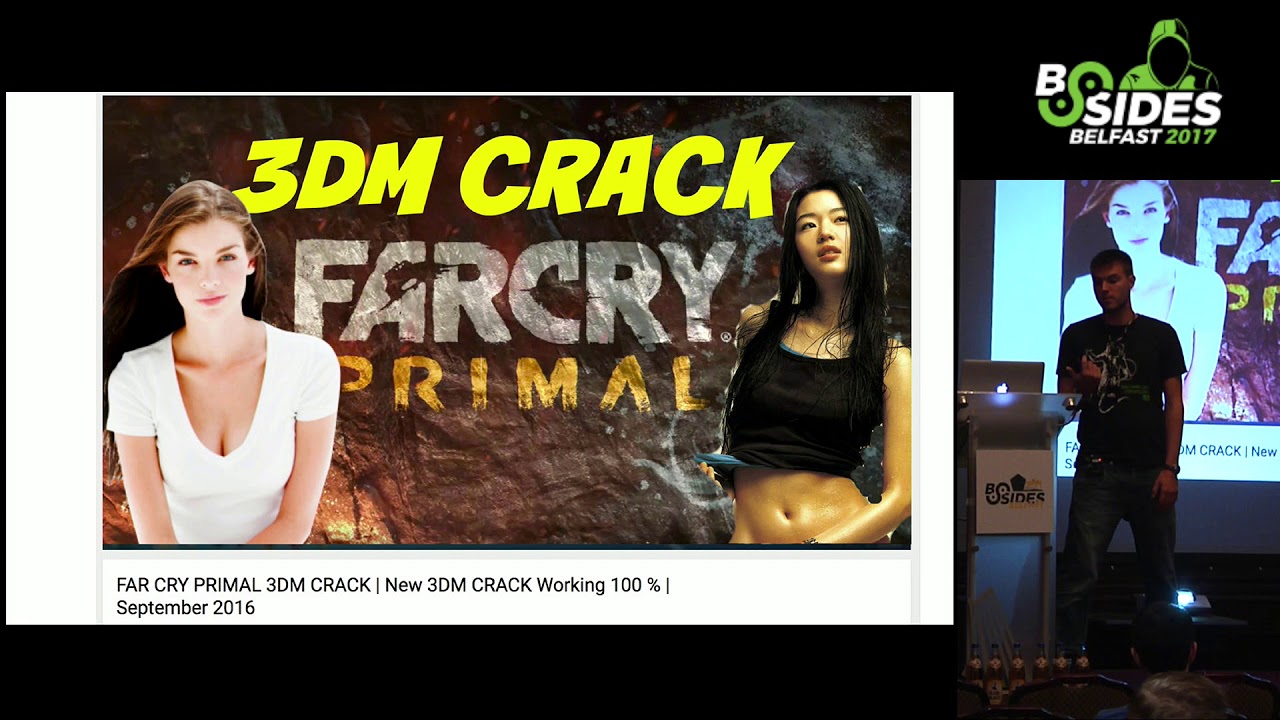
so you don't get your far as black and if you pay so after these crypto files though he did decide to improve it which is maybe a bad idea this time he named it EDA in an article he said there's after girl that he liked he wants to impress her it's kind of sweet I'm not sure it worked and it did fix a lot of those issues so this is one the first times it was seen let's say that you want to play Far Cry it does look like a pretty cool game there with the antlers and stuff but it's 40 pound on Steam it's quite a lot of money so obviously you can a Google for a crack
listen when the first results in Google still a YouTube video it's a meteor the download we see where's it going your downloads far cry and you get this you go yeah you don't get far cry you just get this our message off it just been encrypted that sucks and this is either too and the brats note is pretty annoying it's it's one the worst ransom notes have seen actually they're never paired to find me I've been doing this for five years Best Buy can do the encryption the NSA car do the encryption equates BestBuy with NSA in terms of abilities there so you know he's always talking about but at this point okuu had actually taken to
his advice and he had added the back to all this time so probably violating the CMA he could log into the c2 of EDA and then he could get back with the keys and he got the rule methought about this did work the handle the keys gave it away and you know I guess school won for him at that point after that though the problem with your Kody being out there is anyone could Fork and I'm gonna prove it and someone did do that someone improved either - and removed even more of those crypto files in there they said their motivation for this one to help law enforcement understand what script kiddies and some grants and words work
like so he actually missed though that the author of this Fork missed the back door laughter miss attention someone suggested - you're on github - remover and he did so the back door was now gone from Dalek as well so let's say you want to play Minecraft again great game but you don't pay for minecraft you download this back doored copy and you get this I think this is laughing my ass off at use not somewhere something like that what's right for now it's it so yeah it's a stoic you can't get your files back it's not that I'm the world after this was seeing the wild I guess the author maybe had a change of heart they took it down
and github so he can't download it from that posture anymore when I was looking into this looking at the author turns out he's a 13 year old kid from India so I thought a bit more bad for the guy now at this point I mean it's not a very smart thing to do maybe birth the kids maybe not right ransom whether talking with this kid in Japan four months ago he did write some around somewhere as a demonstration shared the code was never seen the wild somewhere and he got a knock on the door from the police and to me the end actually but certainly the some countries right even demonstrate some ransomware it's pretty serious
here's the last one I think another either two variants yeah quite boring you know at this time though but what happened this time though was that the web poster pretty good after they were told that there is this ransomware being using their stuff as a c2 they took down the command control server and that meant that that's who could not login any more and download those keys so he just couldn't get those files back even though this still had the backdoor in it so that sucks and the people started posting on leaky computer which is a good forum if you ever get your stuff encrypted and they're asking for help that kind of thing the ransomware guy
delivering their stuff took pity on some people he said you know what I can actually get your files back I made a backup of the keys before this all went down we had the condition and that was the coup had to actually sent him three Bitcoin he didn't like the guy apparently and he also had to take down inter and either to you from github so those are the conditions and after a bit of mediating and unaggressive back and forth on the forum he did that and now they are gone so the repositories pleased to no longer on but if he was going to commit history you can still get it of course did believe that the
commit history and the other thing again about your Co being out there as much as out that everybody is out there so there are tons of folks of either to an intel on github all still available there are some improved versions up there as well so someone rewrote it in c++ for some reason if you can no code that I'm sure you can probably write your own rants when it's better than that Phoebe stop it yeah yeah lots of different versions and it's being seen the wild a lot now so this is actually a real problem it's not just some time out where these are some of them my personal favorite is Santa Claus smoking a joint after you've
been encrypted yeah some more wands loads of them this pull off Twitter these screenshots and mostly from other people if he believed me computer so cred to them this one I was told Hut yeah I really wanted to believe this one was real but as Tolbert has actually made as a joke by somewhere and if it's real or not I checked him the phone number and it has been seen some real tech support scams but yeah it's the Microsoft Windows support its use virus yeah that's phone number no longer works but I found a later version which had this phone number and that number does work wanna give him a call they even get there the last speaker to try talking to
them this one looks [ __ ] Philips Louise the Harry Potter theme tune this is quite eerie this one just deletes all your files so going back to kill this type malware in some of the destructive rants much attacks this is kind of a bad version about just deletes everything this one might look familiar guess what this is trying to look like want to cry yeah some person ain't want to cry I guess they thought they'd get my money that way this one was kind of a joke someone you might see in a couple articles talking about this one this makes you play this very obscure anime game to an extremely high level and checks the memory to make sure you've
got the score which takes hours and hours I'm told and then you get your files back getting really bit of this game and then let me get it back yeah but the author of this felt bad so they released a patch which will ask you patch memory to make it seem like you've got that score and they apologized it but this is all based on hidden tear that's why I'm showing these these aren't just around the bits around to win this one lets you give just gives you the key straight away they claimed his educational these were all been seen the while them well the scene on Vice total so either researchers or maybe in
the world this one has scares me sing a few of this one so this is ransomware as a service using hidden tear so this guy would charge you $200 and he'll set up the hidden test server for you and he'll even help you distribute that malware too so he's taking this open source stuff and now he's making cash off of it he seems a little bit up there and says of how much ransom has come from hidden tear these days this is really nice draft by f-secure not of hidden tear but does it all ransom error overall this show there's a big group of families I went through tagging which ones a hidden tab they got quite boring but it was about
10% when I was going through better numbers by Trend Micro that shot up now there is this big scene more I'd say it's pretty easy to fork I mean know we could do is download the code of get up change the desktop and then you're there so but I used to write hacking Strauses teenager I used to put on their education use only that kind of thing I'm not sure it really has any value but it made me feel better um but we put that on hidden to I said for educational use only if you're doing that I guess you know you doing something little sketchy bit there you go apparently open-source license explicitly does not work the GPL does
not let you dictate the usage of your software I'm not an open-source lawyer but I saw someone else say that they're talking about suing me I saw something else on that baton ah and they said that that does not apply so that on arms control and cyber control stuff doesn't control the open source I have some explicit count clauses so I guess be looking the legal side of how you can destroy open source stuff that might be relevant in the finally on hidden tear to sack Pro best-known known as a malware textmate he posted this on github asking do you think open-source ransomware was a good useful thing or not I don't know for me I'm not really
sure I think that github probably can't blame them for hosting it but at the same time somebody great idea to publish it so these slides look I'm really horrible so I apologize in advance if it hurts your eyes but every good tool has a couple graphs in this is a very lightweight graph so just in the context of this talk and the next section you could describe malware and where people are getting it from as maybe being bespoke stuff you write yourself so maybe you write a little visual basic thing there's downloads and execute something it takes you like ten minutes you're right maybe right Stuxnet here you know I spend a hundred million dollars building your own proper
platform good commercial stuff generally the more you pay the more you get so you can buy a copy of the Blackshades rat to spy on your ex-girlfriend for the dollars the FBI might knock your door that point you can go up to strike if you're a professional pen tester I haven't got that background but I hear it costs a few grand maybe look at what's right going up to hacking team what kind of government Grady but still off-the-shelf maybe six seven figures to buy some how about open source lovers the playing field you can get some but there's tons of open source stuff out there obviously and it's great it really helps people do with their jobs you can get some things
like H worm was a bit destructive because they are a worm it's a pretty rubbish piece of vbscript commercializing it's quite successful boat through the Metasploit this is obviously a very useful very powerful platform and you get a lot for nothing the stuff that really worries me though is the leaf malware so there's commercially leaked stuff like there's you spanking malware that sauce copies leak that's seeing tons of vacuum hour these days car burp not a piece of banking malware and then there's a Shadow Broker stuff this has been done to death so I won't go into too much but when you have those kind of government grade exploits basically really expensive stuff going out there that's
when you start to get real problems because it drops from being up there in terms of cost and being there every suddenly then that's are things that one the cry can happen s once the next bit leaked source codes kind of complementing that open source stuff shudder brokers was the most famous phone I think there's some more coming out today everyone knows about that stuff what I found interesting was when they were first copy to over under github it's a bit easy to access github took it down and it wasn't because there's all that matter on there and all that that stuff is because they including the auction message from the shadow brokers and they're asking for
Bitcoin donations and you're not allowed to solicit for donations on github that just one of their no no rules fair enough York's not allowed to put compiled malware on there as well that's not okay you can put scripts on they for the source code and then that becomes a problem when you start to see people I've definitely seen it on networks people just downloading in both nominee me cats the PowerShell version straight off of github in the one-liner and I'm running and then we trying to investigate an intrusion like that from a network level without termination just see encrypted connection to get out and then some and [ __ ] happens so that's quite quite dangerous
Vic got kind of a tough job to do and wanna cry they've been a couple of talks and one cry to death or they're both very good one third are Martin from it was Martin from Tallis yeah spoke about he was talking about how they use the the actual exploit of the eternal explain kind of which they used there's a great person that be analyzing which particular form of export they use it wasn't until about a month after it was initially released that wanna cry happens there was two days after someone released more prepackaged version of the exploit onto github in two days after that one the crackers we used it in and at that point it used to use then just
after that the Metasploit and we never something's a Metasploit that's when you start to see it used in the wild so the Apache struts exploit right now that's just been a mess boy it's gonna start being seen everywhere and that's that's how these things go obviously most people can't be bothered to work out how to do their own explore but once it's easy to use it's gonna get used yeah and they make the comment - they didn't understand how the exploit workers of course they just walked in there hacking team pretty famous before we had to mock their asthma is quite Spenser commercial-grade things they do some interesting stuff they sell to do things like counterterrorism which I
think most good things quite important be able to sell some countries to hack into journalist and people that just disagree the government so some people talking didn't like that and then hack into them it's quite a famous story obviously and all this stuff is not open available including github if you want to download all that stuff didn't take long before the exploits is worth some the other tools who from hacking team we've been seeing the wild what's interesting in terms of again how these kind of Tours I mean distributed these look a lot of Chinese groups there seems to be a district quartermaster that's a free is buying them around Facebook and shadows server but there's one central
entity which all sometimes bill with their own tools sometimes repackage exploits like the the hacking team exports and then share them out to other groups again that's just one way this kind of malware and exploits get proliferated in that case it's a bit more organized they they really help those guys out it's a bit more on leaks stuff but this time what commercial great things so see you some car burp I think everyone's heard of these suits again very famous piece of banking our car burp that was really successful while they made tens of millions of dollars hacking into banks this video another one for my personal collection you see I I spend a lot of time looking at Russian news
websites and things you can't see what's going on yeah yeah don't worry he's laughing in him and I know that looks harsh but he's live from the police in a second it's not quite so bad there's other stuff he had so this is what happens when you are based out of Russia and you start hacking into banks in Russia this guy with one who leaves the carpet he and his brother were leading this gang they were making millions of dollars not just our Russian back to the lots of other places too he was employing people remotely so you'd be paid a cup of brown maybe to write a web inject for Berkeley he's got the grounds
right one for NatWest and then they all pulled it together so carpet was a pretty nice piece of kit it was a very professional Thank You Georgian until he got arrested it was nearly chopped up there what happened booked the car Burt and also burns use was that not long after the author's were arrested the source code first became available on performance and maybe ten twenty thousand dollars and quite quickly descended down to five hundred and then on get hovering everywhere else so now anyone can use all these bits and it is seen in lots of different places it's a couple the more interesting uses the car box car buff source code is that safa
key probably best in this fancy power apt twenty eight they've been in there use a lot recently did some stuff with the US elections they use a bit of car birth you use a bit of everything they also use some a Metasploit to because even though they're very well funded organization why wouldn't they they're also there the the the topic avert or Kaspersky SAS which went specifically into their use of open source software so I won't go into that but one of the interesting things that they raised was that they have their annexed work here they use it deliver malware we've had it for some time in some instances they just use beef instead spend this time building up all
this stuff feels like use open source and maybe it's to make attribution more difficult maybe it's just better maybe some of the guys down sharing amongst the teams I know also vault seven allegedly CIA that includes it's showing that even they use car Bert for one thing and in their own user manual they made their know that all components were carefully analyzed with back doors and vulnerabilities obviously it's too much be pretty careful if he's using this code I know a lot of people in proper for long bread bread teams are apt simulations are using real live malware if you have to do a lot of testing to make sure you know what's going on in there does make it more
realistic test them and then going on to this kind of proliferation of all the different bits of Mao and how it's all coming together it's really crazy to think about how a lot of the Shadow Broker stuff was allegedly from the US government in the context of there was looking at some of those two words and the notes around it a lot of them we've probably made to attack Iran's nuclear program and then they're probably leaked by another country and then looking at one the cry there's some pretty good evidence by Symantec and others that might be linked to North Korea to fund their nuclear program and I won't go into it because attribution isn't
something about go into here not knowing any detail what should I be happy with but it's just matter than the stuff built for the Iranian nuclear program to stop it there's may be inadvertently funding a little bit North Korean one yeah but he does happen to everyone so fancy bare sake those guys is talking about mini Co using car birth and lots of other stuff there left one of their servers open muscle F two servers open and their back-end source code one of their pieces of malware was then just open to the world and our researchers have a hold of it another company even has the other client side of this to to build the
malware to interact with this server side so that means that these guys that are very well known group some people have some of their malware if they wanted to redeploy themselves not let this guy who some of you may know jeffrey car to say that based on that fact that some people have controlled their malware you can no longer say with any certainty he was using their malware and based on that he was saying that russia and though we linked to the u.s. election hacks he also says that it stocks neighbors china and apt one were so interesting guy while he will be talking next with a very dramatic Twitter picture there I think he's just
having a little sleep in the bar right now he did a really good talk but be very careful talking about attribution though so whilst just because atolls open source doesn't mean that you have no idea who's using it at the same time a lot of people you screw with you and know this doesn't mean that you never be sure sometimes it's nice to end them a slightly more positive note about all these kind of things is there an upside to the fact that people were using this malware stuffs getting leaked there a couple of things for one thing there's you spanking malware that is used in pretty much all banking Trojans or at least the cheap
ones it's pretty easy the text on some of the basic versions you can pick up some new text or some of that kind of thing that AV detection is very good so that's why malware authors appetize that them is not based on Zeus if they're selling banking stuff because everybody decreases the value so leech coding that's like less value advances is out and everyone can see it now the interesting thing was right after the car burp code got leaked xylitol took a look at the PHP server server side code of it and even though this was fairly prescient about that between lots of looking people a lot of money in the development of Carlberg there's some exploits in there so he
just logged in to a couple of their CT servers started pulling data off their she's pretty crazy so there were some of the victims and quite organized crime group and wants something is open-source it does make it easy to find some these backdoors and again there was a another talk I saw recently on someone looking at open source malware and finally it used to find back towards their there's obviously the whole separate conversation about whether that sort is more secure or not but that's another thing and then finally I put this on Twitter yesterday it's nice to actually share some kind of code some kind of something useful when you do a talk so I
polished this off to get it working for this talk and if you google yabin which is a conflation of yarra the are being the tool to find our samples and binary being a binary this thing all this does is quite a simple dirty Python script if you give a compiled piece of malware software it'll look for courage we use our right overall to try and find related malware so that it does that you can look at the code that how it works only work for some circumstances it looks at the function prologues some compilers often have the same kind of stack set up that kind of thing so you can see where these functions begin this looks at the start
of it there really there are better more complex ways of doing this but this is one way of doing it I ran this these two for a group called Lazarus quite low name for Sony stuff how's it going I showed the photo view a minute ago I think you missed it that's for the best yes then you some open source stuff and then using this tool I ran it I could find related malware based on the original open source things are doing or some other stuff in there so I found a nice old Lazarus worm which is quite nice dating back a few years doing S&B brute-forcing given these guys are supposed to be also behind want to cry
interested find all their worms another one I was looking at it looks for its specs a couple piece of software been y'all just saw on the system it checks if they're there or not and looking at that software it sparked the North Koreans down the build so that's just an interesting thing that why this worm I'm looking for a North Korean software pippers machines I haven't probably looked it yet so I don't know why but we interests me find out so yeah this is a tool to find related malware check it out see I faxed a bunch of people for screenshots that I just stole I tried to credit them but didn't always fit so there you go and
that's it if there are any questions from anyone





