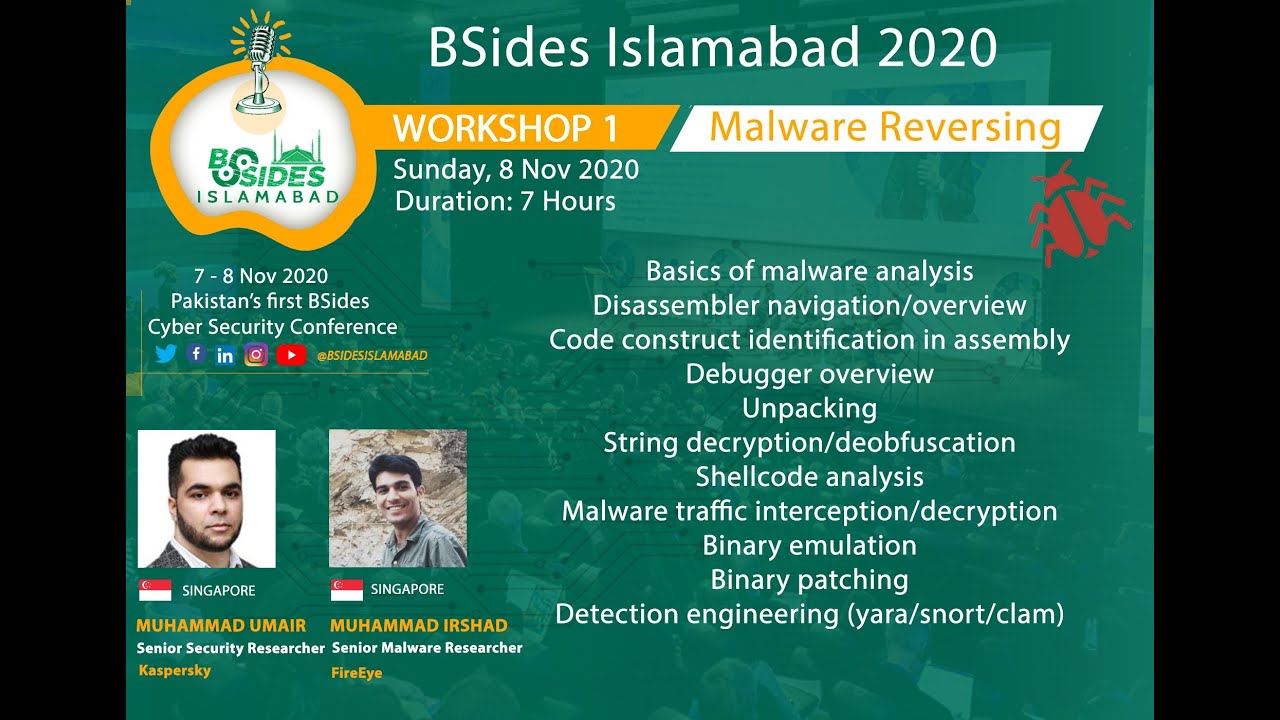
Day One : Malware Reverse Engineering
Tags
CategoryTechnical
About this talk
00:00 Day Start 01:00 Introduction 06:15 Outline 10:47 What is a Malware? 14:06 Process of Malware Analysis 16:00 Topic 1: PE File Format Overview 31:00 PE File Format Demo 1:36:44 Topic 2: Assembly Language Overview 2:36:17 Topic 3: Debugger Overview and Demo 3:12:23 Wrapping Up Irshad has more than five years of hands-on experience in Threat Research/Intelligence, Malware Analysis, Reverse Engineering, and Detection. After completing his bachelors in Electrical Engineering from UET Lahore in 2015., he joined Ebryx Pvt Ltd, where he provided detection capability for ordinary and APT malwares for FireEye NX/EX products. In 2017, he moved to FireEye Labs Singapore, where he mainly focus on detailed analysis and detection of APT malwares. Umair has been in the cyber industry for over 7 years working in the areas of OS internals, reverse engineering and malware analysis. He started his career focusing on Windows Internals R&D for FireEye's detection technologies. Later joined FireEye Labs, and switched focus to APT analysis, detection engineering and hunting. Now he is part of Kaspersky's Global Research and Analysis Team (GReAT), A team of globally spread out researchers, that has discovered and reverse engineered some of the most notorious and sophisticated APTs to date.





