The Scene is Dead
Show original YouTube description
Show transcript [en]
Good morning everyone and welcome to Besides Las Vegas 2025. Um just a few announcements before we begin. We'd like to thank our sponsors especially the diamond sponsors Adobe and Iikido. Um and our gold sponsors which are Drop Zone AI and Profit. It's their support that uh along with the other sponsors, donors and volunteers that make events like these possible. These talks are being streamed live and as a courtesy to our speakers and audience, we ask that you make sure your cell phones are set to silent. So with that being said, we can start with Allison's uh speech with uh scene is dead.
There you go. Try to >> Hello. Oh yeah. Okay, perfect. Thank you. Okay. Hi everyone. >> Hello. >> So, hi. I am here to declare the depth of this scene. [clears throat] So, it's only appropriate to start out uh with some greetings and shoutouts. Uh, so first I want to give a shout out to the fine people from this group called Whoa or something like that. Um, also Conrad database, where are you? You you inspired the title of the talk. We've had so many long conversations and I never suspected I would be much later on coming to be yet another person to declare the death of the scene. Um, also Mr. P and Bids proving ground. uh this
the proving ground is uh where I gave my first conference talk and it's an incredible honor to be coming back and keynoting at bsides. So thank you and thank you for also for the sake of coverage I want to give shout out to Matt, Chris, Ben, Brian, David, everyone with that name. I think we got some good coverage there. Uh, also friends in high places, we love you and everyone that works with me for keeping the dream alive. I'm gonna just hold this mic. All right. So, I'm going to get into some pretty spicy topics. I'm just going to like cover ground rules here. Um, so I'm not going to talk about bad actor names for
the most part except for a couple just to anchor the discussion in people understanding what I'm talking about. Um, I know the general desire is to not name bad actors because it gives them attention and all that. Um, but that's not actually the reason why I'm not naming bad actors is because these bad actors are so forgettable that, you know, in a little while from now, no one's going to know what any of these groups are. Also, I think this is feedbacking. Can I turn this off? Sorry. Um, also, I'm not going to name companies. Uh the reason why is um the public conversation right now around platform abuse is kind of where the public conversation was around data
breaches 10 years ago uh where basically people are blaming companies for admitting that there's a problem and doing something about it rather than blaming companies that sweep it under the rug. Uh so you know the the state of maturity of the conversation is uh the way data breaches were 10 years ago. So, I'm not going to name any companies because I don't want to get anyone punished for doing the right thing because that's happening a lot right now. Um, also bad content warning. We're going to talk about some bad stuff. Uh, if it makes you uncomfortable, you have every right to turn away, walk out. You don't have to explain anything to anybody. Um, I'm going to avoid shock
value, though. I don't like that. All right. So, I'm going to talk about the way things used to be. Um, you know, I think a lot of people here, pretty much everyone here has tons of really fond memories of the old internet and their life path of discovery through technology and computers and learning that computers are cool and actually really fun. Um, I remember being nine and my dad like dialing into CompuServe with the 56k modem and I didn't even know what 56k was, but I knew that it was better than 28ks. So, that was really cool. And I remember playing Hunt the Wumpus. It was my first video game. Um, it was super basic. Um, I I remember
the first video game I broke was Sim Park. Uh, I don't know if any of you guys ever played it, but it's like an educational game. Uh, and I found out that when you're making the playground, you can make the slide dump the person out in a different place than when they walked in. And that was the only piece that would do that. So, I thought it would be really funny to dump people in the water. And then the game started breaking and then I found like, okay, I'll let them free. I'll make a little boardwalk. And then I realized I can just put a concession stand there and they'll just keep buying from the
concession stand over and over again. Wow, that's cool. And then very quickly my whole game became this infinite money dystopia and I learned that hacking is cool. Also, shout out to this one programming class I took in high school. My teacher taught me the most important lesson I learned in high school is that you can violate the spirit of the rule if you follow the rule. And that's how computers work. And he would give these assignments and I would figure out like, oh, I don't actually have to do the assignment. I can just import a library in PHP that already exists. And like he knew exactly what I was doing. And he would just smile and accept my answer
and like, holy [ __ ] that's amazing. Um, yeah. So like my whole teenage years growing up years was being around computers, loving breaking computers because it's funny and it's amazing, it's fun. Um, and now I work in cyber security. I work in like looking at patterns of how humans interact with computers and now that's funny and it's interesting and it's fun and I like breaking it. And people make organizations and you can break them. Here's a cool document I came across when I was a teenager. It really spoke to me. Um especially the parts about, you know, finding truth, using the internet and computers to find truth. Um how computers when they break, it's not
because they don't like you, it's because you messed up and you can fix it. Love that. Really spoke to me. Uh, I didn't realize until today that this document is one year older than me, but like this is the way things were. This is the nostalgia. This is the old internet. And there's something really echoing right now with the mics. I'm trying to trying to stay away from the mics. Thank you. So, you know, I I literally just declared the death of the scene, but uh the scene is more alive than it's ever been. It's just not underground. and it's full of amazing people. Uh but anyways, to my work, um I've been working on the criminal underground
since 2011 in one capacity or another. Um it's been super interesting. I love cyber crime. I love fraud. I love breaking organizations. I love breaking botn nets. It's great. Um, but over the years I've noticed that the criminal underground has gone through changes and shifts over the years. Um, every single year that I've worked in this stuff, it has gotten more severe. The kind of crimes that they get involved in are more depraved. Um, it's probably always been this way, but there's a couple of uh shifts that have been significant. Um, one was the price explosion in Bitcoin. Uh, this turned hacking from something that was interesting and fun and cool into something that will get
you retirement money real quick. And so it attracted a different kind of person. It attracted the kind of person who wants a lot of money real quick, not the kind of person who really loves technology. Um, another shift that's happened that really changed the underground was the pandemic. Um, I don't completely understand why, but I do know there's been, you know, a massive influx of people that were using were not previously using the internet, probably weren't that interested, and now suddenly they were forced to use the internet. And I think that, uh, the criminal underground has changed as a consequence of that population influx. Um, one thing that I noticed is, you know, these people coming in that have
no interest in technology, some proportion of them were interested just in violence and that manifested in different ways like uh viewing violent content, forming communities around that. Um, trying to create violent content, participate uh and experience uh perpetrating violence. Um, prior to the pandemic, there were certain um, lines of activity that we just did not see and then we started seeing it uh, after the pandemic started. Um, so also, you know, when we're talking about the underground and how the industry deals with it, um, part of that involves off-ramps to try to rehabilitate or divert young people away from doing something that they can't take back, right? Um, this is very important, very noble work. Um, and you know, like as
time went on, more and more off-ramps got built, right? uh the industry professionalized. Uh there were things like bug bounties. There were things like the normalization of hiring reformed hackers. Um and also just people growing up and having a family and like you know starting to care about their life. Uh so these were all uh very good things. Um, but there is one thing that I do want to call out that we collectively do need to discuss as like a cultural change that we need to consciously think about. Um, and like I'm not going to tell you the answer, but I'm going to tell you the problem and you guys can work out the answer.
But here's the problem as I see it. Um, it's very common that people have a stereotype or a joke of like, oh yeah, the best way to get a job in security is to get arrested. Um, I mean like factually that's not true. it hasn't been for a long time. Uh, but it keeps getting repeated because it's it's a it's a great movie plot. It's a great TV show plot. So, it keeps getting repeated, but like the reality of actually working in the industry is not true. Um, even the people who have been arrested and then gotten jobs later, their career was set back by years. Their pay is set back by years because of all of their issues with the justice
system and then having a record. Right? So, this is this is not a benefit. And I have spoken to multiple people that have come out the other end of the justice system, you know, living a positive life. And they've told me that they've heard sentiments like this when they were a young kid. And I mean, they never blamed it on those sentiments. They're not like a victim mentality type person, but I'm saying I think those kind of sentiments may have influenced them and other people at that young juncture point. So um one thing I do want to introduce into the conversation is we need to start considering the nature of the offenses. So like what I have hired
convicted hackers and I will do it again. I'm not a hardliner on this but we do need to think carefully about the nature of the offenses. Certain kinds of offenses are more possible to rehabilitate than others. And ultimately the choice is on the person what they're going to do with their lives. But, you know, there is some predictive power in understanding the nature of the offense. So, like I would rather hire someone that hacked the Pentagon than someone that hacked a girl like a little girl or hacked credit cards or hacked an old person. You know, it's a completely different mentality that goes into those different kinds of behaviors. So, you know, we got to consider that.
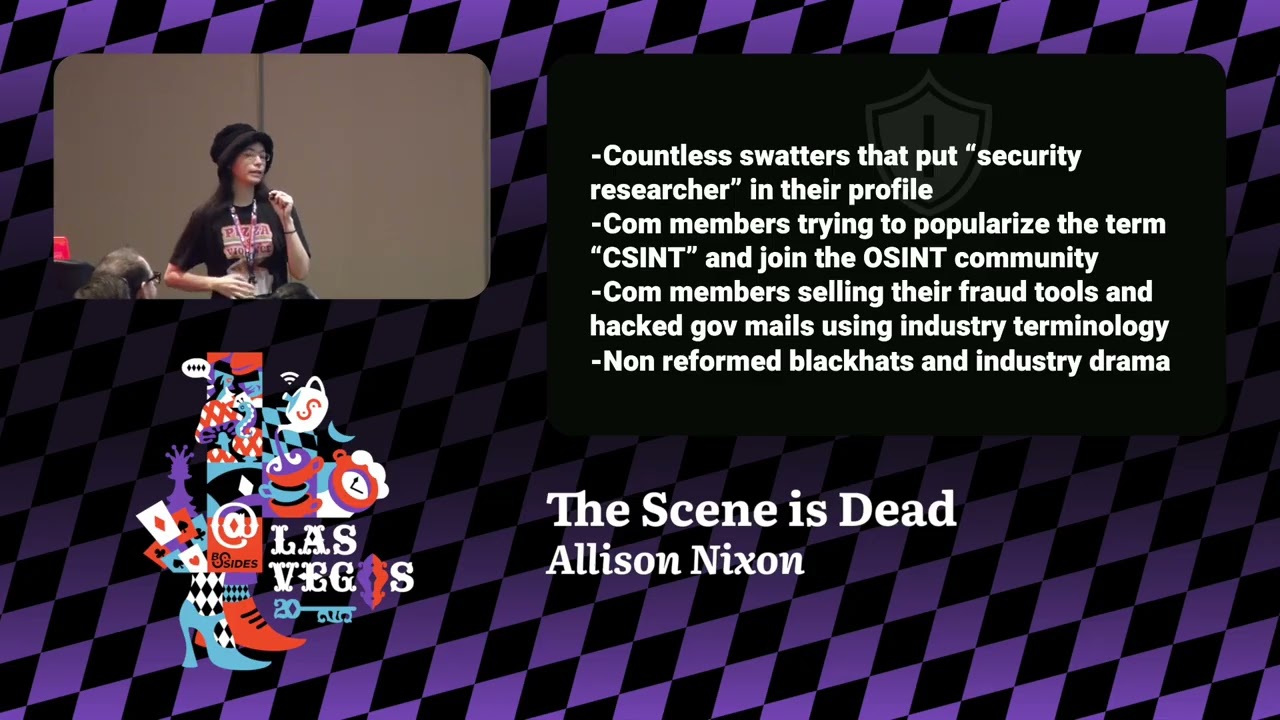
Another thing we got to consider is that current day active offenders think about the industry a lot. Uh I'm going to I'm going to throw up some generic examples and then we're going to go into some specific examples. Um, so one thing that we find in our research is that a lot of high harm offenders, um, especially SWATs for some reason, I don't understand, they put security researcher in their profiles. And like I get that that's something anybody can just proclaim to be, but this kind of stuff makes me want to like change our job titles. like we got to we got to euphemism treadmill the term security researcher. Um, another thing is comm members
getting involved in the OSENT community. Um, I'm currently experiencing a lot of confusion because I'm learning about OSENT tools for the first time through fraud and I'm approaching the conversation from a direction of like oh this is a fraud tool but but no actually this is a real company. It's an OSENT tool but it's used by a lot of fraudsters. So, how do you differentiate like a legitimate service that's just abused versus a straightup criminal tool? Um, also we're seeing straight up criminal tools being used and sold using industry terminology. Um, the term cement is something that's coming up a lot in the criminal communities and I don't think it's coming up a lot in
industry. I could be wrong. CEST stands for closed source intelligence. I'm not aware of any of the cement methods that are legal. I think C should stand for criminal. Um, and I don't think it's an industry tool because it's all involves illegal activity. Um, but anyway, if you ever see that term pop up, that's an interesting term. Um, also non-reformed black hats in the industry, uh, they exist and if you've worked in the industry for more than a few years, you're probably aware of some and you're probably thinking of one and all of you in this room are probably thinking of a different one. And whenever you see any kind of industry drama blowing up, by
the way, if any of you haven't run into this yet, at the core of most industry drama is going to involve some kind of non-reform black hat. Just a little life tip for everybody that may not understand what's going on with that. Okay, so here's a couple. I'm going to go through several specific examples. Um [sighs] all right. So, when we're looking at raw information, um, sometimes people will call out like, "Oh, hey, you're in university, too." And you can see like some of these people are definitely in school for cyber security, but then they're also hanging out in these fraud chats. And I get the allure of doing research. I mean, I also hang out in
fraud chats, but not like socializing. Um, and one thing that I do worry about people coming into the industry is like when you're doing this kind of work where you're looking into the other side, you do need to compartmentalize and like kids getting into this don't necessarily get training on how to do this. And there's no like actual proper public information on how to protect yourself from a both legal and safety and everything perspective when you're sticking a toe in these waters. And it can be extremely dangerous. Um, like I know some people running aliases, uh, like I I remember recently telling someone like, "Oh yeah, I'm I'm glad you reacted that way in that conversation
because if you helped that person, you would be providing material support to a terrorist and and it was like a surprise to them. Uh, that makes me incredibly uncomfortable that it was a surprise to them. I think uh people are doing this work very dangerously and they don't need to." Um, but anyways, uh, we're going to go to the next item. Um, this comes from a court document that I could not get on Pacer and I really wanted it. Um, and it seems like there was one person on the planet that had the document is this journalist on Twitter, um, BX on X and, uh, she follows a lot of these sex daughter gangs, uh, related
to 764 and stuff like that. So, so that's going to be the major anchor point here for bad actor groups that I'm talking about. Um, and and this involves like violent sexual acts for no reason that I can really understand. Um it's it's difficult to understand the motivations but but anyways this person in the court document um he's facing several decades worth of charges and the court document shows that um before he was arrested he was employed with an information security startup specifically working on anti-seam tools and you know I don't know if it's ironic or just predictable that someone offending in that category would also be trying to seek work in that category. Um, I mean, this is kind of where our
traditional conversation of like, oh, hire the reformed hacker, they'll help out and defend against the thing that they committed a crime in. Um, you know, the CSAM offenders are hearing those conversations, too. And we got to be really careful around this. Um, another example, this person hacked the SEC or he was part of the group that did it. Um he posted some video blaming everybody except for himself. Uh and he mentioned that he was in college and majored in cyber security. Uh which is interesting. Um there's multiple actors that I've seen that are majoring in cyber security and then they get arrested for some kind of big fraud. and they were clearly using the skills that they were learning
in their training for school and courses and certifications for these fraud purposes. Uh I mean those of us that work on incidents, we see the TTPs, you know, straight out of textbooks, right? Um so, you know, us as an industry, we culturally need to start thinking about the trainings that we give to people. How can we make sure that this knowledge is not going to be abused and misused? Because right now, on top of the wave of violence involving sexual violence and physical violence, there's also a lot of high dollar fraud happening as well. And some of these really advanced techniques are coming from people that have access training in pentesting and are playing on the same level that all of us are in
this room in terms of pentesting. So, you know, that happened and I'm not going to say what the answer is. I don't know, but I just want everyone to know that this is happening. Um, here's another situation. Uh, this involves one of the really early sex orders, uh, one of the first groups. He was a really big offender. Um, and I thought it was interesting that he's studying computer science before he got arrested. Um, I'm wondering, you know, how much of this knowledge factored into his ability to target uh underage victims. And one thing we're seeing a lot, especially with, you know, the comm and this overlap between fraud and sex crimes is that a lot of these actors are
realizing that the skills that they develop in order to hack and target little girls and extort them using their personal information, it's also very useful to leverage against companies. So we see some of these people flip their skills into different purposes where you know the same TTPs used against little girls are now being used against companies and they will eventually apply for jobs right that's another thing we all need to think about these skills it it's more difficult to dox a little girl than it is to dox an adult because there's just less footprint and for these people to develop the skills and abilities to be able to do this effectively. Uh I mean they're beyond me
in terms of OSEN ability sometimes. Um and and this is going to make them very hirable. So before I show the video, um I want to you know this is a call to action. So I want everyone to think about what I've said and how we need to change things. So one thing is that we need to think about offramps and how we think about them. Um we can't save everybody. There are people coming into this space uh that the initial attraction for them was violent videos, videos of animals and women being harmed and killed and they find this uh enjoyable on some level and and some of some of these people are entering the talent pool. So we need to
understand that, you know, certain offenses here we need to think about a little bit differently. Um, another thing we need to think about as an industry is, you know, it's a fact that we don't have the ability to kick out bad actors from the entire industry. You know, they can get fired, they can get kicked out of a conference, but, you know, they they hop from one place to another. And, you know, this has always been a big controversy. Um, but when these 764 kids start applying for jobs within the next five, ten years, this is a conversation that's going to be forced on us if we don't find the answer ourselves. Because in the nature of our
jobs, we all have access to an extraordinary amount of personal information. And these are personal information on adults and minors and vulnerable people. Information relating to victimization. information where if you abused it, it could cause someone to die. And and we have this as a nature of our jobs. Our jobs are a position of trust. It's not just about skills. It's about position of trust. And we need to start treating it that way because if we don't, governments, our government, foreign governments are going to start imposing it on us. Think about it this way. If I was to apply for a job at a daycare where I would be working with five children, I would have
governmentmandated background check, all kinds of legally required, you know, like can't, you know, have to have a clean record, right? But if I apply for a a job working in cyber security with access to millions of children, what is the requirement for minimum conduct and background check and making sure that there's auditing that I'm not misusing the data like where is that? We need that and we need it quickly because this is coming next 5 10 years. Uh the other thing is that we do need to take a look at the talent pipeline. Um, you know, we need to engage with young people. Um, there are still situations where young people are getting interested in cyber
security at a very young age and they're stumbling into bad communities. It's still happening and there are still people in these bad communities that can be saved, that can live a positive life, but if they get wrapped up into this too deep, I'm not sure if they'll be able to come back. So, this is something that we all do need to have a serious conversation about. Um, and like I said, I don't have the answers, but my call to action is that I want you all to think about this. And I'm gonna close out with a video. Um, you know, I've said a lot of things about what the bad actors are like and, you know, why I have such a
negative outlook about them. And, you know, I haven't really gone into detail about why. I mean, I you guys have a general idea now, but I'm going to give you their words and then you can think about it.
>> What did you get for people? >> Actually, that's a really funny story. When I was around 12, I wanted to learn cyber security and then he spoke about doxing and I wanted to learn about docs because I wanted to seem scary and then uh well I just led myself into calm. He taught me some stuff about doxing. >> Nick, how do you find these victims? >> I find some people with socials connected to their accounts and I just do some uh open source intelligence on them and I find some leads and I just get to work. How does exploring work? What do you do? >> Uh you gather info on them either by social engineering or you use uh open
source tools. >> My main method would be social engineering. I'm not really that good at cyber security and all that. >> If you can tell what's the average age of a company? >> Well, the ratio is between 13 and 17. >> I guess your youngest is 13 then. >> My youngest was 11, but my my average is 13. When you make someone offer those, what does that make you feel? If you're proud of yourself, somebody makes someone else. >> Well, I don't really feel proud of it, but I feel some type of satisfaction. >> Since you're in these paper, did you ever face pressure or threats? >> No, not really. It's more like a community. Most of these people were all
pretty good friends. We're not really like big bullets. We're really put out to be despite the actions we take. I have a question for you. If you was to get a sentence, what is the highest sentence that would be high enough to make you guys stop doing what you did? >> Nothing. >> Maybe just like a life sentence.
So, come with the internet, but what about the more side of it? these groups who take actions against these harmful people, the police of the internet, better known as anti-extortion. Why don't we learn about who anti-extortion is and what it is that they do? Anti-extortion is a collective of groups that help young people victims of extortion. These groups do things such as pointing the victim towards a healthy path, providing support, providing sources for help. So let's say for example a victim come to you and I say they have my family's information. >> You could honestly just pull her information down and get arrested and shout out to my ex exporters and friends in extortion company. Even
though they do extort I still respect them but don't respect what they do. What motivated me to fight against extortion instead of joining it was because I had friends that were extortion victims and I dated extortion victims before and they were terrified of me because they think I was going to make them cut when I was only wanting to help them most of the time. >> Hard to gain trust from the AE community. No, not even lie. Most 80 kids were ex already or did it. Do you think everyone in those spaces is evil or just lost? >> Most of them just do fun to be honest. >> When did you first join the community
and how? I joined the community in 2022. No one brought me into com. I was here as an extortionist. What was your first experience with extortion cultured? I was disgusted and I was actually curious. My main reason for actually joining the community was for friends, not due to my sick intentions. Why did you decide to return to extortion after leaving AE? I explained this before. They backstabbed me. They didn't want to keep me. They made allegations. They're heavily egoistical. AE is more egoistical and more unloyal than extorters. Are there rumors about you you'd like to clear up? Uh, no, not really. Except for the pedophile allegations. I'm under 18. I cannot be a pedophile. What message do you have for
extortionists? I love them. They're not even egoistical and they all have their reasons for doing what they do.
Guess what happens next?
questions. >> Uh, >> yeah, just bring this just bring the stand out to the head of the pilot here.
just come up.
>> Sorry about this. Uh so you're you're really saying that like well like every hacking generation for the past 50 years it's kids doing stupid [ __ ] you know, and then kind of growing out of it. But you're saying there's qualitatively a really a big difference now in terms of the stupid [ __ ] that they're into. I think and >> why do you think that is? >> Yeah, I think there is still the old pattern of kids doing stupid [ __ ] and they're going to grow out of it, but there's a new pattern on top of it and that's what I'm noticing is it is a qualitative and a quantitative difference and I think it has to do with
what initially attracts people to this space, right? So, you know, back in the old days, it was about having fun with breaking computers and making a computer do an impossible thing, which is amazing and funny, right? And sometimes you might go a little bit too far and accidentally hack the Pentagon, but like, you know, stuff happens, right? But these people that, you know, I just showed a video about, they're initially attracted to the space because of violent videos, violent material, gore content, death videos, and they're coming into the space and they initially see hacking as a vector to control other people, to coersse other people. And this is a fundamentally different mindset. And I think it's really based
on the kind of people that see the initial attraction. >> Yeah. So basically this [ __ ] ain't funny anymore. That's really what it is, right? >> Yeah. And and there's like a self- selection bias here. I I think the kind of people that are coming into the space and engaging in that specific kind of activity. I think there's something maybe fundamentally different with the nature of themselves, like what they're bringing to the table. And I think we need to recognize that. >> Thank you.
Yeah. So, um that was a great talk. It it really struck home like to me because um you know, especially I don't know since I was pretty young like you know uh since 2016 and then it really ramped up in 2020 during COVID. Um, I was really big into the Roblox and Minecraft hacking communities. And it's crazy how, you know, the scene progressed from like, you know, just simple hacking and Lua and Java and all that to, you know, stealing accounts, Robux, Minecraft accounts, and then that turns into doxing and, you know, sexual harassment and a lot of random bigotry that, you know, just didn't sit with me as like a kid and teen. But, you know, getting
into all those communities and discord servers really like irked me, but it also brought a weird sense of intrigue that, you know, had I not gone into like, you know, a more white hat like cyber security tracking school, I might have went down the wrong path. So, I don't know. Is there any like guidance to you know the kids in these spaces that are just stumbling into something that seems cool and you know they don't realize it's like something much more serious after that. >> Yeah. I mean, one aspect of this, um, I mean, I think every kid, teenager, child looking at these spaces from the outside, I mean, they bring something to the table themselves, like their
morality, what their parents taught them, like don't steal, don't be a piece of [ __ ] kind of stuff. Um, and and that serves as probably the biggest off-ramp or deterrence or prevention for cyber crime in this kind of online behavior. So, I mean, a kid encountering these spaces, the the thing that's going to most strongly guide them to their ultimate outcome is probably going to be the morality that their parents gave them. Um, I mean, one thing that we've noticed is that, you know, younger kids running into this stuff, it can be more dangerous because, you know, they're still developing their morality, right? Um, I think parents need to talk to their kids about, you know, who they're
talking to online, what groups they're involved in. Um, because right now the the knee-jerk reaction is to like shut everything down. Um, take away the phone, block the communication, whatever, block all the websites. But that's not actually a solution. You can't prevent a child from communicating. They if if you take away a child's ability to communicate, their only goal in life is to restore the ability to communicate. internet blocks are never going to work. Um, and and likewise, like I I go back to like not trying to, you know, punish people for doing the right thing and cleaning up situations. This this problem, like a lot of it gets blamed on the companies, but this is actually a youth gang
violence problem. This is a social phenomenon that is independent of any one website and a lot of it is happening uh driven on third party websites that are operated by bad actors in the first place. So you know as a whole we need to have an understanding of what the problem is shaped like and once we can understand the shape of the problem we can start to tackle it and pull it apart. I I think there's also like a weird intersect between, you know, the community and the alt-right pipeline because um in one of those spaces I was in, it was a simple like Discord server about like Minecraft hacking and it was I was there for like you know day zero,
day one of log four shell when it was like mainly still for Minecraft and not like you know hacking like you know thousands of uh like vulnerable servers but and it was weird because there's this like technical circle there's this very queer circle as well. And then there's also just like this like violent circle of hate and bigotry where you know people were calling each other slurs and you know doxing each other for no reason. It it was just Minecraft hacking. So um I don't know. It was it was really weird to be in and I'm glad I had the morals to get out of that as soon as you know quarantine lifted. But you know I kind of worry about like some
of the people I knew that you know were still there after I was gone. So >> yeah, the social dynamics you're describing, that's my viewpoint of how all this stuff works. Like there is sometimes this small core of violent dysfunctional people that are driving all these investigations that industry has to work on. Uh so I mean yeah identifying that core that's going to be part of understanding the shape of the problem. >> All right. Thank you. This this was like this is super insightful. Uh this is my first conference so I'm glad this uh was a good speech. I'm glad you found it valuable and I hope you make a lot of lifelong friends here. I've made a lot
of lifelong friends at Bides. >> Thank you. >> Hey, thank you for the talk. Um, as a recent college grad, I'm like particularly interested in uh knowing what you think about what responsibility professors and upperassman students have to the students who are coming in as 18year-olds and being exposed to these topics for the first time, often without um any or minimal discussion of ethics besides don't do it, you're going to get arrested. Um, so yeah, curious to hear any thoughts you have on that. >> Yeah, that's super interesting. Um I've actually started asking around you know university cyber security courses. Are there actually any cyber security ethics courses? Is there even any class plans any textbook for this? And the answer
has been no. There is no material specifically addressing ethics in cyber security. The question of like oh hey I found this flaw. How far should I go with it? What are the implications? You know who could I potentially be harming if I do this? How can I avoid harming someone? That's not written down anywhere. And so right now, yes, you're right. There's a whole generation of kids that are going through learning the technical skills, but they're not learning the ethical skills that will direct their activity. And you know, I do see consequences of that on the industry side where people coming into the industry, they uh they don't realize that they're being a bull in a china
shop and they don't intend to be bad, but they just don't know. And maybe if we had some kind of university ethics classes alongside the training, maybe we could reduce some of that from people who do want to do the right thing. >> Thank you. >> Thank you. Thank you for uh touching on such a difficult subject. Um with people that are in this industry seasoned um with gray hair, um how do we um how do we combat this? Like is there a way for us to do something about the young kids that are on the internet? How do we go? H how did you stumble into this research and how can we pick this
research up and move forward with it to stop this activity from happening or at least trying to cut it down? >> Yeah. So, I stumbled into this research because I just find cyber crime to be way more compelling than working on AP. Like AP are just a bunch of government employees that are boring, but cyber criminals are just so creative and interesting. Um so you know that's that's why my work has always focused on it. Um but in terms of combating the problem I mean one aspect of it that ourselves and partners have been working on a lot lately is um arresting the ones that really need to be arrested. Um you know now that you've seen the video you
could probably understand like there's certain kinds of incarceration I can really get behind. Um but that's not the entire underground. there are people that you know can have a future, can be part of society and won't be a problem. Oh, and uh I think everybody needs to take an active engagement in finding those people, pulling them out, making sure they won't be a problem. Um and and you know, other creative ways that we can find that are offramps or blockers to getting into this space entirely. Like right now, a 12-year-old that's interested in cyber security, no criminal background or anything, when they Google search stuff about cyber security, what are the top Google search results? Because one of them who had his
life ruined told me that the top Google search result was a criminal forum. And I don't know if that's still the case, but you know, maybe if the top Google search result was something else, he wouldn't have had multiple felonies. Thank you.
>> Uh, back when I was young and first started getting into hacking security. >> Back when I was young and first started getting into hacking security, there weren't really very many legitimate paths into that. There weren't >> I still can't hear you. Sorry. >> Back when I was young, uh, there weren't many path legitimate paths into learning security and hacking. uh if you were interested in that in these those topics, you sort of inevitably ran into underground servers, IRC, stuff like that. So, there are a lot of people that were doing illegal things, but not necessarily uh immoral or malicious or things like you've showed now that in the modern day there's, you know, co
cyber security, college courses, there's hack the box, uh stuff like that. Uh, are there fewer people getting into the underground now that would have sort of moderated that uh, horrific influence that we've seen now that it's now only attracts these sorts of people? >> Yes, I think that's actually a major factor in why things tipped so severely. Um, because you don't have a mediating factor of, you know, I don't want to say normal people coming in and kind of balancing things out a little bit. You know, they're not there anymore. they're of getting jobs. Uh I mean back when I was growing up, my college aside from like a couple of classes, there was just
no computer classes period and much less cyber security degrees. There was just nothing. So yeah, I also looked at a whole bunch of underground stuff too when I was learning. And you know, back then it wasn't about victimization, it was about knowledge, seeing a stop sign. Now I can talk to people after the talk. >> [applause]