BrakRPi: Crashing Bluetooth Communications On Raspberry Pi Using Braktooth
Show transcript [en]
Thank you very much. Uh hi everyone. Uh thank you for coming and in next 30 minutes I'll tell you a story of my first u introduction into the world of cyber security although I'm not a cyber security engineer or not related to security at all. uh and I'll talk about a story of how I was able to uh reproduce a publicly uh disclosed vulnerability uh on Raspberry Pies and um I'll also talk about Bluetooth itself the vulnerability itself and why uh patching the code uh for this for the vulnerability isn't necessarily enough but few words about myself so I came to UK 11 years ago to study um I uh I studied did a computer science and
office books university uh successfully graduated in 2019. Since then I've been working um I started work working as a full stack engineer and then back end engineer but five years ago I made the decision that one of my friends called a mazakist decision joke jokingly of course uh and uh transition to embedded engineer so since then I've been working as an embedded engineer and uh in free time I also uh write about digital privacy and tech policy. The ironic the ironic thing about all this is that um I actually hated programming in school and I didn't expect uh my that I'll be working in it yet here I am giving my second uh presentation in 6 months and
in my second besides ever um one disclaimer as well um I do not recommend anyone uh trying to exploit the the vulnerability that I'm going to discuss in public or or without any consent. So if you want to try try it out yourself, please do this in your own test environment or with your own devices. Uh although to be honest, if someone uh if someone uses uh speaker with a very loud music, u you can you can do it. Um so Bluetooth um before we start, can we can uh please raise your hand if you use Bluetooth on a regular basis, whether it's for work purposes or not. Wow. So basically there's half room. So
basically amount of people who voted labor next in later in previous general election. So uh Bluetooth protocol it is everywhere around us. a lot of more and more devices uh uh support communication over Bluetooth uh and for protocol that has be and why so why was why it became so popular uh during so uh this protocol was named after how Bus a Danish king who was able to unite lands in Denmark in 10th century if I remember correctly um and uh this protocol was designed as a way to communicate uh between devices access and exchange data with each other. Um and eventually it uh progress. So basically first uh uh device was a uh wireless mobile headset but then it
evolutionized and uh it it was uh it's it's being used in smartphones uh EVs or smartphones of wheels as I call it in IO in IoT including this uh Bluetooth fork I don't know who else designed but anyway and uh to understand the scope of how many devices are um the official uh organization that is responsible for designing Buddhist protocol reported that in 2020 over 5 billion devices were shipped. Uh so yeah the the scope is enormous and uh sometimes difficult to understate. So let's look let's look at the specifics now this so basically this is the Bluetooth protocol stack and if that frightens in if that arrows and abbreviations squares circles frighten you I'll explain to you
as if uh with the TCP IP uh version so we have uh so Bluetooth consists of host and controller uh controller is basically the physical and data link layer parts of the TCP IP which are responsible for maintaining and establishing connection between uh two devices or more devices since Bluetooth allows to communicate one central to multiple peripherals and u uh meanwhile the host is responsible for uh application specific data. So basically create a create data that you want to send to another device and b and then controller uh proceeds to send it over over the radio. uh in this talk we'll spec we'll make focus we'll be focused on we'll focus on three elements of this stack uh which
are part of the host control interface which act as a bridge between host and the controller so basically those are cso ACL and link manager don't don't worry just remember those uh ter uh definitions we'll get to them later so um there is a joke uh that uh usually the IoT S in IoT uh stands for security and with Bluetooth ironically it's also the same because over 25 years since Bluetooth protocol existed uh almost thousand CVEes were filed uh whether it's for protocol or the stack implementation and uh one of them was black. So in August 2021, uh a group of researchers from Singapore uh discovered 16 vulnerabilities in the uh protocol stack definitions in commercial vendors
such as Intel, Qualcomm, Expressive and Cypress. um which allows to exploit the communic communication between two devices with a different range starting from like uh basically denial uh doing denial of service against the connection disrupting it to at some with expressive even going for arbitrary code execution and because uh because of such big names among those vulnerable it meant that billions of devices uh were get were vulnerable to this um the re researchers didn't test Raspberry Pi though and uh at work I I used I I work with Raspberry Pi so uh I asked so basically I reached out to them and asked for proof of concept because at that time uh they haven't published it uh published yet
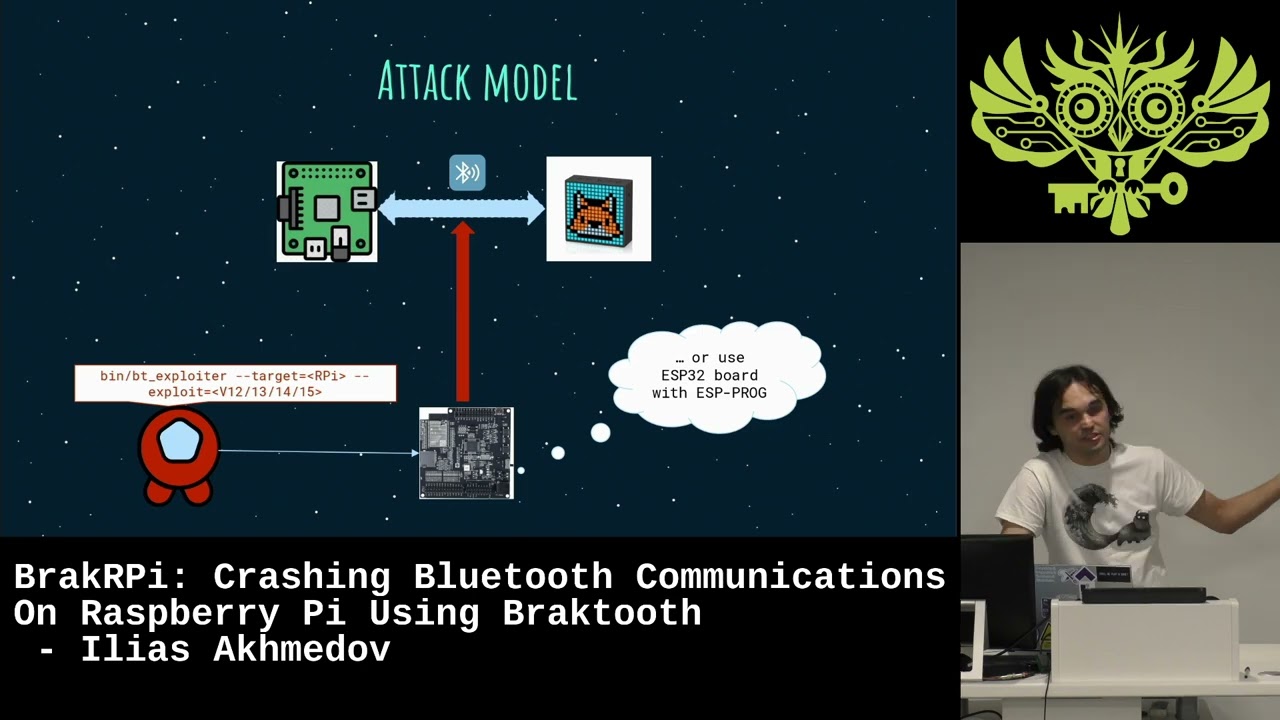
and uh they've been gracious enough to provide to provide the PC to so that I can test it on Raspberry Pies. So I immediately set up the um test system which is basically I use Raspberry Pi uh as a central. I used the I use a speaker as a peripheral device. In my in my case it was a dig speaker actually a really good one. I recommend one. I recommend that. And uh meanwhile I act as an impostor trying to attack the uh communication between two between devices uh using the uh using the hardware in in this case it's ESP 32 room kit um with obviously it's for my laptop but to be honest it's they the
researchers though said that it's explicitly this one but in actually you can replace it with the regular ESP32 microcontroller that supports supports Bluetooth but just make sure that your ES that you use ESP proc uh that's for due to the uh requirements for the proof concept. So this is how it look like well in real life. So you we have Raspberry Pi that's connected to the uh power bank. There's a speaker and there's my uh ESP to room kit. So um first things first I needed to set up the connection between Raspberry Pi and the room speaker. At that time uh the uh Raspberry Pi was running Ubuntu 20.4. for LTS with latest security with latest
uh updates including security updates and um if you're if you're surprised by seeing command line uh the reason why is that uh my Raspberry Pi was running a head basically UIless version of uh operator of the Ubuntu. So um uh due to due to my uh work purposes however it will also be helpful to show exactly what's happening behind the curtain. So the connect so basically establishing connection has been pretty straightforward. Uh I used the pin code to connect. Uh so I verified the pin code and if as if you can see uh it shows it says time box e audio meaning that the device has been paired connected and it's ready to communicate with the with the gway pi.
So uh my first attempt was uh using the vulnerability called uh invalid timing accuracy. Um now remember uh the abbreviations that I mentioned previously SEO ACL and link manager. So we'll focus on link manager here. Uh link manager protocol um is a part is a part of the Bluetooth controller that is responsible for establishing uh and managing establishing pairing and au managing and pair and authentication of the pairing between two devices and then keeping them in uh in communication between each other. uh in order to maintain the communication it uses the timing uh request uh basically it uses timing request response exchange. So basically the uh central device which is Raspberry Pi sends regularly the timing request
messages and the device should uh reply with a response uh meaning and then Raspberry Pi and says okay so it's uh it's live it's uh it's ready to receive data so all is good. What exploit does is that if you send the malformed uh so if you send a malformed packet towards the master so towards the um central device it will stop. So basically the uh it will stop uh uh yeah it will it will it will ignore that it will ignore that packet and basically throw it away. um essentially causing the uh the dis disruption of the communication between uh two devices. My attempt at running this did not work out. So the devices still connect uh
remained connected. But ironically then when I reached out to the researchers turned out it was actually a bug in the PC. So it's not it's not all nothing was wasted. It's not all was wasted. So and then I move to the second uh exp secondary exploiting it which is um involve the max slot type. So um there are five types of the logical uh transport uh protocols in Bluetooth depending on the whether the central device connects with multiple peripherals or just one peripheral. um for connect to communicate with uh only single peripheral it uses either SEO or ACL. ACL stands for asynchronous connectionless uh meaning that uh so in in this protocol uh you send the a lot
in this case you need to send a lot of messages and you don't care about and you only care about a lot high bandwidth of the communication and you don't care about the response from the device. So for example, it is uh used when you communicate your device to a speaker and you want to play music on it. Um SEO on the other hand is actually used for for timing synchronization. Basically for example when you need to use you use a wireless microphone uh because in because with with them timing is very important with ACL it's not that important. One of the fields of the ACL is the logical transport address. Uh so basically what uh this
exploit u malforms so basically that exploit crafts the packet by producing the LT address it's all zeros the problem is the uh problem is for communicating with one device you you can't do that and uh because it's been reserved for the active peripheral broadcast when when the one central device connects to multiple peripheral devices and theoretically what should and in any other case. So the what firmware should do is it should uh detect an exception and basically discard that packet. The problem is as the Cypus and Broadcom SDKs doesn't do that. So basically it receives message says oh I don't know what's happening so I'm just crashing. So um so yeah that that's me. So
basically here's my attempt to run the second exploit. So bas these logs are pretty much what I expected. Then I saw this and I get hopeful because if you notice the line agent uh agent unregistered. So um on Linux devices uh the main Bluetooth uh stack is uh called blues and agent object is uh responsible for establishing uh and managing pairing and the commun uh pairing and the connection authentic authorization between two devices on on the on operating system level to make sure. So basically to save that data and see and because and when it says agent unregistered it means that a that object doesn't know what's happening. It gets completely strange data and says okay I'm out of here I
don't know what's happening and then I saw this so it just crashed. So basically it crashes the firmware. crashes the entire service because if you if you can see it now shows the Bluetooth instead of the device instead of device name meaning that the connection has been disrupted and actually I haven't been able to restore the commun communication connection between those two devices in in 5 6 minutes now now since it was 4 years ago and uh credit to Cypus and Broadcom it has been fixed properly so one would say well that's all that's all fine so what's the problem but one thing is uh patching the code another thing is deploying it and that's
where things are getting very interesting. Um usually when uh one needs to upgrade the firmware uh you need uh the usual usual process which is pretty much secure and reliable one is that uh you sign the you sign the firmware you sign the compiled firmware with a with a private key and then when you apply that update either over the air or or through the debug port or whatever um the firmware version the firmware checks the uh signature sees that okay it's all I applied the firmware. So I I'll apply the update. If it does, if the signature is back is is not matching, it says I'm I'm reject I'm I'm not going to update
it. I'm just get getting rid of. But the geniuses at Cypress and Wcom decided to do things differently. Instead, what they do is they up they upload the firmware at the manufacturing stage in the read only memory. The problem is it's read only memory. So you can't so it means the firmware is getting immutable. So you you can't update it further because obviously vulnerabilities maybe bugs I mean maybe not necessarily security bugs and uh so in in in that case so instead they using something called patchwam so patch ramps uh are based on the flash patch units which are part of the arm architecture. So what they're doing is um uh they they have the they have this field. So these
fields so basically it overrides uh it it it overrides the certain elements of the memory by having the reference to the address and new values and apply and apply those new values. So usually so basically in practice so what what happens it uh when the device so basically these um touchs are distributed as HDD files uh uh for the uh for devices for example on Linux in in Linux you can find them in folder I think it's user lab firmware BCM and they stored as httd files and they distributed uh as part of the uh a repository as a part of operating system repository in Linux And um so what happens is uh when the
device starts up it was the original firmware which is stored in window only memory then then the operating system searches for the hcd files which are in in this uh which are either in this folder or in Android's case for example it may be different folder uh it either which then it extracts those fields and uh it takes the it takes the memory address field it checks the memory address and then apply the value that is linked to that uh memory address value in the h in this patch slot. The problem is um the pro the problem is you can't have there's a limited amount of those pyram slots because because the slot field is just one bite. So it means
you can't have more than 256 slots. To make matters worse, go pi four at least has only 128 slots. In phones I believe it's it depends on the chip they're using but it can be sometimes 192 or 200. Um so basic uh so basically with the problem so basically so basically Cypress is doing is that they uh adding the adding those they and the problem so the problem is um Cyprus uh by 2019 uh when one year after Raspberry Pi 4 was released it has uh all the pyrams were already reserved. Ironically the the data of the from the compilation that was stored in read only memory of the of the of the Cypress chip
N P I remind you this is immutable one it was compiled in 2014 that had to apply 5 years worth of fixes in in only 128 slots and uh so essentially they so basically what happens is they are responsible for what exactly that they only they decide and which bugs they need to fix, which security vulnerabilities they need to fix and if the Python source are running out, they have to replace them. So if you so even if you for example you fix the uh practice vulnerability, something else is unfixed uh and you don't know what exactly is unfixed and that is and based the moral of the story is that one one thing to patch it another thing to
deploy it. Uh it's not it's not as it's not so bad though. Um because uh fortunately in order to uh avoid this attack uh or actual or any uh any other against the against this chip you can use uh Bluetooth external adapters. Uh now I've test I've tested some of them. For example, I've tested TP link with Bluetooth 5. I think it's called it costs 1520 on Amazon. It's been working well. But on the other hand uh what I discovered is that first of all the the scanning range and range of the of that uh adapter is surprisingly less than onboard that the Raspberry Pi Cypress on board chip and uh secondly blue is uh
which is uh again I remind you it's protocol stack for Linux it's not always reliable working with the uh with those devices. So you have to technically value basic weigh in whether you use Bluetooth or not. If you don't use Bluetooth, I suggest to shut down Bluetooth adapter entirely. If you use Bluetooth, either use the external adapters or there is another option I've seen recently to use ESP32 micro controller as a Bluetooth proxy which is which is also doable. I think home assistant uh has in fact has some manuals for that. So um two things uh left to talk. Um so first of all to talk more about impact on devices. Um if you think to upgrade
or if you think that buying Pi 5 will fix the problem, it won't. it they use the the exact almost the exact same chip uh for Bluetooth and for Bluetooth and Wi-Fi which is what cy which is what cypus chip is there for uh but for it's so basically it's it does not concern pyos because they are different uh they're completely different essentially microcontroller uh plus pyos were released uh after bra to was uh publicly announced so on that on that it's on the so if So pyos are out of the scope for for this attack. Um other devices. So in terms of other devices um again I'm I haven't tested with other devices but I know
some people who have and um they and basically some some of the recent iPhone models and Samsung Galaxy smartphones use that uh Broadcom chip and uh they're vulnerable. So if you if you use one of those devices just fair warning also um Bluetooth is targeted. So basically there as I mentioned so there are two Bluetooth protocols uh classic Bluetooth and low energy low energy is uh mostly for spec uh dedicated for the uh low so bas for communications where you don't need uh to constantly send messages and also for for example mesh for mesh networks and uh and this and Bluetooth uh is targeted against exactly Bluetooth classic. But there's a caveat though. Uh a year
before that uh the same group of researchers uh released the another group of vulnerabilities called Swain and this time it was targeted against Bluetooth low energy protocol stack implementations. Cypress Cypus and Broadcom chips have been vulnerable against only one but it's actually the most severe one because it's a buffer overflow against link layer protocol. Link layer is basically uh link manager protocol but for Bluetooth low energy they have different uh implementation but they serve the same purpose. So um to conclude um if anyone wants to read uh about uh read more in details about the vulnerability itself or about the Cypress uh and and comra uh functionality you can check you can check some of these links by the way
don't worry I published the slides on my uh website so again and there will be link at the end so uh uh you're you're covered in that regard um few lot of things are in order. So uh first of all I want to thank uh my employer for allowing me to to give me few days off to actually investigate this and without without being distracted by actual work. I want to thank also Vhabi who was one of the researchers of the black tooth and with whom I've been keeping uh contact when I was doing those tests and he essentially and when I shared my findings he said the gap that's correct the it will be
pies are vulnerable and also I want to thank Iska Lassen from hustle platinum institute who previously she was working at at Simo at Simo lab um because she I've been sharing with uh the findings with her as well and also her paper has been her she was one of the authors of the paper uh that has been targeted against that describes the patron uh functionality and also she's she's she's one of the best experts that I know in regards to Apple reverse engineering devices and the wireless communications and finally I want to thank each and every one of you for coming I hope you enjoy this talk even though it's it's absolutely hot here. Uh and yeah, if you
have any if you want if you want to check my website with socials and contact details, you can scan the QR code and if you have any questions, uh I'll do my my best to answer. Thank you.
>> Do we have any questions? Yeah. [Music]
>> Uh yes. So basically the question is if Raspberry Pi 5 are still are still vulnerable. Yes. Because uh for the Bluetooth Yeah. For because um Cypress chip in Raspberry Pies in all the re like first, second, third, fourth, fifth. um uh Cypus chip is being used for Bluetooth and Wi-Fi communications and uh for in Raspberry Pi 5 they're using the same chip. So uh so yeah it's it's still it's still potentially vulnerable. >> Any more questions? Lovely. Another round of applause.





