API Token Attack: Real-World Scenario & Prevention #shorts
About this talk
Discover how attackers exploit high-privilege API tokens like AWS secrets. This step-by-step walkthrough reveals a real-world attack scenario and prevention strategies. #APIsecurity #Cybersecurity #RedTeam #ThreatDetection
Show transcript [en]
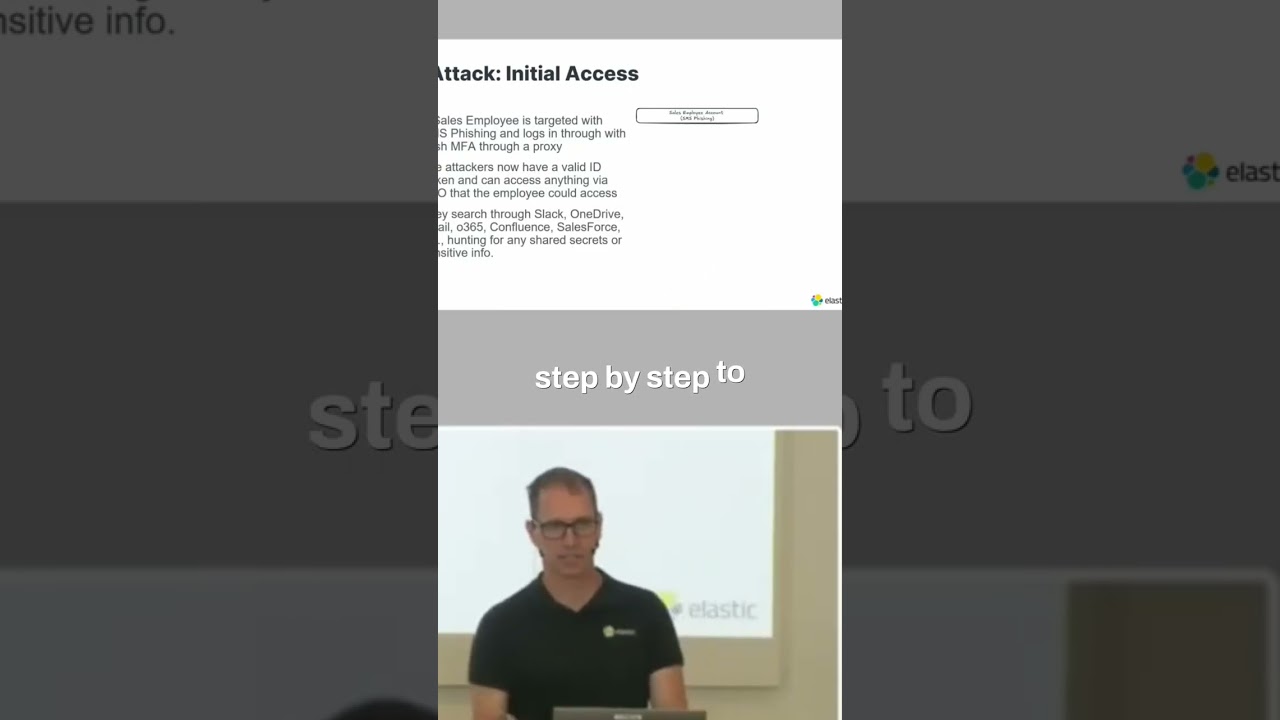
High priv- high privileged API tokens. Once again, these are just secrets that give you access to loads and loads of things. Usually like AWS secret keys, things of that nature. And so now I'm going to walk through a real-world attack scenario step-by-step to kind of show you like what this really what what a an attack looks like and then I'm going to go through how do you prevent it along at each stage of the way and how do you detect it at each stage. And so I know this is real-world because like I said, we have red teams every 6 months we hire a red team to come in and attack our environment. And back before
we went to fight 02 everywhere, this is this is kind of the story of what they did.





