Shadow Server Data Reveals Cisco Vulnerabilities & Threat Actor Tactics #shorts
About this talk
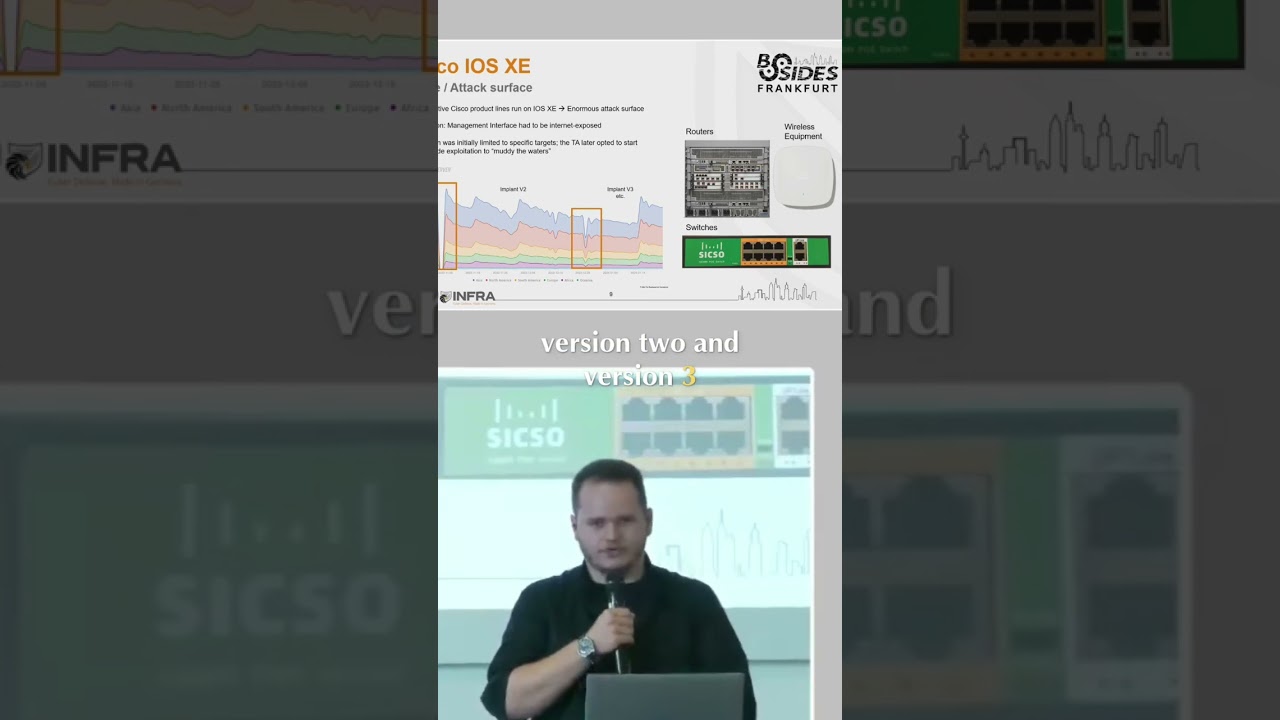
Analyzing Cisco vulnerabilities with Shadow Server data. Threat actors use fingerprinting evasion, seen in implant versions 2 & 3. Login traffic monitored via honeypots to track 'Coyote'. #Cisco #Cybersecurity #Vulnerability #Hacking #ThreatActor
Show transcript [en]
We also include data from shadow server in all of these cases. Um so big shout out to them. Uh this is the tracking data that they have for these Cisco vulnerabilities. Um there there are two big gaps in there. That's because of the um fingerprinting evasion that the threat actors used. I will come to that when we talk about the implant. Um and that's why there are annotations for implant version two and version three because it changed over time uh as details were uncovered. Yeah. So onto the log and traffic analysis. Um as I said we set up pony pots to monitor the situation and to monitor what coyote that's what the threat actor um is named internally um
that secure infra is was and





