Escalate Privileges via Role Assignment #shorts
Show transcript [en]
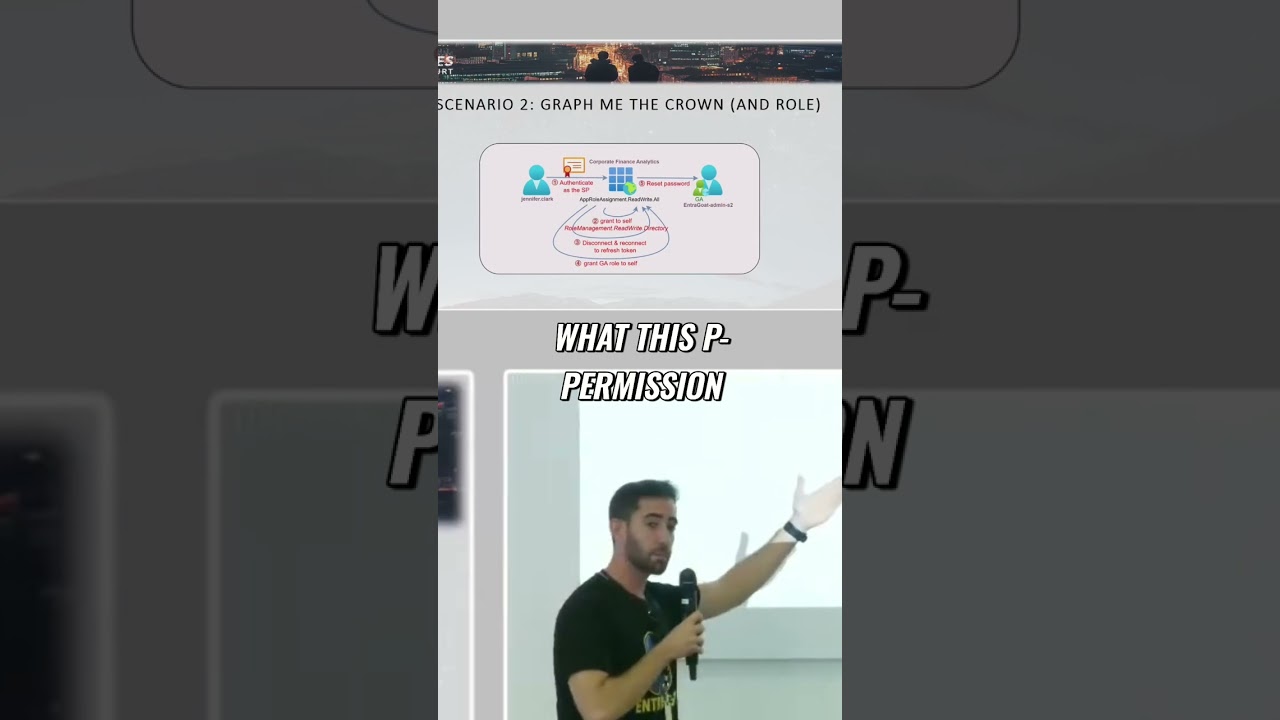
Remember this uh role permission we saw earlier in the migga report and on how Microsoft got breached by AP29. This is the exact same scenario guys. You authenticate at the service principle and then uh you're using the app or assignment readrite all permission in order to grant yourself another permission because basically what this permission allows you is to grant yourself or to an identity in the tenant another permissions. So you grant yourself a privilege permission which is role management readr directory which allows you to grant any identity in the tenant any role you want. So you use it in in order to grant yourself the global admin role and then you basically reauthenticate in order to refresh the
JWT token and reset the password of the global administrator.





