Timothy De Block - The Blue Team Starter Kit
Show transcript [en]
uh this is a very basic talk I won't be doing anything uh very very technical uh this is just um for for security professional work on team limited resources limited time limited people um it's a lot of a lot of the tools I'm going to address here are things that I Dev and I have stories for just about point so before we get to all that um I am a podcaster both consumer and a producer I don't know if anyone's listening to the PBC security podcast I produced that one uh also recently SP on my own exploring information security which uh Doug was kind enough to actually do an interview for this event on a few weeks ago yeah um and it's just
exploring several you know information security topics so uh and I mentioned podcast here more as the shame was but also because I found a lot of these tools listening to podcast I'm sure a lot of people are familiar with security weekly uh one of the first tools I I cover I I someone talk about the tool the new demonstration um so if you're looking for stuff podcasts are great great thing to do on write to work or write about uh I who am I I work for the state of South Carolina I worked for the state of South Carolina for the last seven years and so I have had limited resources and people so had to meet certain
challenges regardless of that and uh you know a lot of these tools are free for very low cost so um challenges had I've had to deal with uh you know first find figuring out how to research tools stay you know one of the things in information Securities you got to learn how to stay up with um so that's challenge itself hey go build a security Assessment program um you know why are you getting affected uh how can we you know Windows XP it's a it's end of life um but we're still going to have some boxes cuz we got to run this look have patient so how do we improve hardening on that and then
um how to you know heal patch management flashes come out with it seven vulnerability in the last three weeks how do we patch that quickly and you know avoid some of these Mal alerts so these are all the tools I'm going to blow by the the delivery of it right away we've got uh Google and Twitter uh for research and Discovery tools and staying up with you know the current some of the current information security use uh inabilities oos dead attack prophecy which isuse for security assessment um you've got the red line tool for forensics um and then the enhanced mation toool kit which is Microsoft PR toool that helps with computer and then finally we have PDQ deploy which helps
with patch management and getting get P adob FL take care of so my first challenge is research um so for and we've got some giveaways we've been giving them away for The Blue Team starter handbook what is the number one tool of security or of it professionals that's why you can't go first go Y and that's that's pretty much what that is I'll say that if you're if you're getting into information if you're getting information figure it in general Google know how to to search for Google one of my favorite techniques within Google is to put quotation marks around different things so Inc tools is going to give you in stuff and tools but if you put quotations around it you're
going to get a more defined search towards that so uh and the cost of that is your behavioral data um but you know it's it's a very valuable tool I think uh had several people shouting it out so uh um I'm not going to do dem i' got demol um so Challenge number two is threat um and so you know how do you stay up with that it's you know Twitter is probably one of the best things for this kind of thing a lot of break news before it hits the news media whether it's an article or a TV uh it's going to head up end up on Twitter and this is this is not just information security this is
sports you see this in sports uh you see this in political news you see this just about everywhere so uh in this demonstration here you got a hacking team um I don't anyone was on Twitter for that one but that was actually a lot of fun uh there's a lot of snark a lot of uh you know making fun of them and um a lot of rhetor there but there's also as you can see there there's a lot of people doing some analysis on this stuff uh you know going through this data finding Adobe vulnerabilities you know they had two or three Adobe vulnerabilities that uh that that adobe didn't know about so let me go follow
Adobe so I know when Adobe is going actually patch this stuff Rel P for um then there's also uh last year was I guess you called the year the open SSL and a lot of that stuff broke on Twitter I can remember when hardly occurred um because I was watching Twitter and everyone was talking about that um and from that there's a lot of um sharing of you know just just general links and information and tools um how I I personally be able to grab a tool and and go find out if uh my organization was vulnerable so um it's uh it's it's a very Val to I can't really say much more about it but uh for the second giveaway
here is Uber choose one and anyone name all five logo there got it anyone you got it yep that's it so that was a heart bleed which is the heart bleeding poodle which is the poodle Venom which is the the the snake there ghost and then shell shock as a show all right so Challenge number three was application security so we've got uh new uh new application even in the state they've got developers building applications that run a lot of their own offerings um so we've got to start testing the stuff before it goes out the door um I think that's very relevant within the news now um so I had no idea what I was doing but okay do it one of
the things I found wasap AAP is free uh before I get really into it is the alternative to that is B site uh and that is actually the tool of choice for application Security Professionals so if you go into application Security Professionals they're going to want you more than likely they don't want you to know BB Suite B Suite though has a community version but it's throttled a subscription of $300 will you the full version so um they both have their strengths and weaknesses I think zap has come a long way uh one of the benefits I found because also on my e podcast I've interviewed s Ben the creator of uh zap he works for Mozel he's actually a
developer he is not an infoset guy he's a developer that want to write more secure code and in Information Security Professionals just started come to and say hey this is a really good tool let me start using it um uh so uh I I I I've talked to a couple people about bur suite and how it works with developers but if you're if you're in your organization that you know money is an issue giving zap to all your developers is going to be a better cell and trying to give trying to get you know however many license of bir we um so um keep that keep that in mind um so now we'll go to a demo and I'm going to walk you
through so another thing that I have no OAS for anyone that doesn't know is open web application security project uh and it's a open source free sharing of uh projects and everything so OAS app is one of their flagships uh oos oos bricks here is a an intentionally vulnerable website um what it does is it allows you to go through and it'll walk you through some of the different attack vectors within the OAS top 10 uh so to set this up though for Z attack propy now I think a lot of people know you have a start that's that's where a lot of people you know fall into you know you can start there and get all
your low hanging fruit but you've actually got to dive a little bit deeper and we're going to dive a little bit deeper but it can actually even go even deeper than that I just I want to show some of the basics that kind of get you going so what you need to do go into here set up your land you set it up as a proxy right so it's just capturing everything that you're clicking on within um within the browser be careful of this because you do not want to go out and start testing a bunch of sites that you do not own this is specifically for your stuff uh get some serious trouble with it um if you otherwise if
you do that so you can see right here we've already started getting the uh Maps I actually don't want this this is built into the application so I can exclude it so I don't get trouble so a lot of times if you're not running if you're running this on the stuff that you have a bunch of other stuff browsing or you got other a bunch of other stuff open it's going to pick up that stuff so you have to really be careful about that there a screenshot there's mine screen capture software will exclude that but you just go and what the idea is that you're mapping out the application so you're going through and you're clicking
on every single thing you're filling out every single field you're hitting every single submit button you want to go through and fully uh explore the application so go to the about page let's go to the setup page go back so you want to go through and thoroughly test this this is a simpler page um uh than most applications but after you've done that you can actually start doing your attacks so you have a spider attack and that just does exactly what what what typically is you can see that it's spidering the entire website and if I do the drop down here we can see a lot more stuff is being found just by using that spider so and the more you explore
the application the more the spider is going to be able to go out and find um there's also the Ajax spider for ajax type of content and this is actually one of the uh cooler things to look at is that it's going to open up a Mozilla Firefox or whatever browser it has support for and it's going to start running through the application for you submitting different things so it's just going through ajax type of content on websites um and that can run for a while so we'll actually go ahead and stop that but um and I'm not going to do this next tag but then you want to do your Force browse site the force browse site is
essentially going through and it's got a list uh zap has some some default list but then they also have some you can build your own list but it's essentially going on looking for hidden directories and it's going to pound each side so this actually takes a really long time not going to even bother launching it um and then after all that so you essentially mapped your entire application then you want to run your active scan we leave it on you know I don't know any was no but you can see some Advanced uh options there um you like I said you can this is just scratching surface you can go much deeper and kind of fine-tune
some of this stuff for uh whatever testing you want to do and so here you can see what zap is running through so right now it's running through path traversal then file inclusion uh it'll run through SQL injection and this active scan hand take a while um to run so then you stop that and then you can go to report here and you can generate an HTML report you can generate an X XML report uh the XML is very useful for things like thread fix I don't if everyone's ever heard or use the thread fix but it's it's a application that's also got a free community version and and an Enterprise version and you can import your XML file
into there and kind of track some of these vulnerabilities so what I like about the HTML report here is that it's going pull up a report that looks something like this so and what's great about this is that you can hand this to to a developer and you can it has a description it has a URL it has a attack and you can you can replicate that attack often times too um so you want to confirm a lot of your vulnerabilities be fun it might be a false posi these SCS are not are not foolproof and and perfect uh they do would have false posi just like anything else um I going to scroll down a little bit here but you
can see that they have um and it show L URL they've actually changed the format a little bit but some of the solutions are longer than others because they're more complex but it gives you you know something that at least a a starting point for research it gives you references and links to follow um so um and you know you take that to developers and and you know try to you want to try to work with them on on securing your application
So and I've uh you know there's there's other like I said there's other things to get into it's got different modes I usually leave it on standard which you get a safe mode attack mode and and it's just it's well documented so you know go out and and you can take this home tonight and go play with it and you know obviously like I said be careful what site you're going to but um that is a possibility um so my next challenge was forensic so we have at the state level we have a security Operation Center that sends us sock they're not internal to our organization they are more like the state has a higher it level and they
will send us sock alerts that we have to then go respond to um so initially it's you know when you get the sock alert just go just just to be safe um but we want to get more of an idea of what why we're getting why we're getting infected uh and what if there's anything we can do about it um you know as I mentioned about false posi there could been false closet we just red the machine for no reason you know there a m a m ad that popped up on the website and you know there and it was blocked by blood or uh something else so uh I use mandate Red Line another Tool uh is
volatility um I have usew volatility so I can't really speak to it but a lot of people talk about that quite a bit um and the cost for mandate red line is free mandate has releases tool for free uh Tim CS who spoke two uh two sessions before this one he gave a talk last year at this event heid Augusta on this tool he went more in De than this um so I would recommend watching that if you're interested in it um so now we'll go back to the demo
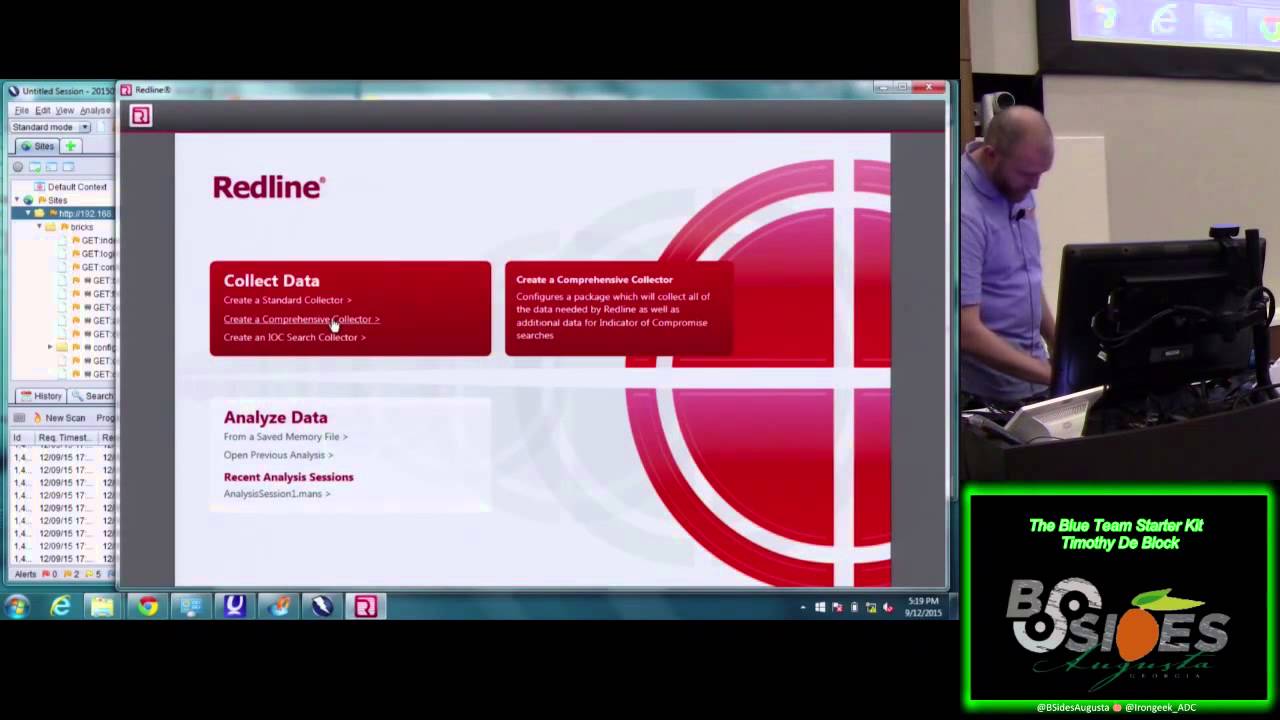
all right so this is this is Redline um what you your starting point is going to be create a um comprehensive collector um once you've done that you're going to have the option to where you're going to store where you're going to have your foric at or your foric folder and then where you're going to U you have like a check box for m so Pi I always check it for memory because you know memory there's going to be more stuff in there um and for people that don't know don't when you grab a machine don't you don't want to necessarily booot it because then you lose information that can be useful for uh looking at this kind of
stuff um so I after you get the session I'm going to show you how to actually launch a a collection um but I want to start this because this this is going to take a minute so you actually after you get your session you're going to click open um here is the package right here so it creates a folder where you define it and all you have to do to launch it test it but it's going to go through and it's just going to pop up this command prompt and it's going to start collecting all the events from your machine and putting it in one blow case one location so you can run the red line
analysis tool on it get a better idea what's going on it's been doing this I've been kind of 5050 on getting this up and running let's close that I think it may because I launched it Trav over time now we'll move
on and this probably has more to do with the fact that I've got I don't know five or six different applications open right now um it is a really good Tool uh it can take it'll take when you when you launch that that colle elction session it's going to take 3 to 4 hours uh depending on how good the the computer hardware is and how how many files are on there um are there any questions at this point we'll come back to that let's come back let's move on no I I was able to test this without it doesn't no unlik Alysa it doesn't require the internet yeah no I I I I've uh they they yeah
they told speakers not to or not to expect Wireless and so I've built like everything I've tested without internet so it's it should work it's just been real Derpy at times um I probably I close out some of stuff like I said we'll move on and if at the end it finally loads we'll or maybe we'll give another shot at the end I don't want to keep people here just just to run Red Line like I said go go home and Run Red Line it's very well documented it you know reading it took me maybe 20 minutes and I was off of running and then you can start going through and checking out some of the
stuff so endpoint security um so we had Windows XP machine still are that work after you know went support there's the the reason why I got this next tool was specifically because had a vulnerability and I got tired of read de um em block that vulnerability so Microsoft's emit is a free Tool uh there's a lot of people that have been writing about this tool um it's that's the interface uh that's simple I've deployed to my ay or I deployed it to my agency um and you've got granular control over all the apps um and actually what I'm going to go run through now is we're going to I'm going to show you how easy it is it
is to install and that you just go click here and while this is running I'll talk a little bit more more about it but um Dave Kennedy has written about this Carlos Perez is L about this the Storm Center has has written about this there are a lot of there's a lot of information about how not only to uh how to deploy this to an AGC you do this at the Enterprise level um but deploying to the agency in an easy way so um I'll show you the the ad doing that but then grab control it's a group you can control with Group Policy by just putting some amdx files on the main controllers and then getting a bin to in
which to to control certain aspects of it that's not going to give you the granular control of em uh that will require an XML file that you can you that you can throw into the log on script and load on to every machine um
one of the things I have seen with red line is I have seen Red Line show me that EMT stepped in before the antivirus um and and blocked the malicious um the malicious action on the machine um what EMT essentially does is behind the scenes it's very technical again very well documented but behind the scenes it's pretty much changed some of the processes that uh malare uses to exploit machines and it kind of guess hides it a little bit in the link version they fix the problems with chrome uh I haven't had a problem with chrome I've had more problems with like Microsoft Office and Microsoft I go figure but optim yeah there's and that's the thing
is that so when you deployed your when you deployed your organization you want to fully test this out for some reason for. I went out of my entire organization fine I tried updating the 5.2 and I dir the developers machines and they were not happy about it I only push I didn't push everybody I just pushed to the all it floor you know use it as a as the guinea pig but um I pushed the developers and their office stopped working and their IE stopped working and and I had to go run around each one and turn it off um so it's a it's a wonderful thing but also it can be very frustrating thing um and they
are like like you were saying if you go to their website they'll tell you what isn't working with what application and it I just put in the base so office um I believe the Bas is like office and stuff like Java and Adobe which is kind of you're your main worry there but it'll go out and uh protect Skype and all this other stuff uh so these are your controls well though one one of the downsides here is that if you have to change these controls you have to reboot the machine uh sometimes you can change the controls and stuff will start working but other times you have to do a full re which is one of the downsides
but here is this is the the control that you have you can see all the protections running here so when a when emit does block something in the bottom right corner it'll use you pop up emit block and it'll give you the exact thing so in the case of my developers I had eaf plus was blocking it for whatever reason so I had to go in and just uncheck them for that thing uh I mean you are unfortunately having to uncheck a protection but you're still allowing all this other St all this other protection uh to occur on the box um and again after you got this straightened out so you want to take a machine from every
Department that you can developers um you know some from the business uh it and and other clients and other areas and go early tested so that you can create an XML file and um um you know use that for your laog on script so uh and then the import thing here you can see that you have also popular software and recommended software so it also gives you some stuff you can import I believe you can import your own into here but um you can import some of the recommended and popular stuff and it's got certificate pinning which I know is uh something a lot of people have talked about so um great tool highly recommend it it's I'm not
going to say it's it's easy there's going to you know it it takes a little planning um and it will require a little management as new updates updates come um but it's it's it's effective because I've seen it and every time you read an article it says new IE vulnerability M you know sometimes at the bottom it says emit mitigates this vulnerability so then you don't you don't have to rush around and go no know um Pat all the
things so uh here are the links um I will make my SL available my website Timothy block.com um and like I said and these aren't even you know this isn't even half my links that I have just for uh getting emit getting it up in within the organization uh there are there's a lot lot of stuff out there and even though some of these do say you know 5 we're up to 5.2 right now um even though it says 5.1 and I think five might be there a lot of those same things so 2014 links there that's still still appli still work everyone get
it all right so patch management um how do I get a flash updated how do I even deploy em um uh you know a lot of I think third party software is one most frustrated things for Security Professionals the P because I don't think there's a really good solution I know suun I've been using suun as a personal uh software for a while now that that goes out and finds the tax for everything but that you know you have to pay I think from 35 to $770,000 to get the full Enterprise version um so one of the tools and I got to give credit I didn't find this tool my sis uh found this tool
while we trying to tackle the problem but it's uh PDQ deploy um it is the only nonfree tool here it is $500 the Enterprise version but you there is a a free version you can take home again like all commun version it's it's throttle um but it's a it's a it's a wonderful simple tool that is just just absolutely worked um and this is PDQ deploy right here so one of the first things you know to get started in here you go in here and look they got a nice long list of vendors you got Adobe up there um you go into again I shouldn't need internet connect shouldn't need any connection oh look flash you know then you just
clicked and all it's going to import you know it's going to import the download for you it's going to create a package read go deploy you don't have you can mess around with uh some of the parameters and stuffff but you don't have to you can just download this and start deploying it so once you once you've imported it you go to the package itself and then you click deploy you can set up schedules and stuff obviously not the free version but choose targets you can do it by active directory you can do it um by pitor which I'll talk about in a second you can do it by you know spice works and you can do it just by the good old text
file so grab a list of IP addresses and just go to town uh that's typically what I do for like my my test User Group have a list of about 18 20 IPS that um I just throw that tech text file and push out uh to the AGC um I can't I'm not going to launch it I don't any machines to patch um but you just let that run for a little bit it's going to take some time I have never had this error out I've never dered anyone's machine with it it's been it's been a wonderful tool um and this is the free version on my machine um the other cool thing about this
um is that it does have Microsoft stuff and oh look there's EMT 5.2 right there so this is what I used initially to push out m 4.0 I also used to push out M 5 two when I dir developers machine so um that was probably that was probably more my fault for not testing thoroughly CU you know I tested it fine on three the three machines I had and it worked just fine but um so EMT seems to if if the machines you need it seems to have a little bit of issue um for instance on this machine um now that I've installed M and I can't for whatever reason launch app
which um so and that's that's pretty much all I had for the the the tools there um as you can see there's plenty of YouTube videos out there as well uh like I mentioned Tim crawler is up there um Simon Bennett Z is everywhere um and not like Z got it actually own uh instructor instructor list where you can hire someone to come out or have someone come out either speak on it or train on it um Tim caros like I mentioned is from last time bid bid clevand had Kevin joso talking about him and there's there's just uh a lot of bid events have a lot of these tools on there so going through
there and then admin Arsenal who is um who made PDQ deploy is uh has some great YouTube videos I got a guy with sits in the bottom right corner explains how to do stuff which leads me to PDQ inventory so PDQ inventory i the cave here is I have not used PDQ inventory so I can't talk to this point but um as we looking to tackle our third party patch management problem the one fault of PDQ by itself is that it doesn't go out and look at what you have on machine so it can't go out automatically update that stuff PDQ inventory on hand is supposed to allow you to do that it allow you to go out
and inventory the machines find out what sofware on there and then you can build packages out that will automatically go out update that stuff so if anyone Serv it's a lot it's a lot like that supposedly at least according to the YouTube videos um and that that PQ inventory is also $500 so th000 bucks potentially could could improve your have in process so again there are the tools um let me before I actually let me go to run red line again see if it actually finish doing its thing yes okay so um so I am investigating an external event um so you can see right there I've got the um so basically you have to do is you actually get like
it'll load up everything on the computer back to the beginning of time um um you want to drill down just by simply putting in the time rle so here I put in uh 817 23 43 and it gives I go by 2 minutes and you can see just within 2 minutes I still have 742 item to go to so the more time you can get um the better uh if if people can get close to that time um so time when you're you're trying to respond to these things is very important trying to track it down but it is still possible um like I said I've seen EMT step in I've seen anire step in
Block Stu so when we're getting these sock alerts we can then go back to the sock and say um yeah it looks like our antivirus took care of it we don't we don't need machine one of my biggest wins with this is that we had uh 30 users get a fishing email with all stuff was invoice a number we had seven people no I'm sorry we had eight people click on it um because the seventh person forwarded into the boss at didn't work in the boss p on it not kidding um uh and so we had eight people that uh got their machine compromised with some sort of exe that was placed in their T folder um so
luckily we do we had some good users that came and informed us almost immediately hey I clicked on this a black box popped up in one away um so it's a matter of getting this on their machine unplugging it from the network and then running it like I said it's it's 3 hours waiting at that points but at that point we're so busy because more and more reports were coming in keep clicking in we're trying to tell people if you see this email delete it we're trying to get you know Mark this spam or you know so we're doing all this other stuff but this we were were able to look through this because we had a general
time and we were able to look through this and find the exe and with confidence say nothing else was in Sp um because we are on all the event machine registry browsing history you can see where like he's an outl and you can see where where the exe got placed in the T folder um so we remove that you know do a couple extra scans just to make sure and then uh we do that on the first couple machines and then we can go grab the other six and instead of them being out for two weeks because we've got eight people that need to have their Machinery we got everybody back working with the day um so that was probably my
biggest win within with using red line and uh I would recommend it and what's great about like I said all these tools is you can go home tonight and and start playing with them you can start looking at implementing in your organization by Monday if you need to do so I don't like said I hav I haven't had opportunities a lot of the expensive tools but these seem to work pretty good uh and these are the most effective so that's pretty much my talk uh I want to thank everyone for sticking around till the end hopefully I got us out a little bit early um but are there any questions any other tools to share yes um I was going
to ask you a question oh you found okay which one
both PBC so uh PBC um is on as pbc.com that's the website for that yeah the I had to search forc okay yeah they PVC stands for Um passion Vision communication and execution the he is silent um but they wanted it be PVC so that's what we went with I didn't have a choice was their Vis I did have a question about the okay all those vended go inst it have you ever seen it have any issues withar that stalls
like oh yeah like Yahoo's thing you know I haven't seen that cuz these usually go out and grab like the raw files and like you can it silently installs a lot of stuff so the Adobe Flash I was able to push out through the day like I I just went ahead and push it if I saw a new Adobe Flash I went ahead and pushed it the users didn't have any idea what's going on I don't I didn't test that out that'd be an interesting to test out though I don't
know right yeah and I know what you talk about yeah where you get yach like yahu seems to be getting in on all that and changing my search engine regularly any other questions does anyone have any other tools I'd be interested to hear if anyone has any other tools to share or if any any of that meet these challenges or otherwise um the one the one I'm reading through now is Chris Sanders uh network security mon implied security uh he presented here earlier today he got a Bookout that that helps with security monitoring um and he's got a lot of tools like Doug security onion um and some other tool some other tools to accomplish that that problem that's much
bigger problem L we n for a while that was
n the put it on
okay anything else if's not we'll uh we'll give a lock you um so name one of the people I've had on the E podcast any one of the people I've had on Thea what you mention well done
I I don't have anything all done yeah I'm all done great job





