People: The Strongest Link - Emma W
Show transcript [en]
there - here and what we're now doing in terms of sharing up thinking with everybody else before I get started you're very welcome to photograph the slides if you want to move for your own reference or share with colleagues or share of social media that's great and if you do share on social media please tag in CSC down there as well as the conference hashtag and we might retweet retweet you if you've been sufficiently complimentary about my presentation but obviously don't let that influence your thinking in any way you've probably thought we are in Jelani art which means please don't take photos of me or particularly don't take photos of me on social media and all my upset people
will get upset I don't like to upset the upset people because they're lovely they don't deserve to be upset so very grateful for your help please in not upsetting them so to start with if you're not intimately familiar with what the NCSC does or our mission here is what we're here for we're here to help with the UK the world safe space little Mike online and we do our work under these four main headings I think we those four main headings are a bit out of date now I think we express it differently but I like these ones better than the current version so I can stick with these and understanding the risk reducing the risk responding to instance
and nurturing capability so the work I'm going to describe today was carried out under that first heading the understand the environment heading which covers quite a bit of a specialist in technical research winner NTSC and so to start telling the story first let's move back in time about eight years before we started working in earnest on people security but in CSG as it was then so if you went back those eight years in time and asked CSG what do I need to know about people in security how should I treat people as part of security what kind of answer might you have got mine included some of these these words and phrases here these are all phrases that
used to be like very common the default when you're talking about people in cyber security and that's still fairly common now more common than I would like personally but we're starting to be were thinking on it's great this is all stuff that is what we used to say ourselves in CSG eight years or so ago because at the time we were just that was the place that we were in like many other people under before that was this one big phrase the phrase that's so big and so threatening I have to write it in red in a very scary font it's the assumption but it's so common so widespread you still hear a lot now I
think a lot of people don't you realize that it is just an assumption quite a faulty one at that it's just taken to be a universal truth for things sometimes I don't think that's true so why why do so many people think this and my theory is that it's because the leaning thinking in cybersecurity because for so long been dominated by technology and technologists technologies are great don't get me wrong we certainly need them inside security but no one can be expert at everything and if you're a deep expert in technology you're probably not a deep x13 people and we need deep experts in people in cybersecurity as much as we need experts in technology just pop up is really
annoying and it's stopping me getting down some of my notes you're gonna miss out on my Hana Harry's so I'm a dog um this is sort of picking up some points from Chris's talk this is keynote earlier and that we a lot of such things in security are a bit broken and we need to really look at how we do some stuff and do it better and I was thinking that listening to Chris talk he knows about this much is getting me going on now he's nicked my picture saying everything that I was gonna say but a much bigger part of me going I know this is fine it's actually really good if you increase it on the same page that is a
good thing and hopefully more people will be persuaded as a result so what happened when we in CSG started to look outside security from this more human centric perspective what started to change well it wasn't long before we realized how disastrously wrong this phrase IP really is so there's an example lots of people have heard if our password guidance I'm very proud that I was part of the team that wrote and published this back in 2015 so now it's kind of a mini case study I'll walk through some of what we learned about passwords when we started to look at them this people-centered way so here are the old-school password rules you know them as well as I do here as a fed
up with them as I am if you follow all of these rules you will end up with what is common thought of as a good password or a strong password using those particular words name you using this process to construct one password that you use regularly most people to do that that's okay and not everybody instantly but most people if you use it to make per say six or seven passwords again you lose regularly most people can manage that they are smaller them proportion of people but make people cancel or do that but most of us don't only need six or seven passwords we're now appoint roles people have dozens or even hundreds of passwords that we're using loads of
places at work in a home and we might not use them daily or even weekly and that really affects our ability to memorize them longer term to keep them current in memory so this approach when you stop looking at it from the point if it's a person you'll have 100 accounts it's really not that reasonable at all so it's not only the password you have to remember yeah it's also the user name on what account it belongs to so that's three sort of separate pieces of linked information with a lot of data potentially so when Cormac Curley whose mother needs the sons this is what he came up with about sort of the impact on
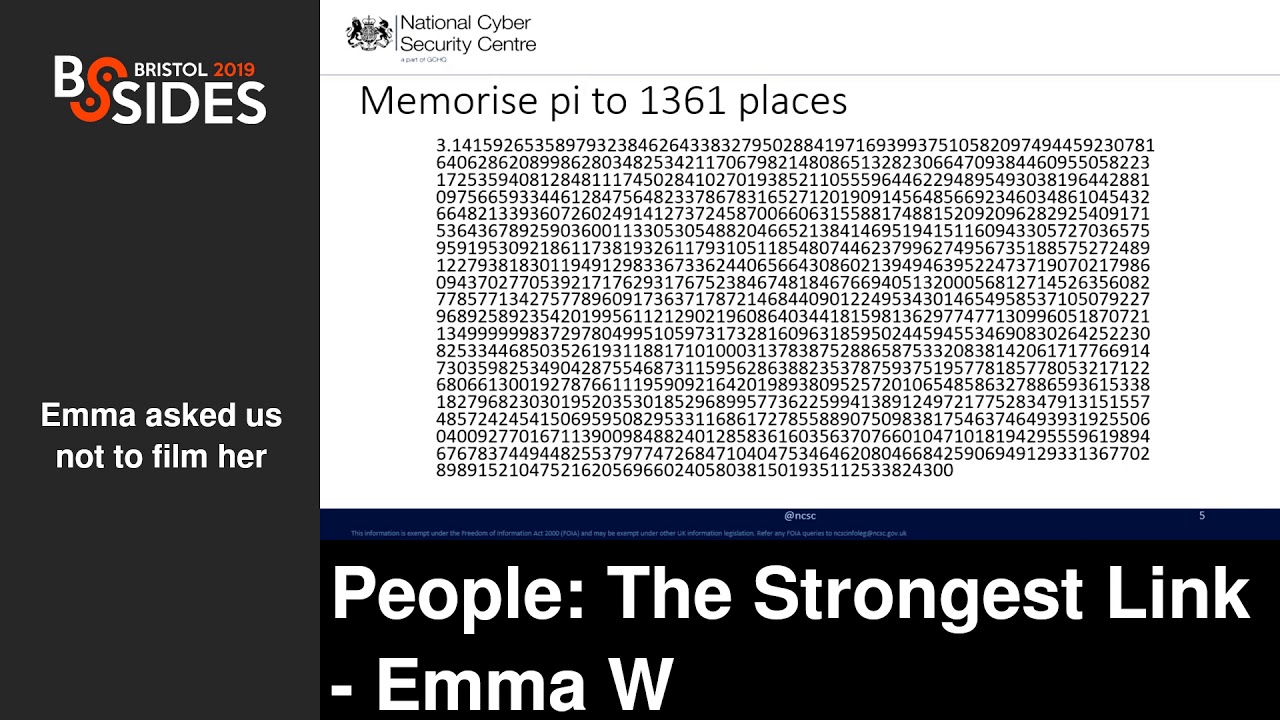
the user of asking them to remember 100 passwords usernames accounts we pass through certainly these criteria it's like memorizing piety to thirteen hundred and sixty old places whenever I say this I go and I bet nobody in this room could really do that and then occasion I give this presentation to GCHQ I don't have to remember not to say that because it's probably stuff doesn't leak in the audience who stand up and start reciting this life's numbers and I think you'll agree most people can not do this just calm and if it weren't hard enough just memorizing that number up there it's not a static one-off memory task it's not just remember that number there
it's remembering a number that's possibly changing because we're constantly picking up new accounts and dropping old ones every so often we have to forget we forget our password Smith to reset them or we find out they've been in their day to breach show you how to reset them or sometimes we are forced to change our passwords periodically for no particular reason except security there is a oh I've looked into this and there is no particularly good reason to think that rotating passwords regularly makes us any secur overall it's just a sort of thing that intuitively makes sense you know when your password refresher password it's got to be a you know possible that the attack is much like to have right so
it's probably better only it doesn't actually work that way when you look into the evidence nevertheless this regular password expiry policies it were the most ridiculously sticky security policies around it's very very hard to get people to let go of it I'm still working on it it's kind of Grand Challenge so this is where common password policies really start to fall down and I would argue it's a good sign of where common security education awareness training policies pulled them more broadly because you're kind of ending up telling people you've got to memorize all this stuff right you can't write it down that's not allowed you can't do anything else to make life easier for yourself you really must not
reuse passwords between accounts you mustn't use predictable password generation patterns that someone else will be able to guess you can't do any of that and if we catch you doing it you're in big trouble how do most people react to that they tend to start disengaging because they recognize that this is an impossible task they can't do that and yet that is what they've been asked to do and that's a really dangerous point because when people start that disengagement then it's quite hard to stop getting back again even before that though I wonder how we got to a place where were asking people to do something this impossible routinely and the answer I guess of course is that
no one ever actually decide to flee decided to because this problem didn't appear all at once it's growing over the past what a couple of decades as sort of online services have become more widespread we've got more and more accounts this problem just sort of crept up on us and so past produce rose and rose all that time and I think we were a bit slow to realize that the world was changing it that way and that we needed a decently differently but it's not completely excuses I think we thought we've missed a lot of opportunities that we could have taken to support memory these problems over the years because if you're asking people to do this
impossible password stuff what tends to happen what kind of things can you see any organization that tells you see isn't working oh I forgot the rest of the other dramatic bit as well as being like remember izing pi2 3260 or places it's like memorizing 17 decks of cards all shuffled together and you know another way of expressing how completely impossible this is for most people so what goes wrong how to use rap to these impossible parser policies again it's stuff that you will all recognize it's stuff we know many people do it's definitely doing myself even now you know which I think just proves it's not a question of Education or motivation or taking security seriously
or anything like that because I've got all of that now this is actually what I do for a living and yet I'm human and if I needed to do some of this stuff to get through the day then I am going to do it so and we know that we all know these things you know these things happen so when we spot them why don't we react more constructively always why don't we say hang on a minute huge numbers of people are breaking our password policy maybe that means we need to look at the password policy we don't tend to do that why don't we do that I think it's because we've already internalized this
idea that people are the weakest link in security no matter what so when you notice people doing this stuff the temptation is just stopped it done so human weakness you know security is always going to be able because people just can't do what they need to do nothing you can do about that just well you know people going to people like and that's the real problem because it stops us looking into question any further which might give us a chance of actually coming out with better answers also it kind of fuels the vicious cycle you know the password policy stays the same people keep breaking it which piles up more and more evidence for the fact that
people are the weakest link and actually it's more that we've been set up to fail at a task that was always always impossible for us so this is like a bit of pretty bad place to being really more importantly how do we start moving out of this bad place how do we stop doing better so now I'm going to run through seven things that we in the MCFC have learned about people during the course of our research the past eight years how these limbs and what we think and what we now say to our customers first of all people are the stupid this comes with a caveat right mostly mostly people stupid you do meet the occasional person
at work is like how are you here yeah very large people are not stupid however sometimes everybody does things that look a bit daft from the point of view of a security professional you look at what they've got how on earth did you make that decision how did you decide that was the right thing to do but actually more often when you dig into it you try and understand where they are their perspective what they know what the assumptions they're making and what they're trying to achieve you can kind of see the line you can see where they thought what they did was a reasonable thing to do they've thought about what they're doing they're doing it for
reasons that make sense to them you may still disagree that what they did was the right thing to do but it's not fair to label it stupid just because it's not what you would do it's this perspective saying again you know everyone everyone is pretty smart biological what they do but no one can be smarter everything and no one could be an expert on everything security people aren't experts on everybody else's jobs and the organizations they work for any more than all of the people and organizations are going to be experts in the security very much as you might want them to be so to understand why and how people do their jobs we have
to talk to them engage find out how they see things so that we can then understand why they're doing what they're doing and what they're trying to achieve you may be wondering why I think this matters that much I think it really does matter it matters because if we start thinking of people is stupid we start treating them as if they're stupid and then that sort of alienation process follows we start thinking things like oh well if people aren't following the security rules maybe they're so stupid they don't even know what the security rules are well maybe we'd better tell them the security rules again and then that'll solve our problems with people not following the security rules only
incredibly it doesn't work like that most of the time our research is showing people do know what the security rules are they probably don't know them off the top of their head because they tend to be quite a long and complicated but they may be important stuff they know where to find the rules they even know who to ask if they aren't sure they want reassurance if people aren't following the security rules it's more likely that that's because these rules don't work for them in some way so throwing the rules of them again just really doesn't help it only makes them further it's a visible demonstration that we know who they are we don't know what's
important to them we don't know how things look from where they stand in and maybe we don't even care that much about what they're trying to achieve you know if it appears to them if we don't care about what they're trying to do why are they going to care about the security rules that we can get important next thing people want to be secure this is the traditionally the point Roman six back and goes oh I'm not sure other ones not remember one again because people sometimes act in a way the makers think the places that the motivations on being secure I think if they do care they just don't always carrying the same ways that
we care and the thing about so they they care but it's not always that easy to transform that caring into positive action that supports security goals so research gives us a quite good idea of how much effort people are prepared to put into doing security well and the answer most people will put reasonable efforts into following security rules that make sense to them which they're able to follow critical point and which support them in achieving their prime models at work however their definition of what is reasonable efforts put into security might differ from ours and their primary goals usually differ as well primary goals as security professionals is to enable the business by securing a
business and Jesus primary goals it's a bit simpler than that the main the primary goal is always to get their job done whatever the job is in the organization being secure you know the digital care about it but it's the secondary goal underneath that primary goal in an ideal world the primary goals and second your goals would be fully aligned you know and you could do security in a way that supports you getting your job done but in practice these goals aren't usually completely aligned because it's hard right next one people are busy isn't everyone busy I know I am everyone's busy we often want people to spend more time and efforts on security but most people don't feel they
can easily do that usually they're pretty fully occupied during their day jobs like I said it's kind of about goals of motivation a lot of the time people's day jobs have been more important to them you know on a day to day basis so there's a question of motivation and reward as well if you don't do the tasks that your boss really cares about you doing you can be pretty sure that that's not gonna end well for you that they're going to notice they're gonna pull you up begin to get in trouble as me some sort of sanction with security tasks that's a lot less certain because partly because I sort of the immediacy isn't
there the consequences are something you do on often immediately obvious security tells people not to do all sorts of things because security we don't always explain why in enough detail I don't think and also there's this immediate you see problems so people learn from experience that you can actually do a lot of the stuff that security tells you not to do and the sky will not fall in straight away so use a weak password probably nothing but I haven't was stopping any important happening we use a password from somewhere else you know so nobody might ever find out if you click straight through a pop-up warning on your laptop from experience two and a half years of having this laptop nothing
bad has ever appeared to happen when I flick through that warning so why would I take the warning seriously well if you let someone in the office behind you even though they haven't got their badge on you know they've got the hands full you want to be helpful you know all these things that security or Draghi you didn't do people are motivated to do all of those things all of those things work for people on some level so just telling them not to do those things because security doesn't work breaking the password rules makes life manageable clicking through pop-ups lets you get on with your work your important conference presentation letting someone in the office behind you
lets them get on with their work and it's helpful right it's supports teamwork teamwork and cooperation with social animals we get stuff done as teams you know none of us are gonna last long at work if we don't look out for each other the organizations although the last long collective success depends on working together productively there's also a bit of a problem it has sometimes we seek to get people's attention on security stuff people are really really good at paying attention to things that help post things are important and we are increasingly good ignoring stuff that we think doesn't help us we kind of have to be good at this it's a survival tactic no we live in a world where we're
constantly bombarded with all information promotes most places security is just one of those many things that demand our attention day to day and from many people's point of view it just doesn't deliver those commensurate rewards right now so I think for securities to succeed really we need to get a bit more picky about what we ask people to do and when we seek to grab their attention to take them away from those primary tasks we need to make sure it's really worthwhile so be a bit pickier about what's really essential and what's nice to have and would be great but actually it's going to take some energy so is it really worth it you know if we focus on the
smallest possible set of essential stuff and far more likely people will actually find it achievable and actually going to do it so this is a lot of sort of stuff in defense of people you might be thinking oh no people can't do anything wrong from this woman's point of view but let's sort of talk about that a little bit more people make mistakes of course we take we're all human we all make mistakes we get things wrong we miss stuff we're driven by our emotions at least as much as we're driven by our intellect we rely on cognitive biases and heuristics which you know again they've evolved they're there for a reason they helpful they help us a lot
of the time but all the time sometimes they make us get stuff wrong and it's important to understand that you know look a bit more closely at when people make mistakes and what's actually gone wrong so that we can understand the underlying causes which really happen and if we understand the underlying causes we're much better place then to find better answers so if a whole lot of different people are making the same kind of mistakes again and again probably doesn't really indicate much about those people it mainly means that the thing that they're using isn't very well designed for people but we've already seen how this works with passwords you know there's a very common
set of workarounds that you see every single workplace that you have go it's not a sign that passwords are working perfectly in humans and especially failing at it the design that the passwords aren't working very well for the people and therefore the passwords aren't working I have some time to think this about organizations you've got we need your Kony and approaches to people who fall for phishing emails a day some places have disciplinary measures for people who click too many backlinks you can even get sacked for clicking too many bad links I do wonder if they thought this through you know because the logical ending point of that process is that your organization will have
hired and fired everybody in the entire world and however you have left will still be clicking badly it's because you can't train people not to take bad links we've proved it with science however hard we tried we will not stop all mistakes happening but we can cut out a lot of the nucleus and the stakes you might say by talking to people about what they need and how they work and giving them tools that work for them right I'm slightly nearer the end of the talk than I thought I was going to be at this point so I might if you try and cut a few bits out let's see all right this is a paint not to spend too much time on
people did nothing sometimes on purpose of course today this is not really the subject of this talk I'm talking about user behavior at population levels and at population levels and most people are trying to do the right thing most of the time so what's the most important thing to say I had three important things to say I just say one of them I think and I'll hear hone in on signal-to-noise ratio you know if we do this stuff I've suggested around making it easier for the people who are well-intentioned to do things right it's a lot easier to spot the people who are setting out to do wrong because you have all those false positives to wade through that
sort of main point of that punishment doesn't drive positive oh hey Lee it's already talked about sucking people for clicking finish fishing lakes and we've got mountains of Criminology research that tell us that the sort of relationship between behavior and choices and sanctions it's nonlinear it's not obvious you know it's not as simple as in still penalties and then but behavior won't happen it just isn't you know otherwise the countries that have the death penalty for serious crime that have hardly any serious crime and that's not really the case this sort of proach assumes that people are rational actors and that we always act in our best interests and that's not how people work at all
you have things the way they split approach actively does harm is if people are trying to do the right things and you punish them because they've managed to do the wrong thing then it doesn't actually make them any easier make it any easier for them to do things right they'll be motivated to avoid the punishment in future sure but if you don't give them a viable alternative route to reach their legitimate goal then let stuck between a rock and a hard place you can either stop doing this it's getting even punished which you might think great well what the fat thing was actually really useful for the business what if it was supporting business goals or they can keep doing
the thing but they'll try harder to make sure that you never find out again if your instant numbers might go down might look like a good thing but not really if you've just driven that behavior underground if it's happening but you don't know it's happening you can't you can't manage it come on a trick you can't do the risk it's not good things makes it a bigger problem finally a lot of people's future kind of stuff focuses on awareness awareness as an end goal and making people more aware of the threats more aware of the risks and occasionally they get around to what are you supposed to do about the threats and the risks but we don't really didn't
go that far the problem is awareness doesn't look or action you know there's a lot of steps between the two and it's not an easy thing to achieve I'm going to go to this but I just randomly pulled this model off each day it's one of many models that are available and just to illustrate the point that there is a lot of stuff that needs to happen after awareness before you get to sustained behavioral change this is kind of something that we all know in daily life you know who knows how many fruit and veg you're supposed to meet your dates hands up anybody Oh a couple of people president I think both excellent okay so
everyone knows you're supposed to eat five free edge a day or patiently seven we always do that we all know smokings bad for us some people's make anyway we know that speed limits are there to keep us safe that sometimes we still speed it's not an awareness problem we know all this stuff and we've made a different decision anyway or sometimes not an active decision so it's complicated turning awareness into positive action right so this is the summary of the guiding principles we've learned about people the past eight years and this hopefully gives you the insight into our thinking on people's security so now I have to move on so there all right I'm vaguely convinced
but what do I do differently bits and I've got five minutes left so awesome I actually may be flown in five minutes but trying to punch you so the first important thing and I think I've gone on about it a bit already listen and learn and understand good security isn't achieved by just imposing our own ideas of how security should work in our organization it's about that too you way engagement listening and respecting how other people say things and what they're trying to achieve at work then helping them to do that in ways that we can live with ways that may not perhaps be totally ideal MA point if you but is it good enough does it get the job done
does it allows us to manage risks alright if so can we never there okay let's move on there's always more to deal with we have to recognize that people are the experts on their own jobs just like we're the experts on security and the right answers we'll all be the one that respects their job goals as much as it respects our security goals you can engage with people in lazy different ways I've trapped a few ideas up there because people always want ideas where to start but really it doesn't matter what you do it's how you do it so signaling trust and openness this is one of those sort of softer skills that I don't like to call soft skills because
they're actually really hard core business skills is a term I prefer so show people that we listening show them that it's safe to talk to us get out there engage on their terms build trust build rapport do all of that and try and have a productive conversation with them don't forget people quite often start in a bad place here you know they might have experience of trying to talk to security people before and even maybe getting brushed off or even coming away with some sort of sanction because you've gone and said like I had to do this thing I know it's not really in the rules but I was trying to be the right thing can you help me do it better and
security god no oh how you did the wrong thing breach you know I think I have tons less less these days I certainly hope so but it's not not impossible reaction so we have to do everything we can really to talk to persuade people to talk obviously to us because if we aren't having honest conversations we're not going to find out the right stuff and make it be better and reflect back this is a really simple little technique that I learned doing counseling training actually but it's astonishingly helpful in that rapport building thing as well as on making sure that you have really understood what some of this said to you so it can be as simple as just saying
okay this is what I heard you just say this is what I think it means is that right the key bit being is that right give them a further opportunity to go to oh yeah that's emotionally right but there's this thing there or now actually you've got totally wrong able to stick is that thing there so it's part of that actually signaling that you're engaged with the person that you're told do you really want to understand their perspective and you really want to help make things better find the underlying causes the security problems really important look beyond the superficial behaviors and figure out what might be driving them which as you said might not be what you think you know you might
have to get underneath your assumptions find out more about how other people are approaching stuff what they know the things you know that they don't know figure out all of that and try and trying to get things right when I say underlying causes people always go oh yeah root cause I know all about root cause I haven't got time for the full root cause Rand which is quite shame because it's a good one but a few very causes is there is plural there's never a single root cause there's never a single thing you can point at to say this is why this thing went wrong this is I think easy to explain if you flip
it and ask for you know people to think about something that went right there's conference for instance mall here today what was the root course of this conference working what was a single thing we can point to this the reason why it works those they're single thing there's motive things latest things all have to come together and line up to get us all here to make sure we had rooms and lighting power and food and all that stuff and it's just the same when you're trying to look for a single root cause for why something went wrong it's never that it's always an alignment is enough things that went wrong and you know that's the only way it's the positive
thing because it means there's always more than one chance to stop a bad thing happening it will stop having a real bad effect and like we often say if your entire system can get owned because one person clicked on a bad link it's not the fault of the person who clicked the bad links because you've got a lot of opportunities to stop that doing damage and evidence-based decisions then Chris talks about this quite well earlier so trying to be brief we don't always collect the right data insecurity we don't collect enough of it we collect it for different reasons like proving to the board that we do something something you're good this book's mean like
fishing simulation training packages they're quite an easy low resource way to do something to generate some data you can easily show the click rates go down over time I think it's all great looked like it's working well something's working but it might not be the thing you you may have been able to train people in a sort of short-term way to support your fishing training links and not click on them doesn't actually correlate with any decrease likelihood of clicking on other kinds of fishing links that look different so it's not the same not the things think right precisely five minutes left let's oh this is an important one budget people's time and efforts quite fundamental change in approach familias
because we used to thinking of people as this sort of relatively malleable resource with loads of capacity to grow and change and do these things and of course people can't do that and people are among it amazingly adaptive and innovative but we can't do everything so we have to focus our effort on things that really mask to us so we have to get in security get used to thinking of people's time and effort as a resource like any other kind of resource and then enhance that call the compliance project which I really recommend going reading about it puts in quite good quite good terms but basically like any other kind of budget you know it's valuable and if
you spend it somewhere you can't spend anywhere else and if you prove to have spent it all and all the thing less wasted you putting it back so thinking about people's time and effort in those terms I find you really helped fixing the environment not people have sort of some lawyers talked a lot about this I think already and we always tend to default to trying to fix people because they look like the thing in the system that did something wrong or the thing in the system that's easiest to deal with and easy to change and neither of those things certain can really true people tend to while people in my circles anyway tend to go to baby change as the
quick and easy fix for anything that's wrong and it's not quick it's not easy and it only has marginal effects really if your intervention delivers like a 15 percent change in behaviour in the desired direction that's a really good result no but there's still another 85 percent to worry about some direct thing and it's quite difficult to translate any short-term success into longer-term sustained behavior and learn from what we've learned why I'll show you this really quickly and we need to do we quite often do single loop learning for like on the right-hand side of the picture we figure out what the problem was we decide how to solve it we solve it we move on to the next
problem but the double-loop learning there is about introducing a bit of reflection on how we solve the problem and what we learned maybe what assumptions we made to start with and how we need to carry that thinking forward into whatever we do next ah next right so this is the summary list of things I think we should start doing differently to really help people help help make our people the best assets to security that they can do in the last couple years in particular we're hearing more and more stories of where people are doing this stuff doing it really well having great effects we're trying to calculate as many of these as we can to case studies on the
NCSC website because we love to prove success and we love to prove we'd love to show real world implementations of the approaches that we suggest so it's it's good I think it's going in the right direction we need more of it I've got a very very quick list of sort of evidence some of the major academic sources that have gone once a day if you only have time for one read users are not the enemy that's where it all started it's great oh god I gets highlights this is very interesting this is just like a proof that yeah we've have produced a lot of guidance based on the principles that I've talked about today and we like to
think it is pretty good you can go read it on the intensity website and later to know what you think via the inquiry service or treatise will come to us on LinkedIn or in vanilla right and that's it so much have we got time for any questions or feeling weak with velocity area straight out the door right right is there anyone present Oh contrary thank you very much [Applause]





