Introduction to OWASP Juice Shop
Show transcript [en]
you everyone then my name is Tim Cole Carter and stay hopefully I'm going to give you any destruction into shop just before we dive in then a little bit about myself that's prime so in the corpse information secured with steam pain so in Manchester I spent the first part of my career working as a software engineer so doing kind of UNIX shell scripts you saw a bit of Java on C++ until I finally saw the IR moved into I've done some instant response but most I would do in ability management say do what you love and univocally life and that's pretty true for me to be honest although I've got to say that because my
boss is somewhat but generally you know I do enjoy what I do to make a living so this is my fourth piece at Manchester I've been every year since 2016 I've got stickers I'm up top I think a lots of stickers or something so if anyone's got a 20-17 stick and I like to give me a sound leave then please let me have a look outside but there isn't one so if anyone's got one then please do let me know so please go easy on me if you've got any fruits to throw anything then save it for tracks 1 & 2 look at me I'm a great the idea is more to say you know
these are some of the sorts of things you might want to do if you want to go down the vulnerability of NSS to interrupt so remember when I do my own CP it was around about the time of b-sides 2016 now I'm attracting to a guy who already had his I got some good hints and tips and advice from him so by all means if any of you are currently studying for any of these or thinking about it have any questions or travel and you know feel free to grab me at some point for a day and asking questions of yourself where I am okay so this is an introduction then so just explain a wasp and juice apart so what
are the open web application security project the state mission is to make the internet more secure so they do that through a number of ways for the OWASP top 10 which i've not got a slide on but it sort of ties in quite heavily with similar stuff you see in juice shop they also provide some tools so there's at attack proxy you can use for some other stuff about to do and book-balancing things like that and then specifically for any bug bounty hunters is a maths which is a really great tool that can make bug bounty a lot easier chapter so I went to every West Manchester event a couple weeks ago which was a secure code
where we think oh it's by the BBC there's a really good night now so in terms of - shotgun so juice shop is an intentionally vulnerable web app so the idea is to sort of developers do of the ways where they going wrong and doing bad things you can also use it for sort of senior managers and stakeholders to show them the effects of some of the vulnerabilities you find in modern web apps and just how much access checking game if you're starting out then you can use an individually to test yourself against some of the challenges to see if you can hack them and learn basic new skills and then if you run it for a
meet-up you can run in a capture fight mode before we in 2019 on the other disclaimer now I've got two disclaimers for you so number one is spoilers so that's just that you know it's an individual challenge you can do it yourself now when I'm doing stuff like that I don't like so half the answer spoil for me so I never read the walkthrough so if
[Music]
you don't do them on systems your own this recovering permission to test otherwise you might begin to visit from these guys on a Monday morning okay so it's plates I've got a live demo so I'm not about to make a fool of myself safe confirm of the end right
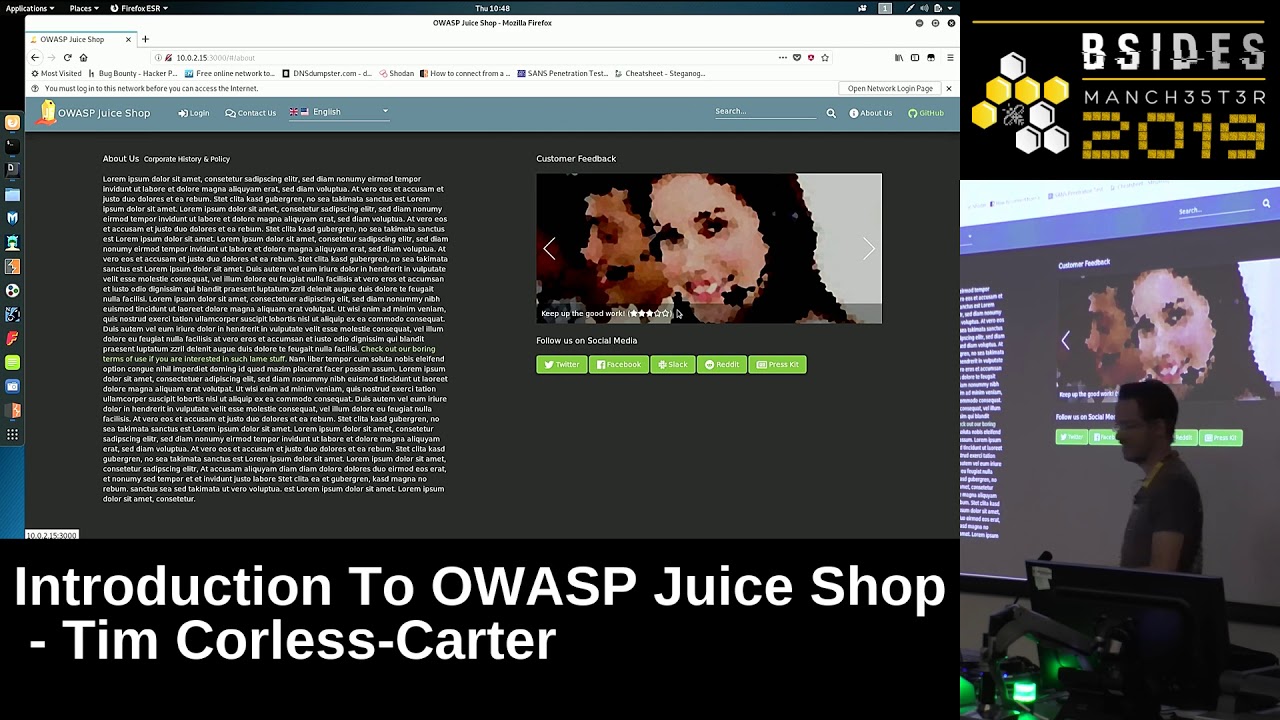
so why is a VM ruining college so for anyone that might not be aware it's a version of Linux it contains pretty much every pen testing tool known to man it's going to use by pen testers on their engagements where they go and try and hack things I can use it for bug bounty or challenges like juice shop and if I like that so when you run it look quite like this you download it as a node.js application then you with NPM 3000 which can go visit it on there we go now whenever I'm hacking or doing any challenges like this I have various rules of thumb the first one is whenever I find a web application are a couple
tool against it called herb and der search so if you verify over a couple terminal windows to do that another commands and I'll explain what these do the hell dot 0 dot 2.15 3000 matter fact I always get a syntax wrong sort of bear with me so David search take a word license and try everything that word list against the first slash of the web application the idea is to find anyway the developer might have left any files lying around in the web directory or anything that generally just shouldn't be there now they're gonna take a little while to run so while they're running we're going to go and enumerate the web application so by enumerate it's just kind of a sake
depends FC tool for just looking around try and understand it whenever you're doing anything like this you should always go and figure out how it works or JIT remotely and how it's supposed to work before you try and hack it because I think just if you know something's supposed to work then you can see what it's not working as expected and see if you can find anything any gaps any security issues so first content to shop works just like any other sort of normal website there's a list of products you can see if you click on one it tells you what the product is it gives his prize description and also some feedback so straight away my hockey fight sensitive
thing because you can see that there's YouTube so I might wanna come back later and testify my SQL injection I'll cross my script in any of those the other thing that Springs out through that is you can see some of these left to comment but it looks like by leaving a comment they've left their username you can see it's an admin username so again you put that in the back for later because then you might be able to brute force rlogin is a I'll do something interesting with it so if it points up and have a look at a couple of others so again just a couple of little comments these are fairly similar euro
fresh shot replicated and cool also in to shop so you've got a login page jubilee so you can go on a hog in manage your profile and track your orders and a lot of things there is a Contact Us page regularly you've got some a feedback so again lots of user input that again I'm thinking SQL injection cross-site scripting you can see there's a ratings mechanism so it's a CAPTCHA thing which is interesting we can go see if we bypass that later so the system then is capture setting here which isn't quite working at the moment and probably because we're running did the search in the background it's just hammering it's probably take you too much resources
language if you up to I'm not going to do that except for development we ought to get back to our need to be so search bar notorious for common vulnerabilities like cross-site scripting tests and so SQL injection so I'm going to combat start and have a look later and then find about was page so the thing that springs are three votes that is it's just got a standard lasting sex so if the developer has been lazy enough to not report any proper comes in there what other corners have been cut the other interesting on this page is all this feedback here so you can see the steroids in the comments that sort of map spiked to contact us page so can i
abused in any way to make something from the contact us page properly and do anything interesting that's just so you can call the project if you want to so with the web application you raise it more go back under search now on they are still running so what I'm going to do is I'm going to cancel them both they're with me Peter style I've got a coupon prepared earlier so for my notes on this is whatever you doing anything like this you should always take very detailed notes so I need to keep note where you can see in the top left there I've got sort of a methodology so I know what tools to run talking the final
information it's if you're doing this as a pen test ultimately on you do pen stuff you're getting paid for the report at the end send y'all have I screenshots on methodology all this stuff stored if you're down for book balance the same thing you've got a report later to show people again if you're doing it for yourself you just remember how you've done it and you can see it later on so looking at Derb then the one that springs up from there is slash robots.txt so in case you're not aware robots.txt is a directory if you put in the web root of your directory to stop search engines like Google and Bing ultra Vista if Alta Vista still exists
from indexing directories in your web application so I can manually go on ignore those two green things I'll explain or there are a minute this robots.txt and straight away you can see the developers disallowed you from visiting the FTP directory so you know that to me that's like a red rag to a bull the search engine from viewing it why so I'm gonna go on a visitor so there we go by visit a few directory you can see is left a bunch of stuff lying around and the one that immediately jumps out to me that is acquisitions to MD so MD is a markdown document format so it's kind of similar to HTML and it's
a flat file and you specify various markup commands then when you open up open a web browser it sort of makes it pretty readable so if we have a look inside that top you can see it says this document is confidential doing on this route so it begs the question why I left it lying around in the web root directory so if you read into the document it says some stuff about we plan to require several competitors which I guess if this was a PLC is probably share price impacting so the entire infrastructure is getting sucked so if it's that one so nice things about you shop when I go back there don't let me down when this loads in a second
you can see these green bars do pops up little notifications on you and yourselves a challenge so you can see if one is you have successfully access to confidential document which is taking an FTP directory the two from earlier right ignore them was because I'm running Durbin the background there's just a lot of generates and areas in the background and that we solved a couple other challenges by default okay so back to the output from Durbin searcher so if you have a good day search one that immediately springs out to me that it's a dot well-known security dot txt so similar to robots dot txt security stops exe is a fairly new thing in comparison
so I can't sidebar people watching this is a fairly new thing in comparison the idea is to file security researchers wire to go if they find vulnerabilities so anything wrong with your web application you think that like an email address to say some details here and except in this case it's although it's notice of the presence this scoreboard so as before I'm going to copy that at the end for do shop now this one always I have no idea why so while we're in any questions this point I should say the paths to before walkthroughs before I came in here to have a quickly through the walkthrough just to make sure what the saying wasn't a load of rubbish
actually the way they solve through two previous strategies they're confidential document and school world one is slightly different so they do it through reading through some JavaScript files I'm showing we're showing certain endpoints it does also say in the official guide though feel free to use County and I've read some other tools in that which I guess it's just what we've done and you know whatever works so again you can see you've got a nice little pop up no idea why it's done it twice just tell me I found the scoreboard page so the scoreboard page is where you come to find details of the rest of the challenges that exist in jus shop and you've got various levels
ranging from trivial easy medium diabolical I think might be very helpful if you do get stuck you can hover over them and it gives you a bit then I decide there is a walk through the one that makes me off on here is find the carefully hidden score web page which is on the scoreboard page so I guess it's kind of like a recursive anything so the next one I want to show you I think it's one of the easy ones hey it's a login with the administrators account so I'm going to leave this tap open so I can refer back to it later and open a new tab sorry sorry did I enumeration there's a login page icon to
the login page and we also saw we think we've got a valid user name so we had the admin that you siphoned sure try it doesn't work so what are the reasons sorry that was a bit awesome is they provide a bunch of resources they provide prevention sheets and evasion cheat sheets so there's an escalation teacher which contains all those vascular infection payloads so what we do now is going to take one straight from that playbook the idea of that by the way they're not encouraging people to act the idea of it is if they tell you how it worked then you've got a better chance of writing code to defend against it so by the way I should say
another sequel and I guess it's just a personal preference thing so I always say SQL I except in one instance which is if you thought the film about the man that fixes databases was good just email me shop password is equal to whatever if that returns one then it seemed that survived again it's average user so let your login to the application so we're going to subvert our now fired in this SQL injection field so we've changed now to something like select staff we users where I mean who I user is equal to AB juice - showed up at the apostrophe two colors a username bit or one equals one so nice 11 in some sort of weird
parallel dimension one way is equal one value eight so true and - - comments out the rest of it so at this point it doesn't matter what you specify for the password you can add supercalifragilistic so I don't show you what matter it's gonna log in because it's ignoring the rest of the query so if I hit login you can see it so if you successfully solve the challenge log in as the admin you can EE very in a second when it loads so I can go and see the admins profile now I can change their profile picture if you want to I could go on change password there's all sorts of stuff I could do I'm not going to do
that because I'd mess up future challenges but it's there for you if you need to okay so the next one I wanna show you was there was a devastating zero stop feedback to the store you can give feedback and what I'm gonna do now so if I just type in the zero feedback if I get this wrong the correct answer so 8 minus 26000 so it's gonna be 60 is length so they won't like me because I'm not specified to start with rating so if I give a star rating then something becomes available but the task is to submit a 0 star feedback back to 0 it wrong at me I can move back to 1 I can
be about 220 all at me if I hit submit wrong answer to capture if you refresh you get another country like 1 + 6 cents out 61 is that great 60 or 70 ok so again you know let me submit it because I'm not specified to start waiting so if I feel like generous and give them the 5 and hit submit you can see thank you for your feedback and your 5-star rating our mission was submit as a our feedback starts not going to cut it survive 12 an open fire book I used to be caught fire book I think it's called something else now but you know old habits die hard or whatever what a great teachers tool is I talked
other networks up well might have to resubmit that so I can see it cool I might have to do another one just comes up enough 3 - 3 - 1 is going might as well I think so you can see that when I submitted this found the parameters you can see everything that I've submitted that sort of thing I can see it as a success so there's also another great tool in fight book called edit any reset so if I right-click and do edit in recent you can see it pops up a window where I can change the parameters and it's as simple as I give them the 5-star rates and that suffice I'm sorry in the
waiver so if I change out the 5 to va0 and hit submit let's go back to the top I'm a completely new way of felt sorry side part hit Send so you can see it tells me I've submitted a devastating feedback to score I can doubly verify that so if I click on this again I go to response you can see it's give me a response for success I'm true and then I can doubly verify that or Tripoli very far away from up see this is where it's gonna start not only you can see these are all the feedbacks and as a scroll along eventually so that's a 5-star last minute you've got one that's not that's
a zero-star feedback that was submit really excellent so the next one wait to show you was a document object model inscription attack with particular cross-site scripting so the search bars a counter a prime location for things like cross site scripting are an SQL injection so if I just type in the search bar test and hit search you can see that what it's done is pretty much just spit out pretty much what I put in so again you can use Firebug or their fields whatever it's called there's a really great tool that way you can submit an element and if you click on that it tells you exactly as I element the bear is in the HTML if you
can click it properly so there you go you can see that taken exactly as I needed to so I can do my test start by adding wrapping it in HTML and behind sex you can see I want to do that it's now underlined it and again in the HTML you can see it's got underlined so while I'm going to do is use JavaScript that it showed me so again these all verbs I'm going to take that and this time search for and you can see it scripts inbox and it's storming the background of successful yourself the challenge begins great what's after we world impact of that what can you do so my favorite as follows so the document dot cookie
function on keyword however it's called in JavaScript it shows the value of all the cookies so I start page so if I hit enter it's telling me the value of the continue code cookie what you do is send that back to an attacking controlled server they would person's cookie value they do a cookie injection which is why you take that value cookie go and log in as empty your masquerading so effectively the interesting thing about this is if you look on the storage table does actually so you've got the i/o code io cookie sorry and the continue code cookie but it's only showing the value of one and the reason for that is I owe one has got
HTTP all these sets are true so HTTP only it was introduced specifically to stop this sort of attack it means that stuff like JavaScript can access cookie values now if you were to see cross-site script in a pen test report or vulnerability scan usually to medium sometimes a high depended is if you'd see she's feeling a lack of hg3 honey and a pen test report is normally like although but what we've done there is combine the two together to give a different impact and it's a good example of why you can make vulnerabilities interacts to do cool stuff [Music] okay cool that's what I want to show you I think it's a game bear with me I'll
find it it submits and our customer feedbacks within 10 seconds so I mean you see my dodgy maths well I've been to fill in so if I close these so one of the things I'm not showing you so far is a burp suite so it's a really great tool and the boat for you guys head says come talk to me it's awesome this has got a number of great features so I'm sure something other one is quickly just to show you so eight plus seven times ten is 87 I think I'm getting better no thank you so you can see in burp suite that this line is where you sent the feed but what's happened is why are
you sending the feed back to crest costs so virtually acts as a proxy so it sees all the requests as they go from client to server one of the great tools inverted lupita send through pizza so this does exactly what it says on the thing it repeats squares so I'm actually just gonna do one two three four five six seven nine and there you go you can see the background to shop which pops up saying you've successfully solve the charge I can definitely verify that if I could see about was page what starts fail at the end it's gonna take a while to load I should say if you're interested in this sort of thing if these bikes are
something interesting there is a CTF run alongside besides Manchester today you can find it on Twitter on phone defend so I myself you the guys from my team are taking part so the more the merrier we could see some other people on it we might even be Wed another moment I'm not sure so I can use your outputs and feedback so I think it's all so you can see where you - you've got one two three four five six seven eight nine ten and one for good luck so the one for good luck was the one I did just get into burp suite so I could run it through the repeats it up to show
you so hopefully it's giving you a favor you can see from the scoreboard that you know there's a whole bunch of challenges in there there's something for everyone really so the easy and the trivial ones you know pretty much anyone can do with a little bit of learning a bit of trial and error the diabolical ones to be honest I bothered attempting that for everyone it's a really great tool you should definitely go and check it out how does that happen some questions afterwards if anyone has one book with that handle so thank you for listening and enjoy [Applause]
go on don't go I said there's a Java version is also because they used to be one called I'm vulnerable web app tvw right how's that used to install there's no another the wasp one but you can find that I'm Metis fireball and that has literally got a charge for each of the our top tens is SQL injection this cross-site script and it is a cross-site request forgery there's all sorts and that's a really good one to start a cookie tease oh yeah yeah so what's going on that if that's okay I've got my sister is client-side validation so it's a little bit of JavaScript to make sure you've submitted something what it should be really doing this
server-side validation so when you submit
yeah there's nothing checking to say okay is actually fired capture and it should because JavaScript and kind side validation is really just to defeat you with things like Burke's really things like that feels nice that's why it works thank you [Applause]





