2016 - James Kettle - Hunting Asynchronous Vulnerabilities
Show transcript [en]
welcome to hunting asynchronous vulnerabilities you may find it concerning that as you browse the web every fragment of information that you're browsing gives off is instantly fed into scores of back-end system for advertising and tracking where the state of is mined processed and mangled for all it's worth or you may think that that's some serious attack surface if only I had a way to harness it in this session I'll share with you a range of techniques for mining invisible attack surfaces and finding vulnerabilities regardless of where they're hiding around 18 months ago I was asked to pen test an e-commerce website that sold designer clothes and there was a staging version of this website but it was completely broken so
I had to test the night vision and this meant that I had to use my own valid credit card details in order to do purchases and as a result I was being extremely careful not to accidentally purchase say a thousand pound leather jacket for myself and after spending the first morning testing I'm not really getting anywhere I went out for lunch and when I got back from lunch I found I had an email it said dear James congratulations on your order of this fine thousand pound leather jacket and I panicked slightly / then thinking about it I couldn't have actually paid for this jacket because at this point I hadn't entered any credit card details
whatsoever so actually I found quire serious vulnerability it was possible to buy items for free the only catch was I had no idea what had triggered this vulnerability I had no idea what had caused it and the client probably wasn't going to appreciate me going hey there you've got a critical vulnerability but I can't tell you how to replicate it or how to fix it it was only after three hours of reviewing my burp suite logs that I figured out what the cause was which was simply a issue I'd added this item to my basket during the morning of testing and the scanner there had been running over lunch time had replayed a particular request which had bought this item so
that was cool and I told the client and they were fairly happy but it left me wondering what would have happened if there was no order confirmation email some random stranger would have got another jacket but I would have never found the vulnerability in effect this email was a callback from the application to to me to my mail server to let me vote to let me know that it had a critical vulnerability and these instances of vulnerabilities that happen behind the scenes that don't present immediate evidence like directly at you that can happen with plenty of other vulnerabilities that isn't just limited to session handling so what I'll be talking about is oh I'll be defining
what these vulnerabilities are that are so hard to find and what it is that makes them difficult to identify and then I'll be looking at some techniques for finding them and applying that to some of the most well-known and widespread vulnerabilities out there finally are we talking about some of the hazards with these techniques and answering 5-minutes questions so the core problem with these vulnerabilities is that they're invisible compare them with your classic sequel injection vulnerability with the most obvious sequel injection you're given application a single quote and you'll get a sequel error message back and you go great that's vulnerable to the sequel to sequel injection and you proceed to exploit it some other the server might
be configured not to give you sequel error messages but you may still be able to find the some sequel injections by using a payload like all one equals one and observing the effect that has on those on the output that you get on the website but this technique also doesn't with asynchronous vulnerabilities and finally with some of the more advanced sequel sequel injection vulnerabilities you can't change the output that you get but you can tell the server to to do something like sleep for 10 seconds and you can time there were spots but once again for an asynchronous vulnerability this doesn't work what are some common examples of of where asynchronous vulnerabilities can arise well probably
the most one is is a vulnerability in a cron job that's just run maybe nightly say say a cron job that does a backup of the database nightly this cron job could be could be vulnerable to sequel injection or show command injection or various other things but as the tester you're not going to get the output of this cron job and if you inject a time delay you're never gonna you can't notice it because it's executing in a background thread some other issues might not be triggered in the background thread but they might require some kind of a event probably the best example of this is blind cross-site scripting where you give an application in your
cross-site scripting payload and it never gets displayed to you it's only visible to some administrator somewhere in some back-end that you can't see and you don't have access to and the admin might view that payload two weeks after your test has finished so how do you find that kind of issue and finally the techniques that I'll be talking about can also be used to identify other issues that aren't strictly asynchronous but are still very difficult to find for example it's a same application is processing your input as XML and it's vulnerable to external XML entities how do you find that vulnerability if the application doesn't display you the result of this processing you there's no
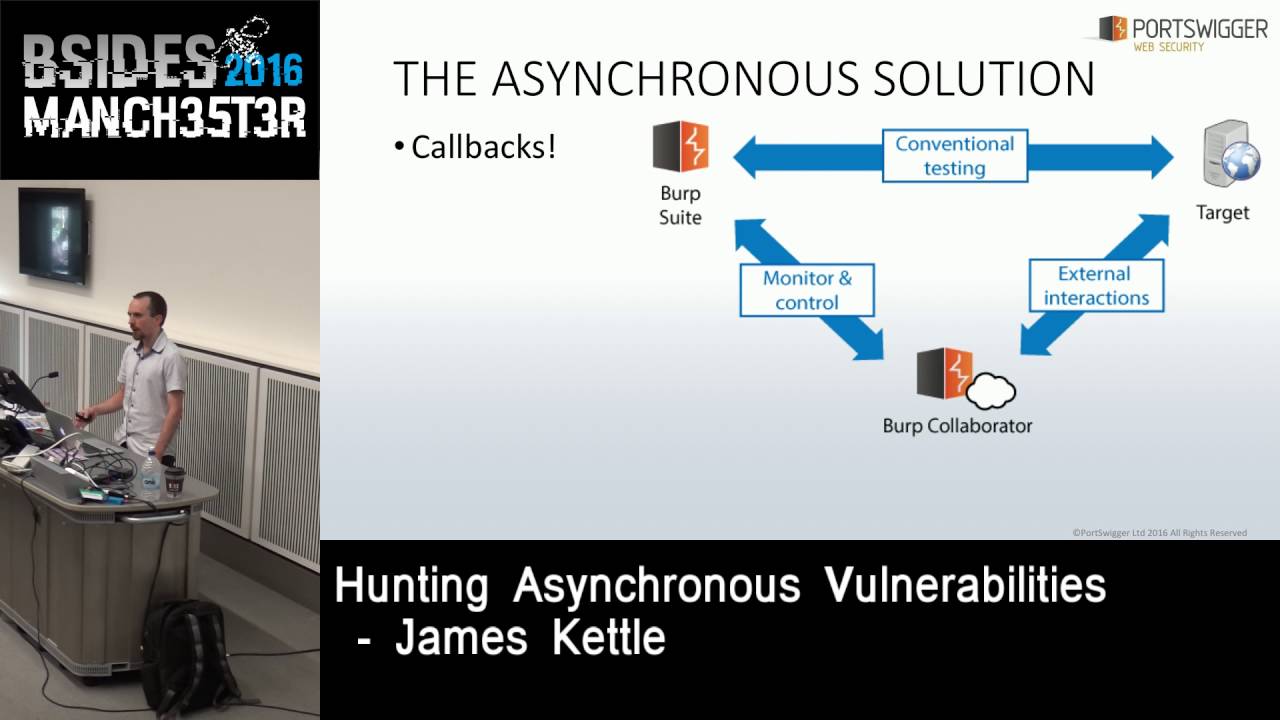
easy way with XML to cause a time delay without risking taking out the server which you probably don't want to do in order to find all of these issues we need callbacks we need something like the order confirmation email that was sent from the website to my mail server to let me know that it was vulnerable and you might be thinking great well in order to receive this callback I need to host a publicly accessible server which exposes every network protocol in existence how secure does that sound well fortunately almost every network protocol uses DNS so actually all you need to do is support DNS is recognized DNS lookups and then you can find SMTP
injection and issues that cause service to make UNC connections to your server and SMB and so on another great thing about DNS for this purpose is that it's rarely filtered our bound on firewalls widely used by various three-letter groups because basically if you block dear in DNS outbound on your firewall things will tend to break so people don't tend to do it also if you're a burp suite user you don't need to host this this public this server we've got the the burp collaborator which does this for you and within the next month or two we're fanning on on releasing and API so that you can right scan checks using asynchronous payloads for your own
personal use okay that's the core of the theory so how do we actually what does it look like when we apply this theory to a vulnerability class well first we need to have a look at what the problems we run into are there's a reason this isn't widely done at the moment the primary issue is that callback exploits fail hard so we're building exploiting a normal vulnerability is typically an iterative process first you find the vulnerability and then you exploit it whereas if you're trying to trigger a callback unless you submit a absolutely perfect payload no callback will happen and you'll never know that the vulnerability exists and that means that the quality of the payload is
really important ideally you you want it to work in every environment that it could that it could plausibly be executed it for example a show command injection payload might be executed on Windows or Linux or who knows what so you want something that works in all of those contexts and similarly if it's a blind XSS payload you don't know where within that HTML markup it will be appearing so I ideally you want a polyglot payload that will work with garlis of where it appears you also don't know if your input is being filtered so you want it to be resistant to filters and of course you want it to be as simple as possible because then
because the more complex it is the more likely things are to go on and if that sounds like a tall order then yeah it's absolutely a best-effort sort of thing let's look at a type of vulnerability where you're triggering a callback by the very nature of it so with classic smtp header injection user input is placed inside an email header and by adding a newline the user can inject extra email headers and maybe make the email get carbon copied to a different destination and if in if there's someone else's password reset email then that's that's quite a nice vulnerability and I actually found that vulnerability in Mozilla persona a while ago but there was a catch which was that the mail
server processed the headers before my header got injected so it would ignore me saying things like please Carbon Copy me on this password reset email in order to exploit this I had to inject a reply to header and then a zip bomb and the idea here was I mean if everything it was a zip bomb got to do with this the idea is the the mail server of the victim would scan the email for viruses they would go whoa there's a really well-known zip bomb on this and they would bounce the email and with a bit of luck because of my reply to header the email would get bounced back to me and I'd have their
password reset email and the what you've got to try and do is anticipate things going wrong like this you've got to say how can this exploit fail when I've exploited this in normal cases what's gone wrong and what measures can I take to handle that XML is a wonderful technology this single XML document uses six different features of XML to trigger pingbacks to remote service and each one of them is really quite simple so finding XML injection of finding external XML entity related issues it's really really simple because it's built it's baked into the core technology the last two payloads on that screen are particularly useful because they don't need to be placed inside the header of
the XML document and that means that you can find XML injection vulnerabilities where user input is placed inside a larger XML document and that's the type of vulnerability that's normally really challenging to find all about sequel injection well structured query language isn't really designed with connecting to external services in mind so there's nothing in the core spec that I could find there let's to initiate a ping back to a remote server so why I've done instead is looked at each database and seen if I can use some database specific features to issue this call back and I thought I was getting nowhere with post play and why didn't I just I I just skim read this page of the manual here and
maybe you can see the thing that I missed this copy command it doesn't sound very promising right but if you look closely you can actually use the copy command to execute arbitrary shell commands on the server that's kind of cool so if you inject something like that then regardless of whether the backend system is Windows or Linux as long as you've got admin privileges on the database you've just found sequel injection in a completely asynchronous way so it doesn't matter if this vulnerability happens in a background thread on some other server than the one that you were targeting because you just got that ping back so that's nice what about sequel Lite sequel Lite the
name makes it sound like this is going to be really difficult right it's going to have very few features that you could possibly exploit well fortunately it's got a couple of features which work on files and Windows has this wonderful feature called UNC paths where basically any function that operates on a file can be ver made can be made to access a file on a remote server over SMB so that means that whenever you've got a file i/o kind of thing and you've got control over the path you can make Windows issue a ping back over dearness great and I thought this was only exploitable on Windows until two days ago it turns out actually OS X has an as a feature that's
similar but even better so here on oh s X as you can see on the top payload you can anything that takes a file path can be given slash net and then an arbitrary domain name and OS X which way to mount that as an NFS share so that's handy if someone's foolish enough to be running a web application on OS X I think it happens sometimes okay what about Microsoft sequel well you can use open wrote set but it requires a non default setting you can require you can use file exists but it requires a non default setting and you can use bulkinsert form but it requires special privileges but what about XP o
XP dur tree if you execute this it tells you you need system it tells you this failed because you need sysadmin privileges so it doesn't really look very promising but if you test it and run Wireshark you'll find that it actually did the DNS lookup to the remote server before checking whether you have the permission to execute it so that's absolutely perfect that means that we can quite reliably find asynchronous sequel injection against sequel server regardless of what privileges the database user has what about Oracle Oracle adds quite a few features you can actually write an app a low to find our core sequel injection that will send you a nicely formatted email to let you know it's found a
vulnerability however once again it requires privileges which in later versions of Oracle you may find you don't have however Oracle lets all users regardless of what privileges they have execute it's XML parsing functionality and as we know XML is a wonderful technology lots of helpful features so what net Spy found was the ala course XML parsing is vulnerable to external XML entities and that means that a user with no privileges can trigger a ping back so what we're doing here is using sequel injection to tell all the code to parse a malicious XML document that will do an x XE vulnerability that will send a ping back to our server great this issue has been patched so if you're up
against a database maintained by someone who studiously apply their patches then it might not work what about my sequel well there's loes file this is very similar to the sequel Lite payload it works if you're on a system that allows remote fonox and the same with select in in to out file so the first is for reading files the second is intended for writing files and at this point you might have noticed the linux-based systems have been getting off really quite easily and it was really beginning to annoy me quite a lot so I thought okay what if I changed the rules slightly what if I say Ashley I know I'm supposed to be like really nice
to this target system because I've got I'm accessing it remotely and whatever but I'm gonna start watching file to the file system did try to trigger a ping back the most obvious thing to go for is to drop a shell within the web route the issues are ping back however from the point of view of a burp suite scan we don't really necessarily know whether where the web route is so we don't know where to write this file so what we would need to do is basically spray shelves over the whole file system and our clients might not appreciate that too much so that's not great for our purposes another option that looked really promising at first is that if you
write a file to the right folder on some systems a mailer will read in that file and email it however I could get it working or working on Microsoft Outlook which is pretty pointless at this point I got even more desperate I was like okay some files you can write to them and they will result in something being printed out so what if we write dear employee you have one employee of the month please contact James kettle at PAWS waggonette to claim your prize' right we've got a asynchronous payload that bypasses outbound network filtering unfortunately the employee needs to be a bit of a muppet and the web server DS needs to be running his route so that's
not that great either we don't do that with burp suite just in case you were wondering what about configuration files so my sequel loads configuration files in a special order from the bottom up that's very very helpful because the selects into out file command that my cycle has can't be used to overwrite files you can only use it to create new files but due to this load order that my sequel users you can you can write a file to a place where one doesn't exist and then if it's the right location my sequel will read that in as a config file and give it priority over the config files that are likely to already exist and there's a setting that
you can set with a config file called bind address and this defines the address that the server will try to bind to and listen on when it's booted up and you can set that to be a hostname and cause a DNS lookup brilliant unfortunately there's a little bit of a catch for this which is that after doing a DNS lookup the server will try to bind to this address so if you do a pen test and say burp injects this command then it's entirely possible that two weeks later when this assignment tries to restart the server it will try to bind to a remote address and just crash you can try to mitigate this by setting up
your DNS server to return the IP address 0 0 0 0 which will lead to it binding to all available interfaces however there's another catch with that which is the missus Hammond might not want it to bind to all available interfaces they could actually be worse than if it just crashed entirely so that's the technique that I think you could use for manual testing in the right circumstances but we're not using that by default okay a sequel it started out pretty easy and go quite hard at the end what about show command injection well here we've got easy remote code execution so we've got quite a bit more we've got quite a bit of flexibility
there's no doubt that it's easy to trigger a ping buck because we've got this luxury of of it just being easy we can try to make a payload that will work in multiple different contexts so we want a payload that works in the three main contexts on Linux and on Windows 2 and the key way to build that you could I think think for a long time or you could write a pause or something fancy or you could do I did and just make a test bed that takes your input and executes sit in each of these contexts and tells you whether it worked or not and then you can start out with a simple payload and
just kind of tweak it a bit and add bits to it and just work your way towards something if it's always something effective reaching this point was quite easy and then I ran into a little bit of a problem so here this payload works in every context apart from when it's inside double quotes on windows so we need to break out of those double quotes but if we put a double quote in that payload that will break out of the double quoted context on Linux so it will then break the way around this is to in it is to inject an escaped double quotes because Linux supports escaping double quotes and Windows doesn't so there we have a single payload that will
work in all of the major contexts that it's likely to be executed executed it okay what about blind cross-site scripting well if you google for multi context exercise you're going to land on a blog post by Gareth hay is called one vector to rule them all and it looks like this it's it's a bit of a beast and it undoubtedly works in a lot of contexts but it's got some problems for our use which is we start it's quite long if your input is being cut off after a certain length then it's just not going to work and it's also quite fragile so any input filtering whatsoever is likely to break the entire payload and and in some contexts it's
requiring window name to be to be defined in advance which we can't always do so we decided to make our own version that was more suited to what he wanted to do which Gareth Hayes who made it is now going to come up and explain
so the idea was to produce a payload they're executing in multiple contexts but was small enough used as little characters as possible I'm sorry back past any restrictions from the web app so we start off with a JavaScript URL context which will executing anchors then we have a closing script tag which we'll get out of a script context and then the HTML context will inject an SVG you might notice the opening multi-line comment in the JavaScript part that will basically comments out of even context so that it still works in JavaScript context then we have a double quote in context so if it's in a job in the JavaScript it's a single quote context it will also work
with the dual quad so if you're in the JavaScript string block JavaScript string with a single quote word important course it'll still work the the plus will act as an infix operator depending on the context that you or the concatenate operator the mouse-over event is interesting because it will borrow the single and double quotes break out of an attribute injection so you know it's the forward slash here will act as an attribute separator then we have an image request which is basically used to create a request to the collaborator server to log events happen so in a blind situation or oh yes increase in tuition you need to send the cut of the request to the club
rates in order to northern new successful now you may notice that the image tag avoid spaces so that is also to prevent the web application from blocking and also the closing comments might notice here axis causing comment obviously and it's also in a regular expression character class so it will when executed using Mike in the double quotes or a scene reported context your wax is a regular expression but if you if it acts as a multi-line comment it will act as an array literal and then continue on so as you can see we avoid using to string from the citizens because it's short it's using array literal and concatenate that that's instead it was also a shorter factor we
also asked Eric the docs because some security products will scrap URLs so you might get a collaborator interaction that he wasn't intended to happen so we use the scared to prevent that and then we call the replace from Jim which removes backslash is the real what role is used as a black string because it works in both cases we are something else we to say that this was witchcraft thank you James cool so we've seen that you can apply asynchronous techniques to many major vulnerability classes I also want to show that you can use it to find some pretty crazy pretty obscure vulnerabilities that aren't generally thought of as web app vulnerabilities for example say you've got an
application that's called something like MediaWiki where you can upload an attachment which can have an arbitrary file name but it has to end in dot JPEG and say someone say a sysadmin or a cron job occasionally does something like tar star to zip up all of the images if you upload an image with that file name then when they execute tar star this will be treated as arguments to tar and will trigger a ping back to our server that's pretty cool and there were variants of that payload for for plenty of other common shell commands and I'm not saying that's a common vulnerability the point here is that just there's some mental stuff that you could find using these techniques
okay let's have a look at a actual application
you might be familiar if you've ever been asked to do a webapp test you might be familiar with landing on being asked to do a pen test of something that looks more or less like this right there's there's nothing going on there there's nothing you can hack and you're like well great maybe they're selling a cookie and they forgot for HTTP only on it but we can do better if you pay close attention to what's going on here you'll see that there's they're using pie wick which is a popular piece of analytic software which is logging your visit and if we take this to the repeater and send it then it looks like a pretty lame
attack surface because regardless of what you send it just says 204 no spots right like what do you do with that this is the perfect example of an asynchronous attack surface of one way you can't see what's going on behind the scenes so why I've done is injected three payloads I've said this is analytic software they're probably interested in what Google queries led people to my to their site so I'm I'm gonna fake a Google search and I'm gonna provide three malicious fake Google queries which I've injected here one two and three so what's going to happen if someone comes along at a later date and decides to export this data as a spreadsheet well you might have a clue
if you were at one of the talks earlier actually for start maybe we get really lucky okay maybe they're using a version of Libre Office or OpenOffice and they're missing a couple of security patches what's going to happen I wonder well it's pretty predictable we have full control over over there server over the sysadmin personal computer which is pretty nice I mean maybe in the pen test that's not what I want to be told but I still think it's cool and similarly maybe they open it in Excel and they make the mistake I hope the licensing works well maybe they open it and they make the mistake of reading the warning error message that comes up this is interesting ah
there we go right so maybe they read this which says do not enable this unless you trust the content of this document unless you trust the origin of this document and if your systemize admin you might think well this document this document came from my private server it's going to be completely just were they so you're going to click through both the warnings that say the same thing and I've got a shell again maybe they're a bit paranoid maybe they don't click accept to either of those well if they click on the wrong cell then actually a browser is going to pop open which is going to leak the contents of the spreadsheet or some of
it to my server I've also just last week found a different payload which will cause the contents of the spreadsheet to be extricated to a remote server on fully patched Excel with no warnings or any kind of visual display whatsoever I was hoping to demo it here but unfortunately it's limited in the amount of data that it can get out which makes it slightly late but watch out for that I hope to get that fully working and release it soon and hopefully Microsoft we're going to say that's a feature and then it's never going to get patched
okay I've just shown a few examples there were loads of things that I haven't looked at but I'm pretty sure would be easy to detect using these techniques like HTTP proxy image tragic this thing I just invented a couple of days ago called remote local fire include which is local file include on a Mac and JJ nd ie injection which was mentioned at blackout Vegas what goes wrong well one thing to watch out for is plainly friendly fire if you inject some kind of CSV payload and you get a meterpreter show back from one of your co-workers who's also on the pen test that okay that is kind of cool but have you really achieved anything
what's the client and a thing like I know the problem that we have encountered a lot more three thought we would with burp suite is as Gareth briefly mentioned quite a few security appliances scrape all HTTP requests for domain names and then they send requests to those domain names to figure out whether there's a apt lurking there or something and this means you you might submit some really great payload for Oracle sequel injection and then some kind of laughs will send a ping back and you'll think the application is vulnerable to sequel injection where naturally it's just vulnerable to having a slightly dubious Wow maybe so in order to try to mitigate that generally we
always try to escape the payloads that we send in in the way that means that for something that's doing a naive grep it what it won't see any valid domain names but the payload will still work or if you're executing something like nslookup you can tell nslookup do a DNS query of this specific type and then you can say okay we knew faster actually reporter vulnerability we needed that exact type of DNS query to come in another issue that ivory fleet searched on is that asynchronous payloads have no concept of scope so they will find vulnerabilities on systems that you were never asked to test six months after you asked to test something completely different it's just
something to watch out for okay three key T three key takeaways are you can do this there's nothing that hard about any of this especially if you use the server that we're hosting for you if you if you don't trust us you can host it yourself you can also do most of this manually just by setting up a DNS server and using some open source software to see what queries you get the key thing to watch out for is that asynchronous exploits fail silently you need to come up with the perfect payload on your first time so you have to do your research at the start ultimately just because you can't see it doesn't mean you can't hack it I'm going
to take five minutes of questions now if you've got any questions after that you can email me or come and talk to me at the back don't forget to follow me on Twitter thank you for listening
okay any questions yep okay yep how am i handling DNS caching what burb suite does is we generate a random and unique subdomain every time that we send a payload so we've got wildcard DNS pointing to our server and we never reuse payloads anyone else yep blind cross-site scripting is a subtype of stored cross-site scripting that's just particularly difficult to find because if you caused and an alert popup on some back-end system you're probably never going to know that happened I think it's quite common that's the impression that we've got since we've released this check anyone else yep
I have not tried or note no I will be interesting to see how easy it is yep yep yeah yep so when I demoed that that was using Gmail using Gmail so Gmail scans the emails for viruses but so I I think the the foil that I attached is $42 if I don't know if you're familiar with it but it's very very well known any antivirus in existence is going to detect it and it's probably going to reject it because if it tries to unpack it to scan it then it will crash because it expands to be like 70 terabytes or something okay cool okay thank you





