From A Simple Log To Sophisticated Crypter - Hido Cohen and Arnold Osipov
Show original YouTube description
Show transcript [en]
thanks oliver hi guys thanks for attending our session from simple log to sophisticated crypto my name is arnold as already introduced i'm here with my friend and colleague hido and we both live in israel and work as malware and threat researchers at the company named morphysek and today we want to share with you our story on discovering the baba data crypto and we'll do so by showing you our point of view when we investigated something that might have been simple or irrelevant anomaly in one of our customers logs and later on we'll dive into the cryptos internals and understand how it works and how we use that information in order to uncover a major campaign that targets
some nft communities including some additional campaigns that targets um the ukrainian entities but before we start let me say a couple of words on what the crypto is for those of you may not familiar with it um let's do it with an example let's say we have a threat actor that wants to use some open source information still for some of his criminal activities if you'll use it as is theoretically security solutions would be easily detecting it either by strings metadata or even some of the code blocks and that's exactly when crypters comes in handy they solve this problem by taking this malware or information stiller as an input and performing some obfuscation encryption and code manipulation
and hopefully the output of decrypter is an undetected file without further ado let let our journey begin so one of our tasks security researchers is to keep track on current trends and understand the threat landscape and its evolution and in order to do so we use classifications to divide the massive amount of data we got from our customers into specific threats or behaviors and that helps us to cluster the data and follow trends more easily so one day while going through one of our customers logs and we came across an anomaly specifically it was a crypt which is an information stiller and at the time we had plenty of those infections but the thing that caught our
eye was the fact that the infection chain that led to it was something that we haven't seen before and the the clipboard was being executed from an executable that was being signed from by so by microsoft which was legitimate and at this time we were taking those first aid ashes like every person in our field would do to violence total yeah and we are surprised to see a zero detection rate which means that no security solution was able to identify this file as a malicious and we were even more surprised to see that this was the case for multiple scans in a very long period of time we took an additional hash from one of
our prevention logs and the result was the same so at this point we were extremely curious to understand how the crypto works and what keeps that low detection rate so in order to do so we need to get our ants dirty and dive into the cryptos internals so this is an example of how the infection chain looks and you can see that it's composed from several components and we'll explain each and every one of them let's start with the installer first stager and the installer starts with the decompressing its files into a newly allocated folder on the disk and this is how this folder looks and you can see that among it has um very files in that folder
and among them most of them actually sorry are in fact the legitimate they belong to a legitimate application or some open source application and the ones that marked in red are belongs to the malicious infection chain once the clip the installer finishes its execution it calls the file marked as one the executable and this executable sole purpose is to invoke the export function of the next stage malicious dll and as you can see it does so with just a few lines of code that are placed at the very end of a log function whereas the rest of the code in that function is actually benign again belongs to legitimate application once this dll is being invoked
it starts its execution by calling some sorry some additional dlls and this part in the crypto is written in a modular way that helps the cryptos users to choose which functionality they want to use for example the functionalities that we've seen or for example a dll that performs persistency in some various different ways and a dll that can download the additional malware and many more so once the dll finish calling those modules it will load a file from that folder to memory in this example it's an xml file but we've seen many other file formats such as pdf png and many more and this file is structured as the follows in between its legitimate xml strings we
have the feldshell code later on we have a configuration structure and after that we have several of encrypted chunks and once the main dll reads and loads that file it will invoke the first shell code by holding a hard coded offset to it this shellcode has several functionalities one of them is to load the configuration structure that was placed in that xml and this configuration structure holds the decryption key and and the description key for those encrypted chunks and the offset and size in the on the on that file and after sorry those configurations those encrypted chunks are actually the final payload and the second stage shellcode and after loading the configuration structure it will decrypt those chunks and
concatenating them to the original form then the decryption shellcode will invoke the second stage code which is the injection shell code and this injection shell code well is responsible for injecting the payload to the original process memory and after so well that's the high level overview on the infection chain but for those of you who want uh in-depth uh information on that crypto can check our blog for more information so why did we name it babadela the following is a code snippet from one of the shell codes specifically the second one the injection shell code and if you take a closer look you'll see that there is there are two um d words in there
the one in green dead beef with a typo which is known to be used as a magic debug value and the second one in the red baba dada is in russian stands for grandma grandpa so it was an easy choice as there were no any other indicators to choose from moving on to what makes it so evasive well if you remember we have the code logic that is splitted to several dlls and those dlls are placed among many other legitimate files and the code in that in those dlls are placed again among many legitimate code and on top of that in your variants we've seen that the main dll is being loaded by a newer
technique that called the cdl side loading which helps reducing the amount of malicious files on that folder by one and results in executing the final payload from legitimate forces as if you remember we've seen in our prevention log earlier and in addition we have the final payload and the second stage shellcode encrypted in some file format for example the xml and they are encrypted as i said and splitted so at this point we have the couple of vlogs from there we extracted some hashes and understand how the crypto works and i'll let you go continue from here thank you arnold so after understanding how the crypto works we had to figure out what our next steps
i like to look at analysis and research as two different things in my in my point of view analysis is focused on a specific piece of malware or a specific task such as incident response on the other hand research is a broad field which is redirected as new information revealed that's actually exactly what happened in our research we started by looking at the baba data crypto itself and now we are moving on to find its usages in the wild at this point we have a pretty good understanding about the inner workings of the crypto we can use this knowledge to translate and translate it into a yahoo for those of you who don't know what a yahoo is
all you need to know for now is that yaga provides you a convenient and intelligent way uh to search for byte strings for bytes and uh for strings and byte sequences in binaries so our yara is composed of three main indicators the first two are being the baba dada and dead beef placeholders are not just talked about and the third one is are few bytes from the decryption shell code which i remind you is not encrypted on disk once we have our java rule tested and ready we can use it to hunt for more samples we hunt in our own data on our own telemetry from our own customers as well as online malware databases such as
virustotal and malware bazaar those databases usually let you use your own rule in order to find format samples so after running this sample collection we had a pretty large database of baba data samples that we needed to extract some information from them so we wrote an automation that extracted some iocs which i'll talk more in a bit about them in a bit and then we used open source intelligence to find some references of usage in the wild so let's go back to the automation and understand what data we need to extract from each sample to do that we need to understand what is our goal and our goal was to find us agenda in a while
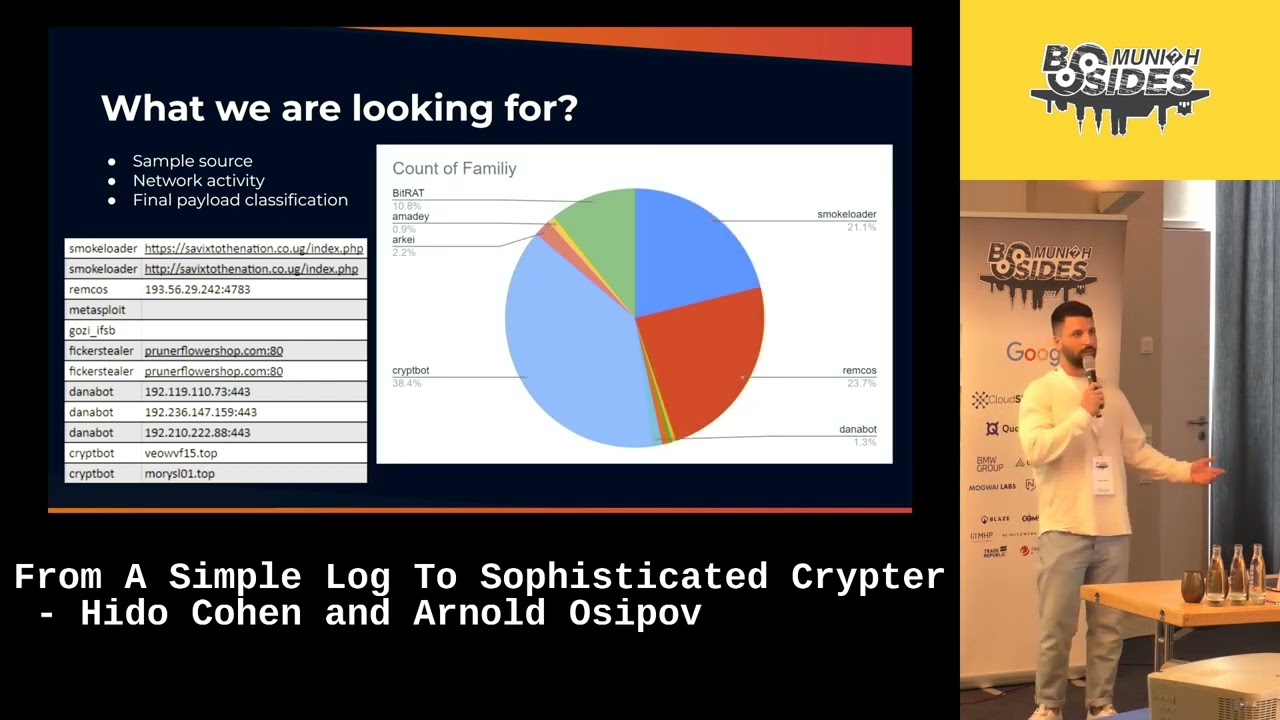
so we figured out that the summer source network activity and the final payload classification will be enough for us and as you can see there is an example this is an example of our automations output the left column is the final payload and the right column is the corresponding network activity network indicator which can be your full url domain or ip or even blank if we haven't succeeded and we used this output to see what manual families made the most use of the bava data crypto so this one was pretty interesting to see then after collecting extracting all of the data and we started open source intelligence we used online sandboxes malware databases social networks and of course google and
virustotal to see any correlation between what we found so far and that's when we came across the following tweet the match with one one of our samples hashes the interesting part in this tweet is that it provided us an additional information to work with as you can see there is some kind of app called mumbin with a what's supposed to be its domain but actually it's slightly different from the original one and a discord message so it's small in here the discord message that classified as a scam alert we wanted to see if there are any other services that follow the same pattern so we took the ip address of the fake domain and we saw that there are
indeed uh other services lister lisa lister listed under it the most famous one you might be familiar with is a fake domain of larval labs and but and then we got into inside those fake websites website looked inside the code and we were able to find some watermarking that allowed us to write a crawler which will find additional fake website like those and after running our automation we found a bunch of them with a one specific common ground that they are all some kind related to the nft and crypto communities the last piece of information we wanted to verify is whether the discord message is consistent among all of those services so we entered the discord server had
official discord server of which one of them and we found that indeed they are all having the same discord scan message this point we understood that there is some kind of an ongoing campaign that targets the nft and crypto communities and we decided to dig deeper and that's what we found for those of you who don't know the nft and crypto communities are highly dependent on discord as the main communication channel the attacker knew that fact and use it used it in order to find new victims once a targeted service it will uh add its bots into the discord server of this service and those both bots will send direct message to each member of the
channel as you can see the the [Music] discord message has an official looking of a username and title the discord the message body calls the victim to download the new desktop app in order to gain access to the latest features and at the end it provides a link to the official website which is different from the official one for example in this case debunk the official website is debunked.com where the provided one is debunk.found once the victim fills in with scam message and clicks the link it will be displayed with a website that looks almost identical with the one main difference that the login button is now a download button yeah um if the victims continues and download
the this file it's actually a malware that upon execution provides the attacker a full control on the infected system we decided to publish a second blog post and that details about this threat act of the attack chain which you can go and read about wait we actually tracked back the activity of this attacker and we found that it was active since november 2020 and and the more interesting part is that since august 2021 its preferred crypto is no other than the babadela crypto we just talked about so that actually explains how we got to this campaign at the first place we wanted to see some usages in the wild and we got them at this point you
may ask yourself why do we publish our work why do security companies and security researchers maintain an active blog there are actually many answers to this question but for us is to hopefully make an impact yeah i think the this figure shows how many new targeted services where each month by this attack chain and threat actor and as you see before uh releasing our first block above the baba data there were around 15 new targeted services and our first blog only briefly discussed about this ongoing campaign so the impact was of course close to none and then we decided to publish a second blog post focusing on the threat octo its evolution over time its
infrastructure and much more and finally we got some impact and as of today we can say that there are no new targeted services and we can say for sure we caused it but we for our own motivation we do like to think so [Music] okay another reason for us to publish our work is to help other with their research for example let's take the case of baba data against ukraine the third ukraine the ukraine third has published that ukrainian state organization has been targeted to saint both and outside malware attacks in this post there provided some details not many and with some iocs but didn't explain so much about the infection chain then security company named elsie took
the word walk and expanded it and what they found is that baba dada was used to drop the austral malwa you can go and read more about this i'm encouraging you a very good stuff so let's take a recap for what we talked about today and what are the main key takeaways we want you to take from this talk and we'll begin by understanding the threat landscape you're working with if you recall that's how the all resource story began at the first place we knew how certain malware infection chain would look like and that helped us to spot the anomaly between the rest of the logs look at the bigger picture and although we started by
inspecting the baba data crypto and its inner walking we then immediately took a step back to understand what role it plays in a full infection chain in a real life scenario use automation to make your analysis easier when you are dealing with a larger amount of data you must automate as many tasks as possible to make your analysis and research much easier and quicker for example in our case we have automated the sample collection the ioc extraction the corolla and many more components and finally share your findings and make use of other findings this is a great community contribute to it it will help others in their work and hopefully will help you in your future
work thank you everybody [Applause] cool great guys thank you very much for the interesting talk it was nice to be taking on on your journey of discovery and also i mean linking to the keynote from this morning sharing your findings um sharing what you figured out it's a it's a really cool thing to yeah to help the community and maybe some of you got interested in also doing similar stuff so yeah we have time for some questions so when you have questions feel free come to the microphone
[Music] um so uh between the two blog posts uh there seem to be around four months more or less uh how much human efforts there is behind this kind of research and how many people were involved and was this let's say uh a focused effort on that or how was this done let's say so um actually after posting as i already said uh at the first ball post we briefly discussed about the campaign so we already knew that there is some kind of an online campaign but we didn't go went in much details and understand it fully but we keep our eyes on it and and then after one after a certain period of time we decided to go back together
we were all together not only because it was uh it has is a lot of work to be done but also because it's fun to work together and and we got back and we decided to investigate more desperate acto and and it's it was i think at the same scale of the first uh research but it's different because the first research is more about reverse engineering and malware analysis where the second is more threat intelligent and and those sort of stuff but yeah thank you thank you you you had this um slide with the bullet points what um about what made this scripture so evasive i'm not i'm new to modern analysis but still none of those bullets was really
new to me so was is there any really specific thing that made it so evasive or is it is it actually not that hard to make crypto um with a zero detection rate so is it common is it a common thing or is it really that special so first of all it's not that hard to make a crypto so evasive but the the thing that was special here that was the fact that this script was evasive for a very long time that was the what interesting in this part and by and this and it does that by com combining all of those bullets as you said together that's how we it does that
very nice then um yeah thanks again you guys for also making a trip from tel aviv here to munich and to present and um thanks a lot another round of applause you





