GRC Engineering - Bringing GRC to a repository near you

Show transcript [en]
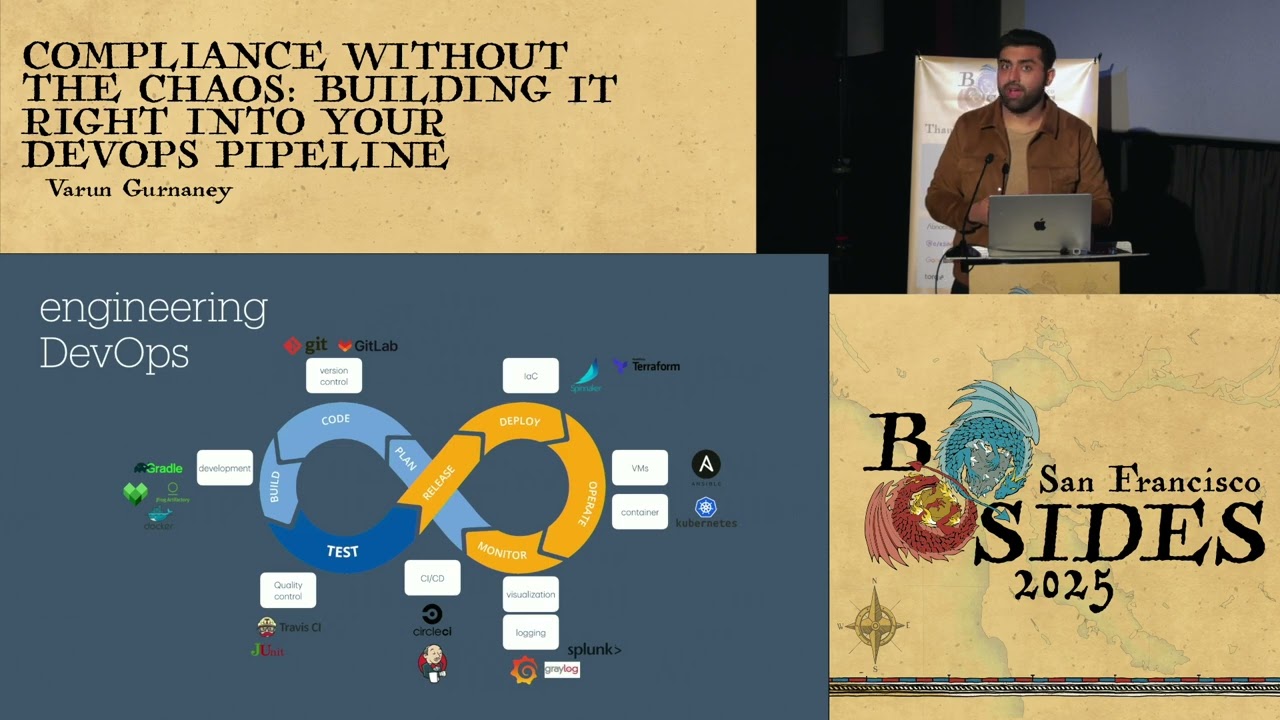
so hello everyone for our next session we have Von who would be speaking on GRC engineering so if you have any questions you can put it up slide.io uh slido and we will be taking those questions at the end of the session thank you
awesome thank you uh for the quick introduction Karthik thank you so much and thank you all for joining in at 1:30 p.m. on a Sunday after uh it's not easy I know and uh just so you know these seats recline so if you want to post lunch nap you can recline those and I won't judge you anyway it's GRC so you can nap it out anyways before I get started I want a quick poll of the audience how many of you here are from the security engineering software engineering IR instance response and all that crazy stuff okay uh how many of you are from the GRC govern interest compliance background nice I'm glad you care about
this uh how many of you all work for a vendor uh cool nice thank you and how many of you all are here because the 13 was already [Laughter] full all right cool so let's get started so we'll be talking about uh three broad topics in the presentation I'll be focusing on the bottom two for the most of the part uh talking about the challenges in GRC and and uh why do they exist and then we're talking about GRC engineering which is an engineering approach to solving those problems and then the audit engine which is how you can solve those problems using engineering approaches little about me uh I'm a security engineer in San Francisco I
started off my technology Journey with writing IOS and Android apps um in my undergrad and then my first job was doing vendor security audits so when you put a software engineer into doing ISO vendor audits uh life just is not fun and if you've done these before you know how it is it's just a painful process uh so I quit that job and I and I went to get my masters here in the US and after that I started working in a security engineer appsych Ro at uh zenes and Robin Hood uh while I was doing that I saw a lot of traction being picked up in the compliance automation space startups got great funding so that means the
market was validating these was accepting these ideas and uh besides accepting this stock is a testament to the market being open to putting Automation in front of GRC so I pivoted my career to solving GRC problems and my my goal in my near career is to actually help um Engineers hate compliance less um and uh I get a smoke when I say that in a in an internal audit meeting and Engineers are like yeah whatever were like you you do you man U just quick disclaimer um I'm not here representing my employer uh this is not what we do at my employer's place and uh I'm here on my own time on time it's a Sunday so it's my
time cool so GRC um it's a pretty broad topic uh mostly goes unnoticed in a lot of security practices and uh it's GRC so it's three words right on the slide U governance is a a team and a practice which does a lot of policies and procedures um risk is a function which will ensure that U security and business um things that happen in these places don't stop the business from achieving their goals and their objectives and lastly compliance the favorite of of all of us is adherence to laws and Frameworks and in this talk I'll be focusing on the last part I will not be talking about gr for the most of the part uh and and you'll see why I'm
saying that so compliance um it's a function in in a company uh which can range from Finance to security and uh coming from a security coming to security conference and security background I care about security compliance part of it um whatever I say and speak in in this talk can also apply to any compliance you can get care about lately AI compliance I don't know if you've seen the iso 401 uh it's it's a fun framework and every single organization will come up with their own AI security framework so brace yourselves for that anyway so compliance um security compliance in specifically U does a lot of things right it it helps with sales so if you
are a B2B SAS right up to an Enterprise company that sells a firewall or a logging service at an Enterprise scale um you need a compliance function to actually make a sale so Finance is incentivized to have this function uh compliance also helps in getting down your fines so in compliance a lot of like privacy Frameworks you need this function to bring down the fines and then of course complying with the latest Frameworks like ISO and PCI nist right all these things require somebody to focus on it um all these Frameworks I mentioned right now nist talk to PCI Hippa they are 60 70% the same they overlap um and the challenge that the compliance team faces is that um these
Frameworks have certain nuances that uh come out in something called as Gap assessment so the compliance team has to work through each framework and see what is the nuanced part of this framework for example like fed ramp will focus a lot on how you do volty management right and PC will focus on okay how you segment your C environment from the other parts of your company and the best part is that people come to compliance with demands like people will come and as a compliance team to do a lot of things imagine you are compliance all of you from various parts of security are now compliance team for this conversation and for this talk so best of luck and uh let's see
what happens when people come to compliance legal will come and say hey we have gdpr and uh please make sure that we follow the rules of GDP have 4% fine on it your Finance compliance will come and say we have socks so if you want to be on the stock exchange do your financial reporting well don't be the next Enron so you have to do socks then your board of directors will come and say hey we found this fancy ass framework and called the N CSF and how do we uh compare with that then lastly your sales team will come and say say how do we do uh how do we sell this we need a sock 2 so please help us bring in
sock 2 so compliance team will actually interface with all these fun people in the company who ask them various things um but the compliance team does not have access or I would say does not have the capability to actually get the answers without interacting with other people in the company so they act like a program management function which goes and talks to different people and get the answers to put it in the framework language so broadly U compliance focuses on two aspects two work streams achieving compliance so how do you get uh compliant with these Frameworks and uh regulatory standards and then audits so every 6 months or a year depending on the Cadence of the framework you have to
show up and perform an audit and then you have to support the audit so let's talk about achieving compliance uh in the first place let's assume that you are in the compliance team of a B2B SAS company and uh you have a new product coming out which sends smss by an API endpoint pretty standard sounds familiar right and you need a sock to for this you're a smaller company needing a sock to for a new product how do you go about doing this you have a kickoff meeting uh with people who you want to address this to so sales engineering leadership product then you do a gap assessment so what you have in your existing security controls versus what
does the new framework want you do a gap assessment and then you tell the teams to fill those gaps and this is a fun ask because teams don't want to listen to people right nobody wants to listen to anybody so you remediate uh the gaps then you test those gaps and then you go for the certification and you get your fancy sock to certification or whatever you go for now the season comes around season changes and uh oh sorry one more part so you interface with people when you do these five steps um so engineering legal and internal audit will be in the Kickoff Part product uh in the Gap assessment part of the product per se and then engineering
will be in the remediation part they need to see what security controls were not in place and what do we need to put in place so engineering comes right there and then the season changes and the audit period comes around and then again you have kickoff meeting you do a pre-assessment that we need to go into an audit let's see um what the Auditors will potentially ask for and do a pre-assessment and do then the audit cycle comes around and then Auditors will ask you to like sample stuff uh so you have some samples that you'll have to test against and the validation happens and then you close the audit while doing this you interact
with uh engineering legal internal audit in the pre-assessment phase you ask Engineers to are you prepared for this audit you want don't want to hear the answer to that but mostly it's like uh we don't know um nobody knows and then you do sampling you go back to engineering and say we received these samples from our external auditor we need to get stuff for this particular sample and then again validation part part of it is by engineering part of it is by compliance and then you close the audit with legal internal audit now all this is good but if you see a common theme right you are interfacing with engineering themes a lot and and here's
what I want to talk about um I know you I said you going to be compliance for this for this St for this slide assume you're an engineering function in that in that company as an engineering function as an engineer as a software engineer on that team you need to move fast you need to ship product you need to fix software bugs if you're a smaller SMB you have latest business needs that your CEO your director of engine ask you to ship if you're a larger big tech company it's going to be mostly scaling up things and being on call fixing bugs um so you're already pretty busy with a lot of things and security is also an extra thing that
happens to be on your plate depending on the organization security is prioritized at the top or are the top five things that they need to do but again it's an extra thing right you're not incentivized or your performance bonus is not B on how many security bugs you squash until you're a security team and then compliance team will come to you and say hey we need your help for this achieving compliance phase and then your audit phase and you're like come on man this is not what I wanted to do this is I don't to Support Compliance audits that's what I want to do as my part of my job so you have to context switch
every single time compliance comes to you and that's a pain and nobody likes pain so Engineers don't like compliance and on the compliance side they have too many Frameworks to keep up with audits the audit calendar is full so you have to keep on supporting audits you are already disliked by engineering teams because you have given them extra work um and then that leads to software engineers and Engineering teams gatekeeping information from you and that leads to reduce uh security hygiene and obviously you're creating compliance gaps this is a culture problem so what do we do how do we actually address this problem and what we came up with I've been thinking of this for a
while and how do we fix this something called as GRC engineering that's the topic of uh this presentation and you can achieve gr engineering as a function in two ways is um you can get your compliance people to do some basic scripting or you can find some um software engineer who you know truly cares about compliance somebody like myself who actually can bail you out of these smaller problems right and the goal of GRC engineering is uh to actually make Engineers hit compliance less that's the focus of it so it's an engineering focused discipline where you want uh compliance people to interface less with Engineers when it comes to supporting audits right and uh since I have the
word Engineering in in this title we need to ship some stuff you can't be an engineering title and not ship product right or you cannot ship non-code stuff this is not like a spreadsheet that's going to be a part of your work it's going to be legit code so um what do we build as an engineering function what do we build here we build on two main philosophies either you support the compliance team or you support the product and engineering team and you do that by either doing audit tooling or you do compliance enablement so compliance enablement I'll get into what it is but this talk will be focused on audit tooling so compliance enablement is is
going to be a way in which you bake in compliancy stuff into your infrastructure I'll give you an example any small company or a large Enterprise has some kind of kubernetes deployment right and kubernetes has something called as uh the controllers part so you can have tooling consumed from your Cube API server or your Cube audit logs and then push that into reports that look audit friendly this is not rocket science it already happens in other disciplines of security but but you need to find a way in which you can have Engineers write a small tool which can sit into your kubernetes cluster and get logging information from your uh Cube audit logging and then pump that into an
audit ready artifact as in spit out a PDF file or a spreadsheet that the compliance team will love so that's what I call the compliance enablement tooling every infra part like kubernetes or or Spiner or or GitHub has different architectures so you need a person who has a skill to go into these systems and build out this compliance tooling it's hard it's not easy but you need the right person the right motivation to do this in this talk I'll uh focus on audit tooling now what is audit tooling audit tooling is a way in which you help the compliance team first because they are backlogged and uh you do that by building stuff in a way that you pull
from different systems and then you prepare audit ready artifacts you can do this in two modes uh but but before I do that I want to talk about an an important part just give me a small what a
break compliance is old but it has changed in the past 5 years there are many companies and startups that uh promise you a sock too for a very inexpensive price there are many such tools if you walk upstairs or go to RSA you'll find a bunch of them you drive down 101 South you'll see a bunch of those ads on the Billboards uh and and they they're honestly great I don't hate them in fact I love them I love those vendor tools because they have actually solve the problem for smaller Enterprises so I recommend using the those tools if you are a company of a certain type and size so if you're a sash shop uh you're
completely deployed on a cloud first infrastructure you have cloud-based tooling you have all B2B SAS products you use to to run your company they will work great for you your entire infrastructure is deployed on a public Cloud which has apis perfect if you have an on-prem deployment it won't work for you um your engineering team has one single way of doing a thing think about um patch management right you have if you have a very variety of infra components patching is harder if you just have E2 instances patching is much easier so if you're a smaller uh Shop with a smaller blast inter blast radius these vendor tools will work perfectly great for you and if
you're just a new GRC function just get them to work for when you begin building your team and they'll work perfectly off the ground for you also let's focus on when they don't work for you you're a large Enterprise when I say large even if you're like a 5,000 person 10,000 person company which in which you have multiple engineering teams that um depend on custom tooling you will have to do your own stuff you have a large Cloud deployment on Prem stuff and you and and you have seen a GRC tool that acts as a glorified ticketing system then this vendor tools might not work for you okay coming back to audit tooling so there are two modes in which
you can operate the easy mode the hard mode Let's talk about each one of them uh in the slide so easy mode this is a way for you to show quick value to your in organization very easy pick a control that takes too much time either to operate or to validate write a basic python script and then you show value s app.py file maximum 15 lines you learn from chat GPT and you basically do it let's a quick example uh let's say you're doing vulnerability management um and uh these are the criteria kind of follows and on the right I've just written kind of a pseudo code script which keeps your slas as integers and
then you have a check SLA function which just checks if the due date and the current date time is you know is the right way so to check for slas is going to be super easy right because you can just do this instead of doing this you historically would go to the engineers and ask them to pull those tickets and do this manual checks and spreadsheet you write this one script and your your golden this is like a quick value proposition for you in a hard mode you actually pick a control area like change patch access access management that's actually a pain point for many people and uh and then you actually go and build the audit
engine okay this is the hard part the audit engine audit engine is a backend service that does the entire audit heavy lifting for you it has um it has it needs two things to be successful you need to have a list of all controls and you need to have a list of all applications that your compliance controls depend on this you won't find in non-mature GRC function need to be a really mature function to have this kind of maturity to go for the audit engine okay what are the requirements for doing this um let's look at one by one you need an interface um to store all your controls or a way to pull from an existing GRC
tool so if you use uh an existing GRC tool which has all of your controls just hook it up with that and you're golden you need an interface to actually keep a track of all your Scopes so if you are in scope for ISO sock to PCI Hippa like a way to store all that scope in a database and and then that's how it looks like right you have uh all the that's more of a how do you create a table in in SQL and uh you have the sampling details in a Json blob and uh you have the audit start date the end date so you're keeping track of of the scope of the Audits and then you need a
way to uh you need to to map your controls to your application so if you have an HR application you have uh connectors to that HR app so that's in a cheex DV so all these U black boxes are going to be Crow applications when I say we need an interface because you don't expect GRC people to actually go and write the code so you as a GRC engineer need to go and build those CR application which can actually handle these things going further let's let's going to we're going to build out system design as we go through uh talking about each requirement so the controls home talks to these two uh pieces scope DB
and cheex DB okay since we have multiple systems for one control area we need a way to accommodate the complexity so we need a serializer we need a way to trigger the audits we need a way to meet a continuous compliance needs continuous compliance is a nice buzz word essentially just a for Loop you keep running it or you keep it's a crown job you keep running it multiple times every Monday 10: a.m. do it that's compliance for you we need a way for us to chain different applications uh in order to satisfy the need of one particular control and that's going done by the integration middleware let's look at how these two fit in
together assume that you have let's talk about one part of uh this entire diagram look at the vulnerability Management caliz in the center you have different teams different teams in engineering use different vulnerability scanners you have five different scanners because on the period of the past 5 years you bought all of them and all of them work in some way but they don't work together and for the audit you need the report from everything right so you chain them together and the serializer will kind of have a common way to pull the data out from these scanners and then you pump that into your middleware uh let's look at um the access management sterilizer this is a
sample from GitHub and from a KS logging system that's how I feel your dictionary should look like if you look at the the top it has the user uh dictionary and there is a access list so no matter you use geub you use skates or you use Spiner you use like force CR you use anything else in your infra you can just serialize that data into one specific way in order to consume it in one specific schema so you're defining the schemas here for your serializer okay so just pumping it in so on the right side we have the uh scope and check DB and this time we plugged in the integration middleware and the
serializer which pumps to the audit engine okay and uh we we also have these three new things this is more of um a system design concept where you have an API server to handle all the traffic um you also a web interface to interact um to give a UI to your compliance team and your senior leadership where they can see how you can actually interact with these audits so trigger audits continuous compliance status checks metrics all the measurements stuff that leadership loves to here you can bake it into the web interface then you also have a worker in which you can generate reports so you have a dedicated uh compute and data store for generating
and storing these reports and that actually you know wraps up your your system designed for the audit engine and the the engine can operate in two uh different modes I call it the uh the audit period mode and uh the continuous compliance mode so if you look at the audit period mode that's like you trigger one audit at one time and then you can go sequentially through you know pulling the sampling from Scopes D then you pull the data from Integrations scope with the sample perform the audit and generate reports and this happens all in the back end right and if anything fails you want to resample it's just a new Arrow right you have to like connect two systems and
Trigger it in the same way you don't have to like reach out to the engineering team again resample set meetings piss them off no just do it in one interface as I said continuous compliance it's a buzz word right essentially you move the arrow around so if you have all these parts built out you can play with how you do uh compliance so yeah that's uh pretty much it let's go through the summary and uh so we first looked at the challenges for compliance uh too many Frameworks disliked by engineering teams we looked at um the engineering part the engineering problem that Engineers face compliance gives them more work and then why vendor tools might not work for you
because you're too huge and you have custom tooling to for them to be used uh and then audit tooling you have two you have two ways to do it the easy way to get buying from your bosses and your leadership to do GRC engineering and then if you have the you have the investment and you have the motivation you can go for the hard mode and build the audit engine out and uh yeah GRC enging is a rocket ship to fixing your compliance and Engineering problems and in the final way we built out the system design um for this so yeah that concludes my talk are we on time yeah okay we have four minutes okay so we
have four minutes left let's are there any questions that are on slider nothing I put one on there okay I can can ask yeah you want mic I can just say it okay um and I'll try say louder so um a lot of what you're talking about makes me think of uh kind of you know in the last decade how we saw the rise of devops right and kind of introducing introducing reliability in the development life cycle process and you have all the other iterations that kind of come from that have you like do you think that there's some lesson to learn here in terms as we kind of build up this this idea of GRC
engineering like is there something that that some in other words is there some ownership or some principles do you think that you should take to your normal a normal software engineer that can make this process a lot smoother so I know you mentioned devops and then it became Dev SE Ops Dev Ops and then if I say let's if I would have submitted a talk with the title Dev SE comp Ops it wouldn't be fun so I don't think uh like if we have compliance as a separate engineering function I I think it's easy to scale and scale up and scale down if we try getting software Engineers to do hey you do you do
software engineering you ship product you fix bugs you be on call you patch your systems for security and by the way we have an ISO audit coming up and I need you to do this no with any software engineer has talked to they are not happy supporting compliance stuff so I'm like okay fine we know what we'll build a parallel function and we'll do it for you and we'll do it for compliance as well so I would love to find software Eng who are willing to take on compliance in their Sprints uh but yeah I don't find people motivated enough to do that so yeah thank you for your question any anybody else who has a question that they want
to ask okay awesome that was perfect then oh you have one
perfect so it it depend depends on typical answer it depends on your compliance need if you're just doing sock it's once in 6 months um I think if you're doing PCI it's once a year and then socks is that's every earnings again socks is also buy anual depend so you can like set it up like a you can have a lever or a gear and you can set it up depending on uh your Cadence I would say do it every morning at 10: a.m. what's the harm it doesn't take much compute anyway so and it achieves a continuous compliance needs uh if you have an order coming up next week you don't you don't have anxiety for it
so compliance people have a lot of anxiety right because you don't know what's going to hit the fan
so with the structure rather than just putting it on a Google drive or maybe using a data warehouse snow or something um yes I have built those things out and personally I I come from a software enging background so I go towards using Prometheus and custom tooling uh but I think you can build things off out of like U you know Tableau dashboards basic stuff right or any logging or dashboarding tool um data warehouses will work great once you have a lot of compliance data underneath it and you will become a compliance data like in the future and by the way that's a segue once you have a data Lake of data in compliance you can use AI right
I did not mention AI anywhere because I don't think it's the right time for compliance to do AI at this point of time for the majority we have in compliance as an industry um but there are people are doing it and it works great for big Enterprises who have a compliance data L But to answer a question there's nothing open sourced uh but I know people who are working on open sourcing stuff so keep a track of what advancements are coming up in GRC engineering you'll find something soon yeah I think we on time so do you have thoughts about putting it on a Time series database where every single commit a repository um I think your Version
Control will track all of that for uh pull requests and commits and merges you as compliance Ledger you already have that right in terms of your audit logging from every tool you build out and once you have this entire system designed up you will have loging components within this for your own compliance stuff so yeah you will by defacto get those things for free once you go for a system design like that okay guys thank you so much and we let's have a round of applause for Veron and if someone has any other questions uh you guys can chat on the City View so because we have to continue with our schedule and we have
another presentation coming up in 10 minutes if you want to talk to me on LinkedIn just hit me up thank you for you thank you so much