Modifying WhatsApp Messages
Show original YouTube description
Show transcript [en]
So now I'd like to bring up our next speaker, which actually has something to talk about that touches each and every one of us. Because this speaker is going to talk about WhatsApp. And everybody uses WhatsApp. I know I use WhatsApp. This conference runs on WhatsApp. And throughout the year, we spend so much time via WhatsApp to plan it. So I'd like to invite Yuri to join me here. Yuri Lipschitz, please join me. Give him a hand. Hello, hello. So let me tell you something about Yuri Lipschitz, OK? Yuri has more than 10 years of experience in product security. And he also likes Whiskey, which is good because we've got some up here and back there and he likes running and in
fact he recently ran from a lot to Masada and then back This is crazy. This is unbelievable. I can hardly run from here to the backstage and back So that's really remarkable now Yuri has a dream to run a marathon one day and today he wants to share with us how he Modifies your whatsapp Messages ready Yuri. Yes. Okay. Take it away. Ah, we have of course drinks for Yuri and Omar Nasdaoviya Give him a big round of applause First time on the B-Sides Tel Aviv stage Yuri Lipschitz Hello everyone. Hello B-Sides Tel Aviv This is my first time first opportunity to speak in before we do this large and I'm going to speak about what sub messages Modification this
is the way to contact me Something went probably wrong here. The presentation might be hacked. But I hope it will improve. So let's go forward.
Something happened. Just a second.
So first, some initial understanding of the audience, because we are going to speak mainly about iOS devices, about iPhone. And so I want to understand who is the iPhone user? Who is Android? Oh, wait. And who is both? Very few really technical people here.
OK. So a little bit about myself first. mainly building a security architecture for large companies like work for PayPal for some time. Interested, very interested in operational security, Bitcoin wallets unlock, emails, like to break different things. And very, very active WhatsApp user, sent a lot of messages, almost 40,000 as you can see. And I even met my wife via Facebook one, so it's a little bit ungrateful to Facebook what I am doing right now. And now let's do some understanding about level of security in our audience. Who is WhatsApp user?
Okay, Telegram and Signal. Very few people like security. Okay, so let's continue. If someone doesn't know Facebook, so Facebook exists from 2009, has 2 billion active users, and from the security side, mainly known for end-to-end encryption. So basically, end-to-end encryption sounds very promising, so let's speak about it in short. So basically, end-to-end encryption is encryption in transit. It's used in a formal case to encrypt messages, and in transit, the interception of messages is really complicated. There is some research, but it's essentially impossible to do it without very, very significant effort. But is WhatsApp really encrypted? So it's encrypted in transit, but apparently WhatsApp database on iOS is not encrypted at all, and the backup is not encrypted
either. And additionally, there is no Data modification control. No anti-tampering at all on application level. So as you can see, local backups for iTunes are not encrypted at all. iCloud backups are not encrypted. The only thing that is encrypted is if you specifically backup your WhatsApp database to iCloud to do some kind of one-of-a-time backup. Then it's encrypted with your keychain key, which also can be derived, but it requires some effort.
So now how do we attack the database? We need access to targeted phone, so the attack isn't quite simple. We backup the iPhone, locate the backup file, usually it's this long file name, It might be some different file name. It's quite easy to find this information in Google. Open your favorite SQL editor. And inside, you basically need to go to this table, to the WMessage table, and edit it. Just find the message that you basically want to modify it, edit it. You can copy the message and modify the content. And then you essentially create a new message.
After you're doing this operation, you just restore iPhone from backup and you have different WhatsApp history on the device. Let's say as an attack direction, as an example attack direction, some important person's iPhone is stolen, the WhatsApp messages history is modified, let's say some malicious messages entered into the conversations, and then it's very hard to discover, very hard to determine that the modification took place, and it might even cause legal penalties, legal ramifications, because WhatsApp in some countries is accepted as an evidence. So here's an example of original communication between Bob and Moshek. So Bob is good, Moshek is bad. And then this is basically what Moshek is seeing. And he modified the communication on Bob's phone. And Bob has significantly different messages
with large amounts of money he is ready to pay now.
And Moshek might now potentially extort,
those agreed sums from Bob. So again, we just entered via simple SQL modification, additional messages, or modified existing messages. And in addition, it's possible to add or modify attachments. It's possible to create entirely new conversation. It's a little bit more complicated. But it's entirely possible. So you can create communication which never existed between a group of people if you basically desire to do so. Now, again, something happened with the presentation. It's probably hacked. OK. So as we see, WhatsApp was used in numerous countries in different political and criminal cases, and people got indicted and jailed based on WhatsApp conversations. Now, by the way, there is some initial decision by Indian Supreme Court that decided not to accept WhatsApp as an evidence anymore. Maybe it's related somehow to
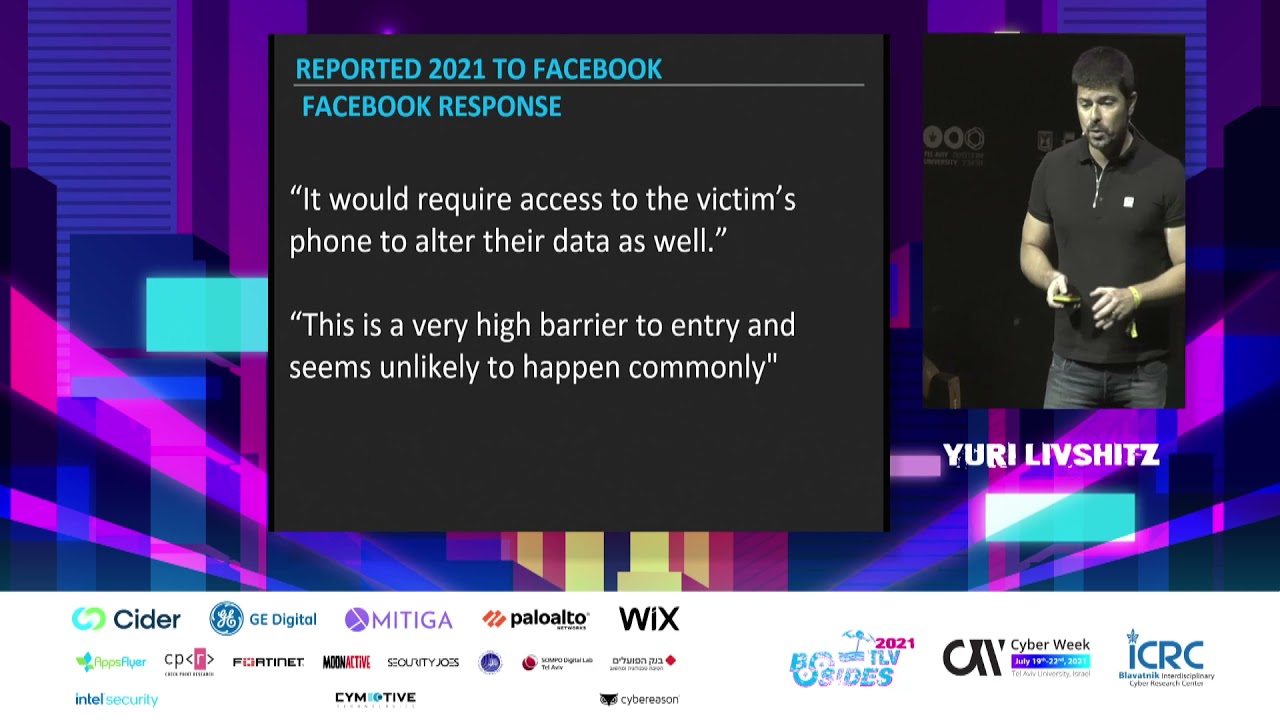
the assets that I'm showing you right now. Now, I reported this finding to Facebook, and Facebook response was quite long. So this is basically a short summary of the response. They say that it requires access to victim's phone, and therefore it's a high barrier for entry, which is unlikely to happen. So I have some doubts regarding this response, because as we know, multiple users use very simple pins on their phone. It's easy to shoulder-serve them. It's easy to do multiple attacks, because phones are not so well protected by general population. And if you see, basically, if you just search for mobile application security best practices, so the two main things that are basically not done on WhatsApp site, so data isn't encrypted,
and no anti-tampering is deployed on WhatsApp application site at all. Additionally, if you compare it to other messengers, like Signal or Telegram, Signal has full DB encryption at rest. All the data is encrypted, including attachments.
or at least majority of the attachments, which is relatively complicated to do. For Telegram, they implemented significantly more complex data structure, so data is stored in blobs, hashed, and has some kind of fingerprinting that prevents tampering of the data, but data is still visible, okay? Data is still visible, but if you use secret chats, for example, which is Telegram options for stronger security, Everything is encrypted. All the data is encrypted. And it's impossible to discover any data later on. In addition, I have some problem with the Facebook way of securing WhatsApp, because even if you use Face ID or fingerprint to lock your WhatsApp applications, there is such an option in WhatsApp applications that probably very few people use. So basically
it then acts like a sort of Bitcoin wallet that you need basically to use face ID or fingerprint to enter the application. Still, everything is unencrypted. So even if you use this advanced security, you are still exposed. The data is still exposed. And finally, there is some problem with the continuous advertisement of end-to-end encryption by Facebook. So basically, I've seen that it's in a way
makes people confused. Most of the people don't understand what actually end-to-end encryption stands for. And therefore they are exposed to additional risk because when you secure end-to-end, you understand that it's basically you are secure on every end. But in reality, you are just secure in between the ends, between the devices. You are not secure on the device itself. You are not secure on your backup. And this is basically what Facebook is telling us if you basically read the documentation on WhatsApp about data handling. So they say, we don't have your data, but if your data is backup to some external cloud, the data can be taken from there, the data can be exposed from there,
and if some government submits Sabapena to iCloud or submit Sabapena to Google, it can easily get your information. There are multiple applications that can basically fetch any kind of WhatsApp communication that's used by Forensic. forensic experts, and just without any communication with Facebook, they can essentially get all your data, unless you completely delete all your backups. That's it from my side, and I am ready for your questions.
you so much yuri that was super fast so i have a question for you okay let's give that to omel so stick around for a moment with me i have a question for you how many how many whatsapp messages per day do you think you send and receive every day five thousand one thousand send and receive i think that might be Received significantly more for sure. I mean in thousands, but the send I think around 100 probably so I think I think I probably send so many more Do we have any questions in the room? We have one please stand up and shout with your mask on
the question for everyone. So thank you for the question. The question to Yuri was a little bit more about the differences with iPhone between WhatsApp on iPhone and WhatsApp on Android and what would be the vulnerabilities or the similarities with WhatsApp on Android and how does that work with the other encrypted messaging apps like Telegram and Signal. What do you say Yuri? Yes, sure. So unfortunately I'm a smaller Android expert than my iOS and iPhone architecture knowledge, but what is surprising is that iOS and Android, WhatsApp security and data storage is handled differently. So for Android, the application runs sandbox, and you need root access to get into the database. And all the backups on Android side are done encrypted. But
And here comes the bot. The encryption key can be easily fetched by majority of the forensic apps. I found multiple forensic apps that can basically derive the Android database and basically expose it to the application. Now, modification of Android messages It can be easily done, obviously, on a rooted phone. There are even applications for it. They use mainly to do some jokes on people, but they can be used for malicious intent as well. So if you have a rooted phone, every message on the device can be modified even without any access to backup or any access to any external storage just on the phone. With regarding to regular font, it's probably a little bit more complex path to enter and to modify the
messages, but it's still possible. We got one question here. Keep your mask on. Yell your question, please.
The question was, with iPhones there is encryption for the file system, and usually it requires authentication using Face ID or fingerprint ID. So how does that work, Yuri? Sure. So the device itself is encrypted at rest. But if you have access to the device, you can get the files. If you can backup the device externally, you get access to the files and to the database, as I showed you.
There are two paths to get. First is access to the device, so you need unlocked device. Second is you need access to or you need access to iTunes account of the person. Otherwise, yes, it's a barrier for access. It creates some complexity. But again, multiple people use very simple pins, and if you know the pin, you can access the device. All right, we've got some more questions down here. Put your hand up really high so we can see it. And there is a microphone that's... Oh, Mary is working hard, so hard to get all the way to you. And be advised, we have laser pointers that will find you if you don't have your mask on. I'm not kidding. We
actually have them. All right, let's hear the question. My question is in two parts. Number one, how trivial would this be to correct? And number two, assuming this were corrected, would you say that WhatsApp security is now comparable to that of Signal or Telegram? Yeah, sure. So it's probably not so complex to fix on a technical level. The question is how complex it is. entire WhatsApp ecosystem, like basically ability to fetch the messages on different other devices. So basically there are two ways to correct it. First it's encryption and second it's just hashing of the messages. So if you have some kind of anti-tampering inside the database, we cannot modify the messages. Given that it is corrected, yes, and WhatsApp security is probably in this dimension is
for sure comparable to Signal, for example, because they're essentially built on same protocol. The thing that is different now is Signal using full encryption everywhere, and WhatsApp isn't doing so. And I assume that one of the reasons WhatsApp isn't doing so is exactly due to the reason that they want to avoid subopenas. They want just to divert them to cloud providers So it creates an easy exit from possible allegations of government investigations. They say that the information is exposed. Just go and take it from cloud provider. Take it from Ycloud, for example.
Any other questions? Any questions for Yuri? OK, I have a question. If you only had to choose Signal, Telegram, WhatsApp or Slack. What would you take to a lonely island?
Not Slack. Not Slack. Here I agree, but
very complex. Probably Telegram and even WhatsApp because it's convenient after all. You know, I like it. I personally think that signal is also pretty cool for those who don't know signal was founded By a hacker called moxie Marlin spike who has a pirate sounding name and he's pretty cool So I'd like to thank you so much for his presentation. Thank you Yuri first time Besides Tel Aviv stage you did awesome. Thank you, Yuri. I'll see you on the marathon Thank you, Karen. I'm kidding. I won't be on the marathon. But thank you so much, Yuri.