BSides Cairo 2020: Hunt Evil by Mohamed Sadat
Show transcript [en]
First of all, I want to tell you that I am happy that I am able to do this event and I am happy that the number of sites is increasing every year. Since the beginning of the technological age, humans have always had two ways to survive. The first way is to set traps to protect themselves or search for the food that they eat. But unfortunately, these methods are no longer available in the world. They exist and we try to make them more accessible than they are. The same idea exists in cybersecurity. For our organizations to survive, we have to get security controls to prevent attacks and to end these attacks. This raises a question: If we didn't prevent these attacks, if
the attacker was created, if the attacker found a way, as we see the attacks in the long run, what would he do? The second question is: How can we detect from the sponge? From here, we came to the framework that you have to be able to test the security controls and the security that is already in the system. We are all working on the framework and we are trying to do program detection We don't know how to start a free-from-hunting program. There are many resources on the internet, but they are free-from-hunting. We want to turn from free-from-hunting to practical. If we ask anyone who wants to do free-from-hunting, what is the most distinctive thing about successful free-from-hunting?
It is the orientation and the place. I am Mohamed Al-Said, I am a financial security manager at Financial Company. This is the session I will be doing, where I will be showing you how to make a real-time program and make a real-time orientation.
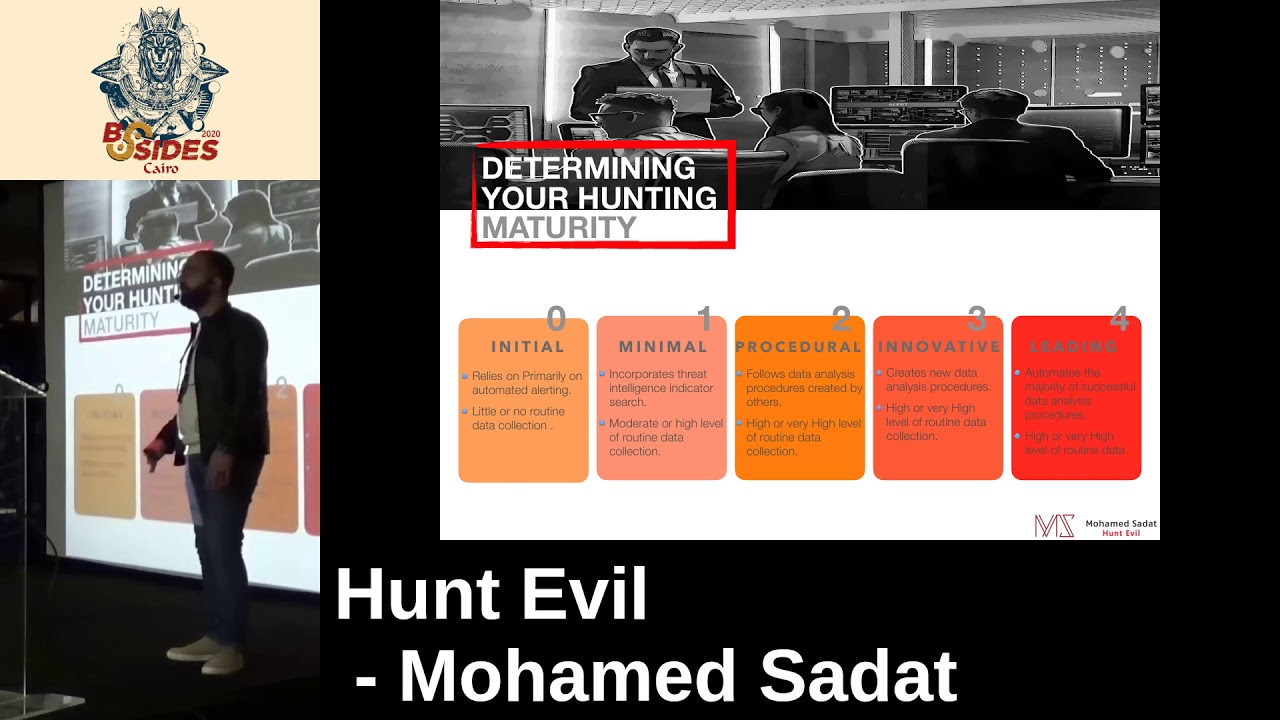
First of all, we will discuss Threat Haunting and its importance. We will know what is the Haunting Maturity we have, how the matrix is, and how the Threat Haunting program works. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use
it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The
point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of
two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use it to create a network of two different types of activity. The point is that we will use Basically, you try to reach the threat before it's even possible. And then you try to reach this threat and detect before it does any damage to you or your tech. Threadhunt is human driven iterative proactive search, that is, the analyst
is searching for the thread inside the company before it is published. This searches for the database, the network, the endpoints, and any suspicious or malicious activity that is done by the automated tools. As I said before, prevention is ideal but the potential is a lot. You must prevent and at the same time you must take something that will help you. Since I made a decent survey on the organization, I found that it is a good example of the organization tool that I used in the third function. What are the three things that are correct about threat hunting? The first point is that the runtime can be fully automated. As we said, the runtime is a proactive search. So, from a trash to a reactive network, you have
to do something. If a detection occurs, you can reactivate it and do a free hunt. You can solve the problem and see what happens to the detection. The second point is that the runtime has to have advanced tools and you need a very high data traffic. So, that's true, you can start threat hunting with tools that are used in the normal tools and you can work with any data, but at the same time, if you have advanced tools and data, then you have the best threat hunting. The point is that the hunting is one of the things that we have to do and we are experts in this topic. No, the threat hunting is the same as any technique you can use. Even
if you have a family experience, you will start with a level of threat hunting. Not all levels of threat hunting are the same experience. The threat hunting method was first because you have a special threat hunting. First, we have vibration and process. We have to find the vibration and process of the threat hunting. Second, we have experience, efficiency and expertise. We need tools, technology and techniques. These are the main things we need to know about the success of the threat hunting program. You need to know what technology you are using, what techniques you are using, what data you are collecting for threat hunting. The first level is the initial level, which is the highest level of automated alerts from the firewalls and the
IPS And in this level, you can collect data or not collect data at all The next level is the middle level. The middle level is where you collect data, but it is only medium data or real data. And the next level is where you rely on the field intelligence indicators. The next point is the procedure. It depends on the data analysis procedure written on the data You get it from another person But this point you collect high data or very high data You collect a large number of data The point is that you collect data high or very high
The level is the level that you can do any successful hunt with automation. For example, detection tools like the sensor, the file, the IBS, the IDS, anything because you are trying the same task that you are doing again, you do it with automation. And at the same time, you collect high and high again. If you want to know what level of the content maturity you need to ask yourself a little bit more The first level is the basic requirement You need to ask yourself the following questions Do you collect the automated alerts from the file group or IBS or any other automated alerts The second question is, do you have an incident response team? If someone was a dust analyst, what is
the answer? If the answer is based, you will be able to cover the basic required If the answer is no, you need to do four things, which are to acquire automated detection alerts, to have a field of intelligence, to have an incident response team that you The level backer is 100 years old, it needs 9000 questions, the first question is that you will collect logs from the network, host, application, you will find the fields from the intelligent thread, Do the people who have the software take the indicators and do 100% search on data sets to find any flips in the network? If you want to buy a base, you need to buy the network of variables If you want
to buy the node, you need to do two things You need to make sure that you buy the server, the network, the host, the application, and the point after that you need to put the The team must practice and be able to do the work and then search for the work. The work back then was a procedure of a push. Do the people in the software follow the procedures written on the outside? Do they do it on the inside or outside? Do you have a specific threat hunter in your team? If yes, you have already covered the procedure approach If yes, you need to do the next step You need to find a threat hunter and enter the procedure
and let the team members walk on it You need to add the data collection according to the procedure you are walking on to develop skill so that people can go for threat hunting The next level is the level of practice You need to be in the 4th grade The threat hunters in the team use threat hunting techniques They use threat hunting or death attack and death attack procedures They use it in relation to the environment they are in that they are using the ThreatHunting platform or not If the answer is yes, then you can cover the innovation practice If the answer is no, then you will need to join the ThreatHunting team to create the data housing process and to
start the ThreatHunting process in each area The next level is the leading program You have to wait for successful threat hunting, any harm that you do is good. So you have to wait for the threat hunting activity to be done because of the camera. You have to use the data science techniques in threat hunting. You have to have a methodology to increase the team and increase the threat hunting program you have. If you have a basic program, you can start the leading program. If you have a ground program, You need to make a process to make any successful hunting activity. Now we know what is hunting maturity. We will come to know how to measure
the success rate of hunting. We will measure the success rate of hunting. We will come to know how to measure the success rate of hunting. First, it has a number of incident by security. Any incident that you know or have seen in the field of threat hunting activity, it has the success of threat hunting. The second point is the number of compromised both by security. You can detect which one is compromised by threat hunting and what is the threat. The third point is the role of any incident discovered. Any incident that you detect, any threat, The number of detected The reason why I mentioned thread hunting is because you can find the thread hunting and do automation on it. Because you can't do the same thing on the thread.
The point back is that the login came with the identification that you are a fraud. When you do thread hunting, you find something that is not as good as it looks. So you ask the people in the network to make it look better. Point number four, if you found the probability of identification A, you found it and you can't see the activity of the three-factor, you can't see it in the mirror. Point number eight, insecure practice identification A, you can't see the activity of the three-factor, you can't see it in the mirror. Point number nine, number of hot translation in the UN, you can't see it in the mirror. Threat hunting activity and how to handle it, and how to start it and so on The
next point is what are the things you did on the transformation and what are the things you fixed The last point is what is the visibility gain, what is the visibility gain you can get after the threat hunting activity You can't see it on the screen Ok Now we will see what we will hunt and what we will hunt. To know what we will hunt, we need to choose the attack mode that we want. As you can see, we have four attack models, and you can choose any attack model you want. Why do we choose an attack model? Because the cyber-intelligence, which is the main part of this attack model, will be able to recognize the TTPs of
the attacker, the behavior of the attacker, the techniques and procedures of the attacker, so that we can know which attacker is the attacker. So, we have to identify any most conserved activities of the attacker As we can see here in the cycle chain of Michael There are 7 steps to the attacker's work The most conserved are the most data points And the most data points are the activities that are considered For example, there are persistence, let's remove, collection, concentration, command and control The point is that you have to print the calendar. That means that I will divide the cyberplot, the cyberkill chain into three parts. I will divide it into three parts. I will divide it into low
impact activity, medium impact activity, high impact activity. And I will say, I will start with this month. The next step is to say that I have the following weeks that I have the following weeks, week in the medium and week in the low end. This is the result of the result of the hunting calender. This is the result of the hunting loop. The hunting loop is here, we have four steps. First, you make assumptions and see what the attacker can do with you What are the indicators of compromise that can be shown in the network Second, I investigate my tools and look for the indicators of compromise I start to analyze the words that I assumed are present or not The third point is that
I discover new TTPs that I couldn't see The next step is to create the automated cycle that I am doing instead of the first and second step by adding the detection tools or detection controls
There are many tools that we can use in threat hunting. Some of them are very useful and some are not. I will explain them in a bit. But I have to look at three things before I choose any threat hunting tool. First, investigation or capabilities. What is this tool used for? This tool is used in threat hunting techniques. This tool is used in data set. This tool is used in Is it integrated with the 3D Intelligent or not? The second point is the support tools. Is 2D has standard support tools or not? I will customize it in the next lesson. The second point is whether 2D uses machine learning techniques or not. The last point is
the deployment of the tools. Is it easy to integrate with the tools? Data sets that can be investigated whether it is a certain number of data sets or not Is it possible to investigate such a thing? Is it possible to destroy the data if there is any indicator of the probability of the data? As we know, the players always come with different shapes and different tools and they always try to find certain things that most of the architects do which are the tactics, techniques and procedures for most of the architects So we will see now what are the tactics, techniques and procedures that have the highest effect on the organization and how can we start from
here First is the internal recursion, as we know the attacker wants to know where the host is and where the network is and where the right frame is The internal recursion has two parts, the host enumeration and the network enumeration The host enumeration knows the configuration of the host, the users, the hostname, the IP The network enumeration knows IP of this host, what access it has, what network box it has, what host it is around it. The point is the distance, how the attacker can connect or attack again even if we made a remediation or a start of the machine. So, there are many things. First, it is possible to Scheduled task execution Any task that is scheduled or scraped or any program that can be
run again after the boot or shutdown or another update can be run again by the execution code The second one is injection, which is an ejection program to the default port so that it can be connected after the boot or another update The next point is the gestation modification, which is the gestation run or run once, which is after the host runs again, this task will run or the session will run. The next point is the control command, which is how the attacker will be able to utilize the tools, how he will be able to connect to the C2 server. How do you utilize it? It uses two methods, common port and common protocol It uses common port and common
protocol to be used in the general connection It uses the unconnected connection to be used in the general connection
The next point is the login of the machine. How will the machine get the data and start moving from the vector host to the data base to get the data? First of all, the hash is captured by the hash of the log of the machine. Any user can determine that it is the log of the machine. The second point is that the whole boot desktop has the permission to connect to the server The third point is that if there is an internal web server in the organization and it is vulnerable, it will be able to run the web server with the permission of the browser The last port is the bus rejection that ejects the malicious code into the bus
of the legitimate application. The exfiltration is how the data is extracted from the Okay A4 with threat hunting techniques that we can use in threat hunting First of all, searching is to find the right searching criteria to get the desired result There are two things we should take into account in searching, that we don't increase the search criteria limit because it will give us more results than we want or the search criteria limit will be less So, the results are higher than we expected. The second technique is the Plastic. The Plastic is a collection of data. You can call it a Plastic or Rubik. You can collect the same criteria or characteristics. You can collect them and then you can get the data from them.
The point is that the programming is the same as the data processing, you can connect the data to a certain computer, but the difference is that you are the one who enters the input of the computer. For example, the computer is connected to me at the same time. The second point is the stack counting, where you can see the accuracy of the activity If you see a brute force attack, you can see its accuracy and how many times it has been done to determine if it is a brute force or a cold force These are the four standard techniques There is another point It is a machine learning, but it is a little bit advanced and not standard. You collect data and
give it a number and start learning from this data and labeling this data. And then you enter the data and label it. So, it will start to tell you the name of the most important thing that it has learned. And it will start to tell you if this data is the same attack or not the same attack. Okay. You will start to know your maturity, how you will measure your threat hunting program, what techniques you will use, what you will hunt, what the top QTPs you will hunt on it. You will ask yourself what you will look for to find the right data to start hunting. First of all, there are several points to consider when you are
looking for a process execution mechanism. What is the process ID? What is the privilege of the process? What is the value of the data access? What is the p-value? Who changed it? What is the last name of the file? What is the last name of the data? The network data render, which will be connected to the source IV and the destination IV, with the L-source port and the destination port. the file revetion that you need to know the file and the file as a whole the second point is the data sets that you need to know the data session who created the session from the user and the session who created the source and the destination
Prolog is a solution that can snap all the traffic in the network Proxylog is the log of any website that is connected to it The difference is what connection I will get to the water, what connection I will get to the perfect The switches will run the route, what is the communication between the network and the source of the destination IP The last thing is security data, which is threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence,
threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence,
threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence, threat intelligence,
This is the first example in the 3D map, it is connected to the command and control as we can see it is in the system number 6 in the cyber health check The attack in this attack is trying to connect to the command and control server through the digital port and the digital product port So, maybe someone will ask us what we are looking for The connection between you and him. I know the Abir Talquah server, the server of the Rodas server. If we want to see the data of the HTTP port, we will see the data of the port 80 and 80 data of the protocol, not the HTTP port. Then we will get the data and see what the result
is. Exactly, this is the problem. We will see the ProResLog, this is the S-ResolutionLog that I put through the HTTP log in SSL, and this is the NAS. What else can we do? We will automatically add another log to it.
Can you give a list of the reports that you have received from the government? For example, the reports that you have received from the government? Yes, I can.
The first thing we will do is to see the un-gifted connections that we have in the data set. We will use the bool 80 and the data set that we have in the data set. Then we will see the un-gifted connections that we have in the data set. This is the CPU server's RBID So this is how I did the RIGS algorithm Because I didn't use the same step I did the RBID of the Station Server And this is how it looks