BSidesMCR 2019: Exposing AWS With FlAWS - Mike Lehan
Show transcript [en]
thank you very much just the choice check I know they've had a people issues with the audio today can people hear me give her the back give me my pace all rather light give me a wave excellent I'm I'm Miley Han I'm a software engineer CTO of a student prop textile and northerner and the skydiver we can talk about that later of the bar you can follow me on Twitter and 1k and the cloud has produced a really great new way for people to leak your personal data to random strangers and so what I'm going to talk to today talk to you about today is how you can find out whether your cloud is leaking random data to
strangers and if you are responsible for managing that cloud how you can prevent it this is going to be focused on AWS and is relatively entry-level so if you come in here as a sort of hardened database pen tester there might not be much new for you today but what hopefully you would get is an idea of some resources that you could use to train other people in 80s security this is going to use a platform of floors cloud which is set up by a security researcher called Scott Piper officer maruka solving and who's very kind of let me use his resource in this talk today these principles are directly around AWS however if you are
responsible for managing infrastructure on Google cloud platform or as you'll a lot of the same principles are likely to apply they might be presented differently there might be different interfaces and different patches and holes that people are fixed over the time but essentially the core features of how you manage access and how users can inverting if the wrong people access will generally be consistent and flawless our cloud has presented as a sort of training exercise that simple is like a CTF so if you've ever done CCF's either competitively or just practice websites to teach you various skills in testing or hacking then you're probably familiar with the format forces in six parts so I'm going
to go through each part of the floors program the best thing about this hopefully is that it means that after this talk you can go away and do this yourself you could try and follow up a lot of the things I'm going to be doing are quite complicated to just do it manually it involves a lot of messing around in the console in your browser or typing commands in CLI so if you try to follow along you'd have to be really fast which you might not be the move for after a heavy carb lunch so this talk if you recorded the slides will be available immediately as soon as I finish on the besides works like and
so I encourage you to listen and what I'm doing and then afterwards go and try to sell yourself especially if you've never used any basketball it's a really great introduction to how you can start doing some basic testing and securing a various resources so challenge number one web hosting and public Commission's the challenge presented like this each time on their pretend challenge it gives a URL which is going to be helpful if you're a look at the slides later and the description on the website so this level is buckets of fun see if you can find the first subdomain so this is presented like a traditional sort of CTF hint and you need to know a few
principles about aid aggresses storage platform for this s3 is Amazon simple storage service it was not their first service that released but it definitely was the one that propelled their DBS into the use of lots of companies and to this day it's one of their most successful and most used services stands for simple storage service and the principal part of s3 is the bucket a bucket is essentially your area for storing some sort of files online a key thing is Buffett buckets are geographically located so I can have a bucket in London you can have a bucket in West Virginia and that plays a part however despite the fact pockets are unique to a region their host names the
name of the book it is globally unique and this is going to be important in a moment and funnily an object is basically a file it's a file always some metadata and so everything in ideographs refers to buckets and objects rather than folders and files an object can have lushes in its name which sort of makes like a pseudo file file structure but it's not really it's really a DST book it's are flats and you just happen to be pointing slashes in your object names that's not hugely important for the what we're gonna do today and web hosting has become one of the most popular uses of s/3 s/3 allows you to click a button in the console and host a
website directly from s3 and one of the key things about that is this book it having globally unique names your book is in a region before websites your bucket name much must match the address of your web player so if you want to host Google from a book it he needs to have a bookie called google.com I'd only want a diverse account in the world kind of hole in a bucket called google.com now obviously chosen ones like Google comm you also need Google's name servers which they're probably not going to give you to test it but if you wanted to do this you can do that it leads to a slightly strange domain sporting issue
where you can sort of predict domains that might want to host an s3 and future and just take their domain names I mean that's just kind of a dick move but maybe you want to have some fun with someone you know setting up a company and you can sell the book it matter than or something Oh s3 websites are also accessible at this longer URL at the bottom of the slide bucket name dot s3 website - region Amazon is calm so for example if you are hosting google.com from an address book it here big you'll calm s3 - website - say you're in London EU - West at $2 in NBS calm and this is
pretty useful for research so it's more stock cloud is itself hosted as an s3 static website and so the first challenge has told us we want to find something to do with that bucket we can run dig to find an airport floor soft cloud which gives us an IP address but running nslookup on the IP address we find that its s3 website uswest - great we know now that there is a bucket called floor sock cloud and it's hosted in the region us West - so now we have this ability to find what's in the bucket but obvious that doesn't give us access straight away what does it anyway us have a really great command-line tool
and the idea is you have an account you miss all the Kamala tool and you log in with your account and you do stuff on your account but the Kamala tool isn't fully restricted to using your own account it can be used honestly you can simply tell it don't look for my account credentials use any credentials you want and so we can do a simple lookup in s3 to check for this book it using LS which is very familiar for anyone who uses UNIX system so LS s3 protocol floors cloud and then there's no sign request parameter which says don't give any credentials along with this request I'm totally anonymous the way thing is people can absolutely block
authenticated users but not anonymous users because address and in this case we see secret man hash and that's the way the rest of these levels all work we'll find a secret page and when we pass our secret page we will get told you found a secret file go on to the next level the mitigation of this is that when you enable website access s3 adds a policy and these policies are used to control access to all resources in any way that's not just s3 so if you want to use anybody s a lot you're going to have to learn that policy language it's known as I am identity access management and the policies have this very similar format
in JSON so they add that positive to you so that anyone can access your website what a lot of people do though is they panic and go on reflects not working because they aim on the policy that inste try and be their website and it can take a few seconds so then they go to this page and they have say oh look there's an access control listing and I need to allow everyone to list my objects at this point you've exposed the entirety of your book it permanently which means even things that aren't linked in your web route could be accessed by anyone using the address command-line tools we'll see why that could be a properly dangerous it's a bit
later so we're on to challenge number two and this uses the access controllers as well so again we've got the level ID at the top therefore if you follow this on the slides later you can jump straight to a level and cheat your way through this and we say the level is similar with a slight twist but you're gonna need your own database account setting up your own NOS account is pretty helpful if you want to be testing anybody s for someone else obviously if you're running on any BS if you all have an interesting out but if you're testing stuff it might be helpful to have a separate account for running your testing in I'm definitely recommend
splitting out any BS accounts for different purposes wherever possible [Music] when you create an alias account you get given route credentials and as is standard practice don't use your route credentials for everyday access you can create a user and you can give it an admin access policy or you can give it a more specific policy than what you're doing I'm not going to come out here because I could do an entire talk just on setting up your initial database account there are plenty of tutorials online to do that the key thing here is you generate an access key you'll see a security key for it and you can insert this into the console so if you go into
any PS of type configure you can give it a profile name so let's say you're doing this after the talk you want to type a profile be size 19 and then put in your access key and secret key and now you can run as that user on that account for the work you're doing here and it won't affect any other LMS accounts that you happen to be running with on your system and you can put in a default region you best west to is good but this because everything is hosted in u.s. West to this exercise and now we can simply do the same thing when you're lost I'll put now with our own profile
and uh if we'd run this with no sign requests we'd have gotten access denied but suddenly even though we're not the account that is the Bukit we can see all the files and once again we get on to the next level the reason for this is a canned access control list doesn't have a set of Canvassers control lists how easily can you see that there you should see it relatively easily and the different Isis control lists can be applied to a bucket or an object to allow different levels of user certain accounts certain groups of users things like the ADA best mod delivery system access to your buckets it can details are great for quickly setting up buckets
and easy security fencing but they're also great for not quite understanding what they do for example this can be a CL is about authentication so the only it's full access and authenticated users get full access so to me an authenticated user means an authenticated user of my system so if I set up a bucket and give it this ACL I expect other users in my a degress account can access it anyway this language is slightly ambiguous here authenticated user means any user of AWS in the world and at this point you apply what looks like a secure policy to your bucket and anyone with an MS account which is free to set up can go and view your bucket this was easy to
apply it all the roof of the console they have removed that now because it was such a big floor but it's still possible to apply in the command line and a lot of old tools that kind of create s3 buckets for you and do like a lot of setup for some sort of data storage maybe for something like WordPress as a content management system stories area may still use the old ACLs so do check when you're installing these whether they have these ACLs attached to ok on to number three a whole new way to expose get once again we have the URL there and this is similar to the previous levels but we're going to find
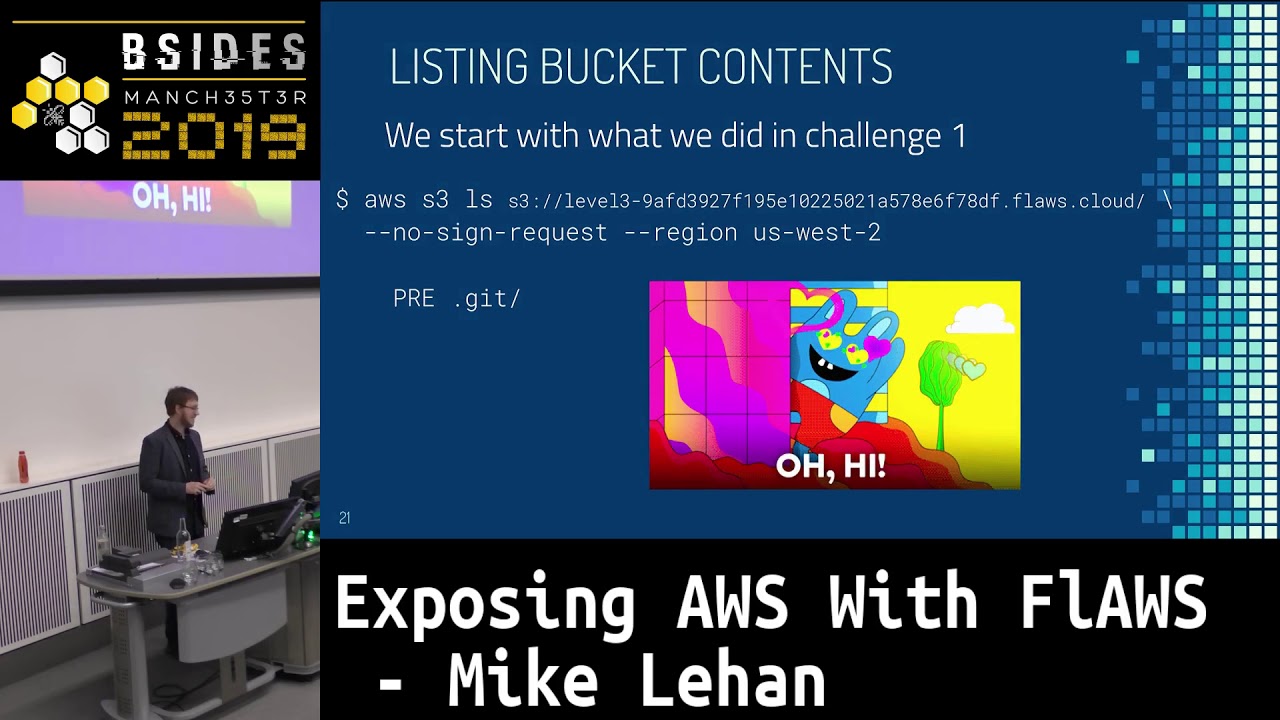
that AWS key any of us keys are really the bread and butter of any sort of attempts a hack or test any res accounts if you have a key you can probably do something that someone doesn't want you to do we can do the same thing we didn't challenge one so we go on how we list the to the Bukit with no sign request this pre symbol appears in our command output is prefix so even though they don't technically have directory structures they will tell you this is the prefix you can look inside it and here's a prefix called docket ah hello what you reckons happened here well some poor soul has uploaded their docket file
let's pull it down to our system we extracts it using s3 sync and now we find out within a regular git repository and we can run git log we see some commits we see the first commit and then we see another commit home I've added something I shouldn't have done using it we can now check out what's in that first commit that the second one did so going to check it out I'm going to an LS a look access Keys dot txt probably more regularly named than it would be in a real scenario and now we haven't any BS access key and secret key let's check if it's still valid we've run a TS configure with a new
profile name so we can keep sort of ramping these up and store them as we go to continue our test and then we can run some commands as this key so let's list all the buckets on this account and we see an bucket called level 4 well don't run to the next level now another vulnerability was needed to expose this problem they already have this open bucket but actually if you're building website a static website what's the likelihood that you'll simply sink your entire directory oops in a TBS now the IDS sync command ignores dot files by default until you add a whitelist include or what or blacklist exclude flag at which point if you add an S to
flag it will then include everything you didn't s clewd which can include your dock your file directory and so now you've synced your kit directory to your web server and that access key might just be used for this simple static site people use such as us a lot in businesses something like a marketing sort of marketing campaign how likely is the marketing department to roll their keys regularly how likely are you to have just given them a key that has way more access than it needed to for them to run their marketing campaign you know you've got that email from them while this isn't working again and you throw your toys down and you could add
admin access to them for their for the week you say well I'll take it off the end of the week and then life happens and suddenly your keys being exposed you can look at this and guys it's all hypothetical this happened to Instagram it was reported as instagrams million dollar book because instagrams security team famously said they would pay a million dollar book bounty if one was found spoiler alert they didn't pay the bounty instead they sent the FBI happened first and found it so Google that one you can find a really good rise up on it eventually they paid a bit of money but make sure to ignore docket files bore so don't commit your credentials in the
first place this is source security 101 credentials don't exist in version control or just anywhere near something you're deploying and if credentials are expose don't just do a commit and hope no one notices role the credentials recreate them and that's another good reason to use separate credentials for everything you do because if you expose your providential as on some random marketing website they need to roll them and they're the same credentials now prod us to go down watch you finish your potential so separate credentials for every use case is a really good lesson from this as well we're going to learn to break into servers by cloning their hard disks this is something you couldn't do before the cloud so once
again we have a lower URL and you're going to get access to an easy to running at this very long subdomain and we're told that a snapshot was made of this ec2 instance right before nginx was set up on it let's go over some jargon ec2 is Elastic Compute cloud basically Amazon's VPS offering and the snapshot is a full copy of a disk stored in s3 now unlike a lot of things in s3 buckets you can't access it through the regular s3 command line but it is essentially in s3 and at me that's inherent to a lot of the sharing and access resources that s3 is your formal to and EBS is elastic block store basically hard disks 80 refs
have to give an acronym to everything they do so hard this become EBS etc but after a while you learn to speak in acronyms and you say cleverly taught some headers and thought about snapshots often made public to transfer them as been accounts so I want to move my account that's doing everything after one account is doing prod staging dev marketing testing analytics all this sort of stuff I'm hosting us a random katfoe is in there for my life and actually I decide maybe that's not good idea I want to move to multiple accounts that make a sensible structure for my organization but I mean there's all my images that are built on my servers need to be transferred there
are ways to do this to involve changing permissions on both sides and using interesting command-line tools the other way to do this is to go into your snapshots and take make public and then send the URL to someone else this is a common way people transfer snapshots and guess how many people forget to punt it and make public box afterwards to find out snapshots on an account all you need to do is know the account ID so let's go back to our hacker credentials from before and we can use this get call identity command this is really handy for when you're testing if you find some keys the first thing you want to do is
run this and this will tell you who you are and I know the account ID now of someone who I can look for easy to snapshots and so now as anyone not just as the user there I can do it as my own account I can check for snapshots owned by that account ID and I'm putting here region uswest to just didn't think because you might learn it if you've configured it the right way but I often add the region just to make sure I'm in the right place if you really should be doing a test and you admit the region one time and you totally missed something that's blatant and obvious so always try and people for both in in
anything you're doing here for testing and look we've got a snapshot staff ID real on hash and hey it's not encrypted that's good news for us so we can now do this this is a long procedure this will take you probably 10-15 minutes if you try and do it yourself I'm not going to in front of you because that will take up all the time I have and so I'm just gonna walk through what you do go and try this yourself it's quite interesting you create a volume using a snapshot ID so a new EBS volume new hard disk and then you create the new easy to your instance and you give it your own key to log into so when you
create an instance even give it a key even if you're using someone else's hard disk image you can give it a key enabler for just inject a key into the system for so therefore you can always login even if you're shooting someone else's disk image you sign this is for that key and then you mount this extra volume you've added to it the commands are mounting different / OS but you should be also find those up fairly easily and so we're on this disk we've got our instance we can SH into it because our instance this isn't anyone else's system now the nice thing here as well is that once you're exploiting a snapshot anything you do on
here isn't likely to hit the original target so you can do quite destructive things testing here to find out whether it be vulnerabilities in the original server and look we found a file sets or nginx fire stage again well better name than any of the files you tend to use you know attempt 3 dot H dot back and so let's have a look what's in it and we have a HT password commands that's saying a pasty password file in our nginx setup and as you may expect we can now browse the original URL and we enter our username and password for HTTP basic auth and we get the link to floors level 5 where's I'm instigation for this don't
open snapshots to the public unless that's forgot if it is your goal I'm quite wondering what you're doing but also be careful the process of creating a disk image is very different from the process of writing some sort of provisioning file because when you write provisioning file you know exactly what's in it you can read it when you're creating a disk image you're not always certain what credentials you invented at some point that might be stored in a dot batch history file stored in the temp directory stored in logs so if you do want to make it easy to and share it publicly for some reason really check how you've built that and make sure
there's nothing sensitive on it when you are sharing share with one specific accounts you can do this it's a bit more complicated but if you know someone else's account ID to transfer an ec2 instance you can share the account I'll find a way to encrypt snapshots when everybody encrypts a disk snapshot you need to permission to access that snapshot one permission to look at the snapshot which we had because it was publicly but the second thing is permission to use the key that encrypts our snapshot and keys are much harder to accidentally grant access to someone else you have to go and say I want to give this person access to my key and the nice thing is if someone gets you of
this snapshot which is public and tries to decrypt it without access to your key you'll get a message in your logs saying hey someone tried to use your key they didn't get in they tried to use it and now you someone's trying to venture into your system and take the distaff shots which means you can firstly make them private and secondly you know you've got someone targeting you that might be a pendant or you've employed and yet which is good you can say hey we're aware of this or it might be someone malicious so be aware of that exposing credentials via proxy this is a fun one this is to have a simple HTTP only proxy on it and
there's an example growing never at Cellcom through a proxy running open boxes isn't something most people tend to do but is something people can do accidentally for other reasons and to exploit this we need to know about the easiest view metadata instance every store instance has a server brewing locally to it which can be hit on one sixty nine two four four one six nine two five four if you hit the server with a HTTP request you get a really long list of commands and information about the server that you're currently our anywh esq is this but also Google cloud platform users they might be addressed as Ewing is this same IP address to host
information about the server that you are running on which can include loads of random and pointless details also could include things like security credentials and this is useful for the system because it means that if I'm writing an application to run on ec2 and my application doesn't need to find credentials I have its own credentials to access area services I could simply provision an instance with a role that allows that instance to do something anywhere say create and us three bucket or file in it and that's a really handy way to limit your security because your instances and your code base doesn't have access keys in anymore but we have an open proxy on this system
so let's curl it so we're curling prop the floor cloud address soft proxy and the metadata server as you might have expected with my long preamble we get into it the first set of listings you get is API versions each time they add new things they roll the version so that they don't break all things which don't expect things to be there or so the format's but you can generally just use latest if you're testing what's available in our latest so we have a whole list of things but you'll hopefully notice one right in the middle on the phone column there that says I am identity access management and predictably if we go into it we get an
access key and a secret key we also get the token and that's interesting because this is using not a database user account or group but a role and the reason it's using a role is because that's how instances are given permissions roles were excited differently to use this the user has access key and secret key they can just access any BS with anytime a role uses its access and secret key to generate a short term anywhere from 15 minutes up to I think four it's 48 hours it's other limit and might change key that can then be used in perpetuity for the time to do things so therefore if you want to exploit this you can't just say the
access key and secret access key and your talk will only be valid for a certain amount of time or expires so if you get hold of this you have a time limit now on your further test with it unless you can just go back and abused a proxy a second time so we're going to put these into our aggregate credentials but we have to add an extra field we have to edit this a degree exponentials file where we have the name of our profile whether we put the access key and secret key and z and then add this session token' and you can use the SDS accord entity feature and other features to find out how long you have so if the
person is smart this has a token my on your last 15 minutes that limits what you can do in that time and hopefully by that point they've spawned in the logs that someone's hid their proxy the other day if they're not monitoring it though you can just keep getting a token again and again and again and keep exploiting them it doesn't matter what time limits on it so let's use these credentials now and predictably we get a address to another file in this directory and we can go on to level 6 what's our mitigation here don't run proxies would be my number one thing the chances that you need a publicly accessible web server running a proxy
that can proxy any website on the Internet is pretty low maybe you have use cases I would love to hear about them but in general if you can help it don't run proxies through public less or web servers if you do need to use a white list of allowed proxy domains you probably don't need to proxy the entire internet unless that's you literally your point of your service you can specifically block the method ater IP in your proxy or you can use a wife to block any request that comes in with that IP string in it do be aware that various X points exist for a lot of common wefts that people can find weird ways to encode a string so that
the laughs doesn't see it but it still goes to the proxy eventually so you have sort of walking on eggshells point where you're trying to block sir and IP addresses should be entered in query strings or headers so the nuclear option is you can use route tables on your instance to block anything on the system accessing the method a service this will also hose any application on the system that relies on the metadata service existing to get credentials - it's not that useful but I guess if you were running an easy view server that was doing nothing with anything else on any bus this would work for you I don't generally recommend it our final point here is the insecure
security audit I'm always very suspicious of anything being given out with the word security in it that turns out to be insecure that seems to be this kind of false confidence thing that generally leads to people ignoring the thing with the word security in it because oh that must be secure we'll look at all the other things so this final challenge you're going to get a user access key so you're gonna have to make another leave account with this user access key and secret key and you've been told by the challenge that it has a policy called security audit security audit sounds very formal and very nice ah I can order some security with this policy that's really useful
and this exploits very common thing in any BS which is the canned policy anyways have a lot of manage policies that they provide to do certain things that anywhere slightly happen access one which just grant you access to everything and you generally you if you give someone up in access you sort of know what you're getting into but if you give someone something called security order you'd expect are they can they can audit my account that it's secure but that stuff the end of it right that's not a hugely important account and there's a number of any best policies that have this kind of risk the most common thing they do is that they need s3 access at some point so
they need to put some files in s3 to work properly and what they do to do that is they just grant full access to s3 and which is great for listing buckets and things but now if your story database backups in s3 that policy also allows anyone to download your bandwidth backups chances are even your security auditor probably doesn't want to be given access to your database backups or anything else that sense in s3 there any ones we have to get the things that they are auditing they're probably not Oddity in the content of all your files that you're storing there and overly permission are is policies are just very common another keyword is the session
manager policy if you are using session manager at all if anyone knows that addressed is using that the default session manager policy is insecure and if you're using it on a role that role has way too much access to s3 go and find a better one comes up anywhere support they will give you a better policy for that so let's have a look specifically at security on it this is a cam policy which allows examination of resources in an account it allows viewing policy content and here's a key thing for privilege escalation if you get an account access key the next you need to do is know what your account has access to by default any risk doesn't
tell you that and there's a reason for it because now if you start something from a list buckets and you can't that pops up in the logs of whoever owns the account hey someone's using this key list buckets but they're not being there being blocked and now you know that someone's obtained the key to your system that they're trying to use maliciously if the user can find out what policies are attached to their account they now know exactly what actions they can or can't before now that might mean that they can't form any decent actions but it also means they can now evade detection for anything else they do in future you now have no
way to find out if that user is doing anything malicious so so you've granted one of your Regulus team members secure if you order along with a few of the permissions someone now gets into their account and use your security on it they can find out who they are what they can do that won't raise alarm bells and now any other permissions that user has are open to them and they can find out anything they can work on in your system so this is a classic routes of privilege escalation once you do someone's policies you probably know way more about our organization than you need to and you can work your way from there I'm
also likely to refuse like users and obviously if you find a username you can then go and check a publicly available database of leaked passwords like username and maybe you get in that way and to actually exploit this on floors like cloud is really it takes lots of individual steps I need to onto my complex none of them really have anything to do with security and more to do with specific resources that exist in a dress so I encourage you really to go and try and do this yourself with what you've learned but if you do do it you'll get through to the end of floor stop clap and summary you want to roll credentials regularly this
is a general practice that you should be applying everywhere ADF's credentials generally hold the keys to the kingdom for most companies running on any breast rather regularly rather than immediately if you suspect they're being compromised and check out Adrienne volts for secure credential storage apply at least privilege on I am and seize any user role group anyone that sax SNES find out what they need to do don't give them admin and then decide to restrict it later because later is too late you won't know what they're using you'll block them from servicing production website to stop working I have policies one at a time add provisions one at a time find out if the user can do what they need to do and
then stop s3 has released a new public block public access feature in the last few months I would advise using those if you don't know book it needs to public click the big block public access what this does is override policies and access control lists on a bucket permanently but still understand what's under the hood because sometimes you might need a service a bucket to be public and these kind of nuclear solutions will break things for you finally if you're a pen tester checkbook it's fine creds and examine policies and hopefully you're going to get somewhere and get your report done or your bounties claimed thank you very much for listening I am NOT evil of questions
because I've used all my time but I'm going to stand in the hall out there and I won't talk to me and I'll be at the after-party as well boom you can check out the slide which will be on this URL here as soon as I get outside tweet me if you like this if you didn't like this if you have complaints if I misled you with the title and check out oh gee lbs on slack it's a great group really great security channel as well in that so come and talk to people be nice ask questions and thanks again to scott piper for providing floral cloud and there is now floors - if i don't wants to go further
with this hopefully i'll be doing a talk on that next year [Music]
you





