Employee's Personal PC: The SECRET Gateway for Hackers! #shorts
Show transcript [en]
What happens if one of your employees says, you know what, I want to log into Slack from my personal computer so I can keep up to date with chat when I go home, you know, that way I can, you know, talk to people about stuff. And then their kid comes along playing Roblox or something and installs some like Bitcoin mining info-stealing cheat code that they found on the internet. We've had this happen. And then they steal that Slack token. And now that Slack token's available on the internet. Do you know how long a Slack token session lifetime is? It's forever. How often do you have to re-log into Slack on your application on your desktop? Almost never, cuz that'd be
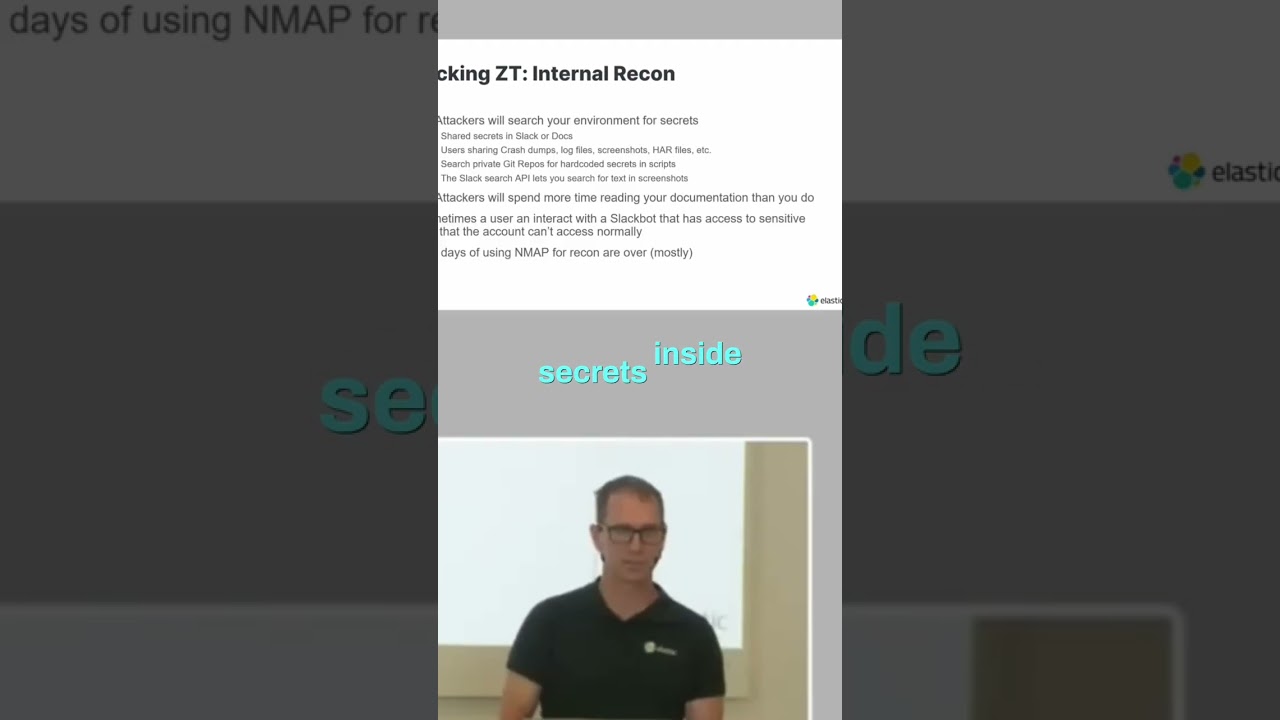
annoying. Same thing with mobile, like your mobile applications, like your like how often you have to log in and re-log in on your phone if you have that your email, all that stuff. Those have really long lifetimes, and so those sessions, they may not get access to everything, but the attackers can get access to that application and from there start pulling the threads and gaining more and more access. Once they get those access, then they do recon and they start hunting for secrets inside of your environment. Um you if you're not hunting for secrets actively in your environment, they are out there and I trust me, they're everywhere. They're in docs, crash dumps, screenshots, all over the place.
Um the attackers will spend more time reading your internal documents than your employees do, trust me. They will learn everything about how the environment works, how everything synchronized, how you onboard a new employee, how you offboard an old employee, um if you purchase a new SaaS application, how do you join that to your IDP? They're going to read all of those documents. And they're going to look for all these these gaps and these ways to abuse it.





