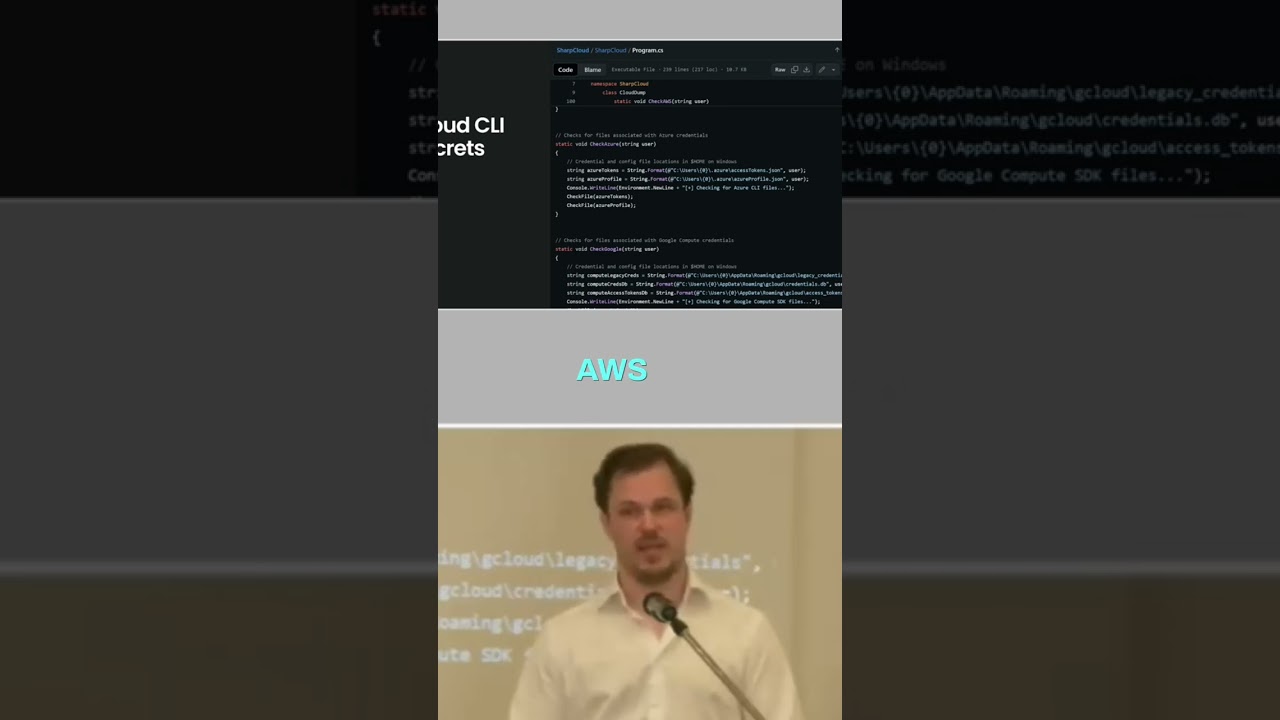
Secure Server Access: Cloud CLI Authentication Explained #shorts
About this talk
When networks are locked down, attackers can exploit API access. Learn how they use CLI tools to authenticate tokens and gain control via cloud init commands on compromised servers. #CyberSecurity #NetworkSecurity #APIsecurity #CloudSecurity #Infosec
Show transcript [en]
Assume that you have like a fairly locked down network. It's only able to access APIs from this specific server. What's going to happen is that someone is going to remote into that server. Then they want to use like Google Cloud the CLI tool or you know, you have like AWS CLI, you have AZ and so on for the different vendors. But what happens is that they log in, they then are on that specific server. They do like a cloud in it or whatever command and they need to enter and authenticate the token and that's going to be saved in their user profile.





