Jenkins Security: Secret Exploits and Old Servers #shorts
Show transcript [en]
We see that there is a connection from a internal Jenkins server. Does anyone know about Jenkins? I guess. Um, when I talk to we do a bunch of different stuff at TrueSec, but when I talk to the uh persons doing like DevSecOps and so on, they say that yeah, it's not that many that use Jenkins anymore. It's usually like GitHub Actions or whatever that's trendy like everyone is going to use right now. But we actually see quite a lot of companies from my end which work with companies that are affected by breaches that they have that really old very important Jenkins server. They're built completely like built into it because of like they developed plugins and whatever. And it's
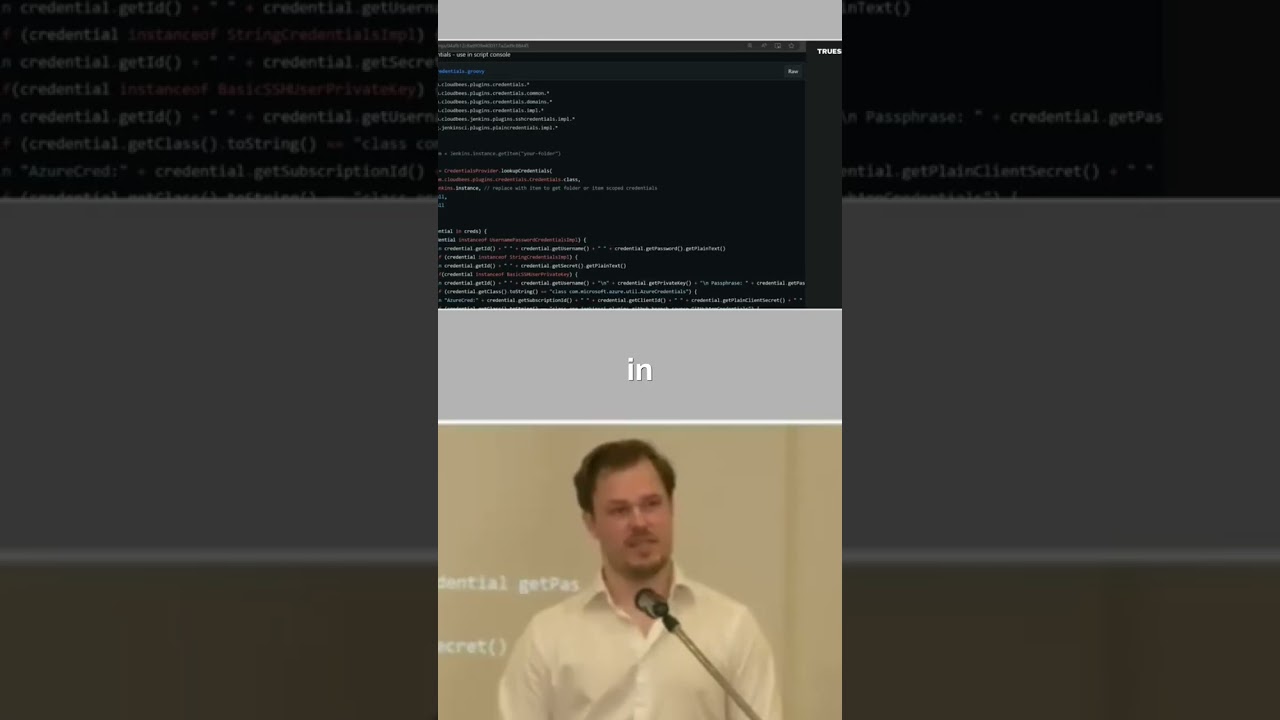
just like this massive Jenkins server that is responsible for building everything. And it's really hard to maintain it. So what's what's not to love about Jenkins? It has this kind of awesome feature that if you're logged in as admin, it has built-in code execution. So, as it right in there in manual, so it has like a it's a groovy console and you can interact and run OS commands. You can also run like a simple script to dump all the secrets. And guess how many secrets you have in Jenkins if you have one big Jenkins that is responsible to, you know, pull code from repos, push it to where it's supposed to run. And like all those secrets that you have to run
your entire production is going to be in Jenkins right? And that's what we saw that we saw that they did that in this case. So, by carving the file system we found this deleted file which contains a complete dump. And actually it has this weird format of like output format. You see it has like class space colon space something. So, we're fairly certain exactly what script they used which it was from like an online tutorial for how to do it. Um, so So, yeah, that that would be the first step right?





