Slipping The Net: Qakbot, Emotet And Defense Evasion
Show transcript [en]
perfect so hi everyone thanks for coming along yeah so my talk is slipping the net quackpot emotet and defense evasion uh a little bit about me first so I am Kean Heasley um I don't do a lot of social media these days but I on LinkedIn if you want to add me I have my personal blog site here Blu tangle dodev so if I'm researching things outside of work and I come across an article that mentions a technique that I don't see detections for anywhere or I go looking and I think oh how would I detect this I'll throw up a blog entry there so a lot of it's around defense evasion or attempts to uh basically um disable
security control stuff like that uh so I'll just throw up some very simple usually Splunk SPL or something there um I'm the threat team lead at Ador security we're in mssp and we do security Consulting and we have offices in London and Edinburgh where I'm based um and that's me just outside our office actually so just to run through what we'll be talking about today uh introduction which we're about to jump into I'm going to talk about what is quackpot essentially what are we talking about when we talk about quackpot a little bit about quack bot's history um what is emotet a little bit about uh emotet history uh the OneNote campaigns that we saw from emotet quackpot earlier
this year a little tiny bit about emotet attack chain iteration so how they go about their attack chain once they get the malware onto your computer with their fishing emails and then a more in-depth dive into quips attack chain iterations so little changes quackpot have made this year to try and Dodge uh your EDR detections your seam detections AV detections and it's something that I had to keep up with as part of my job and something that I found really interesting because it literally change dayto day they would tweak little things here and there to try and get around detections quick conclusion and then there will be time for question and answer at the end
so I think a lot of people and I go to a lot of talks where people talk about quib emotet as low sophistication as something that you know will be caught by uh email controls antivirus EDR controls but I want to make the point that when we look at these UK government statistics here for um uh both companies and businesses the kind of attacks they're seeing fishing is way up at the top here so 79% of companies um had fishing attacks 83% of Charities had fishing attacks now those weren't necessarily successful but those are the main attacks they're seeing when they when they talk about you know what kind of incidents they've had in their
environments so I want to make the point that low sophistication works and fishing works there's a lot of money in fishing there's a lot of effort Behind These groups and the malware and the infrastructure and everything else and there's a reason for that because it does actually work they manage to compromise people and we'll see that they they then manag to sell this access on so before when I was writing this talk I looked at uh statistics sort of year in review from big companies crowd strike Mandan uh around incident response and threat hunting and what I was trying to look at was the percentage of initial access that they say is fishing related the simple answer to this is
each company has completely different statistics so for some of them um fishing will be number one so it'll be something like 42% of initial access will be through fishing for others most actually it is the second so exploitation of public facing applications has moved up that's probably because of mve it because of various VPN um vulnerabilities uh things like that and then down at the bottom is your stolen account credentials but to be honest fishing can feed into these stolen account credentials so this is almost a loop here these last two uh this is a a good diagram from the ncsc they did a report on ransomware as a service and the sort of extortion e
crime um uh landscape right now and this came out a couple weeks ago just a really nice diagram so you've got your direct exploitation that would be exploitation of public facing applications you've got brute force and then you've got your email distrib ution which then goes through um uh traffic um determining system so it'll decide where to pass it onto and then you've got your Steelers or your loaders loaders can then you know load on ransomware Steelers will steal your your credentials which follows back into this third here and then that goes to a Marketplace and then you've got your post exploitation tools and potentially run somewhere at the very end there so they're very much part of the same
ecosystem but fishing is something that that does work we do need to worry about so I said we get a bit into the history here um quackpot is actually 16 years old so this is uh Microsoft published this May 20th 2009 quackpot this is a little bit there sort of definition of it if you get this in your Defender you can go here and it'll give you a little bit more um context around quot so in two years qub will be old enough to uh to vote um Joe Joy salvio discovered emotet in June of 2014 so otet is is a a younger uh fishing framework um as we'll see otet skipped a lot of the awkward years
that that quackpot had we'll get into that and uh this is one of the the first ever quackpot fishing lures so originally as we'll get into as well they only targeted uh I think it was German and Austrian Banks so they were very very highly targeted we think of emotet now is just sending out scads of emails to anyone who uh who they can reach but originally it was very very very limited in who they were trying to Target and why they were trying to Target them but it was always about banking so QuickBook um AKA ta 570 crowd call them Mard spider secure Works call them gold Lagoon they're also known as cuot cbot with a u which I I don't like
and pink slip bot um they are now a fishing group but they're also an initial access group uh they originally a basic banking Trojan and possibly the First Banking Trojan so the first Trojan that was specifically designed to harvest banking credentials and send those back it was first tested in the wild in 2007 although it the campaigns didn't really start on 2009 so there were isolated samples that were found in 2007 of the earliest versions of quack bot while it was in development but 2009 as we'll see was when it properly kicked off quackpot are believed to be primarily Russian unlike emotet there's never been any arrests of quackpot members or the people behind quackpot so
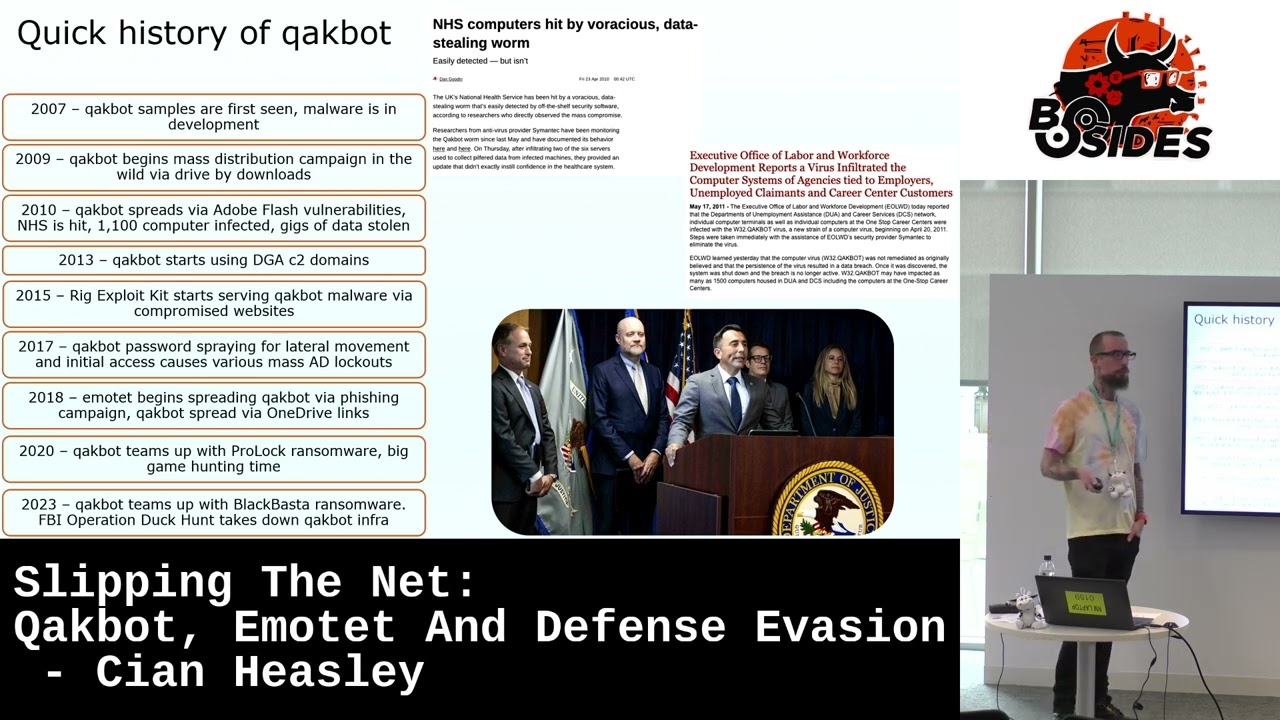
there there are the people that developed quackpot the people that distribute quackpot people who run quackpot infrastructure and then there's Affiliates so we're talking about quackpot as a group and a malware and a bot net at the same time it doesn't quite line up but we just have to go with that because otherwise it gets quite complicated um and they are now malware as a service so they're loading other malware and they are infrastructures to service so you can rent parts of their infrastructure um or you can rent parts of their their malware and what their malware reaches this is a quick history of quackpot I had to cut a lot of stuff out here um so 2007 as I mentioned before
quackpot samples are first seen malare in active development 2009 quackpot begins Mass distribution campaign in the wild via drive by downloads so initially quackpot was browser based malware so it was trying to quietly install itself um it was hoping to exploit various uh vulnerabilities uh similar here with 2010 cbot spreads via Adobe Flash vulnerabilities remember those uh ABS nightmare um in 2010 the NHS hit 1,100 computers infected and I think it was something like 6 gigs of data was stolen um and that's a little bit about it up here so that's an article from the time from I think it's the registry talking about NHS computers being hit by a vicious data stealing worm and this
over here it didn't make it into my timeline because of space but in 2011 the uh executive office of Labor and Workforce Development in is this Massachusetts was also hit and and they had a ton of data stolen as well and they had um people's uh Social Security numbers in the US uh stolen a bunch of data was stolen there too early on in in kot's career there wasn't a lot of these big um organizational wide compromises it was mostly individual users individual people uh you know accidentally opening the wrong email but there were these large sort of um Omens of of you know future full organizational compromises 20 13 qu botot starts using DGA C2 domains uh one of the things
you'll see if you look at these these botnets is that they change the way they handle C2 a lot so this is something that evolves as people start detecting them or trying to find them they'll they'll come up with ways of trying to obscure them or trying to get around you know detections um 2015 rig exploit kit starts serving qub malare via compromised websites so this is another thing that you still find today um when that first stage of qub emotet is loaded on a computer frequently it will download the next stage from a compromised website and that helps them get around any kind of uh domain um monitoring for like newly created domains or domains without any um
previous interactions so they can use those uh 2017 qub made the news they were password spraying for lateral movement and it caused Mass ad lockouts in a number of large companies so essentially they got access to one machine and they thought they were smart they were trying um password spraying within that organization of uh what they thought it were like standard usernames and passwords but because of AD lockout um they were causing Mass lockouts in companies so um people were logging in on Monday and finding that all of the accounts in the company were basically locked down because quot had been trying to access them in 2018 emotech begin spreading quackpot via fishing campaign and
quackpot then is spread via one drive links this is another way that you know trying to get around security controls so instead of hosting the malware on a compromise site you stick it on one drive you stick it on Google Drive somewhere where it's unlikely to be blocked it's more difficult for security controls to catch uh 2020 quackpot teams up with prologue R somewhere and this is big game hunting time so this is deliberately trying to hit large organizations um get a foothold in a large organization quackpot then hands that off to prolock ransomware and then 2023 quot teams up with black bastter ransomware and that was uh the beginning of this year um and then FBI operation
duck hunt takes down quot infrastructure and this is the announcement that was two or 3 weeks ago um in the last 12 hours I have seen a number of new stories actually that relate to emot in quackpot and one of the ones I saw earlier today in between talks was that quackpot affiliate has now started pushing dark gates malware so none of the people involved with quackpot were actually arrested um their infrastructure was seized some of their cryptocurrency was seized but unfortunately the people who are developing it the Affiliates the people who are running the infrastructure all of them are still free fre to to go about rebuilding things and I think they're doing that as we speak so um
when we talk about quackpot being taken down I think it's wishful thinking I I would love that that was the case but there's a lot of money on the table for them and this is a quib shied hole in the ecme infrastructure um ransomware groups rely on them initial access Brokers rely on Stolen credentials there is going to be someone who will fill that void and if the people who are themselves are not arrested or or stopped from from just reconstituting things they will rebuild so emot um AKA mummy spider Crow strike ta 54 Hodo geodo or gold cabin is secure Works um people ask so I work in thread Intel and threat hunting why all the
different names the simplest way to explain it is that different companies see different things so you may think why don't Crow strike and secure works just agree on a single name but they both based on the Telemetry they see may see different aspects of of mummy spider or emotet so their definitions of what emotet is might be very different from each other when it comes down to it and it is better to have those are separate it's annoying and I work in thread Intel and I'll be honest I have to sometimes keep spreadsheets which links all these names together but it does make sense so otet is a fishing group they're also now an initial access group um first
appeared in 2014 as I said um the malware emotet the group name is known as mbug although interchangeably you could call them both emotet it's suspected that they're based in eastern Ukraine and I'll get on to why that's more than suspected they are now a loader for other malware and similarly to quot malware as a service and infrastructures of service and I'll get on more to how they handle this infrastructures of service in a a better way than quot [Music] does quick history of emotet so 2014 as I said emotet first appears spreads via fishing links initially targets Austrian and German banks exclusively that's all they do fishing lures all of that all of the um the links from themselves all
designed for Austrian and German banks 2015 they expanded to Target Swiss banks as well and they introduced this modular design so they can add modules to their initial malware and so they add dbos and email login theft modules 2017 emot begins downloading and loading additional malare like dryex uh and then emot borrows lateral movement Brute Force technique from want to cry and not Peter uh 2018 emot Tech forms distribution relationship with trickbot the info stealer and quackpot as I mentioned in history of quack emotet begins harvesting entire email contents as well as contact details and web browser credits so they're constantly expanding what they can steal from systems that they infect and then I'm I'm assuming ways to monetize that
stolen data 2019 emotet introduces EPO so I talked about infrastructure as a service emotet in 2019 introduced Epoch you may have heard of it before you may be familiar may not epochs are essentially entirely separate bot Nets so they have their own C2 infrastructure they have their own update Cycles they may have slightly different versions of the emotet malware and then they begin using compromise host as proxies to obscure C2 infra and this is something that clarot does as well so you have your C2 infrastructure here that's proxied through infected hosts at one layer and then maybe another layer and then maybe a third layer so if you're at that bottom layer and you're trying to
figure out where the actual C2 is you would have to go through those proxies have infected other hosts and that's a way once again for them to prevent people taking down their C2 or blocking their C2 and it's also useful because the infected hosts are frequently in residential areas um you know they're not something that would normally trigger as suspicious um I think qu and emot have also used these proxies and they've sold them to people to use so that you can if you're attacking a company inside the UK you could rent um compromised hosts and you could then proxy your attacks through those to avoid geolocation or geol blocking um in 2020 emot had a bad year
emo crash was released and this isn't an email to um CB requests saying we found CBE and emotet and uh the response was sorry CBE IDs are not assigned to bugs in malware but it was a nice try um and so that crashes emotet installation so I think it was a registry key if that was in place emotet installation crashed could be wrong about that and also someone hijacked emotet c2s and distributed memes instead of payloads so this would have been a compromised site you would go there emotet would expect to find the next stage for its loader for its M and instead they get hacker so 2020 was a bad year for emotet 2021 was a worst year for emotet
I talked about eastern Ukraine this is still images from the Ukrainian cyber police essentially raing uh a home where a number of emotet operators were living this is a computer that I show people at my work if they complain about their home PC setup it's amazing what you can do with a Dusty PC with no sides and bits hanging off of it but they made it work so as well and a soldering iron and all kinds of just random stuff there's so many photos I went through a ton of these on a slight tangent because I'm the last talk today so it doesn't matter about time I looked at um all of the ransomware bus and similar bus from the
last three or four years in Eastern Europe they tend to post a lot of these videos and photos um a lot of the the flats that are raided or the apartments look like this so they look like in America would be a fraternity house in the UK you'd call it a UK party house I guess like a student party house um the ones that did interestingly was uh klopp klopp had home offices that had brand new iPhones brand new iMacs uh sorry MacBooks brand new standing desks everything was Immaculate they had filing cabinets it was properly set up like a better home office than probably anyone here has um I uh there was a couple of other ones that were equally
like sort of dingy and decrepit the important thing though is that they had that computer hanging apart but what they also had was little gold bricks hidden all through their Apartments um so once again we can laugh at them we can laugh at their computers and their tradecraft and their setup and their janky way affecting computers but they still managed to collect all of these little gold bricks after all of it um the other thing that was amusing me about looking at recent raids was um the Russian government for some reason raided revil just before the Ukraine war I don't know why and so this was the depth of winter in Russia but if you've
ever lived in Eastern Europe the apartment blocks are the stalinist apartment blocks are so warm that when they burst into arrest re they're all in shorts and t-shirts and little slippers um because it's just that hot in the apartments um I think that's all still ongoing they arrested them then they released them and now they've arrested them again I don't fully understand why so the one note campaigns um so one of the things that develops along with these fishing campaigns is how what the initial file is so usually they would use uh Microsoft uh Excel or word and they would would embed macros in them um earlier this year or late last year Microsoft started blocking macros
in office documents by default so this is Microsoft has blocked macros from running because the source of the file is untrusted it made it a lot more difficult to persuade people to click through to then run the macro that would then run the next stage of the attack chain so standing standard fishing payloads would no longer work one note documents though can embed other file types and I actually use one note a lot in my work to collaborate with people I did not know that it had its own file type until all of this keep off so essentially you can embed scripts you can embed other files completely in a one file which is what one not uses as
its file extension if you save stuff from the cloud version of one uh this demonstrates how CL emotet evolve as security does although emotet returned initially using old office docs so even after Microsoft um disabled macros by default emotet started after I think a three or four month break they stood up their previous campaign before this block took took effect so they just just fired up the same the same infrastructure before finally realizing it wasn't going to work and copying clb and switching to one note so this is from the beginning of the year this is your uh ISO files which was the previous um file attachment of choice and you can see that going down
and then the beginning of the year you can see gradually one note files and I'm sure this line would keep going if we look at it and that's from crowd strike I should point out so this cuts to kind of the heart of what I'm saying here which is if you've ever played mous trck you turn the dial here the mouse gets caught here everything else in between well maybe not in M Tru but in in fishing you can change you can change how you're you're doing each of these steps you know and then the end result is still going to be the same the next stage of infection stealing credentials loading rant somewhere whatever it is
that they're trying to do so when OT finally woke up and decided to use one node instead of their their filed macram campaign this was what they were what they were going for so your email arrives with one note attachment emails are in a reply chain so they compromise somebody and they're acting like they're replying to an email that you've sent so you're getting a re whatever from somebody that you probably know with a one note attachment um the malicious one note attachment loads an eded wsf file W script executes that eded wsf VB script file wsf file retrieves a zip archive the zip archive contains an inflated dll so this is another defensiv asion they inflate dll
files over 500 megabytes because a lot of Av and EDR can't really handle files that size properly so it's a way to to basically stop them being scanned properly and then the D is launched by reg spr 32. exe and so you would see this document is protected you have to double click View and actually that view button is loading that wsf file so they're actually forcing you we not forcing you they're conning you into actually running the program yourself and that's just a little bit of what's what's behind this whole VI thing here it's the wsf [Music] script so quackpot TCH chain iteration is somewhat similar so this was their initial OneNote campaign back in I think
it was March so email arrives it link to a OneNote document or an attachment the email can be thread hijacking or not so it might be just a random email or it might appear to be in a thread again uh the onee link only permits certain user agents so they were setting a user agent and if you want to try to to get that that second stage without having that that user agent you would get a 404 so once again it's a way to stop people checking or people investigating and all of these attempts at defens evation are a bit clumsy but taking together and iterating through them uh it does have an effect it does slow down people being
able to to investigate I didn't mention it before but emotes had actually had a way to stop people uh deliberately infecting virtual machines with emot then monitor traffic it would detect most virtual machines and then just basically stop working working or if you altered the emot head itself the um executable it had a a hash of itself that it would check and it would just disable everything after that so they themselves were trying to get around researchers in that way um so the malicious onee document loads HDA file HT file runs curled by DXE to retrieve a dll file that may be disguised as a gif or a text file um doesn't really matter rundl will will
install it anyway um HDA then sleeps these sleeps are used either is another wet method of Defense evasion so if if there's a long enough sleep maybe an EDR won't pick up the next stage or also it gives time for that DL file to be retrieved it then runs the DL run d32 payload is injected into a legitimate native Windows application and you've got a full compromise and from there creds can be stolen uh the next stage malware can be installed ransomware whatever they want to do essentially from their on in and similarly again you've got this do HDA file there and you're going to double click that to try and enable content in this this
one this is from BX underground BX underground made fun of uh essentially quackpot um constantly tweaking these things and they crazy sort of mouse trap like attack flow so you got to PDF downloads a zip runs a JavaScript runs a par shell installs a dll and um yeah once again people do make fun of of these groups but somehow all of this works and it works very well for them and these sort of really complicated attack chains I can never tell if it is all defense or if they're just throwing whatever they can into this to see if they can make it work yeah so this is my summation of cbots attack chain so you've got your
initial email you've got your next stage loader and in between hereby dragons uh it's essentially whatever they can think of to throw in there and this changes dayto day um frequently it'll stay the same with little tweaks but sometimes it'll be completely different methods of getting scripts to run things downloaded everything they they'll run through it and we're going to run through some there so max muttin I thank him at the end and crypto lamus both are an amazing way to keep up with emotet and Quack bot so they are constantly tweeting out research um and you can then use that you can then go to um sandboxes online sandboxes uh find the files that they're
referring to get the logs out of that um very very useful very very handy so this was one of the quack bot rund deal 32 uh tricks this year so if you were searching for run D 32 a path and a dll with a comma and then the the load Point within that dll um I didn't know this before but it doesn't need a comma you can just put a space in there it sounds silly but if your seam detection was Asis dll comma asterisk that comma is not there anymore that's broken that detection and that's just a little quick look so this works SSD DL and that's your your entry point there exact same
thing again space once again seems silly if you throw enough of these into something and change them out constantly you're getting around detections you're breaking them uh this is renamed LOL bins so your W script. exe has been renamed to Walkman wsman exe reg.exe has been renamed to land Loper so once again you are getting around people monitoring these LOL bins uh living off the land bins you are just renaming them you're moving them somewhere else entirely and you're using them for whatever purpose so in this case wscript.exe is loading oh this is another thing that they do they um name variables within scripts and also the scripts themselves with random um Dictionary names once you've
seen that you'll never forget that because entrance P or you know all of these are Zoop pathological not normal things that you would expect to see on a on a computer so they moved that W script somewhere else they've used x copy or whatever into a temp directory and they're using that so hopefully if you were looking for somebody using W script DXE for them you would miss this um similar with red DXE they are importing um I'm assuming this is like a registry entry here called Zoop pathological blizzards so that's that's your first uh defensive asent there is just these renamed executables Oh meant to highlight this the other thing they're doing is this and I think
I'll get onto it later on another slide this is padding of um their uh path so we'll get on to that as well uh this is cerutil so cerutil has been renamed to quitting. exe they're decoding what is labeled as an SQL file uh the output is a text file but actually that text file oh then they're out decoding that text file into output 2. text and actually that output 2. text is a DL that they're then loading so once again just an odd number of steps to get to this point where they're running their D and that's the next stage their infection I mentioned this before so multiple path escapes I hadn't seen this
before in Windows uh so I wanted to test if this actually worked and so I went to spun sure enough not only does it work but it does show up so things will work in Windows but they won't necessarily always appear in the logs so even if something works within Windows the way that it's logged may be different so that you need to check both that it's possible that it can be executed but also what it then looks like in the file so in this case those multiple path escapes are in there and especially in Splunk you have to escape backslashes so if they put in four backs slashes you have to put in eight back slashes to
escape each one um if you were looking for user administrator and you had that hardcoded in your detection you would not detect this it would need to be users asterisk SL SL asterisk administrator so this is just another way of breaking seam detections that can be you know a bit brittle if you don't realize that there's a lot of weird command lines stuff that you can do oh exclusions so you think okay um I've got in this case Defender and I like Defender so I'm not picking on Defender but you've got Defender running on the machine quack bot manages to get on there everything will be fine uh this is the power shell that was being run by
quack for a while so there's a lot going on here they're getting um the value of a registry key and then at the end they're deleting it but in the middle they're creating an exclusion for the entire seat drive or whatever drive it is so they're adding that exclusion to Defender so Defender will no longer scan that entire drive and this is a trick that a lot of um thout actors have started using in the last couple years just throw that into any any po shell there's a couple other ways I think you can do it with wmi just add an exclusion so Defender is still running technically speaking it's just now no longer running
on the entire drive that it's installed in um Windows command line redirection so in this case they're doing an echo at at the front uh the andand is it'll run the next command if this one was successful of course Echo is going to work they are creating a directory and and and using curl they're giving it a name in that directory they just created downloading the file from what's probably a compromised site here this label is an HTML file they put a ping in here a ping will then it's almost like a sleep it's another way of just hoping that an err or you know something else will time out it won't it won't actually keep monitoring these the
string of processes that's getting increasingly convoluted then it's going into this directory that it created up here and then W script is running that JavaScript that was originally labeled as HTML so once again if you look at this it looks off until you actually dissected and realize why but if you see something like this you immediately say something's going on here something weird uh Windows command line redirection we've kind of touched on already so this is reading um one. that and then it is essentially and two. and then it's outputting those into three. and then you got your andand so if all of this succeeded it's then running run DL 32 on that 3. D so it's basically I
think combined two files into one and that file is a d and then it's it's loading that so once again just another weird complicated way of doing something that might Dodge your r detections or might confuse in um so this is Windows command L redirection with double pipes and this is a bit of audience interaction here uh what happens when the above command line is run any ideas so I tested this out myself um so these double pipes are essentially it will try to run that command if it's unsuccessful it'll move to the next command so what you wind up with stand over here this is the command at the top it'll try to run each of these
randomly dictionary generated words each one not recog recogniz as an internal or external command it'll go down it'll go down until it finally reaches this CMD at the bottom and that's essentially like a batch file and all that do did was uh basically do um uh OS info so that was just me testing all of this and that's it down at the bottom so once again it's just a weird way of um putting as much padding in there as possible putting as much sort of rubbish in there to try and blind edrs or try to confuse detections I'm fascinated by this I'm sorry if everyone else isn't um so just been kind of wrapping up the
talk a little bit early um and this is the conclusion and this is what I want everyone to take away from this which is that fishing groups and IU groups in general will continue to take this approach to defense EV asion they will continue to iterate through little changes they can make they'll be reading um uh explanations of Windows uh living off the line commands that maybe we've never even looked at that people never have looked at uh they'll be trying different ways of of redirecting texts redirecting commands um this is the doesn't look great but this is throwing spaghetti at a at a wall it's the best picture I could find which is really
rude um and essentially I'm asking are your seam detection sturdy enough is your EDR and are you revising your detection so if you were detecting quack pot's behavior in November of last year with a seam detection have you been keeping up with what they were doing before they were shut down this year and I think that's that's the point that I'm I'm trying to make here and don't always rely on seam detections or EDR detections without checking in on them and making sure that what's being seen in the wild is mirrored in what trying to detect thank you I also want to give extra thanks to crypto lamus and Maxell as I mentioned earlier two Twitter
accounts that cryptool lamus is a group of people who study um fishing groups and what they're up to and uh it's a great way to keep up when there's small changes like that you can then use that as a way to Pivot and do more research I want to thank my wonderful team at adarma and the good people besides Cambridge for having me come to speak does anyone have any questions pleas see any change change or in Trends or initial access has been particular increase decrease um the last years or so just I'm interested because you we put all these controls in as blue teams for MFA number matching um you know to try and
get around um you know the MFA bonding whatever you want to call it yeah there's conditional access there's all this kind of Education where all that defend in dep but still there is that initial access broker getting to those compromise system in the first place to you know use that their C to or to hide their C2 so I just wonder what the trends were see y so I think the credential Steelers are becoming an industry unto themselves so you can rent them you can buy them there's entire I mean telegram channels of people doing support um where they say sorry you know this is broken this week I'll fix it tomorrow I'll give you a refund there's
tech support available and this is even for the Fairly cheap ones that are like $50 $100 um the more expensive ones I assume you could get even better tech support so I think if you have a lot of security controls in place and you monitor closely you'll be safe enough if it's a determined group like a scattered spider who compromised MGM the other week and they're able to get on the phone with your tech support or they're able to actually get through to somebody directly and talk them into helping them circumvent those controls you're in trouble but I think if you MFA monitoring for MFA um not MFA burnout but constantly that you were talking
about it there um the word escapes me um all of that stuff if you're monitoring for that you should be safe enough but if it is a determined attacker you're almost going out of initial access broker in in the way that we think of selling credentials you're going to initial access brokers who themselves are going to compromise systems deliberately so they're going out of their way to find a way in because they think there's money there or they think you know it's it's worth doing so that that's the big thing I think and I think scattered spider is interesting because I I think that they are native English speakers I I strongly suspect and other
people do as well they're in the UK and the US and I think this is a sort of synthesis between uh Eastern European crime groups like uh Ransom groups and people in the UK and America who may have the the linguistic skills or the understanding of Enterprise environments to be able to call up and con people convincingly without you know strange usage of language or relying on AI or anything else so I think that's something we may see more of and I think lapsis kind of kick that off scattered spider is like a more professionalized version of lapsis so um any more questions yes uh from your experience what do you think how long does it take for EDR vendor to
update their detection after a specific new technique being the wild I don't know so I work more on the seam side so I primarily do threat hunting I also do some threat Intel so um the ways that Ed's work is kind of opaque to me like I understand in a general sense but I don't know their life cycle for for new detections or anything like that you do work with customers right yeah but like no Insight on average I don't I don't work on the E side at all we have a separate team that works on the err site so I I it will depend on the vendor it will depend obviously on the techniques that they're able to
track the monitor but you know like Defender for example I think is the security Intel updates are I know certainly tends times a day so you also have to differentiate between ioc's so that's easy uh you can feed out your bad IP addresses your bad email addresses all that stuff versus behavioral stuff which I think maybe takes a bit more time or you want to be absolutely certain because if you screw that up then you're alerting on a lot of stuff that you shouldn't and we've seen that with I think def Fender especially there's been cascading false positives that have happened a few times because it's allerted on a specific behavior that maybe turn out to not be malicious
so um I don't know the exact time frames but I imagine I would say as quickly as they can but I se are always going to be faster because you know you just say that's a bad IP address send it out for for blocking any other questions I'll point out we've got an hour and 20 minutes you've got to come up questions or you're not leaving sound serious I I would recommend the security blue teams so if you want to have a look at labs and some of those things that's where I kind of started getting into knowing more about qu and um one of the labs actually is very identical to that with the HDA
files behind and then you have to you know figure out what's going on and it literally was just an image with six HDA files behind the image so no matter where you clicked they'll get you regardless I'm actually doing uh s 4508 right now for instant response and I found I was talking to someone about this earlier I found it very useful with thread hunting as well because obviously it's after an incident has been declared so it's different in that regard where start hunting is proactive in response is reactive but you're still what looks bad from an incident response detection or hunting um still bad before it's detected so uh certain things shouldn't run from certain folders certain
processes shouldn't be running other processes all of that it's actually been very useful to formalize in my head um things that I I knew didn't look right or you know instinctively but you know to have that actually spelled out you know this process should never be interacting with this one this should never be running from this trory is is for useful as well that's why I think it's um the tools are vital to have the soal because they may not necessarily understand all of that yeah and I think that's where things like Tax Service reduction Microsoft I par supporting some of that that's there yeah and also you just hope that they never get to the
point of getting on machines and I think maybe we don't do enough to make sure instead of just using ioc's for detections for feeding them into firewalls for feeding them into other platforms where they can just be blocked at a network level before they ever make it onto machine in the first place so uh any more questions you know whe in terms of the kind ofly kind um in regards to the evasion techniques um I'm assuming the security researchers are feeding that back to Micosoft work onious kind of other detections and we've seen a lot of um bring your own vulnerable driver uh being used I this backstab being used to disable edrs are quietly disable edrs there's a bunch of
different ways to disable edrs that are some are easier to detect than others there's ways that you can mess with um registry keys for instance there's the exclusion that I talked about there where it's still running but everything's excluded um you can use vulnerable drivers to then uh interact with and then kill processes quite quietly as well so yeah I would say that they're they're definitely aware of it um and it is a cat m game where there'll be a new way to bypass or disable an EDR and the company will then have to find their own way to to prevent
that so this is the last talk in here um I think the closing remarks are in here 5:00 um and presumably they're going to tell you how to get to the party which is probably what you're waiting for um thank you very much