Rose Songer - Designing the Path Forward: Security Awareness for the Indifferent Workforce
Show transcript [en]
hi all welcome to my virtual presentation on designing the path for security awareness for the indifferent workforce today we'll cover discussing security awareness overview designing the path board and then we'll wrap up but first a little about me hi i'm rose i am a governance risk compliance consultant with cso i've been at cso for about a year and a half now i have about 14 years in iet nine of those years are in security i have a bachelor's in advanced networking and a master's in cyber security and information assurance my industry experience goes from dod which i did serve about eight years in the navy to health care education and retail but outside of those professional things
i'm passionate about fitness reading i love cat memes my family dance and of course security awareness this year i am super excited and proud to be presenting at b-sides columbus i actually had my very first presentation at b-sides columbus last year and so it's really exciting for me to be back and be presenting another governance compliance type presentation and can't wait to see all the other presentations that will be at the virtual conference this year so let's jump into discussing security awareness to level set so security awareness is a way for us to provide our workforce with education surrounding cyber security we are trying to help them demonstrate good safe security hygiene practices this includes
trading for computer network physical security i also like to highlight that security awareness should also incorporate changing the culture culture we ultimately want to encourage these positive interactions and conversations with security and i.t as you guys may know security has a bad rep of being the no sayers um we can leverage this program though like security awareness to be able to encourage our workforce to feel uh comfortable coming to us and talking about things or asking questions about security or reporting issues ultimately we want them to be comfortable and confident when they come to us and know that we're going to provide them the information that they need and then we build that very collaborative nature with
our co-workers and our workforce more importantly though if an event happens relating to ir or incident response our workforce feels comfortable reporting to us so we can act a little bit quicker so normally with programs what i see is an initial or managed state of maturity so programs will be doing some things they'll be hitting you know the compliance or regulation items but they're not necessarily taking their program to the next level i think that we have a hard time getting our staff more engaged because we aren't making training relevant to them i like to think of security awareness from a marketing perspective we want our workforce to want to buy or invest in the skills that we're
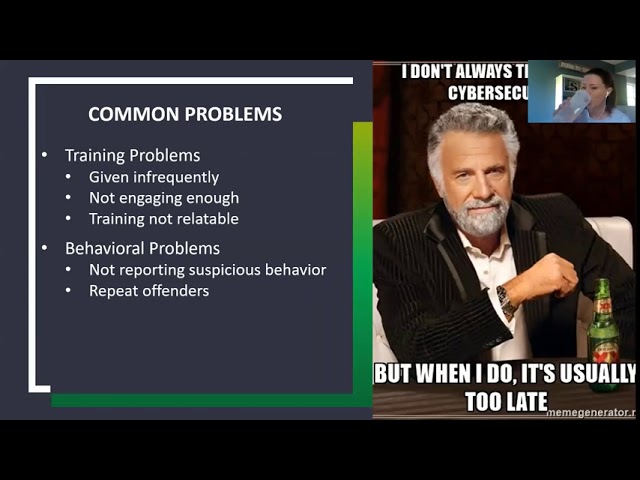
sending out to them if we're just sending out the skills and we have no reason for them to invest then they're just going to complete the training as required but not actually put those skills into practice which is what we ultimately want them to do if you guys are familiar with sans i would highly recommend reading into some of the materials they have they have a really great white paper on um designing your program more like marketing to get your workforce to buy those skills very interesting article that you could read for that so moving on let's first talk about the common problems that we typically see this list that you'll see on here is an
all-encompassing really it's just to give you an idea of the problems that you may see with your program i've broken the problems into two different areas and those are training problems and behavioral problems so out of the training we uh can see issues such as given infrequently not engaging enough and the training not being relatable so given training infrequently the workforce isn't going to be able to remember those skills or be able to put them into practice repeating the training over and over and over will get the idea to them um not making the training engaging enough again i mentioned this on the previous slide but with not being engaging enough they're not going to want to retain
any of the information and then with training not being relatable uh if you're giving them training that maybe not necessarily pertains to the job functions that they do they may have a harder time understanding it so these training problems will help you get an idea of maybe some root causes of why your program isn't functioning the way you want it to so we also have these behavioral issues so not reporting suspicious behavior and repeat offenders with this you're trying to encourage your workforce to put these skills into practice that you've taught them if you do not see them reporting suspicious behavior then that's an indication that they're not really understanding the training or they may not understand who to report
to which also is a problem so you want to have your users not repeating the same mistakes over and over and over again so again you want to get to the bottom of what these problems are and do a root cause analysis over your your whole security program before we move off this slide i would like to point out the meme that i threw in here i did throw a lot of memes into my presentation they always make me chuckle i don't always think about cyber security but when i do it's usually too late so as we all know our users um [Music] with all their best intentions when they try to do the right thing
they'll click on the phishing campaigns they'll provide their credentials a week later they realize something isn't right and then they finally think i should let security know and i know we've all experienced that before working in our field so before we move on to implementing security awareness let's talk about some metrics that have been reported recently so this report comes from fish labs which i've added as a reference at the end of this presentation if anybody was interested about reading these metrics in depth i highlighted a couple interesting metrics though so one of those is 98 percent of attacks in user inboxes contain no malware these attacks were attempting just to get credentials or have email scams so
i think the attackers or threat actors are more focused now more than ever on obtaining access via credentials uh this is a stepping stone to business email compromise which could set the company up with significant consequences i know i recently as part of my role as a consultant um have seen a lot of different business email compromise and things like that occurring where once they get access into the account they're setting up email forwarding rules or downloading the user's mailbox or whatever it may be and so there's a whole lot of information in there that could be potentially compromised so it's important that these users are getting good training on what not to do and when to
report it if something does happen uh another interesting metric uh within this is that the most effective lures were from finance hr um and e-commerce and i so i think people see that hr or finance related anything coming to them and they want to immediately act without thinking uh which unfortunately is what the threat actor is trying to get them to do our job in security though is to train our users in a way that they think first and then reacts later um reacting with letting security know or taking the appropriate steps not clicking on the email and providing their credentials or whatever information is being asked to them
now that we've talked about security awareness and what some of the problems are let's look at the path forward and how we design it so i've split this slide into two components and everything eventually funneling down into metrics so with overall development you have the compliance or regulatory and the big ones that you're going to want to consider for your program are things like hipaa pci nist iso and other factors like that moving on we need c-level support so in order to build your program to the effective effectiveness level that you need you need that c-level buy-in and once that is achieved you can build the governance documents that will drive the program um one aspect though that isn't considered
or isn't often thought of when in building security awareness is partnering with other departments so how can we work together as a team to mutually benefit everybody can you utilize skills from other teams for example can you partner with marketing to come up with targeted marketing material for your workforce or partnering with production teams to find out security related training that would be interesting to them such as vulnerabilities for the other side of program components we have training and social engineering this is going to be the actual training the staff sees and or completes so um just in my experience the most difficult aspect of implementing security awareness was getting the buy-in from the c-level
or the workforce i often got the impression that they feel security awareness was just another thing to do again we aren't making it relatable for them this is where thinking of security awareness as marketing is such an interesting and good concept we want the c level or the workforce to buy or invest in these skills that um will benefit them and the entire company and often people they forget that they're learning skills that are applicable to anything they do regardless if they're at work or not so we live in the technology age now uh and we should really be teaching our skill our cyber security skills to the workforce so they could go out and be able to do whatever they need to
on technology without compromising themselves or the company that they're working for so at the bottom of the slide you'll see that everything eventually funnels down into metrics ultimately with any program you want to have the output of your program funneling into some sort of metric some sort of dashboard those metrics are going to give you indications of how your program is working and if it's not working effectively the metrics are going to demonstrate that once you have those metrics you should be prompting your program into a continuous improvement cycle right so you could take those metrics you could figure out the root cause analysis and start figuring out where to improve this program and so now you have yourself in this
constant state of improving with your c-level buy-in and hitting your compliance or regulatory marks so now we're going to move on to the different types of training that staff can receive so this includes web in person correspondence behavioral role and group based each type of training has different methods of delivery that could be used and you know there's definitely a lot of different ways to conduct trading ultimately i think we just need to recognize that everyone learns differently so while web-based may be less impactful to the work day and easier are they really obtaining the skills we want them to so with these programs and with security awareness a combination of all of these things will be ideal
for your organization to get it to a maturity level that's acceptable so um you could do in-person classes every once in a while you could do correspondence newsletters are really easy to pull together and send out and then if you're using a platform such as uh no before you can use the web-based materials and all the games and items that they have in those particular platforms another item that you know isn't quite talked about enough within security awareness is the behavioral role in group based type trainings so this training is tailored to different groupings of people the group base would really be tailored or role and group base is tailored to those groups of people that
um are looking or perform performing certain job functions uh so you have like developers or administrators that may have you know elevated privileges and so now they're receiving more customized training that is a little bit above and beyond the normal parameters of security awareness training but it's providing to them more security skills relevant to the job role that they're performing which is essential for um a company to you know continue to be successful so uh we have frequency of training that is something also that needs to be discussed when you're developing a program um normally what we see is programs trying to get the check mark for compliance or regulation requirements so this is pci hipaa iso nest whatever
they're trying to just get those check marks okay we have to get this we have to do training because um hipaa requires annual training and that's all that they're doing which we want to get away from just doing the bare minimum we want to bring our program to the next level of maturity and we do that by doing more frequent trainings based on those different types of training that i just covered so another component of the training is being event driven so with event driven companies will have the training done at new hire and annual so um if you're just doing training at new hire and annual while you're meeting the intentions of what you may need to do from a
compliance factor your staff won't really retain the information if you're only doing it at new hire and annual especially at new hire your staff is coming into a new environment a new role they're being thrown a lot of different policies standards they have to read everything they have to get used to the environment and then on top of that we're giving them security awareness training which they may or may not retain and then you know a year later they're having to take the annual training again you know they're going through it really quickly and they may not gather all the information that they need so doing the training more frequently than that will help make it repetitive to a state
where they're actually going to remember what you're training them with every 90 days is would probably be more acceptable if you're trying to get your staff to a state where they can't remember the stuff that you're teaching them and putting it into practice with every 90 days though i'd highly recommend rotating any materials that you use so while we're trying to be repetitive we're not trying to beat them with the same newsletter you know every quarter we want to change the material up and if you're designing the material yourself do it in a way that's going to stand the test of time meaning that you can use it again and again and again so same
fishing concepts while the technology might vary from year to year on how threat actors are exploiting things the concepts that we're teaching to our workforce are generally going to stay the same so a security awareness month uh you know i definitely think that we could leverage this more to engage with the workforce it's a whole month dedicated to focusing on security um it's i think it's a great thing that we could use and i know my meme off to the side doesn't quite reflect it it's cyber security awareness month here's what you do open your email take a handful of best practices and throw them in there whatever people read that's the correct dosage um yeah i could i could get that
i could get the feeling behind it but cyber security awareness month is a great tool to use to start uh leveraging it for conversations so with security awareness month um many people don't know people outside of security may not know that's a thing and so october is your time to do this it's right before the holidays your users are going to be more inclined to shop online to give out the credit card numbers to be doing all this stuff on the internet and so you use october to tell them all the do's and don'ts that they shouldn't be doing in cyber security and with that you can promote this culture of change within your environment to
encourage them to have dialogue with you and to communicate and encourage these very positive interactions so you're promoting all things security and make it fun if you have if you have the capacity to do it absolutely do it if you don't have the capacity then obviously you'll just need to um work with what you have but if you do have the capacity highly recommend doing raffles games lunch and learn sessions having posters out and videos so i've been at companies before where we've done stuff like this and we have gotten such an amazing turnout people got really excited about it they wanted to win things they wanted to meet the people they wanted to eat the
food um we know food gets everybody there so make it fun your workforce will remember it and they'll they'll say oh man you remember last year we had that whole month we learned about cyber security things i was able to get cookies and chick-fil-a and um it was a lot of fun and they're going to remember things like that and they're going to remember that positive interaction that they had with security so next let's talk about social engineering if you remember at the beginning i talked about this as a component of security awareness so um this is a practical way of testing your workforce and all those skills that you've been teaching them so it's going to focus on doing a
fishing exercise to see if they remember what they should be doing and um this will give you a way to funnel into your metrics and really understand if they're actually remembering anything this testing should be done on a regular cadence so for phishing campaigns to really be effective you'll want to test and retest especially testing for the ones that failed done right you could get these metrics you funnel them into your overall security awareness and you could gain insight into how well the training is being received so uh protect you from social engineering and attacks sure just email me your password so again testing your staff and you do a phishing campaign and you get their credentials it's not a good
thing and it's going to highlight the things that they don't know and what you should be training on a little bit more so yeah if we could just stop clicking on phishing emails that would be great i am sure the security team would appreciate very much not having to respond to events and incidents over the weekend because of a fishing campaign
well talking about incident response incident response is something that i like to consider as part of the security awareness it's one component that i notice that may get overlooked incident response is a way in which your team can respond to an incident and minimize potential consequences to the organization so they will give them the capability to respond if an event or incident occurs organizations that aren't as mature may not be testing the responsiveness this could lead to issues when an event or incident situation occurs so the tabletop exercise is where you gather the key personnel and you walk them through a potential scenario the people that you would typically include would be the security team uh top
executives so anybody designated on the communication plan of an incident response plan once you do the tabletop you can use all the gathered responses the information that you took down during the tabletop and generate plans or run books which will help them respond if an event or incident occurs so incident response is a program on itself um incident response tabletops and training and stuff like that should absolutely be considered with security awareness you don't have to run the program or dictate you know the tabletop or anything but it's a component that should be considered and taken seriously to make sure that your organization is prepared for those events or incidents so we're going to wrap up this
presentation discussing metrics uh interesting quote here that we have is if you can't measure it you can't improve it and i absolutely think that any part of your program you really should be measuring it um with this you need to be able to understand the health of your program if you uh want to be able to get more money for your program or continue to mature you're absolutely going to need to be able to report on these metrics to the c level so that way they have a proof of proof on return on investment um because if they're not getting that return on investment value do they want to continue to improve on it so metrics that should be used to track
behavior can be for risky employee behavior employee incidents are incidents being reported reported phishing email percentage assessment of employee knowledge and employee completion of training so metrics this doesn't have to be your all-inclusive list it's just a couple items that you could take into consideration and these are going to be the more analytical side of the metrics metrics that you can't really get from you know the tooling that you may have in place or anything like that is positive interactions times that employees are reaching out to discuss whether or not security functions and certain processes are working employees reporting risk and stuff like that so um that starts to show that the culture of security
is being accepted at an organization and you can't quite capture that with the analytical side of metrics but it's definitely something that should be accounted for when you are thinking about your metrics so um i created a dashboard to go with the training or with this presentation rather and it's completely mock dashboard it's based on a completely hypothetical situation um the slide it's made up of metrics for 461 employees the dashboard it could highlight you know the annual training completion um again while we don't want to just solely focus on compliance we still need to make sure that we're tracking it it is still going to be an important component of your of your security
awareness the second metric here is to demonstrate how your phishing may be going so you'll see that i highlighted the user click the link training um if you test the workforce provide training and then retest you should see the amount of users clicking the link go down over time which is highlighted in this metric you'll see that it goes from 61 to 24. so you want to see that decrease in the users clicking the link and then the last metric that i provided was for physical security so while we highlighted the need for a lot of different security awareness habits i didn't want to forget to include that we want them to practice good physical security
situational awareness habits so this includes stuff like locking the computer making sure that they're using their badges appropriately um and you know just having general situational awareness of the things going on around them uh locking the workstation though is especially important when you think about environments that work with you know hipaa or highly regulated data so you want to make sure that your workforce is doing those things appropriately so we're going to wrap up the presentation now hopefully you guys have been getting a lot of insight into establishing a program that will be more effective for your workforce so here we have a checklist of things that you can do for your program first determine your compliance
requirements that is going to be one of the foundational pieces of the program that you're building so again while we don't want our program just to be a check box type activity we do want to be mindful that compliance or regulatory items are a huge factor of what we do you need to receive the c-level support so again anything that you want to do and build and mature you're ultimately going to need that c-level support so think of all the ways that you can start the dialogue with them to improve your program build partnerships with departments so we touched on this very briefly at the beginning of the presentation building partnerships with other departments highly encourage you to do this
build those collaborative relationships and encourage them to want to come to you guys to talk about things other departments may have people that have skill sets that you wouldn't have ever known about in fact one of my clients has someone who works in marketing that actually has cyber security background so they make up infographics all the time if you're not talking with these other departments you probably would have never known that and so i highly encourage you to start dialogues with these other teams next you'll want to develop if you haven't already done it you'll want to develop your program governance as we all know with most things in security you really should have the
governance to back the things that you want to do so the governance can include policy standard and procedure you want to have those things established so if you're trying to meet those compliance or regulatory requirements you're meeting them but also you're taking your program to the next maturity level with having that governance established also recommend making sure that the procedures are in place that way if the you are the single point of failure you are putting someone in a position to be able to continue to run that program after you have went to work on something else you're out of the office develop the training materials so i'm not saying that you have to buy
a tool such as no before or something like that you absolutely can develop your own training materials internally will it make your life easier having a cloud portal or something to be able to do training absolutely but if you have budgetary type constraints that will prevent you from um being able to leverage a platform like no before absolutely deliver develop the training materials internally furthermore you can customize those training materials to be more applicable to your environment so again you're making that training more relatable to your workforce in a way that they're actually going to want to invest in it next you'll want to conduct security awareness activities so don't just do once and done send out the
training material conduct the activities get out there and talk to your workforce um right now we're in a remote environment most of the workforce we're all working at home even this conference is virtually you can absolutely do training anytime invite your workforce to come to a webinar and just do like a quick 15 minute presentation on a certain skill you want them to have yes you'll have to you know develop the materials and you'll have to spend the time on the meeting and so it will take time out of your day but the return on investment will be much greater if you take the time to help them develop their security awareness skills and then finally you'll want to build or
report on the security awareness metrics so ultimately you want to be able to improve your program you're not going to be able to do it without having the metrics to back those improvement opportunities going even further if you're seeing certain metrics that indicate problems are occurring then you could take it a step further and do root cause analysis on why those problems are actually occurring and so now you're getting to the root of why your program isn't working the way that you need it to these metrics are also very enlightening to the c level so um you don't necessarily just need to report on you know the dashboard items that you should i showed earlier
you can customize it in any way that you think your c level is going to be appreciative of the story that you're telling to them so you could contact me at any of these platforms that i have listed i have twitter linkedin and you can reach me at my work email which is up here on the screen i love talking about security awareness so if you guys need a person to be a listening ear to hear if you're doing the right things um absolutely contact me i don't mind at all um so yeah hopefully today that you learned something that maybe you haven't been doing yet or haven't thought of in a way and you
can encourage your workforce to be more receptive of the training that you're trying to give them with that i guess i will see everybody at the conference bye
you





