Double Entry Accounting for Security
Show original YouTube description
Show transcript [en]
all right good morning everybody Welcome to bsides Las Vegas this is the uh track is it yeah ground truth tracks um today we have Shel U uh and he's going to be giving a presentation Double Entry accounting systems for security um just a quick couple quick announcements before we begin I would like to thank our sponsors our Diamond sponsor Adobe and some of our gold sponsors prism Cloud sem uh semrep and bluecat uh for cell phones if you guys could please put them in a silent mode uh for the duration of the uh presentation and at the end if you have any questions uh if we have time I will be walking around with a hand mic so
just raise your hand kindly and if we don't uh and we do run out of time uh you can just pull the speaker off to the side and ask questions there so uh without further Ado Mr you thanks very [Applause] much I'm gonna hold this can I hold this no all right maybe not I didn't realize uh pal Alo went by PR in M Cloud now that's their name anyway okay so thanks for coming um I'm s you and um I don't know if you had a chance to see the keynote but I did make a quick reference to this in the keynote it's all around how do we um start applying certain practices that we know in accounting
towards uh security right and so let me uh if you don't know what Double Entry accounting is I want to give a quick definition um it's a summarized version of what you can just find in Wikipedia okay uh so so for so some history back in 1458 um the medes I think or anyway some Italian guys uh figured out how to do double entry accounting before that it was single entry accounting makes sense right and the basic idea is you have these two ledgers uh so you have a cash Ledger and you have a let's say a different Ledger and they are supposed to balance out okay but it's two separate ledgers that help uh provide a
set certain set of benefits and so I'm let me read those benefits and you can see where it might apply so it offers an an accurate and reliable comprehensive view of our transactions it minimizes errors uh basically leading to more trustworthy reporting and facilitates easier compliance and auditing sound familiar sounds like something we we want in security I I hope so right so these fundamental principles that we look for in security well gee uh in accounting we have those uh we have something like that already in place so the question is where do we have the opportunity to see Double Entry accounting uh type of uh functions happening in security you just don't recognize it for what it is but once you
recognize it you're like ah this is it how do we how do we make more of those type of systems how do we uh ensure those systems can be uh reinforced and so on so forth so now now as I talk about this I have to set some foundational uh principles I have that's how I think I I think in principles because if if you don't if you disagree with what I'm saying in my conclusions of the principles uh then you can disagree well you could disagree with me on those but let's go I would rather go to First principles and say do you disagree with the first principles that's why I share Frameworks all the
time okay so uh one of the things that we oftentimes hear from many vendors is hey this is your single source of Truth okay and that's a myth I think we all recognize that to be a myth because the reality is that there isn't a single product that tells us the whole the whole truth right and I think we intuitively know that but let me dissect those words for a moment what do we mean by whole truth okay now you may have heard the word whole truth um before in a slightly separate context which is in sworn testimony right so the question is what is the truth the whole truth and nothing but the truth and can we actually handle
that right so what is the truth okay and then the whole truth and nothing but the truth well let's let's talk to those because those are you may Wonder like why do we repeat those three things in sworn testimony they must be different because otherwise it seems kind of redundant right okay so what's the truth well it's pretty easy right uh truth is just don't lie um don't alter anything in response to a question so an example inse security would be or just an it in general is hey tell me the encryption status of this um widget here and if I get answer back that says it's disabled if I ask a witness and the witness is
some tool and the wit the tool says hey it's off okay then I need some sort of cross-examination perhaps with a different system or something else that says no no it's actually it's actually turned on maybe I go to the actual system or something like that okay so this is an example of um where I'm not telling the truth and you know it's easy to verify just go and look for it and vo voila right then you have the whole truth so the truth the whole truth and the whole truth is about not omitting uh key information and this is this is actually a lot harder okay how do you know you're missing the whole truth so I can ask a
question hey um do I have any security groups that uh allow inbound access and I can have a rule that says Nope I have no security groups that so I may have an alert asking for the whole truth I'm expecting the whole truth and the alert is is to say hey do I see this another example beyond what you see here is um what you see with a lot of miter hack uh claims okay hey we see this TTP um well you see a very specific form of a TTP but do you see all aspects of the TTP and of course the answer is no right um and that's an example again of a place where you have missing whole
truth and so uh how you understand the actual truth here is really hard and I'm going to talk about this in Greater detail uh but the whole idea of the whole truth is well I asked about security groups and I and my answer was no I don't have any Azure security groups but well I might have some AWS ones right so I'm not getting the whole truth here and that's one of the problems that we have in our security tooling all right so I'm going to come back to that in a moment but uh the last form of sworn testimony or the last aspect of sworn testimony is nothing but the truth so uh I I was trying to think
of some good examples for this one and I I like making fun of the security vendor industry so the one I I figured was okay hey security vendor security vendor in particular and the answerers hey look at all the certifications that we have and all these awards that we won and somehow that's supposed to tell me that they're secure or that they're a great vendor um and upon cross-examination we realize they failed their ISO 27,1 and they just basically paid for those those Awards by the way I should mentioned not all those awards are truly play to play um but I didn't spend time to figure out which ones were which but the point is that um
nothing but the truth is an example of something like this all right so okay so you understand now what what is the truth the whole truth nothing but the truth um and when it comes to as I mentioned the truth it's easy to validate you have the truth or you can you can check against the truth and you know it's false you know it's not right you can also validate and cross-examine this but the problem with the whole truth is you don't really have a m means to understand the full scope of what is the whole truth okay and so this is a this is a hard problem um and I thought about this and I said huh could double
entry accounting help us understand the existence of the absence of whole truth okay the existence of the absence of whole truth all right it's a mangled phrase but bear with me um what I want to know is am I missing the whole truth I may not know what the whole truth is but I at least want to know that I'm missing the whole truth how would you know you're missing the whole truth truth you wouldn't know because you don't have a means by which you do that but Double Entry accounting allows us to do that we would say hey I have this one Ledger that says I just incremented something by $1,000 but this other Ledger there's a mismatch here I'm
missing something okay I don't know what that is but now I investigate all right so let's let's talk about that and see what that looks like so again cyber defense Matrix for those who don't know uh something I created when I was at Bank of America blah blah blah okay but uh the more interesting ECT of it is that I can split up the I can I I can look at this as a ledger as two types of ledgers okay one side of The Ledger is on the left of boom and it's what I call structural awareness tell me the state of the environment this is all before anything happens this is like your inventories
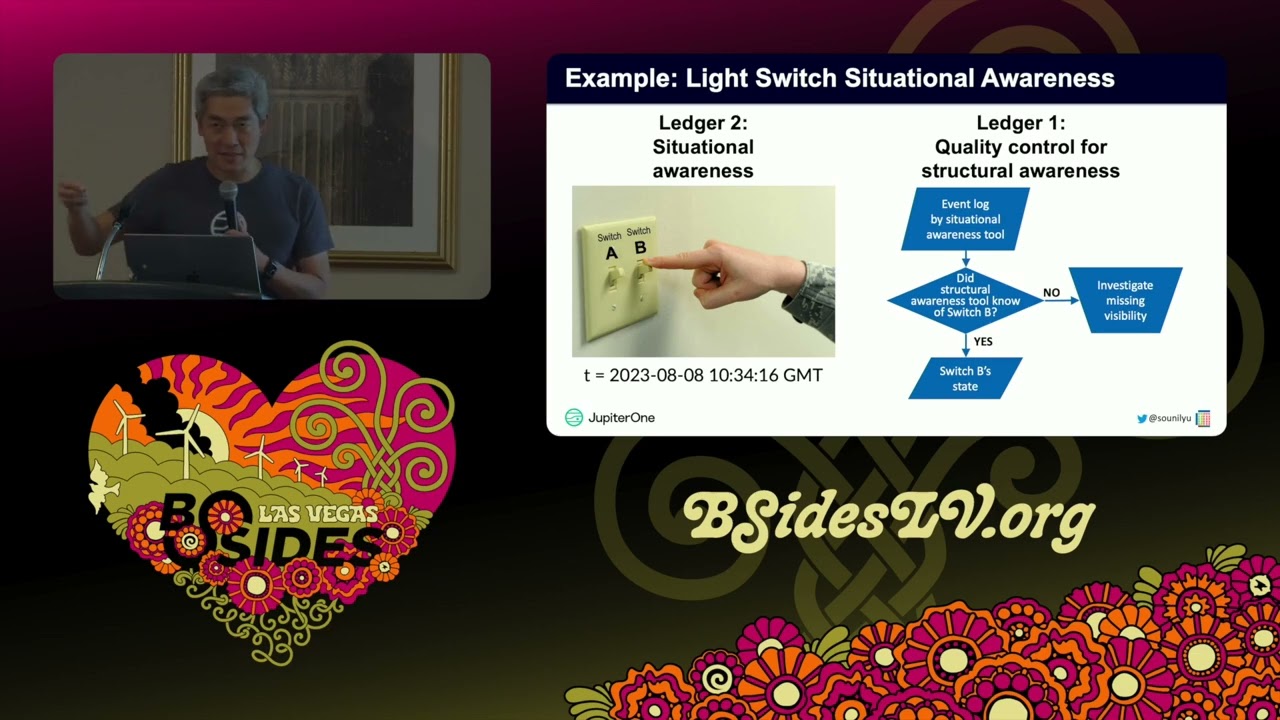
this is your uh cmdbs um if you have a vulnerability what listing that's where this is this is your tax surface this is everything on the state side of the equation this is the State Side Of The Ledger then you have the other side the right of Boom side and this is uh what we call situational awareness what I'm going to call situation wear in this this is after something bad has happened these are your events these are your logs uh all those sort of things um uh these are where your compromised systems live and so on so on and so you have Ledger one and you have Ledger two and they're two completely separate systems which is
what you want for a double entry accounting system you don't want them to be if if they were the same system then it's essentially a single entry accounting system but these are two separate types of systems and what's really kind of cool is that they provide quality control for each other okay so let me explain how that works so let's take I I'll explain as a ledger one system a structural awareness system this is again like a cmdb or something that gives you again what I call structural awareness your state of your environment so let's say you had some uh some widget some switch and at T1 it's on and at some point when you pull again
it's off okay so your maintaining State first you know that switch a exists and now you know the state of the switch and at some point between T1 and T2 someone something happened okay but in this polling cycle and so now the natural question is hey other Ledger do you did you see that activity okay did you log that because now if I did I'm like okay good I um I at least am collecting um I have a log that observes that activity however if the answer is no then I know I'm missing something okay now the answer may be there's many different reasons why the answer may be no but now you have a choice do want
want to spend time and effort to investigate uh this side of the Ledger that is missing the whole truth okay and the answer may be I don't care um and and by the way in accounting that's often times the answer too like you know what this is a um uh uh some um uh what's the what's the kind of fund that's like really small dollar amounts um P petty cash petty cash yeah it's petty cash fund okay and you know what do I do I need to have a precise accounting of every penny that's spent there it's there's a reason why it's called petty cash right um and so in that in that sort of sense I may not
choose to investigate because it's petty cash uh but other cases oh like that that's the equivalent of saying you know what I don't know what's happening in my guest Wi-Fi network but I don't really care okay but if it's in my DMZ I care a lot and so this whole notion of um knowing when you have a state change you can reconstruct events from State changes right not really well but nonetheless there's a mechanism for that and conversely on the other end so you have somebody switching um flipping a switch and you do the same thing you say basically okay I see that uh switch B is off or I did something to flip switch B
State system other Ledger did you do you have do you know about switch B is that even in your inventory and if the answer is no again it's what I'm calling visibility here I'm missing visibility that means I may choose to go get additional sensors to see that switchb uh but again I may also say I don't care all right but nonetheless I have a perspective of the existence of the whole truth I may not know that I still don't know the whole truth but I know that I'm missing the whole truth okay and here in you have this Ledger system which we already have these kind of tools in place but we haven't figured
out how to balance the ledgers together and so that's the idea the or at least not more than the idea that's that's actually what I'm doing and I'm starting to see vendors actually bring these two systems together um and it's actually pretty cool because now you're bringing two different systems but at the same time you don't want them you still want them to operate somewhat independently because that you need those sort of checks and controls um and ultimately the goal here is uh well so what I've seen with a lot of uh uh attempts here is those who try to take uh event-based systems and reconstruct state from there okay and if anyone's tried to do that
it's hard and it's painful and it's highly inefficient okay so any reconstruction of state to events and from event to States State um is going to be incomplete um and less efficient because you're your the way that it works is uh you have to like if I if I'm going to recreate events from State well one of the problems is if I don't have the right polling cycle I'm going to miss the event right so am I going to increase the polling cycle so it's every one second no it's just it's not going to be uh re it's not reasonable for you to do that so it will be incomplete you're not going to have every instance
of every state change but nonetheless with a sufficient number with with a decent polling cycle and over time you will see those State changes and you'll say Okay um I'm not missing the whole truth here again the goal here is not to have the whole truth all the time it's just to know when you're missing the whole truth and then likewise with events to State well if there if there's no State change then you never know about the the uh resource itself and so um again that's why it's going be incomplete but also uh any sort of event-based system uh struggles in maintaining state and so that's that's the other challenge that if you've ever
tried to do this it's hard um so my my advice to you is if you ever if you want to create this sub accounting system which allows you to basically know when you're missing the whole truth um use it for the purposes of that balancing equation but not for not to replace the other side okay now there there are a number of implications that come as a result of this um first is this perspective of what is uh so I mentioned the quick keynote some of these things that we're trying to do um may put additional burden on us actually okay because we're now moving into a space where um there are standardized practices that look like
accounting and if you're moving into that sort of space then there's an expectation that you're practicing um you know those generally accepted practices as well so now the question is like well you know what I I don't want to set a bar that's higher than what's in accounting think about accounting how long has been around yeah you saw the you know the uh the uh double entry accounting thing it was this was 1458 okay uh and of course accounting existed before then too um it's a very mature practice it it's people care about it a lot because it's all about money right and yet if you ask a CFO and ask them hey you know what how like how precise
is your accounting do you have any like how are how comfortable what level of variance are you comfortable with and they'll tell you oh you know it's okay as long as we do the boat within 1% we're good okay um 1% would be great in cyber security uh I think we're often time asked for like 0% okay like no mistakes no anything right like uh how realistic is that for us if Finance which is a much more mature uh um practice with many more tools and many more processes can even get to zero themselves so what sort of why are we sending a bar that's higher than them um for ourselves or for external regulators and then uh there now for
many organizations they actually still practice single entry accounting when they're small and they don't need to there's like a whole Cash recal System and there there's a bunch of things that I'm not in finance or accounting those who've ever studied it I'm sure you know what I'm talking about but there is a there's a point where you switch you say you know what we need to have more rigor here um and so I don't I'm not suggesting Double Entry accounting is a per is perfect for everyone in fact uh it's not Double Entry accounting and accounting is not perfect for every organization either so at the right time you switch and you say okay you know we
need more rigor here um there's an expectation of more riger when is that for cyber security as well because we can do this we can actually do double entry accounting but it's going to take a little effort well partly because sometimes you don't even have a cmdb you don't have a SIM you don't have something that captures that you don't have the other side of the Ledger um but once you do now you have the ability to now do this double entry accounting okay and then I I just leave it with this question of do we want to have something like sarb Oxley for security because it comes with uh penalties if you don't do
it right U but as I mentioned earlier um we're already getting P penalized uh with lawsuits and SEC fines and in some cases criminal prosecution because we don't have these practices well understood all right um now this is just one example of accounting an accounting principle you you saw me talk you may have heard me talk about impairment and other sort of practices there's other uh systems that we've seen that may seem like double entry accounting but actually end up being more single entry accounting those are uh just where it goes back to the truth question in other words you say hey someone some something is saying um we are compliant in this way here and I just need to verify that
that compliance is happening that's not Double Entry accounting that's just a tell me the truth I'm confirming and doing cross uh cross-examination of the truth um pretty straightforward but I think the whole truth again is a really hard problem because you don't know if you ever know the whole truth but Double Entry accounting helps us do that so okay with that questions go ahead I
like thank you I love applying other business Concepts to security that makes perfect sense right because because we're not doing anything new so taking legal Concepts hold truth and how you respond and is that fully the correct answer or intentionally vague right um and using double entry accounting the other thing however that other business practices use and maybe this is an addition to your first principle's list in this concept is the notion of forecasting so in finance we use forecasts as another check this is what we were expecting to occur in this period and then we have accur you know um the actual numbers coming at the end of the month and we look at the
difference between forecast to budget which is actually even further so we we planned in January so now we have forecast to budget forecast to actuals and we can carry that forward month over month as the year progress is now very different of course than insecurity but perhaps as a first principle the qu I guess my question is are you introducing the concept of applying other methods or are you suggesting this one specifically oh I I'm uh so in um another slide which I didn't bring here I actually introduced a whole bunch of other financial principles like uh I mentioned impairment perfect sense uh I actually specifically left out return on investment agreed uh because I agreed
that that's the forecasting piece but I I I had it in I took it out because I'm like uh I but returnal investment is not just a forecast there's so many other parts of the forecast the for T is um license entitlements we expected that our company would grow by 500 employees this year so when we renegotiated our Microsoft E5 we did it to 300 new entitlements knowing that we would pay the bigger fee for the final when they do the true up right so forecast also of what we expect to see occur and when we see anomalous Behavior once a month we should look at these are the things we expected seasonality oh this makes sense
because it was August those things don't occur yeah these more of them um um so we could take the rest offline but uh not all the I would love to have every PR as many principles apply but there were some I still struggled with to figure out what the right pattern match is um but I found enough patterns that like ah there's something really here that we can that we can latch on to okay uh and we had a question here yeah one more yeah going back to your your thoughts on uh due diligence and rigor MH um in cyber most of the time we think about um uh materiality as a purely Financial construct or
reputational only if it has a reasonable impact on that same financial situation have you given any thought to whether there's an alternate way of thinking about materiality in this context using these principles um great great really great question for which uh we as a community are struggling to find the answer um is familiar with this but I asked I specifically asked this question to a whole bunch of cesos and uh beyond the you know whatever uh F CFO says in terms of Monet like materiality 20% Revenue whatever whatever okay I'm like yeah I I get that uh let's let's take that one off the table how else would you define materiality and it was we we don't have
a good answer we don't have an answer at all we absolutely need to have an answer how would you apply this materiality did you apply this materiality I don't have an answer either but but but the problem I well the answer to some degree is this notion of variance okay uh is the variance material enough that it's that the public needs to know about it and and this notion of variance uh we of course the the on the finance side it's numbers money right but I also mentioned this notion of variance in this context like how how variant is my is ledger one from Ledger two Tom okay uh you want to just yell anyway we're out of
time after this yeah right after that's take 10 minutes all right have any questions if you want to pull the speaker aside but we do have another presentation after this so thank you for coming out thanks kman appreciate it