Startups: SOC 2 ... Now or Later?
Show transcript [en]
please join me to welcoming our next speaker Elise liberti who will be speaking to us about startup so to now or later
Ellis hello hello how is everybody also I can't wait to see some of you guys after cuz there's a lot of people here for the most boring topic ever but anywh who I'll make sure I don't go over I already broke something okay all right so startups sock 2 now or sock two later um a little bit about myself I'm a senior software engineer I've been the head of R&D I've been team lead I started as a front-end engineer um but one thing is that I've always been an engineer but always in the cyber security space so always building sass always Niche to B2B cyber security products navigating the sock 2 landscape for startups first you have to understand
sock 2 requirements familiarize yourself with the sock 2 framework Focus focusing on the five trust service criteria security availability processing Integrity confidentiality and privacy and determine which are relevant to your services and make sure you Scope the work appropriately Define the scope your sock to assessment based on your services you offer and the data you handle limiting scope can reduce complex complexity and cost and that's usually one of the biggest things that people don't want to do it because it's going to cost money and it's going to take time Implement robust security measures prioritize establishments of strong security practices that meet their criteria as forms for the basis of framework get your engineers and your
devops and everybody doing something from the beginning so that once you implement this it's not this big shift in work document those policies and procedures make sure that they document what they're working on so then when you get here it's not this m scramble to make sure that everything you have is documented use technology and automation this is one of the biggest things when it comes to saving money and saving time because even though these tools cost more in comparison to your R&D team and devops and security you you'll be saving a lot of money on their salaries leverage those tech technology Solutions and automation streamlines in compliance processes such as continuous monitoring and Automation and logging prepare for
audits engage with a qualified auditor early in the process conduct Readiness assessments or or Gap analysis to identify areas needing Improvement before the formal audit again use technology and Automation and you won't have to do so much of this manually educate your team ensure that all employees understand sock to requirements and their individual responsibilities regarding compliance you can do this by simply having that process started early they know this is how we do it and this is why we do it continuous Improvement treat sock 2 compliance is an ongoing process regularly review and update controls policies and procedures to adapt to new threats and changes in business this also has skip that forget it budget
accordingly allocate sufficient budget and this isn't just for cost this is also for time and team like how many people are used taking their time allocate that sufficient budget for sock 2 compliance processes including tools training and the audit self compliance can be resource intensive but is critical for business growth and customer trust the five trust service criteria for sock 2 compliance are security availability process Integrity confidentiality and privacy for the sake of this talk as we're kind I'm going to stay on the topic of more startups and how your Tech team is um affected we're going to talk about the top three which are the most common ones that um people get security confidentiality and
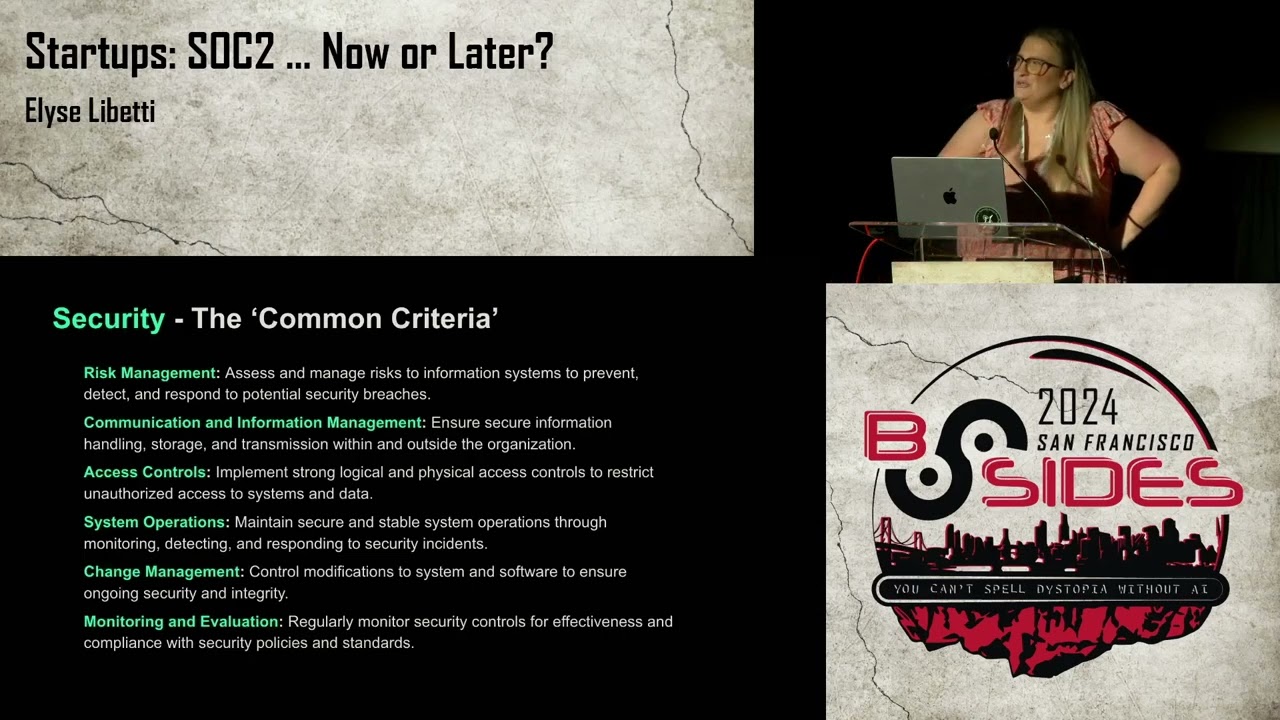
availability security also known the common criteria if you're getting socked to the Bare Bones is security you need to have risk management assess and manage risk to Information Systems to prevent detect and respond to potential security breaches communication and information management ensure that secure information handling storage and transmission without the outside with does not go outside of the organization access controls Implement strong logical and physical access controls to restrict unauthorized access to systems data so basically everybody should have the bare bounds nobody should have access unless it is required for their job to have that access otherwise they don't need it reduce risk system operations maintain secure and State a system operations through monitoring detecting and
responding to security incidents this could be as simple as a slack alert a channel that has Incident Management you can use the AWS incident manager the pingdom for if your system goes down there's so many little facets you can use something like data dog Etc um simple things like that um go a long way with soak to compliance change management control modifications to systems and software to ensure ongoing security and integrity this one you goes back to that make sure that you have a process if you don't get one um code me uh code reviews code quality how do how does something get merged into beta or production or staging and QA do you do
code reviews does it require one or two people have this document and stick to it um because as you're getting audited yearly cuz sock 2 isn't a one-time thing um unless you're doing type one then it is it's a frozen in time um then you need to have those processes in place to make sure that you're continuing to be compliant monitoring and evaluation regularly monitor security controls for Effectiveness and compliance with security policies and standards again there's checklist tools new AI tools that you can do this with without having this be someone's job availability Network performance monitoring monitor Network performance and availability to ensure the system operates as intended and is accessible when needed again that goes back to
leveraging a third party tool like data dog or uh Sumo or pingdom and all the others system availability again Implement control to ensure systems are available for operation use as committed or agreed meeting performance criteria Disaster Recovery this is a huge one there's so many even large companies that don't have a process around this what do you do oh well everything is secure no one's getting in it's not going to happen but what if they do cuz they do like what are you going to do how are like how long is it going to take you what's your SLA around how long it's going to take you to get back online if someone hijacks your um
SCM backup and and data recovery this goes with the security incident handling Implement backup processes and data recovery procedures to maintain data integrity and availability in case of adverse event a lot specifically around data bases a lot of the um Cloud providers it's a simple terraform attribute set it and forget it make that your policy this needs to be implemented every day every two days every 30 minutes whatever it is take that snapshot you never know what's going to happen no matter how secure you believe there's always a way capacity management regularly evaluate and manage system capacity to handle current and anticipated loads while maintaining system availability and the third is confidentiality information classification this one specifically is
probably one of the biggest when it comes to B2 be like another business wanting to use your tool like why should they do business with you proving that what their data is is stays within them and stays within our organization is huge information classification classify information to indicate which data is confidential and establish handling requirements based on its classific access restrictions again Implement controls if you don't need it for your job you shouldn't be there encryption use encryption Technologies to protect confidential information during storage and transmission this could be encryption at rest or in transit wherever it needs obviously sometimes like a pure front-end application is not going to be encrypted but if and where
needed make sure and have that be your policy and those Auto tools will flag you on it when you're not establish policies and procedures for retaining confidential information as long as it's needed and securely disposing of it when there's no longer required this one specifically kind of goes back to that document your processes come up with what you're going to do and put it down on paper when I feel like one of the biggest things that issues that me as an engineer and my peers have is actually documenting something like I I you find yourself explaining the same thing 15 times to someone or multiple people instead of just writing it once in a Wiki and
leaving it be agreements and contracts utilize confidential agreements and clauses and contracts to ensure that third parties adhere to the organization's confidential requirements this kind of goes like back to like do we do sock 2 now or later well we're requiring other people to do something or ISO something of the sort audit and monitoring regularly audit access and use of confidential information to detect and respond to breaches ensuring continuous protection of sensitive data building trust in the start startup ecosystem by doing sock 2 earli you're going to demonstrate the commitment to security achieving the com sock 2 compliance for security shows startups commitment to maintaining high standards in protecting both their systems and your data ensure system reliability by
meeting the availability criteria startups can demonstrate their systems are reliable and consistently operational which is crucial for customer satisfaction and trust and especially in my field of always making SAS for cyber this is the biggest if if they're depending on me to help them make sure that they stay compliant I have to be available and consistent protect confidential information compliance with confidential confidentiality criteria ensures customers that their sensitive information is properly safeguarded enhancing trust in the startup's ability to handle confidential data they're getting trust by their customers and they're handing it to us so they need to make sure that what their word is to their customer is what our word is to them transparency is in process openly
communicate about the measures taken to achieve even maintain sock 2 compliance it can build trust with stakeholders showing transparency and security and operational practices third party verification utilizing an independent auditor for your S 2 compliance adds an extra layer of credibility it wasn't someone in my organization this was a certified auditor CPA um that did this and they have nothing to do with our tool they went in they poked they proded and we are compliant strengthen client relationships sock to compliance helps in establishing those strong relationships with clients who value security and confidentiality you're going to see this a lot more in medium to large Enterprise level businesses and when you're starting a startup and
you're preed and you want to catch that whale so you can get series a series B and go far get acquired rest invest do all the things if taking that first step to have have those compliances early on is really important um my previous role I was in healthcare cyber security um and we didn't have sock 2 ISO none of it um and it was hard to find customers I worked there for six years and year two or three we had a huge Hospital organization um make us jump through so many Hoops just to do a POC they wanted us to fill out every single person to do a questionnaire and I mean this wasn't
like a questionnaire this was a biography of the Bible it was huge and you would have gotten that trust and there wouldn't been so much mistrust to make these things people fill out these forms and have these visits and have this certain type of equipment if you were already certified and then when we did go to certify it took took over a year to to even get to where we could have an auditor look at it it was an absolute Nightmare and then 3 months later we got defunded um where in this case like where I work now we got type two within three months and I started them a founding engineer we had nothing and
recently we got type two and it took maybe 30 days tops and that wasn't people working full-time it's just here and there 30 days that's it by starting those processes early gives you a competitive Advantage especially against your competitors when going after those whales and those medium organizations that compliance can differentiate themselves from competitors appealing to Discerning customers who prioritize data security and system availability especially if your product is around security reduce risk and improve management compliance helps in identifying and M mitigating risk early which improves overall management and operational resilience attract Investments investors are more likely to fund startups that have proven compliance and recognized standards like SAT 2 and even ISO Etc as
it suggests maturity and Readiness for growth instead of this hit the ground running just Scrappy duct tape and popsicle sticks do what you can and once we get more money we'll deal with it you're not going to get more money long-term trust and loyalty loyalty consistently maintaining sock 2 compliance Fosters long-term trust and loyalty with customers vendors and partners securing the startup's reputation in the ecosystem summary of above the balance finding The Sweet Spot how do I as an early company that has small a small team not a lot of funding how do I still get sock to compliance to get those customers but still make a product you leverage tooling you automate maintenance you
create processes and budget Engineers time with leveraging tooling we use Integrated Security tools Implement tools that integrate seamlessly with existing systems to Monitor and enforce security controls with minimal manual intervention a lot of these products today have a Helm chart that you can just pop in and boom you're set up so C sock 2 specific Solutions choose software Solutions designed specifically for sock 2 compliance to streamline compliance efforts such as automated compliance checklists and dashboard monitoring cloud-based Security Services employ cloud services that offer built-in compliance features like I was saying about the database that is a simple attribute in tari form and cloud formation etc for Dynamo DB every 30 minutes it'll take a snapshot reducing
the need for internal tool development and maintenance here's an example of a checklist tool I I strips The Branding but if I'm sure a lot of people know exactly who this is you put in your policies you give them I am access someone messes something up Bing action item or you you've got a existing system and you want to get Su to compliance certification Bing these are the things that need to get worked on and as always insecurity leveled by risk automate maintenance continuous monitoring systems deploy systems that automatically monitor compliance status in real time alerting teams to potential non-compliance issues before they become problematic automate reporting use tools that generate compliance reports automatically saving time and assuring
accuracy regular updates and patches set up systems to automatically handle updates and patches for software reducing manual workload and maintaining security most sems have some kind of action or plug-in that does this for you GitHub has dependabot and every day it'll ping you and say you need to update this minor version and it'll give you a PR to do it so when we got our sock 2 compliance the first time in type one um the question the auditor asked was what tool did you use and the tool that we used was Al our tool and they said well is it sock to compliant and my CEO said it will be when we're done here like we got
to this is what we're doing um and it's simple it's just like the checklist you put in your policy at your organizational level or Etc and instead of you getting those red flags and going through the checklist it will submit PRS for you which makes that annual cycle much more simple automate those policies early with a tool that will make it so that there isn't that burden on Engineers devops uh developers together really right to bridge that Gap and have something that keeps you in track so to speak um that tool We've ran through with um some very uh well-known purposefully vulnerable products and just a few of the like just running it through with a few policies
like there wasn't client authentication no dedicated tency no data versioning no encryption at rest and immediately told us what resources Etc that were violating that policy and then submitted that PR create processes standardize procedures develop clear standardized procedures for tasks related to softu compliance this ensures consistency and reduces the learning curve for new team members document practices Implement robust documentation practices early that are easy to follow and maintain it's like 21 days to break a bad habit if you start on the if you start from the beginning doing the good thing there is no 21 day but wait M making compliance checks and audits smoother and less timec consuming have an incident response plan have a
predefined incident response plan that is easy to execute reducing the burden during stressful security events and that comes to having as a service level agreements around how long does it take for you to respond to an incident having an on call schedule what does that look like is it 24 hours a day is it during business hours is it only on the weekdays um Etc budget Engineers time this is one of the biggest reasons why people don't do this early we want to hit the ground running we need to make a product we need to get customers we got to do it we got to do we got to do it we don't have time for
anything else but if you budget properly again and start early with the beginning of your system you're not taking as much time PRI prioritize compliance tasks clearly Define and prioritize these tasks in uring Engineers spend time on high impact activities scheduled compliance time allocate specific time where people work on this versus regular work training and support provide training and resources to Engineers on sock to compliance instead of just telling them to do it give them the why they'll be much more interested to enhance efficiency and Effectiveness reducing time spent on troubles shooting compliance issues and the most important is Outsource where possible you're not going to be able to out Out Source certain very Niche things but finding an
expert in in a certain realm of what you need to complete for certification takes the load off of one of your employees and doesn't take as long because they know what they're doing and they'll do it right strategic timing now or later you're going to build trust with future and current customers if you do it now elevate your reputation easing the procurement process and with large Enterprises enhanced incident response management this one's huge this doesn't just speak to making money and keeping people happy and getting customers this speaks to using your time wisely like if everyone's scrambling around and going through cloudwatch logs and trying to find what it says and I can't figure out
where the exception was thrown they're wasting time and honestly the tools don't cost as much as the time of your employees and lastly reducing friction in sales processes none of that crazy questionnaires and getting all these tools and implementing all these new processes because you've done it already Lessons Learned sock 2 isn't just a checklist it's much more it's a business growth strategy operational effectiveness and security compliance identify which TSC your company will benefit most from bare bottom is security and usually those top three are the ones we discuss security availability and confidentiality three and the most important if you ask me automate continuous compliance is key this again sock to compliance isn't a oneandone
thing the world is Ever Changing every year you have to get the certification again if you want to rep it and if you're not doing anything in between you're not budgeting your time number four now or later now the sooner the better thank you does anybody have any [Applause] questions yes we do have one question for you that was posted on slido cool thoughts on if sock to is security theater flu screenshot what's the absolute minimum a company can do to get sck to certified certified okay so the absolute minimum would be that simple security only not availability and not confidentiality and even simpler is type one I'm going to go back to security um
type one is Frozen in a moment in time on March 3rd this is what my system look like this is what you hand the auditor anything after March 3rd is not suck to compliant nor certified it could be compliant but it's not certified type one says in a moment of time I was doing the right thing and then security is the only right thing that you have to do um then you have type two which is a little bit more um work and engaging and again requires time and money to um continuously keep that up does anybody else have questions yes there's another one okay security and sck to or distractions at most startups Outsourcing is great but
startups move fast and take risks do you have a favorite vendor maybe y security okay um I don't can I say anything about that because I know I'm supposed to be like very vendor neutral on these things um yes I do I shared screenshots of the two that um I've used and one that I built um uh but it doesn't have to be a time sync especially when like you said you're moving fast like we hardly had a project and got type like a product we had bare buns prototype and got type one and continued that implementation and it was I'm telling you not maybe the engineer like the R&D team probably spent maybe 20 to 40 hours
total amongst everybody not congruently um documenting and doing a few things there really wasn't much it was mostly like red tape that um our product manager dealt with so if you start early and Implement it'll be a lot less of a Time sync and the tools obviously if you've already started how do you con colleagues that process can improve effectiveness of if done right um the best way to convince somebody is by doing um documentation for example you could tell people all day please document this and they'll continuously just communicate via face to face or slack or an email but never in a Wiki um do things by example you'll see a lot more change if you hit the ground
running especially when you're at a startup you can land grab there are so many gaps in responsibilities at a startup that you can see a whole and for example this and be the one that starts implementing processes implementing Incident Management and take ownership of it that's the best part about being at a startup we can only take one last question that's okay with you how much responsibility should cloud providers share for S to where defaults it seems like undifferentiated heavy lifting heav software company out to you see that well um so not necessarily are they you can't so some of these defaults cost money and when you are cutting Corners you're not going to want to do um a
snapshot every 30 minutes um they do have those though and if you use a tool like the the few I showed and there's many more um and declare that like I want encryption at rest on this this and this um I want Dynamo DB to be on demand capacity um client I roles Etc um then when you miss a step and if it's not a default then it the tool will catch it instead of you having to go and like for example in terraform go to Hashi Corps site go to your cloud provider find the resource which there's then 15 that all pertain to the same resource and they're all subsect of it and find the one and then
read through the attributes that gives you this like hardly any information so then you go to for example AWS and there's hardly anything there and you got to Google and connect the dots Leverage toing thank you please join me to say thank you is thank you





