Legendary Defender: The Voltron Analogy
Show original YouTube description
Show transcript [en]
well thanks good afternoon everyone who everyone is doing well enjoying the conference so far my name is Brian Carey and welcome to the legendary defender so I first saw Voltron defender of the universe back in probably 1984 in 1985 and I was fascinated from the start about the story of these five heroes who alone are very strong right they pilot these mechanical lines if you're not familiar with the show but when the situation becomes difficult enough or dire enough where they can't defend alone they are ready to form Voltron and harness the powers of the combined group now in fairness I was probably more interested in the toys in the show at the time but it reinforced this concept
of strength in numbers or more importantly strength when working together as a team that stuck with me all these years so as I grew older I also came to love different analogies as making points so I thought what better way then to make an analogy for security teams with a beloved TV show so I'll start with some context which will illuminate the problem as I see it I'll then introduce the eros corporation followed by an introduction of our heroes in the story I'll explain how these heroes can be strong when working independently of one another and also how they can be weak when working independently of one another and then I'll then explain how our heroes are far
stronger when working together then we'll meet the legendary defender our main hero and we'll finish with a summary and if we have a chance to make you a at the end if we have a minute or two to spare so just a little bit about myself for some context so I've had the opportunity to work in IT and security for over 20 years I've held a myriad of roles from entry-level analysts to sysadmin security analysts various management roles as an IT sector to an interim security officer for a manufacturing company so I've experienced a lot right I've had successes I've had failures in my current job I have the opportunity to meet with dozens of clients a year
and discuss their security programs I helped identify process people and technology gaps and help recommend solutions I meet with companies big and small and in many different industries and despite all these differences I see a lot of the same problems over and over again and a lot of it comes down to organizational dysfunction so allow me to elaborate a little bit so I call this organizational problem right so let's face it organizations around the world are under attack daily from sometimes very complex attacks or probably far more often attacks that aren't super sophisticated most organizations have technology in place whether it's firewalls Network segmentation ids/ips anti virus malware protections encryption vulnerability management the list goes on and on right more often
than not technology is probably not the problem usually when I meet a client for the first time I might have a few people in the room you know usually someone from senior management maybe a mid-level manager an analyst or two and as soon as I start asking questions one of two things inevitably happens right maybe the analyst starts explaining how their technology is deployed how their processes work and I can see the expression from the senior manager like he or she is hearing this for the first time along with me right you could see that fits right I didn't know how this is the technology was working or how it was deployed or maybe the senior manager
explains how the technology is deployed and how the processes work and the analysts are biting their tongues and shaking their heads like really this is how he or she thinks this is working this always translates into the analysts not trusting that their senior manager understands what's going on or maybe worse doesn't care to find out the disconnect is born right you might hear my CIO isn't a technical person he or she wouldn't understand or my CI only cares about budgets nothing else right they keep trimming the department and they expect us to keep everything protected right this can lead into siloed responsibilities what I call the fiefdom right an analyst might understand how a V is deployed but doesn't really bother
to understand how the technology is just one piece of a larger puzzle they make decisions that make their job easier without consideration of how it affects other members of their team either up or down stream but I can't tell you how often I've seen a company with different AV solutions at different corporate sites or multiple versions of asset management tools patching tools VM scanners etc this is the definition of teams not working together the opposite of a true SEC ops model right it's no wonder these organizations struggle to defend I've also seen many organizations have a really great vulnerability scanner in house someone from security runs daily weekly monthly scans and has all these great reports about
vulnerabilities that exist but they aren't the ones that have to remediate it all right I get the question all the time hey we're identifying everything why do I see the same vulnerabilities pop up every single month because nobody's taken the time to understand the needs of the remediation teams what else is on their plates are they even being given the data in a consumable format how often will your business allow systems to be rebooted for patches to apply all right there are a lot of factors to consider and these are factors a lot of organizations don't take the time to figure out and this is what I mean by suck-ups versus i.t i.t sack right now every organization is
different and I don't want to pretend that there's a one-size-fits-all solution but more often than not organizations that take the time to understand the challenges they face are in a far better position to defend we need to empower a security culture within our teams one other example we see a lot an organization might have a great incident response plan right they've taken time to document the key personnel and their responsibilities in the event of an incident the problem is is they never inform those team members of what their responsibilities are and they never practice it right so when the time comes to initiate a plan nobody knows what to do and oh boy how do we
love to blame our users right now I understand that often they can be link but IT departments have to get out of the habit of viewing users as enemies I'll address this later when we meet our heroes and I know this is not the security awareness talk per se but we have to start thinking of our users as frontline defenders right how often I see organizations where users just don't want to raise potential security issues to their service desk or to IT security IT or security directly because of how they're treated right if I see a weird pop up on my workstation or my workstations acting strange I'll just ignore it rather than rather than be
made to feel stupid by IT so let's introduce the era's corporation so for the sake of this talk it doesn't really matter what they do the point is is that they're under attack from the darkonian mafia right those are Conan's are doing all sorts of bad things to them and the era's team has five defenders who were responsible for thwarting the attacks and securing the organization so let's meet our five defenders first we have RC so or maybe just some other senior manager now yes it's true they are an important part of the defense structure the CSO is the guardian spirit of IT sex strategy bad CISOs and I use that term somewhat loosely don't listen to their
teams and don't understand the challenges that they face see so sometimes come into an organization and try to implement a solution that worked at their last job right there is no one-size-fits-all solution you think back to that conference room where the senior manager or analyst was talking if they misunderstand how the technology is deployed or how the process works do you think they'll be adequately able to address the needs of the security team in the business right they're very likely to misrepresent security maturity maturity upwards and because they're unlikely able to translate business needs into actionable strategy lower-level analysts don't have any direction outside of keep the lights on so when is our C so ready to form Voltron right
they should understand how to align security strategy to the goals of the business the CSO needs to be able to communicate these goals to the entire security team hey just because you maybe as an analyst think an organization needs email based DLP solution doesn't mean that that aligns to a business goal or need and therefore you might not get the dollars the Cecil has to understand the risk posture of the organization and make decisions based on this there shouldn't be an adversarial relationship between senior management and team members alignment with the CSO is critical for the overall effectiveness of a security program now if you are the SI so make sure you have regular conversations with
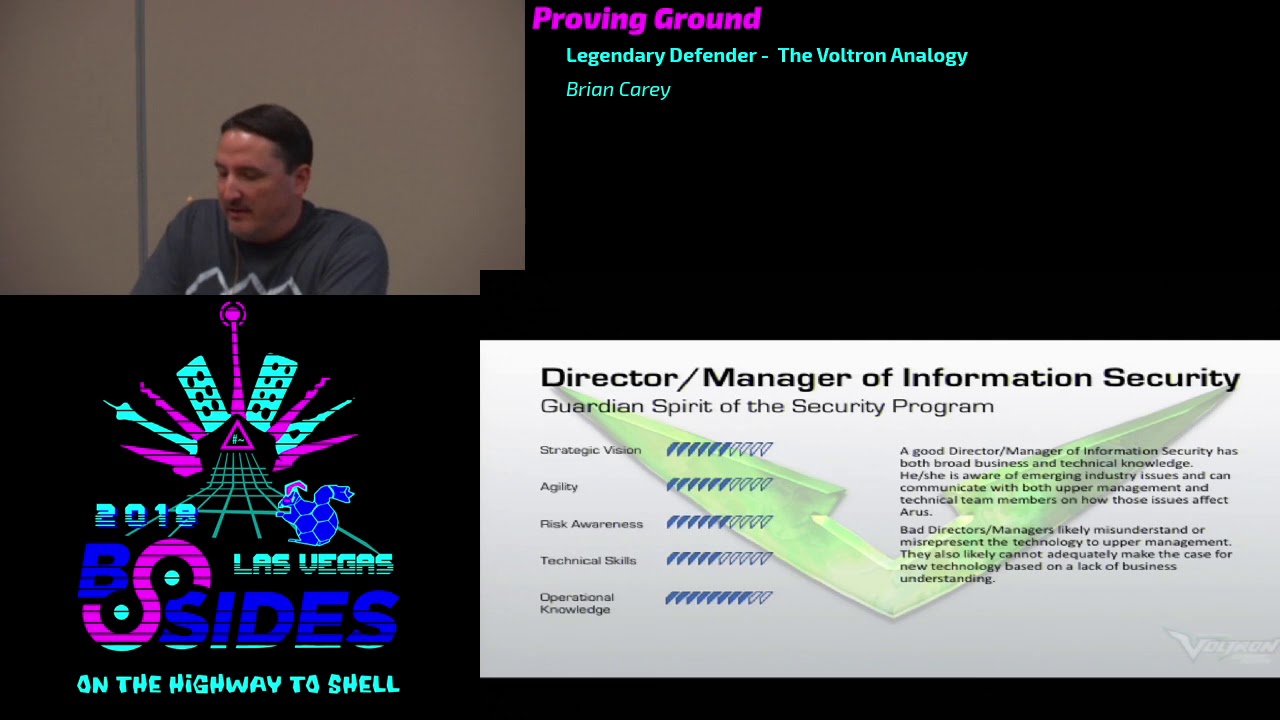
your team if you're the team don't be afraid to communicate successes and challenges to the C so now next we have a director or manager level so yep you'll notice our first two heroes are senior management alright if you've been working in the trenches for a while that shiver you feel up your spine is normal it's not abnormal to feel like management is working against you this is likely to happen if your director or manager is unable to bridge the gap between technology in the business you may find yourself in a position similar to a previous job that I held right where we had some rotation among director levels right one day I suddenly reported to a director who previously
served in compliance and while she had great managerial skills she had absolutely no technical knowledge whatsoever our department was now relying on someone with no technical skill to be able to communicate sort of from the field challenges to the C so now in a case like that she was able to exhibit some of the good qualities I list right she asked the right questions to learn about the technology we had deployed and she was able to map that to a business reskin goal a good manager is going to advocate for their team so when is a director or manager ready to form Voltron those managers have to help their CISOs bridge the gap between technology and business they need a good
understanding of each a good manager should know the issues that face their team is the team having trouble identifying classifying assets did the latest pen test identify previously unknown vulnerabilities how do these things translate into risks the business can understand how do I help get the resources and tools my team needs to do its job if my team has a roadblock how do I get it removed now we come to the folks whose hands are actually on the keyboards right the folks who are responsible for implementing the technology from monitoring the technology and alerting other team members and management when something is wrong now use the term analyst very broadly here but if you are
responsible for something like a B deployment and management the sim or logging web filtering email protection vulnerability management pen testing right you fall into this category so let me tell you where I see the problems with this hero most often if you're lucky enough to work on a team where you can separate these functions out just don't wear blinders when I go in to assess an organization now you might have an analyst too understands the VM platform or again who understands how anti-malware technology is deployed and these folks become hyper focused and can't see how the one piece of technology that they are responsible for fits into the larger security program worse yet you might have analysts who
disagree on what the best AV product for their platform is for example I've seen plenty of examples where the end-user workstation team might deploy one AV product and the server team deploys a different solution or again let me highlight the issue of vulnerability management if you have two or three patching platforms in production how can you reasonably expect to consistently provide actionable data in these cases now if you have a team that communicates well and your director or manager understands why different AV platforms are deployed and this has been signed off and approved great but if these decisions are being made in a siloed fashion it can spell absolute disaster this is especially common for
organizations that have multiple geographically dispersed locations so when our analysts ready to form Voltron now some folks may not want to hear this but it is important to heed the direction of your manager or the C so they need to provide the animal with projects and priorities if you as an analyst disagree by all means inform and have the data to back up your claim as to why you need a process defined or a technology deployed but don't go at it alone understand the technology you're responsible for and how it fits into the broader security strategy and if you don't know what the security strategy is by all means ask but just be prepared to explain the
technology you use and be prepared to react if an incident occurs so I went back and forth a little bit on who would be my fourth hero but I want to introduce a hero that I call the business process owner now this may or may not be a title or role that you have at your location but what it's meant to represent is business management and technical roles so these are the people who set the strategy for how the company will make money right they are often the ones who choose the application platforms or technology that IT and security must support the reason I bring this group of folks up is because those of us in IT don't often think of them as
strategically important but far too often my experience has been that this group in particular often operates without any guardrails they choose applications or technology to support their business dreams without ever consulting IT or security and we are often left scrambling to try to piece together a security strategy to deal with some technology that the business is suddenly sprung on us this is where duplicated technology often originates the best example I can give was a previous manufacturing role that I held every site suddenly decided they wanted security cameras installed in a six month period I had requests to build security into twelve different camera platforms different physical Hardware different vendors again nobody thought to think hey do we have a solution for
this already in the organization something else that we can leverage so when our business process owner is ready to form Voltron when we put in or when we in security enable them to be agile while setting boundaries put together a security requirements document that allows for that agility to occur while still adhering to security principles if you're a business process owner all I can say is just please please please consult with IT and security first before you do anything oh yes our end-users how we love to joke about them now again this is not a security awareness talk but but I think you know think for a moment that you were someone in HR or finance or maybe manufacturing
you have a job to do that yes probably relies on technology but you are not a technology person if we treat these people as nuisances or take the attitude of our users are dumb do you think they'll engage with us and let us know if they suspect a possible security incident we again we need to treat our users as frontline defenders and equal when it comes to the overall protection of our organization if a user does something that causes work for you use it as an opportunity to educate again when I assess an organization I'm very curious to see what tools users are empowered with to report suspicious activity do users know how to even reach
you do you have a service that's that calls route through maybe a ticketing system if a company tells me they have a thousand users and the service desk or security gets like five calls a month right that sets alarm bells off on my head right away right I can guarantee you it's not because the security program is mature so when are our users ready to form Voltron now I know we probably don't have a lot of end users here today but this can only happen when we an IT empower them and they are willing to speak up and get involved we used to have a saying in a previous job which was Security's everybody's responsibility right did you get a
phishing email tell somebody did you open an attachment that has you nervous especially tell somebody write IT and security can only help if they know something is wrong so there are some common themes here when our heroes don't work together and don't fully understand their role as defenders in the organization right there is no unified security strategy you might have policies and technology in place but efforts are often duplicated and everything is being done on a reactive basis let's fix the problem we encountered in January with this technology oh now we're seeing a different different issue in February let's fix it with this technology right there is no true risk analysis in these instances this is how dollars get wasted
and this is very often how dollars are not available when you truly need them to mitigate a risk within your organization sea levels and boards are disengaged one of the questions I always ask early on when I meet a new client is is information security a topic of that your board talks about or that your executive team discusses regularly our security concerns recognized at all if the answer is no it's clear there's going to be dysfunction in that organization right you have siloed IT or worse shadow IT right every location or team makes decisions that work for them and IT is left to try and support a mess of competing technologies and God forbid a security incident occurs right in this
type of an environment would eros be able to react would eros even know that an incident occurred right probably not because nobody would know what their role is so what happens when our heroes do work together right there is unified security strategy it is well communicated and everyone from the board to your executive team to the IT teams to security to your end users and the business understand what their roles are policies are written to align to business goals and proper technology is deployed based on risk estimates that have been performed your board and sea levels are engaged and information security is a regular topic at their meetings and perhaps there are even some KPIs that are reported to them
so what does this all mean it means when we all work together our heroes are ready to form Voltron the legendary defender so we've had a chance while meeting our heroes to discover what makes them ready to form Voltron we're now talking about the legendary defender but this is really just an incarnation of all of our heroes working together right we are aligned as a team so let's talk about what this means in the real worlds from a programmatic standpoint right so the assets of your organization are understood you know what you have to defend and you know who owns those assets you know where they are physically and you understand their criticality right you're maybe running a
robust owner ability management program scanning all your network segments with regularity you can prioritize remediation not only on the criticality of the vulnerability but also on the criticality of the asset itself right you've got a scanner integrated with a ticketing system so that incidents and changes can be tracked and sent to the right people the first time and you've got proper endpoint protections you've got AV no local admin access web filtering etc you've got robust incident management you have a plan that everyone understands and everyone understands their roles and you practice it you have a good security awareness program and keep your teams up to date with relevant training but most importantly the lines of communication among the team stay
open no matter which lion you are in this scenario just be open to feedback
so the main point in here is you are not alone none of us are alone in this it is extremely rare that I see the legendary defender at any organization if you think you're the only organization or person that struggles with any of this I can promise you you're not right don't feel like you as someone NIT or security has to plug every hole in the dam immediately right your business should be guiding you people often get confused as to who is supposed to accept risk right the odds are may not be you probably isn't you right you may be responsible for identifying and explaining the risk you know but it's usually maybe a business leader senior management that
has to take in all of that data and make a decision and here's the thing you may disagree with the decision that gets made and this is okay it really is senior managers get paid to make decisions like this so let them make the decision but don't be afraid to advocate for yourself if you see a risk or you see a problem you need to speak up like don't meet the challenge head-on alone and please remember your colleagues are not your enemies at least they shouldn't be if you are identifying with some of these bad lion traits that I've been mentioning take this opportunity to effect change within your organization and just respect one another and respect
differing opinions right the challenges that we all face are hard enough when we work together let alone when we have to face the enemy on two fronts so with that I just want to say a really quick thank you to Patrick who's got the green mohawk here as my mentor Thank You Patrick so I think we came in like a minute short so I don't know if there are any questions any questions raise your hand I'll bring the mic over
a great presentation I want to talk a little bit or ask you rather about the end users as you said we love to blame them but what do you think we can do to maybe help modify to some extent modify their behavior but also modify our behavior to somehow mitigate some of that kind of click now think later mentality that they frequently have is there something that you maybe identified I don't know maybe push all the security updates at a certain time so they know if something comes in you know late at night on Friday or whatever that it's most likely not a legitimate you know security update or something like that yeah so I mean I think there's
two things you bring up there right there there's there's definitely security awareness piece so there there has to be education within the organization generally a lot of companies you skip it over or the extent of their engagement with the users is maybe we do at phishing tests twice a year there needs to be far more regular engagement far more regular training sessions if you will with the the end user population to get them to understand and better educate and then I think it's how we engage with them right I think part of it part of the issue is again generally more than not when there's an issue it's put more work on us now they've done something that
that's going to cost us you know maybe hours of work to remediate and we have to approach it as if we take that adversarial relationship with them at that point they're just very likely to not engage with us again so we need to be as supportive and and again just use it as an any opportunity to educate as much as you can and just try to put a positive spin on it if you will I mean if they if they do something and they do call you start immediately with hey thank you for telling me about this right it's it's that's the first step but that's the most important piece you know so first - thank you okay and
that's that's the positive tone already with them and then you can work on you know maybe some of the other remediation things that you need to work on the one but but to me training is the key follow up grab this guy first okay thanks for the talk so other questions though we face challenging challenges because we outsource more and more so we hire a virtual CEO we have managed security service providers we Business Process Outsourcing do you still think that this can work out or is there at some point like lost battleground or something so are you saying so is the is the outsourcing of security a good idea yes I mean it's some of the heroes are outsourced to me
I mean not much changes in my in my mind I mean I think what ends up happening is organizations outsource security and then they think that they don't have to think about it anymore somebody else is is handling this and as the business regardless of who's responsible for security whether it's an internal person or somebody a third-party provider you as a business or you as an IT leader within our need to maintain engagement but yes I think it can work as it's a model we're seeing a lot a lot more of a lot more managed service providers a lot of third-party providers a lot of external Sox things like that but yes I think it can absolutely work
assuming the business stays engaged with them if they if they outsource it and say I'm not thinking about this anymore you're doomed to the same problems that you probably had previously all right big hand [Applause]