Yara For Hunting Malwares
Show transcript [en]
um and let's introduce our next speaker um I'd like to introduce uh laka dub and uh he's speaking on Yara for hunting malwares so laka let's see uh here we go you are connected
uh it's kind of hard to hear you um not sure where your microphone is but did I share my screen now no no we can't we can't hear you uh are you you can hear me now oh that yeah there you go that's much better okay so should I share my screen yes okay
okay is it visible now perfect yes we can hear you we can see you and we see your screen okay so should I start my session yep go ahead okay okay so welcome to my talk on Hunting malware using Yara so good morning afternoon and evening depending on where are you from and firstly I would like actually like to want to thank you all for taking time to attend this talk so in this computer era uh one of the most difficult thing to do is to look for adversaries in our environment so basically this Advanced adversaries like malware uh have good uh and Innovative persistence techniques and have the ability to stay under the radar so in this session we will talk
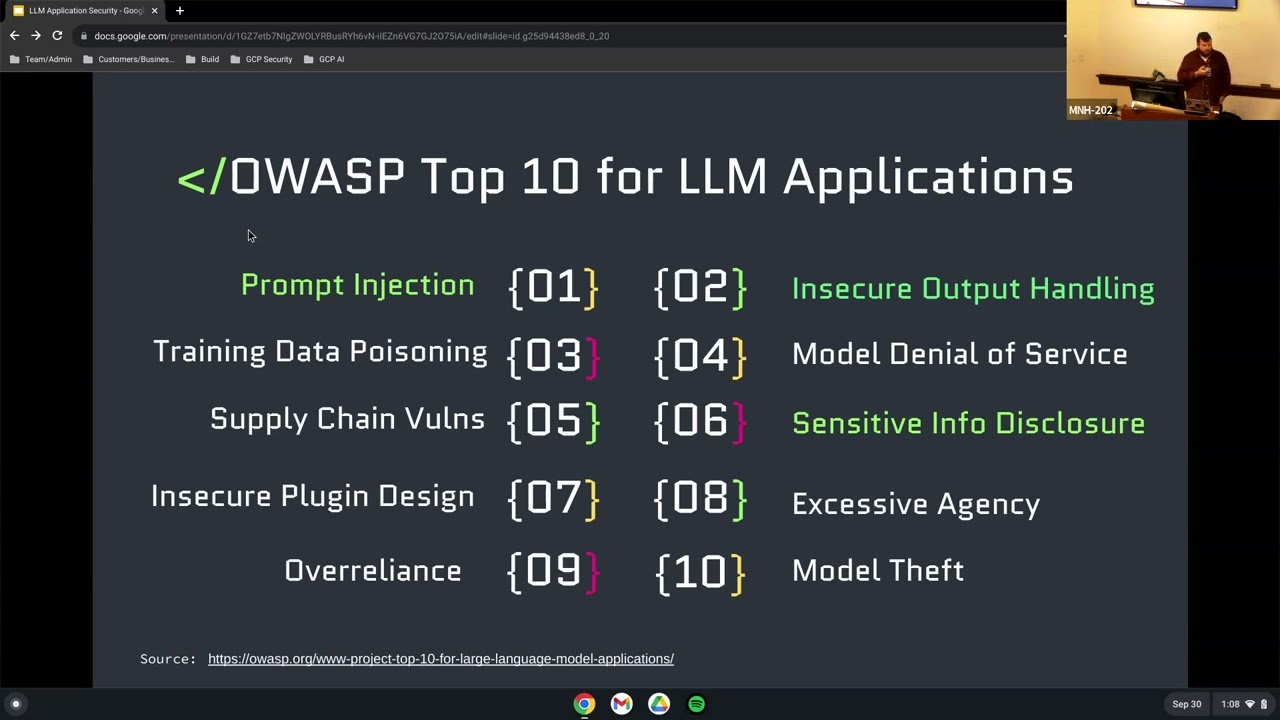
about uh how can we identify this Advan adversaries like malware using Yara so little bit about me I am an undergrad student have a deep interest in malware analysis memory forensic and threat Intel and I am also active chapter Le uh for OAS Bal OAS chapter in India okay so let's see about uh what are we going to talk about today so we will start with the what Yara is and what are its uses and all then we will move towards creating our our own Yara rules and we will also look towards an art of building some resilient tool and we will then then move forward towards a demonstration and work with some live malware samples and then we will also
look over a tool which can help us in creating our Yara rules automatically and then we will conclude with some final thoughts okay so little introduction about Yara it's a pattern matching Tool uh basically mostly used by malware researchers and in used in malware detection it's a tool based approach for creating descriptions so basically descriptions consist of strings and all we will which we will be looking forward and Yara can also be used in classifying malware on the basis of malware friendly so it's a most most common tools for malware researchers to classify malwares and detect them and most important one it's a free and open source tool so it's developed uh and used uh by virus total
uh so it's a best in the field for detecting and classifying MERS so let's look over purpose of Yara so as discussed before it's a important uh tool in classifying malwares on the basis of malware families and VAR and other than this Yara can also be used in tracking Mala camps on the basis of strings and C2 servers domain IPS and all and not only limited to this Yara can also be used to create your own antivirus a antivirus based on signature and other than this Sara is mostly used in the field of memor forensic and incident response to so why so before y it was very difficult for the researchers to detect and classif y large volumes of Mal samples
and basically as we can as we will see over here in demonstration uh that uh Yara can effectively be used in around thousands or terabytes of Mal samples and it can effectively uh generate positive results which are in the form of detecting Mal and other than this it's a compl completely text or hexad decimal based rules so it's it is very easy for a developer to quickly adopt on Yara to create their own tooles and they are so easy to use like uh you can easily pass this rule in your sock or IDs so it's just a very easy way to detect this malicious activity in environment so let's see our how can we create our
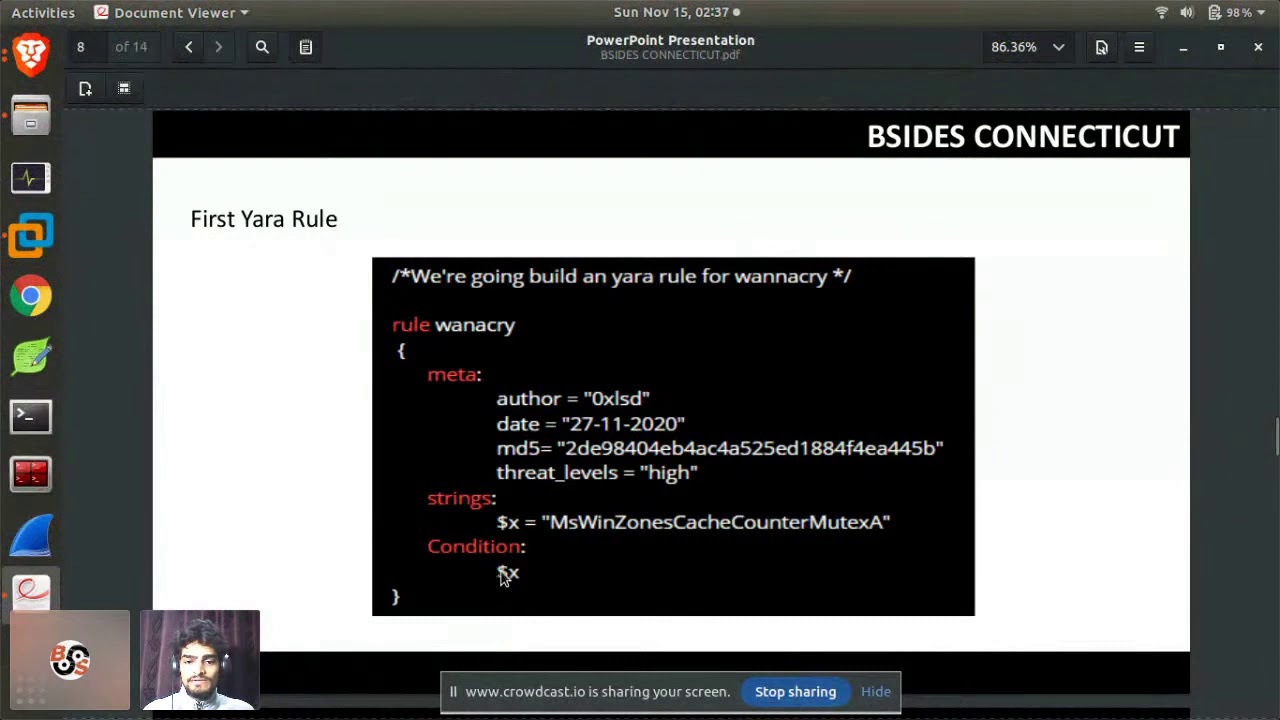
Yara rules or what all we need to create this kind of rules so basically Yara rules required URLs IP addresses file LS and hashes emails and other strings which are very unique in a binary and this strings can be easily found using utilities and different tools present in uh environment like testing utilities which we will be seeing in few minutes and other than this there are many common malware which uses unique entry points and addresses or API calls so we can also use them in our Yara rules so let's look over first Yara R so basically Yara rule compris of three common sections one is meta the other is string and the condition and Rule starts
with a name of a rule like over here I have named it like a The Meta section is the section where we place our arbitary data and the data arbitary data like the name of an author or a date on which it was created a unique identification value like md5 Su or hash value so that other researchers can easily identify that for which Mal sample the rule was was created and the next one is strings so basically this SE this is the section where we will be placing our strings uh for example this Ms vson cash counter mutex so it's a string pres it's a mutex for a vry Mal so we have uh this is if
uh when we run this rule so if a rule manages to find this string or this string present in a binary uh that which is running in our desktop or laptop so the rule will trigger so uh the trigger mechanism works on in the condition section so basically if we going brief so if our condition uh dollar X is valid the rule will trigger so it's just simple so the art of building and resilient room so this is the most important part of building and Yara Ru so the uh the building mechanism starts with the analysis process so in this we we get a B malicious binary and we will analyze it to uh in the process of analyzing we
have to Target to uh find few strings which are very unique so here we jumps to our next section in the identifying phas so here over here we will try to identify strings which we will be using in creating our Yara rules and again we jump to our next and we will using this strings which we have identified previously we will create our rule so after creating we have to test so basically testing uh uh the best way to test our rule is to create database a big database of malware samples with some uh positive binaries or non- malicious binaries like uh I have created over here okay so example so the folder comprises of
around 260 binaries and randomly few are malw you are ransomwares you are drens and all uh and and few over there are not milici so that we can test our rules like uh which generates less false positive and which are more resilient okay so after that after testing all these rules so we can deploy them in the IDS or sock or any other operating mechanism which the firm is using and then the last but the best one is to monitor our rule for any further updates so let's we have to look for the strings or the data which we will be using in for creating our Yara rule so basically tools like a strings are very
efficient for extracting data from a binary and the utilities present for both the common environment which are Linux and windows and to create based rules we prefer a disassembler uh most common one is AA okay so let's move towards our de demo and we will now work with some live Mar something so
okay so over here we have six binaries and using them we will create our
okay so let's open a
file okay so basically what uh does this name is we have to name a file and the extension should be Yara
and okay so we start with Rule and name of a rule you can name it anything I have just name it here and again so Yara is basically much closer to a C programming so we will see few things related to C in this in our y rules like the Rules start with the parenthesis and end with parenthesis similar to a c program okay so next we have to place our meta section over here we will place our metad data or arbitary metadata okay so anything which we can add over here we can like name of an author you can name anything
okay and the
date so you can place more few things which you required like M or any high value or anything else we will it only do over here next is strings so this is the part the important part okay let me open it
another okay so let's start with some
strings okay so this is how we have to look for various strings in the binary so over here this is found our first string okay so this is there is no legitimate D named as launcher. D in the windows so there are high chances that this is uh malicious or uh EV one so okay so we will use it in our okay so basically each string spacement rule consist of a name so like over here I have named it as X1 because we will like few more things so 1 2 three order all the strs have to be enclosed in double parenthesis sorry not parth double inverted comma okay so let's look for
more okay so you have to go in very detail form while looking for res you have to search in a pile of since just over Okay so this there's an exe Nam exe but I it seems like it's a legate so can ignore it
we can also ignore this days months because there are how many chances that they can be used in the legitimate processes so basically the main thing is we have to ignore the common ons and we have to look for the uni
strings okay they are Comm so we will ignore them and look for few
more e
okay you find the directory path over here again we can use it Ru and as c as I told is much similar to C and she often uses Escape sequences so again y also use the same so we our Escape
sequences look
for Str
we can find a URL so
okay so this has need this so yeah we can use them too so basically y doesn't have any hard and fast to the amount of strings which have to be L you can add and number of strs like the amount you can find in in a
binary like so yeah this is a name of a mutex so we can use it there is AED binary also so yeah we can use it too so let's copy it
okay six are enough so let's move to
condition okay so basically conditions and Yara can be defined in various ways like one this is the easiest one so if the condition this condition names if the rule will trigger if any of the one condition or more than one condition is uh sorry not condition the string is present in the running process of a computer so let's save it and look for few
more like this one but we can we will be looking for some IP addresses now so yes we can we can find find it or not
I guess there is nothing much left so we will look for different
encodings encoding means over here we can see like the binaries have various encoding so yeah we can use this they using the Linux utility have a plus point so we can use like seven or all so we can get some more unique strings so let's do some let's startet from 16 and yeah way we can find an I so let's add it another
SK sequences and let's save it and test it so the rule starts with 10 OFA and then name of a rule and the location which we want to SC
something okay so basically y have a good quality of defining in which line the error is so let's look at in
okay the strs
this
just a second I will stop uh my share screen share and I guess there is some issue with my
installation e
uh can you see my
screen can I get a confirmation for our scen
okay so the issue was we have missed paresis so let's check it now and see it works fine okay so the issue was I guess we have missed the parentes okay so work so basically the rule starts with the initials of Yara then the name of a rule and the location which we have which we want to scan so the six binaries are now confirmed that they contain this all strings present over here in our team so the rule works fine now okay so let's look go into
to look a completely different scenario of of the rule okay so let's start so in this in this scenario we will be looking on that a single binary is not enough to create a Yara rule like previously we have done by using a single binary okay so let's start
done that up and
okay so let's look for Strings
so basically the search of the way to search of Str through as I told before look for Unique ones so again we will do the same over here like this this seem to be so basically the thing is uh it's not always the same that that the present exe or binary is malicious so we have to look for look then in such a way that we get our positive results like this if we compare this to BLS the mspcr is from the legitimate and as I have seen many times that the legitimate BL often ends with the in a lower case as compared to the evance like over here and we also have to look for and if it if in this case if
this D varable one uh have to be in the L case so we will look for it we will try to search and take about the D so this is the prop and then we can also look for few more Str in
the like this two DS over here they are the leg legitimate one so we can see that they use the lower case extensions and see we can find a name
and again find you so yeah we can use it
and again one more D and few uncommon strings so yeah you can them
we can bre this SC a little bit so that it works for
us for
much more so let's add a condition for
this again we can use one
Let's test it
okay if you ignore this
a this was the rule which we have created right now so the rule triggers for single binary but we have one more binary over there so give and and the 11 vers which I have created have both the M of same so I guess we have we should look so in this situation we will look for the for the strings in other binary to so let's look into
it for
then have to leave this and the okay here there are few uncommon ones so we can use this because we can leave this yeah already so we can
it e
seems to be legitimate so we will ignore for other two strings
and then so we will look for the other encoding now
okay so now it have lot of over there so we have to look for something in common because many of them needs to be legitimate so
and all so we have to look for
Strings okay on three it seems to be some decription of the can add done
and let's it test it let's Che does it work not
and see it works fine now so what we have done is we have looked for the strings which are present in both the binaries so there are many chances that you will face the situation where we have to use multiple malware of the same malware family to create your you efficient tool so let's look into the different scenario where we will be creating a code based rol and this one and let's create a file over
here okay so basically some links from the code base rule so the code base rules are basically created using C bits which we will uh figure out from our dis using our disassembler so let's create our Comm syntax and then we will move into a virtual environment where we have a mar sample running in our I okay so one more thing the this meta section is not important even our rule will work if we don't trade it so let's not add itting this rule directly we will move towards
stren so the code base rules are basically the head asml values so to add hexad decimal values we will be we have to use parenthesis in instead of invert double inverted commas so let's move in a virtual environment over here yeah I have opened the binaries and we can see over here use portion of the code is similar in both the different binary so this is what a code base rule is we will use this op code bit present over here and here and the few code is different like few bits of the codes are different which are because of resistors and we can also look over further down that the code is again different so this is what we have to
look for similar code in the multiple Mar samples and using this similar strings we will create our code base R so let's start with using this op bits so uh over here just and in this smaller sample in the small sample the register values are different okay so when the values are different we have to while card them using the question marks so let's go in the next line where C1 and C1 is similar so
again the registers can be changed from binary to Binary and compiler to compiler so we will again while card that and we will focus on our constant value which is z b so we add it and the next one Z app
and then again this do are the register Valu so so it's not hard and fast tool so we can add like this AF and we can while card this D1 and D7 so this go different from condition to condition so like over here we have D7 and D1 even if we while card this and for V carding this one D1 and D7 we can v card the last portion of the of code and it will work fine for us or we can completely while card it too so it's completely your call what you want to do in this situation and then again if you move in the next line which is 39 and D5 and over here 39
and C8 so9 and again as it's a register we can file card it because it can change from compiler to compiler so it's time to play our
and there is only a single string so we will that and let's save our tool and try to compile it
and you have code the rule which we have created using a code works completely fine okay so let's test this rule in our mware database we have created and let's see that it works in this
situation just to find two different binaries okay so this is what we have this is the way we have to test our rules using our pre-created database is to test the efficiency of our tool okay so I have a pre-created rule for M cats too so y using Y you can also look for your M cats or other post exploitation softwar in our environment which can be used in red team assment to harden your defenses so let's see does it work fine or not okay let me explain the yeah so this means that in this portion of the code the rule will uh accept any value from 0 to three same goes above so this
are some best things which supports supports Yara supported by ARA in our hunting okay so let's test this
and you will see that do it work yeah it works for our binary completely works fine okay so let's move further so an automatic tool for generating y so we have basically two common tools which is Yen which also developed by floran and other one other another one is Lara generator so both are best in the working uh but the most preferred one I will say is the Yen because it uses uh huge Str string database like over here which we have created for malware samples Yen similarly Yin uses a big database of things to create some best tools and I would suggest you should try both of them and see which works fine for
you so final thoughts look for while creating Ur rules you look for unique extin and similar codes and in the code base rule while card the things that can change from various binary to binary uh like the register values and for testing just create a big collection of malare samples and some non malicious files like over here this is a small database I would suggest you should use something much bigger than this for testing your rules and that's from my any questions
okay I have any and you can ask questions if you have am I Audible
hello do you have any
questions okay so do you have any questions to ask feel free to ask them
all right thank you so much okay that was uh that was good uh we always love Yara here okay there's one question yeah I can we can say that uh it's not an Standalone tool but yeah it's a great for using an endpoint security as the rules can be passed using all the uh many common ideas supports Sara and other many tools like in we have many common tools based on Yara also so like cucko andand box and and many thread hunting platform supports it so yeah it can be used in endpoint security too okay Yara uh I have not tried Yara for detecting fishing em campaigns and emails but yeah I can guess it can work
because if you use the strings which are present in a fishing email or fishing campaign yeah I can say that uh it will work but yeah I will not I'm not 100% confirm about it would like to try this thanks for this one I like it okay is there any other question all right perfect I think that's ITA if anyone does have any additional questions please post them up on the Discord talk yeah yeah sure I will look over them y other than that thank you so much and we get ready for our next speaker okay it was pleasure speaking with you thank you thank you