Who's Breaking into Your Garden? iOS & OS X Malware You May (Not) Know
Show transcript [en]
not been jailbroken. So please give a warm welcome to our next speaker, Claude.
Thank you guys. Actually this is the first time for me to make a presentation here in United States. So kind of nervous.
My name is Claude Shao and I'm currently working with Palotten Networks. All of my 10 after I graduated working on the antivirus issue, first of course in Windows, and then when the Android malware became a problem, I moved to Android, and then most of the recent one and a half years, I worked on always an OS X issue. So our topic is about the malware. Just about one or two years ago, people always ask the problems like this. Does iOS malware actually exist or Mac, is there any harm for malware on OS X? So some media, some top media even said, let's ask an expert. But if you really ask it in a Cora or some other platforms, expert will answer
you and say, oh, never mind, they are not. No problem at all. So I doubt that. Our statistic data is here. Of course, AV security owners have their own standard to classify a new family, so this only reflects our standard. Through this chart, you can see that over the past two years, there is a huge increase of iOS malware, especially that previously there are pretty many of approval concepts. province, sorry, proof of concept male whale, that is Joseph Research's load spread in the world. But in the past two years, there are more and more trojins and spider whales in the wild and you never see a pork anymore. So, on OS X, it's similar that you'll find that in the past four years, there was a huge increase
of trojins, ant whales, spider whales, etc. And there are lots of POPs. potential that want to program. And you can find that in the North Yelp, there are also some exploits being used by Melville in the world. So, this is statistical about the new families. If you count about the absolute Melville sample, unique sample number, you'll find it will be still increasing month by month. Today we are talking about these topics one by one. I'll introduce lots of actual hyper problems as cases with you. And I think that as far as I know till now, this should be the first presentation ever that talking about the iOS malware issue. So let's begin. First one is about problems in non-GL broken devices.
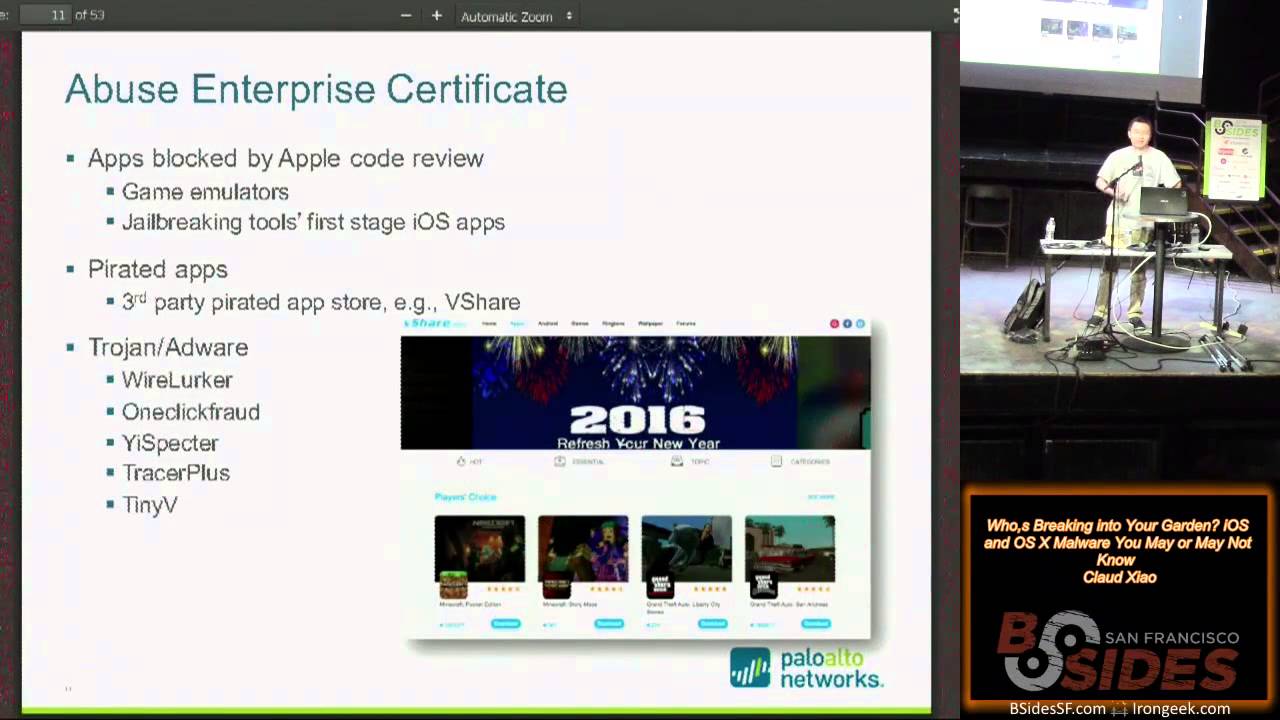
This is a very simple workflow that normally Apple's design that normally an iOS app will produce and release. The developer released an app and submitted it to Apple. Apple will perform code review and then sign and then publish to Apple Store so that every customer could download it to the devices. So this is very simple but it's important. The importance is that Apple's security design and lots of security virtualization or assumptions will rely on these procedures. Yes, it is not a technical procedure, it is just a human design procedure. So, if you find any way to bypass it, basically you win. There are lots of cases. The first one is the most popular, the enterprise distribution. So, this
program is also designed by Apple. It is used in this case that if A company developed an iOS app that only used internally, which means it does not need to be published for public downloading. Also, some companies or organizations like the FBWatt or the NASWatt may not want to take a look at their code, then they were also using this one. So, through this program, any company could apply for certificate and then write the app and then sign it by themselves. No code review, no submission, no distribution anymore. And note that there isn't any restriction, there isn't any technical restrictions on say which devices could install it or use it. There are only legal restrictions that you should always use it internally. But that's not the real
world. So, in order to use this program, What you need to do is get an account for enterprise developer. That costs about 300 bucks a year and you need to assign legal documents. The most hardest one is the DUNS number. I don't know what's that, I just copied it from Apple's website anyway.
Okay, but if you are not a good guy, what will you do? Of course, you cannot provide that one. Oh, sorry, I cannot provide that either, anyway. So you can actually buy it from the ground market. If you want to buy a whole account that will be only used by yourself, you can get it by 800 bucks. Or if you just want to distribute some emails, you can just buy a service that will sign it for you. And you will not get the certificate yourself, but you will get it validated called signing. I call that as a signing as a service. So it's S-A-S. That's three bucks, a cup of coffee. So, this method actually has been abused, has a very
long history. Then I remember in about five or six years ago, they are beginning to have lots of ritual game emulators begin to use this way. to distribute themselves in the world. They are not harmful, but they violate the copyright license. So they will never get any chance to be listed in Apple Store. And so this is, I remember the first case that being abused is the I4GBL or something like that anyway. So later, some of the jailbreaking tools, that is something like Panku or other ones, will also use this. for the first, in the early stage that if you want to jailbreak your iPhone, in the first stage it will install an IPA into your devices. That IPA sometimes also sent by enterprise
certificate. So there are also some parity apps that use the enterprise certificate to distribute through the third party Apple store. An example is VShell. VShell existed in, I think, beginning two years ago and it provided services to at least eight countries. Even some of my colleagues' children in elementary school know how to use it. Also, this is actually maybe a security flaw that you can bypass parent control in old iOS versions through the enterprise certificate. So my friend opened the parent control, disallowed his son to install games from Apple Store, but one day he found that there are some extra games that occurred in the devices. I have no idea. So, from about one and a half year ago, since the Welllooker, the malware began
to abuse this way to distribute and we have seen more and more. So, this is I think the most popular method. Another kind of developer account or say certificate is personal certificate. Previously, you will need about 100 bucks a year. Oh, sorry, I'm wrong, 99.
a year to get a personal developer account. Since last year, Apple released another new program that you can, if you only want to sign it, test it in your devices, you can get a certificate free. So when the program announced, there are already many medias and people in the community doubted that say whether this program will be used to distribute
pirated apps. However, this program, in order to use it, you have to open your Xcode and then compile a new app and then use Xcode to apply for the certificate. Then Xcode will sign it for you and push it to the devices of yours.
So, what we saw is that It will be abused but likely will not be widely abused or automatically abused. But this thought was broke by a newest discovered malware that we discovered in Northwick. The name is Sig Helper. Sig Helper actually implemented lots of protocols that used the Bible. For example, one of the protocols implemented is that it reversed the Xcode client and then it made clear that how Xcode negotiated with the IPOS server and to get that certificate done and how it sent apps and stored apps. The most interesting part is that it implemented all of these inside the iOS app client. Which means, itself as a normal app, it could apply a certificate by your Apple ID and then
sign it and install it. Everything get done in the iOS devices. No need Xcode anymore, no need a Mac or a PC anymore. Sorry, no need a Mac anymore, no PC here. Another interesting thing that this malware itself as a parity of Apple Store's client, successfully landed the Apple Store, landed the official Apple Store. I have no comment on this. Another kind of problem is that serial volubilities named Moscow. This volubilities was disclosed by the researchers in FileI and reported to Apple in the
past years and then till now has already been fixed. So these vulnerabilities occur when there is a collision of bundle ID in the iOS system. So these include if it's an IPOS bundle ID or VPN plugin's bundle ID or bundle ID that is scripted in the manifest or extensions. Then if there is a collision, the default policy of the default policies Apple made may have security flaws. For example,
if there is a new installed app has exactly the same bundle ID with existing one, it can override it and get all the data belong to that app. So why these problems exist and how to abuse it? This is what I said that Apple designed many of security features around the procedure. Because in a very good world that everybody should submit the app to Apple Store and then Apple can control it, there won't be any collision. However, if you use the EnterpriseSand and distribute it in the world, bypass the Apple Store, then nobody can control it. Nobody can ensure that there won't be collision. I think this is the This is the main reason that this kind of vulnerability is being awkward and being used. Actually,
the first one, the Apple bundle ID collision vulnerability has been abused in the world. The picture see here is an example that you can see. The bundle ID is Facebook Messenger. So of course it's not the original one and you can see it contains an embedded.mobile provision file which means it's sent by an enterprise certificate. Also it contains lots of code that come from the hacking team's leaked data. We don't know whether this sample is made by hacking team or someone else but this one occurred after the leaking and you can see it will trying to read lots of
chart history from different kind of IAM apps. Of course, all of these require jailbroken, but this is successfully abusing the vulnerability.
Another kind of problem is private API. Private API means that they are not documented in the official SDK. and some of them are pretty privileged. Also, just as what I said, Apple thought that you should always submit to Apple for code review and the code review will disallow you using these private API. So, I guess maybe by this reason that some private APIs do not restrict it very well in the system by sandbox. If you're using enterprise certificate that bypass the code review, you can use this. So for example, I give some examples that through the mobile installation framework, you could invoke some API that could be used to install or uninstall iOS apps on site. And through the springboard services, you can get a
list of all installed apps. And some are through the call, you could get some of the privacy data like this. A real case is the inspector that we found last year. So this malware do not require jailbroken and it's spread through multiple ways. Some of them are pretty interesting. For example, we found that it will spread through the internet traffic hijacking. So, these hijackings are launched by third party but by the ISPs itself. Actually, it's an advertisement platform so that ISPs could inject the advertisement to the HTTP session. However, ISPs do not know. I think they may know so clearly about what kind of content will be shown in the advertisement. So, this malware actually
injected the ITMS services protocol data to this advertisement session and then the normal iOS user will find a dialogue to say whether you want to install some new fashion apps. Also, it will also spread using some worms that the Windows platform, I will explain later. All of this was sent by an enterprise certificate The name is Beijing InMob technology company. This is also the creator of this malware. So, through abusing the private APIs, it could do really harmful behaviors. Includes install some apps. Some of them are even hidden. Hidden means that you cannot see the logo, you cannot see the name in your iOS phones. Because this is a bug in, I think, before iOS 8.3
or 8.4. And it also collects some of your privacy data. It could remotely install some apps to your phone in further, and it could replace existing apps or trying to hijack other apps launch. Because through private API, it could monitor which app is running in the front and then promote a new interface in front of them.
This is how to talk non-jailbroken, but another more important problem is that the Apple Store itself. So this way, it's not to bypass code review by avoiding it, but just go through the code review and land the Apple Store. The first case, I think maybe some of you have already heard about this is Xcode Ghost. So this is the compiler malware. The attacker successfully created seven versions, including dozens of files of the Xcode compiler itself, in fact it changed it. And then this attack actually existed in more than six months, half a year, that nobody discovered it. Maybe I will explain later. And it finally successfully affected more than four thousands of apps in Apple Store. And these apps accumulated hundreds of millions of installations in total
and affected users around the world. So this is, I think, very interesting that previously we have top free apps and top free games and top paid games, top grossing games. And finally, Apple have already created another list of the top affected apps, this here, showed in the background. So the idea of compiler Melville came from actually computer science guru, Contemson, that when he got the Turing Award, He make a presentation to show his tricks to embed the backdoor in the C compiler that he created so that he can log in everyone's computer. However, when Contemption doing this hacks is pretty complex, you need to pause the C syntax generation and then generate some code in storage to identify whether it's a backdoor slot,
whether it's a remote login session. However, after 30 years, how easy can you create a compiler malware? The answer is a single name. So, in modern systems, including Linux, Unix, OS X, many, many apps or system configurations were through the text file. So, the attacker successfully found that the only thing he needed to do is change one line of configuration of X code so that it can force that AV apps compiled by this X code affected the malicious code. So this way, I think everyone could recreate it off the golden information. So another problem is that why developers were using third party infected Xcode to compile their product and to release it. The answer is complex. First of all,
IPOS Global CDN has some issues that if you download it from mainland China, you may get about, I think, at least two days, at most, maybe two weeks to download a new copy of Xcode. This is the first one. so that developers will share Xcode installs through the cloud services. Hence, the attacker trying to make the infected Xcode and spread it through internet to developers' forms and even tried to make some SEOs to help his distribution. So, these pictures are captured in the first day that I was investigating this malware. that I tried to search Xcode downloading, of course by Chinese, through Google. What I found in the first two pages, except for the first one
result is the iPods, all other 39 results are malicious. This is very successful SEO. Also, the last problem is that lots of developers will disable the gatekeeper. That mechanism is used to ensure that the app you downloaded is original, is not modified. But lots of developers have this hobby to disable it. Actually, even me will disable it almost every time. Because as a developer, lots of apps that you need to use do not send in any way. So people will sometimes disable it. There is another potential vulnerability. But we cannot prove it happened. So, let's ignore it anyway. Xcode goes, it's not only a malware, but it's actually, since it infected hundreds of millions of
users, another problem is that it exists their vulnerability inside it. So, this malware will communicate with the C2 server through just HTTP. The payload is encrypted by a customized algorithm, that is just a DES with a fixed key. It's a stream with the first eight bytes of stream with. So, which means you can hijack it. That's very easy, you can hijack it anyway. So, through hijack it, what can you do? Through the C2 commands, you can reach an API called OpenURL. Guys, this URL, this API, the open URL is super, super important. Through this API, you can actually launch other apps. This is the key of the inter-app communication on iOS. You can use it to
invoke some system services. Even, for example, you can use it to ask a user, to phishing user to install another enterprise Enterprise Certificate Signed App. Also, there are lots of application level vulnerabilities that will be triggered by this API invoking. So this is very, very powerful API. I suggest you to try to make some fun with this API. For example, trying to find any kind of popular iOS app, legitimate app, and likely you will find an open API and try to control it, you can do pretty many of things. I personally think this could be classified as a kind of vulnerability or backdoor just by some details or background. So this is a pretty dangerous issue. It's not an end.
The story does not end actually. After the Xcode goes, we found that, for example, TinyV and Zaghelper also infected by the malware. So, which means there are pretty many of the samples that are infected by two malware or three. And it's hard for, maybe hard for some antivirus vendors to detect it correctly. Some more potential talk include that You do not really need to distribute the 5 GB Xcode installer and you do not really need to ask people to install it. You can simply locally modify it. Note that Xcode is installed in a normal, in a fixed and normal position. You can modify it without any privilege, without any root administrator privilege. Also, there are lots of AdWords, I
will show it later. There are lots of AdWords distributed in the world. You can just use any kind of AdWords or using any kind of vulnerability to just modify it. That's all. Another issue is that the similar problem could be due in Android SDK. Yes, some guys have already tested that. That works. Still pretty easy. Another problem is that Xcode is a compiler. Can you try to infect some SDKs or other developers' resources? Yeah, you can. And this happened. XcodeGhost has already infected some installers of the Unity 3D and distributed, but this is not so successful that only a very few of developers downloaded it. So talking about the third-party SDK, this is a problem that maybe some people do not realize that SDKs usually,
especially when it's a advertisement SDK, they're usually available only in the binary form, which means for normal developer, there is no code review or he cannot know what exists inside it. But you will always use it. embedded into your app. So these SDKs will share your contacts, include they will share, they will run in the same process, they can access all your privacy data. So, will this be a problem? The answer is yes. Till now, we've already discovered three different SDKs that are spreading the well, the contents of harmful or malicious or suspicious code. The first one is not so well known. Its name is Jui He. And the behavior is to collect your contacts and collect your information and then send
short messages to your contacts. Sounds pretty like the find on the call, the first iOS app store mail. So you do not use any advanced techniques. You just invoke the official normal APIs. So it was very fastly discovered by the developers, because your phone, your normal app will ask for the contacts. So later, they are Yoomi and AdSage. They use the private API along with the encryptions so that they could do some more harmful behaviors. And these SDKs really affected over thousands of apps in Apple Store. I have to say that all of these SDKs are from China. And so now it's FAQ time. Many people ask me that, first of all, why is it so comfortable in
China? Second, why do we need to carry about these kinds of questions? So I think the main reason is that the ecosystem is not so perfect in China. people still could try to sell users' privacy and users still accept some privacy or jailbreaking things. So, Autarkus has motivation to do something like this. Why is matters for us? The problem is that first of all, many of the SDKs or other problems will affect around the world. For example, XcodeGhost, actually because
lots of popular utilities or other apps were developed by Chinese developers that they were also affected. Another problem is that Malware authors are trying to learn more and more techniques. An example is that in the OS X, last year there was some vulnerabilities in OS X being disclosed that could locally get the root privilege So one of them, after being disclosed, after five days, an OS 10 AdWall quickly updated to a new version and used this one-day vulnerability exploit to get a root. Jesus. Even an AdWall in these platforms will quickly adopt any progress in the field. I think this is the main reason that we need to care about everything. So talking about private API, You may think that I just said Apple
do not allow any app in Apple Store that use it or use it in any way. But a recent academia research shows that there are about 7% of apps in Apple Store actually use it. Not directly, but using some dynamic loading and reflection to invoke it. And then the strings of the API used for reflection was encrypted. So it's just dynamically invoking, that's all. You can? No. I see. Okay, okay, I do not comment on this. So, the problem I think Apple store is that if the malicious app only targeted a specific kind of data, which means that the node contains traditionally or normal generic suspicious behaviors, it's super hard to find it. For example, they
are fake talk, they are Insta agent. Insta agent will be in the top one in Apple Store. It will ask you to import the Instagram account and password and to provide some function connected to you. But it will in the background upload the account to the other server. You don't know what they are doing. But this is the only malicious behavior or harmful behaviors it has, which means by traditional way, it's almost no way to find it, to automatically identify this behavior before you know it. So, a most recent issue I think in this direction is a Twitter bot. That's a popular third-body Twitter client. And people have already discovered it will send back the Twitter session. to its own server and then people
found abnormal login through some other sources. So this is a single kind of problem. So, all previously actually had some techniques, had some, it's not advanced or so, but still had some techniques. But the last one, I don't think there is any technical. Zig help that discovered in last week used a very simple way. I think that even children can understand it. That if you open this app in any region or any countries in the world, except for China, you will get an app that teaches you how to learn English. But if you open it in China, it will be a third-party app store. That's Zig help. Also, this malware trying to self updating through the
dynamically loading Lua script. So, using Lua script to reflect Objective-C method. So, this way it could upgrade some new functionalities without going on review of Apple Store again. This is another trend I think. In about one month ago, some researchers disclosed another third-party SDK that is called a JS patch. That one provided functionality to all iOS apps that you can use JavaScript code to upload or hot patch your apps. So all of these bypass the sound web restrictions that do not need any kind of dynamic load code loading. And I think it will be another new method that Melville will adopt as a standard. So another question that some people ask me is how we discovered this one. Actually, very
simple. This one hard-coded plain text. It does not obfuscate or increpid any of the suspicious behaviors. So you can identify through any kind of static signatures. For example, these two, one is used to install third-party apps, one is used to log in into the iTunes. Yeah, that's it. So which also means, I think, maybe Apple's static analysis checking on the Apple review procedures is not so good, not so well for the security checking. Anyway, it's a top secret, I have no idea. The next problem is that targeted attack. Yeah, pretty many of Melville has already been used in the targeted attack. Some of them are advanced, some of them are not. And this is a list from in the past two years, but
there are some more in previous.
Those malware has already used many interesting ways to spread. The most popular is phishing through email, just like other APTs in the Windows platform or even using to attack some industry control system. Also, it was said that the name is XSser. It was said it also used the WhatsApp messengers. but I cannot confirm that. Also using some USB installation, so the newest Orchard Lotus uses the watering hole.
Hekinting also found some way to try to develop some more advanced spyware for iOS. And this is a screenshot that they send an email to an iOS expert to say, can you help us to develop a new one? And actually, if you search by Google, you can find more and more iOS spyware. Those are commercial spyware. So I will not say they are illegal. I just say they are not good thing. And you can find it. There are even top list. So when I check this list, Interesting thing is that the first one, each client could attack no jailbroken devices. I think, what? Never heard about that. But the actual answer is that it requires you to input
the iCloud password. That's your Apple ID.
Another problem is cross-platform. This is not about what we normally say. If we say cross-platform, it's normally said a malware that can be run in different platforms by the same code, but this is not about that kind of cross-platform. It's about to say that the attack is not only in a unique platform. The first problem is that, I have no idea how many of you guys know that you can install an app from PC or Mac to your own iOS if you ever paired it once in the first time. So first time you plug in your iPhone to a laptop, it will say you need to pair it. After that, if your PC or Mac compromise, malware could
automatically, in background, no user interaction, install malware into it without user confirmation. So this is what has already been demonstrated in the black hat two years ago. And then, well-looker learned from it and talked in the end of 2014. Another problem is what we call backstop. The idea is very simple, but the result is pretty worse. So, simply speaking,
By default, totally by default, when you connect your iPhone to your Mac or your Windows, iTurnos will automatically back up all of your data, notice all of your data to the PC or Mac without encryption to a fixed position. So, if you are a malware of PC or Mac, what will you do? Read it, pause it, steal it, that's all. Everything is done. So, we did some investigation on this potential problem and we actually found six different families had this behavior since six years ago. But nobody noticed it. This is extremely dangerous because everything, including your eye association, including all your email, your contact, your photos already been here.
That's the problem. Another problem is eSpector. This is not kind of cross-planform. eSpector, one of the ways it's spreading is through the worm that's named Lindon. Lindon will run in the Windows PC and hijack the session of the Tencent's IM message named QQ. It will hijack the session and get the token. So through the token, it will access QQ group charting's API and trying to upload some malicious HTML to the group charting. So everyone else in the group will get a notification, say that you uploaded a new HTML file and you used some titles and poem words to attract you. click it. So if you click it through different platform, different malware will be downloaded to your devices.
And for iOS, this is the inspector. Another example, maybe still not well known example is what we found from about two or three months ago from iOS Total. that a micro malware. Micro malware is a malware that abuse the future in the office documents. So this is pretty popular in last century. But I have no idea why from last year it became popular again. So normally this kind of malware attack Windows. But this sample is very interesting that it will also attack Mac. You can see there is a function named MacShell. So it will determine the system. If it's Mac, it will invoke the Apple script. Apple script then open a Python code. The Python code will build a backdoor connection to the C2 server. That's the functionality.
And till we discovered it, maybe till now, nobody detected it. One of the windows detected it as suspicious without any other knowledge. So what?
Yeah, there's not a problem or no problem just for fun. Yeah, indeed, there are some Windows malware went into Apple Store. Can you believe that? And they even sell that. So for $1, you can go to Windows 1 and for $2, you can get a JavaScript malware. I have no idea. Yeah, you just believe a lot. Anyway, the last problem is that the advertisement and Apple IDs. Advertisement, this is what I see in the web prepare of these slides. So two times, I don't know how many people made this situation before, but my colleagues always made this, that if you're browsing the internet, you will, especially you search by Google and got some results, you open it. You were usually
being redirected to a website like this that your Adobe Flash Player or Media Player being out of date. Unopted. Ridiculous. I uninstalled my Flash Player a thousand years ago. So anyway, this is a major way that content OS X and AdWords being spreading that scare you, cheating you, or fish you. But anyway, it's not a news. Come on. Somebody even thought this is a new malware, it's actually not. So, in OS X, the most popular problems in the last year are all AdWords. Those AdWords were made in the last two years. And if you downloaded something that has a background like this, and then it's installed, in most cases, there are just one of the AdWords families that already know it. And those
AdWords already used some techniques to anti-reverse engineer or try and avoid being detected. For example, using the packs of obfuscators. And even for example, not only the back row of packers or the JavaScript obfuscator, this piece of Python code is also being obfuscated. And it's also using lots of different script languages to implement the main functionalities so that you will not find it cause the script much more easy to obfuscate it to avoid static analytics. So they're also using encryption to protect this language, this code, and also adopted anti-VM and anti-debugging. So advertisement is, I think, is a huge industry that, Melville also would like to get some money from this. Another kind of talk, except
for AdWall, another kind of talk we found is that Malware is trying to earn money from the advertisement through stolen the developer's credit. So AdSafe is a very normal Malware. You know that in the iOS, if you are a developer, you will develop free apps, you will get a unique ID from each advertisement platform. You embed it in your app and then you can get money from the advertisement provider through that ID because they know that it's your ID displayed this as. So, AdSafe is a jailbroken malware in iOS that uses a mobile software to replace all of these IDs to replace it through an attacker's unique ID. so that all targets, other than the original developers, will get money from the advertisement platforms. So, there are
already been dozens of advertisement platforms being hijacking through this way. And I got data, when I found it, I got data from one of the advertisement platforms to get some statistics about how many users being affected. It's huge. Also, this trick, also learned by some others. Note that there is a log save-free in the modmui repository that also learned from it, did exactly the same thing. So I think they are from different authors because of... Okay, due to the time, I'll skip this. But anyway, just to note that modmui is the default repository in the Cedia. Which means all jailbroken devices can't find this app before it's been removed. So, I just said,
sorry, I ignored that. Sorry, I have no idea about, there should be a slide about Xcode Ghost, but I have no idea why it disappeared here. Anyway, actually the Xcode Ghost is,
I noticed it in August, about a month before we published the report, but I missed it. The reason I missed it is that it's because the key reader is also infected by Xcode goals. And the main behavior of Xcode goals, except for the OpenURL API, the main behavior is to upload these users' privacy data to the server. That's all. Why the people created so huge project? make so many efforts only collect so few user privacy. So finally, I have a, I think the possibility, I cannot confirm that, but it's a possibility that it's the same. The Xcode goes out there also trying to steal the advertisement promotions of fee from the original developer. Because that
still through the IDFV, some of the app promotion ecosystem using this idea and all this data, trying to track that which app is promoted by who and then give some money to that promoter. So this is a hypothesis, but I cannot prove it because I cannot confirm it because the original authors, two authors had already been arrested. So another issue is Apple ID. Apple ID is super important nowadays that you connect it with your privacy in iCloud and it can be used to control your devices, send messages, pay money and use it to either download premium apps or trying to promote the free apps to the top list. It could also be used to get some development certificates. So this is another thing
that malware users would like to get. So that happened in about two years ago on Ford, in iOS, Melville that only have one function that is using mobile substrates to hook the communication between the Apple Store's client and the server, hijack the HTTPS traffic and get the data inside it. So there are some more later. As a conclusion, I think that first of all, there are new families and then non-jail broke and the Apple store has already been compromised. There are targeted attack and the problem is now limited in the single platform and people will also make a huge profit through the advertisements, through the Apple ID, etc. So one more thing, although Apple's platform is not so perfectly secure, I think they've already made great effort,
especially on helping people to protect their own privacy inside most recently even I think. So from this point, I support IAP here. Even I said many of not good messages to them. Thank you, that's all.





