From Law Enforcement to Cybersecurity: Building Skills That Matter

Show transcript [en]
So hey everybody, good afternoon. Thank you so much for attending this talk today. Here uh we are going to be going over from law enforcement to cyber security building skills that matter. So for all my gamers in the room or online, we've all played Skyrim. You can't get past this part. Who are you? We need to introduce myself so you guys kind of know who you're looking at and listening to today. Now, I'm not going to read this. This is a quick little bio snip sha uh snip chat of my LinkedIn that you can quickly navigate to and kind of find out and figure out who am I, my background, what I've been into. I think the real
important thing that you guys need to know about me is kind of who who is Andrew Karate behind the cyber piece of this. And I'm a D&D nerd. I like Critical Role. I'm a father. I'm a scuba Steve World of Warcraft for the Horde. I like to go to the gym. I was obviously previous law enforcement obviously from my chat if that wasn't a hint. Um I love food. Who doesn't like noodles? That was a Naruto reference of how I was trying to eat the noodles for those that watch Naruto. If you don't know what I'm talking about, disregard. Uh I like to travel and I get to travel thankfully thanks to the military and just on my
own time. That was a picture of where I was in Germany. Uh every year and I joke about this. I like to get my yearly photo with John Hammond, my ginger lookalike or vice versa. Um I like food. I'm We are a Disney household. My wife has never been to Disney until we got married. Now we go every year. I did it to myself. Um I obviously have my my handle and I also go by Ginger Ninja. Being a redhead also with the last name of karate, it just came naturally and that's what I would been called. Uh being in Arizona, there's some lovely hiking places the wife and I like to go to. That's a picture of the wave cave.
If you're ever in Arizona, just a little east of Mesa, there's it's an amazing hike. Only takes about an hour, but it's really great. Um I am a sock analyst. So, with the this is fine meme, that is my life day-to-day dealing with sock detections and living in that. Um, and I'm currently still in the military as a warrant officer. So, we're going to talk today obviously with my transition breaking into cyber, but also just to talk about getting into cyber security. So, coming from law enforcement, I saw that there was a lot of similarities of sock analysts and beat cops. So taking calls for service were kind of similar to picking up sore cases to an investigation. Doing case
investigation was very similar to working a case and figuring out why this alert fired. Uh writing police reports to send up to our higherups so that they could kind of see what's going on within your city was very much the same of having to create reports and then sending those up to audit or to your teams to kind of figure out what's happening within your environment. But a lot of folks ask the same question. What do I need to do? Where do I need to learn? How do I start? And any of us and all of us that have been through applications, especially right now, we know that feeling when we're the one picked out of 10,000 people when a job
goes open for about an hour and there's already 5,000 applicants. So, what's the first thing we do when we want to transition or break into a new career? We go to Google. So, we type in what any good analyst or co-orker would do when navigating and doing case investigations. We ask Google, "Hey, how can I get into cyber security?" And with that, we're going to start pivoting and pivoting and looking for the right role that fits us. Some of you would like to be sack developers, maybe dev sec engineers, purple teamers, DLP compliance, sales, there's so many uh how do I want to become the next John Hammond, network chuck, things that kind of help you kind of pivot to the right
the right direction of where you want to go. So the next thing we then look at is career maps. Everyone likes a map. Everyone likes a way that's going to direct us and maybe kind of hold our hands of, hey, what's the best route that's going to take me from point A to point B? Now, obviously, there's several different roles here. If you look at the very bottom of this little list, and this was honestly a simple snip snippet off the web, a quick old Google a quick Google chat looking for career maps. And this has to be the map, right? This is what we need to be successful. This is going to take us from point A, IT,
assurance GRC analyst all the way up to SISO. But, but wait a minute, Andy, that that can't be it, right? Because I've been on Google and when I type in career maps, this is the map I find. And the map from here we can see is from Hack the Box now. Hack the Box recommends a kind of different path than what we just saw with titles and kind of lateral moving up and vertical positions. Right? Maybe starting with try hackme going through some walkthroughs understanding some blue team red team methodologies cracking a box getting root and then moving maybe to immersive labs then going into hack the box then vulhub and so on and so forth as we start to pivot
around this kind of windy trail which I had to laugh at. and anyone here that's a red teamer or anything how it end at C. It kind of made me chuckle because I don't think C is the new ending point here of where you're going to end your red teaming journeys getting into cyber security. But Andy, hold on. I I went to Google and this isn't the map we need to go to. This is the map we need to use. And obviously this one is from coders.learning and this map has a completely different path we need to learn. Well, Andy, this is telling me that intro to cyber security is my basic fundamentals of understanding malware, fishing, password
attacks, operating systems, networking, and it's more of a left to right, upto-down model that that's then going to get us to become a cyber security architect. Well, hold on, Andy. There's more maps, aren't there? That's right. There's more maps. Anyone here in this room, if I were to ask you how you got into cyber security, would probably share a different story. And by going to Google and trying to find the best map for you may not be the same path that I took transitioning from law enforcement to cyber or whatever role you sit into. This can be the same thing for my students graduating or coming up on graduation here that are juniors and seniors that are breaking into cyber,
mastering their degree, working on projects, getting certifications, which we're going to continue to talk on here briefly. Now Andy, what's the point of these maps? Well, the point of these maps is that you get to choose your own journey. Everyone in this room, as I mentioned, has a different way that they learned that they how they understood a concept or how they maybe trained or mentored or asked a mentee to kind of break down how they were successful. As many folks know within this industry, we find mo role models and other folks within our industry or folks that are doing the things that are being successful that we can kind of try to mimic or fall behind saying, "Hey, well,
if it worked for them, like maybe if I follow down that same path, it might work for me." But as always, that's not always the case. It happens. Some people choose to go through education via through school. They want more structure. They want something that's a nineto-ive. They want assignments. They want something that, hey, if I don't do this, there might be a punishment such as a bad grade or not graduating. You also have the right path, which is the scary wooded path that maybe that's self-taught. You're going to go on YouTube Academy, LinkedIn, a lot of open source tools, and just self- teach yourself, which is not a bad path, but it's just a different way of how someone
learns and breaks into this field. Now, diversity and roles in cyber security. And I've I've made some slight adjustments to these slides because when I initially tried this out with my DC40 group locally because I'm from Arizona, having all six slides on there was kind of difficult because they thought it was all just kind of a square for a square. The way this is kind of uh divided up is we're looking at six different roles here in the next three slides. So one thing that I always explain to people is when folks talk to you if you're in currently in cyber security or they're young folks trying to break into cyber security there are three roles that
people want to become pentester hackers blue team sock defenders or maybe IT help desk but what these roles I'm trying to explain to folks is there's so many more opportunities and ways to break into this field you have things such as becoming a GRC analyst understanding compliance audits telling your company what's at risk and then how to secure it you have things such as being a cyber security awareness trainer setting up fishing campaigns for your organization, making sure that folks are not falling for that friendly new LinkedIn request that you maybe got at a conference you just went to, but maybe it was from a malicious actor. You then have another important piece which is your project managers. So maybe
if you're working on specific agile project projects or other things along the road that need a little bit of handholding to make sure that deadlines are getting met and the company's making sure that they're getting every dollar for their minute or if you're an MSSP you need to have those kind of check-ins to make sure there's a planning method of how things are being communicated to your team. You also have priv privacy and uh legal which I'd say is really came around in the last 5 to 10 years for ransomware insurance legal aspects of what's need to be protected. I'd also say it slightly falls under the GRC aspect of what data needs to be
protected during organizations on breaches and other communications that come across uh with those specific skills and with other things of hey are we allowed to post this data? Are we allowed to collect this data? Asking your legal team to do that hard legal aspect of work of looking up case laws and other previous events that have happened is another great way of how some people can break into cyber without even knowing it. And of course the two I'd say most prized possessions of what folks want to do in cyber security or some they want to do that cyber security analyst role which is are your defenders that are looking up detections working up cases and ensuring that your environment is
staying safe or your pentesters who are ethically breaking into your environment and trying to make it unsafe and then resafe by making up those reports on hey we were able to bypass this certain rule or this large language model and we need to refine this to make sure it's actually safe and secure. All right, everybody. I'm going to need a little bit of help on this one. Can someone in the audience either by shouting out loud or show of hands explain to me how they could solve the maze to my left, your right?
>> And as I work my way through from that left
and you come down and you don't want to go into that. >> Okay.
>> I'll save you some time. So, you're analytically going step by step and going to go from point A to point B through the the maze. Correct. Okay, that's awesome. Is there anyone else in the room that can tell me another way to solve it?
>> Excellent. I see another hand. I see that one. What about you, sir? >> Excellent. Okay.
>> I want to
All right, I see one more hand. Go ahead.
Awesome. So, real quick with that excellent group exercise, thank you for everyone for the participation. See how everyone had a different methodology or analytical thinking to solve the problem I put in front of everybody. So, when it comes into I'd say skills that matter most, we didn't have to be technical. We didn't have to open up a control prompt. We didn't have to write out a detailed SOP. We simply had to have a had a good strong conversation and then explain the different ways that we can solve a problem. So this ties into I think soft skills and being able to communicate and storytell which when you're trying to break into cyber you're trying to be the
best candidate to help solve a problem or solution that an organization is trying to fill for. So the point of that exercise was just exactly that to show that there's several different ways sometimes to solve a problem. And when you guys get into these roles or if you're already currently into that role just to always remember kind of keep that same mentality because not everyone's going to look at something the same way. And by doing so we're able to solve these problems by using different mindsets. Now, now as I mentioned, but Andy, what if I'm not technical enough? What if I don't know how to code? What if I don't know C++? What if I don't know Python?
These skills that you're going to be learning through either self-education or through a education foundation through college. These things can be trained and these things can also be learned on the job. Uh, I'll tell you with full transparency, when I first got my job leaving law enforcement into my first role at the state of Arizona, I did not know how to code. I did not know Python. I did not know C++. I could barely navigate around a command prompt. Now, I explained that to my employer and understanding that, hey, look, I understand that I might be missing some of these technical pieces that you're looking for within the best candidate. But how I was able to transfer a lot of
my skills from law enforcement was, hey, I'm still very standardized and systematic. I can still walk through a process from point A to point B, and I can still give you a full fivew of who, what, when, why, where of why an event or something is happening. And the other thing about being resourceful and considering kind of building out your own home labs and doing uh capture the flags and other additional training on your free time, you can still take all that experience and then translate that into a resume or conversation. So obviously being in law enforcement, I had to spend most my days doing my actual job and then the evenings go through try hackme, hack the box,
opening up my own VMs and learning those skills on my own. And then having those conversations to my employment and management allowed me to still show the skills I learned to get through that break in that first initial uh break into breaking into this organization of cyber security that we're all into today or trying to get into. So here's no ploy on college, but uh one of my favorite memes I've used on another challenge I'll explain here later in the way was get a degree they said. So as I mentioned education I think is very important. I myself hold a master's degree and I can thank the US military for that by using my GI bill.
But college is not for everyone. I use a really good story from one of my colleagues that helped mentor me and get me into cyber security where he was a high school dropout got his GED self-taught though within Golang and Rust and Python and he easily picked up a job working for a government contractor clearing six figures still works that same company today also with a few new certifications and with a TS clearance. So now why do I say that? Because Andy we're we're here at a college like the college is sponsoring the talk. I understand that and I like I said I I I I would push people to if they can go to college but understand as
we mentioned before in our maps there's additional ways to pivot through cyber security and leverage if you're either transitioning from a current current role that's not in cyber to get into cyber security and I also mention here as well as like the certifications can fasttrack or maybe pat a resume certifications are excellent but the caveat is is when you're using certifications to pat a resume to become an alphabet soup after your name and you're not retaining the information. You're not doing a service to yourself. I've had pe I've had talks with folks on my channel and across the environment where they have every SAN certification that I may or may not even heard of on
top of Google and Azure certifications, but when I ask them maybe a certain specific question on a networking topic, they they don't know. They have to look that up, which is fine. There's no harm in that. But just understand that if you're going to be going through either education for a good strong knowledge base on the basic foundations of college, retain the information the best you can that you're going to be able to explain that to on a resume or pivoting to that next role. Same for certifications. Don't just get a a certification then dump all the information. I've taken certifications that have not passed, but I still learned and took all the information from those trainings, sand specifically
because they're just it's they're very expensive certifications and some of the training can be difficult to maintain and actually learn. But I took that back to my organization and I still helped set up new SOPs and procedures that still trained and kind of did a train the trainer to educate my younger analysts that haven't been to those trainings. So, quick optimization on LinkedIn searching for those that are looking for jobs. So now this is probably about I'd say maybe a month or two old, maybe even three now. But there was a method in here where if you go into the LinkedIn job search, you could actually pivot the uh URL where rather than filtering for
24 hours by changing that to 3600, it allowed you to filter jobs that were only posted in the last hour. Now once again, for a little uh uh audience participation, who here can maybe explain why it would be important to see jobs that have been posted in the last hour compared to the last 24 hours?
very true. Very possible. So, what he said is that uh for those that are obviously watching the video and maybe didn't hear on the uh bides chat is that someone could still be waiting to see applications come in through that post. Um anyone else? >> First get priority.
>> Okay. So, he said that first applications can take priority. So, I will I'll put some truth yay and nay behind that. So, yes, I think my I would agree that with I'll get right to you. I would agree that by being one of the first applicants, if it's being actually looked at through a real person rather than an automated process through AI where you're meeting all the requirements to the role, it could be higher possibilities that you would be the first one to be looked at. I agree. So you sir
So he mentioned that once again like being able to be the first one to apply you could be the the first one to be looked at or once again many companies like you mentioned once they hit a certain threshold of applicants they will take down the job because it's it's honestly just too many applications to go over. I know when I was back at Wells Fargo, my manager dropped in a position for an entry-level security analyst. Within two hours, they had over a thousand applications and they ended up having to take down the wreck before even the first day. So, just a fun little tip trick and I think I'll be posting these slides at the end of the
talk as well. So, don't feel that if you can't see that or if it's hard to read, I'll make sure that these are somehow visible. So, continuing on with get a degree they said. So, what's the return on investment? So that's one thing that as I mentioned before when it comes to whether going down the education route through schooling, whether it's going through your own uh YouTube learning and certification maybe uh paths uh what's going to be the benefit out of these and what's your end goal. So targeting searchs that boost credibility faster could be important. So if you're trying to get an entry role into cyber certifications and you want to be a security analyst, you'd want to target
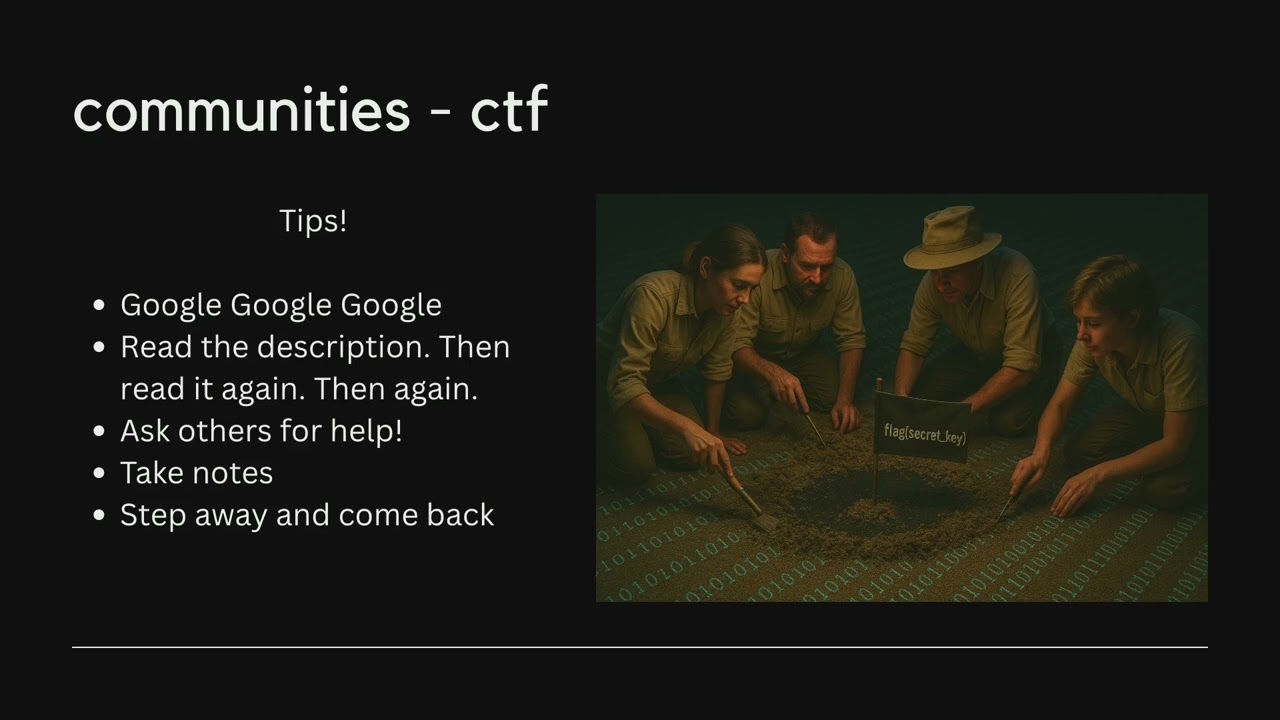
blue team certifications. If you're wanting to maybe try to get that mix of experience and certifications, that's where building home labs, uh, participating in capture the flag just like how Bides Cache is doing theirs today and just mentioning that, hey, I was I go to my local meetups and I compete in these CTFs on my own or with a team to kind of help and grow kind of some credibility even though you're not in actual environment or a network. You can still mention that, hey, look, I've used malware reverse engineering lookups. I've done large language model uh CTF events where I've had to break language models to provide me information it wasn't allowed to or uh
there's been pcap uh I know there's a pcap challenge on this one today where hey I've navigated through wire sharkark and I know how to look for specific events that could be malicious depending on the traffic we're seeing. So then as we tie into like what certification do I get Andy and that's going to be a piece where as I mentioned before certifications are excellent and some of these are I think slightly outdated and once again these are all images to simply grab from from Google and some of our beginner certifications. So, for example, Security Plus, the CSA, ECDFP, blue team level one. Um, I've talked to many folks, one on my channel and across even hirings that we're at
such a different level of what organizations are trying to expect out of junior analysts that I'd say Security Plus has moved up to what they're looking for is a CYSA or the cyber security analyst certification because it's such a concern that if we hire these new analysts that don't have the actual experience and an event occurs, who's to blame? Is it the onboarding? Is it that we hired a brand new analyst out of school that has or holds no work experience? But then here comes the chicken and the egg of how do I get experience, Andy, if I don't get a job to get the experience? And that's going to be I see some head shakings and
that's going to be the hardest part to take in mind. And I had a great conversation with one of the one of the folks here that were in the uh room earlier for check-in. Consider this on a resume and when talking through the resumes. CYSA requires in CompTIA's ver verbiage that you should not be taking this certification unless you hold three or recommends 3 to 5 years of cyber security experience. So what does that mean Andy? Well, if you hold the CYSA, could you leverage that? Hey, I know this is a 3 to 5 year certification level where it's saying you need that much time to experience to hold this, but I already hold that. There's also
been conversations I've had where you can also leverage, well, hey, look, I'm I'm a brand new analyst that has no bad habits. So if there's certain policies or procedures that companies have, I've used I use that line many of times on my first few interviews saying, "Hey, look, I have no bad habits. I am a cop breaking into cyber security, you get to train me from the ground up." Now, that can be a positive and a negative. I got some good headshakes. I got some bad headshakes. Well, we don't want to train someone from the ground up. We want someone that already has a good foundation or a foothold into this into this kind of uh tool sets or type of
investigations that we're actually trying to look upon, which I totally understand. I also had some great follow-ups where I made it to a third round interview where I'm like, "Cool." And they're like, "You know what? We really appreciated your drive." And that statement really stood out to us because we can train you and make you the analyst we want you to be. And then I got beat out by an internal hire, which happens. So, how are we preparing for the interview and what are we prepping for? Um, a good friend of mine, Eli Woodward, who used to work for Early Warnings, mentioned that titles don't matter. However, you still want to try to find and look at the next title you want to
become to. So, if I want to become a cyber threat intelligence analyst, I would want to go look at LinkedIn profiles or other folks within this organization or maybe within the network I work in of, okay, well, what are they doing? What are they training about? What are they learning about? Honestly, just reaching out to someone on LinkedIn or your network saying, "Hey, my name is Andrew Karate. I would love to talk to you for 5 to 10 minutes on I'm working on trying to become a cyber threat intelligence analyst. I wanted to see if I could take a few minutes of your time just to maybe pick your brain on things I could be doing to better myself." Now,
what's stopping you from going to Google or Chat GBT or going on Crowd Strike or other kind of organizations that could be telling you and showing you what other maybe threat teams are already pulling up and doing? There's nothing. But doing that extra little step and talking within your your network even and leveraging that to kind of try to level up your next position is nothing a bad thing you can't do. Titles are goals and as you look for that next title and those goals, align your goals in your training with what's going to make you the most successful and the best candidate to move up to that position. Cyber security is huge as I mentioned
before and we're going to keep talking about for the next few slides that it's not just cyber it's not just pentesting it's not just being an analyst on a blue team and it's not just IT help desk there's many different positions that you can get into and prep for for these organizations now another quick show of hands and who here has been through the technical interviews for Amazon maybe through threeletter agencies where they have you open up a command prompt and then they have you run a bunch of commands and they they want to see you code or create a new file or create a process through Active Directory. Anyone in the room? See a few hands? See a few
hands. You'll understand this then. So that interview be like a battle for the worst thing in the world of they're going to put you through the ringer, have you open up command prompts, go through the whole thing, and then you actually get into the job. You're like, "Hey, here's the Confluence page. We have all these procedures already written out. Nothing really deviates, but we just need to make sure you knew what you were talking about." And why do I say that? because it goes back to my initial piece of learning learning and breaking into cyber security doesn't mean you have to be a Python SME or a scripting SME or know exactly how to work your way around
a command box however or the command line. However, having those basic and fundamental skills to at least be able to look up the right information or to do a Google search or to maybe even go through some SOPs or procedures if you're in an organization can go a long way to show that pro that uh the employer that you're you're willing to learn the information and do that extra step to make sure that you know what you're talking about. So, the technical jobs don't start technical. So myself included, even when I got my first role outside of the state of outside of law enforcement into cyber was with the state of Arizona Department of Homeland Security. Very fancy title,
very long name. And I got to work at the state level. We had organizations, teams, cities, counties that fell under us. And I remember telling my boss when I initially got the job, I'm like, "Hey, uh, we can take out the senior security analyst title, man. We can just we can just call it information security analyst." Like, "No, no, don't worry, Andy. The title is just for HR. we're going to train you up and teach you everything you need to know and make sure you're successful, which made me feel slightly comfortable, right? But the thing that's wild is is the importance of titles and breaking into this field is there was so many different people at the state that when
we had certain RFIs or requests for information come up to the state level and come up to us for a solution or a question, it put a lot of focus on me, but I realized that they weren't technical questions. they were really just kind of procedural or a little bit of research I had to find that we already had SOPs for or maybe that organization already had SOPs for or previous engagements for for other teams or counties and I really just learned it was a lot of just me having to do some research and reading. So if someone ever told you that breaking into cyber is going to be just some easy button smashing with maybe running and working
a few detections a day. Unfortunately that's not the case. You're going to be writing reports all day. You'll be going through some uh maybe deep dives into uh SOPs or some standard operating procedures and doing some other dive into other policies in your organization or other organizations if you're an MSP or an MSSP. Another important part of getting into or breaking into this field, whether it's from law enforcement or whatever career you're looking into, is getting into your network and community engagement. So obviously you guys are all here at Bides Cache here in Utah and you didn't well maybe some of you guys got paid to be here by your employers but I would assume that most of us are
here because we want to come learn or talk and find other like-minded individuals that are in cyber security. What's happening? What are these talks about? What is maybe maybe there's a company here that you knew from seeing the besides Discord chat or folks coming on LinkedIn that's at a company you want to go to and you want to make sure you were there to talk to that person presenting or maybe try to link up with here at the the event and just kind of ask some questions and say hi. Now, there's a way you can also social engineer your networking community skills. And I say this because even myself, I'm an extroverted IT guy, if
you guys haven't picked on picked up on that yet. And I like to talk. I do briefs in the military. I talk to folks all the time. I've been given the nickname of Tiger when I worked at the state because I had such a good personality, but I always talk too fast. And I'd also be told by some of my employers like you Andy the best thing we like about you is you make us say three more things a day but the worst thing we like the worst thing we hate about you is you make us say three more things that we don't want to today because they don't want they want to be left alone. A lot of folks that work in
it they can be recluse. They can be to their own very introverted they don't want to talk or maybe work with a team. But being a little bit able to step out of your comfort zone and make friends or talk at these conferences and even set up small skills like you know what I'm going to go to my next bides and I'm going to shake three people's hands and just introduce myself. but that's it. I'm not going to add their LinkedIn. I'm not going to ask for phone numbers. That's it. You've already stepped a little bit out of your shell to kind of go to the next step. Well, the next challenge you might set for yourself is,
okay, well, the next thing I plan to do at my next tech meetup, I'm going to meet three people, but I'm going to exchange LinkedIn informations. I'm going to start growing my network. Then we're done. We're good for another month. But now, let's set that next really strong challenge. So, on your third meetup, maybe find someone that's talking and presenting. shake their hand, introduce yourself, see if they can meet up on a digital coffee for 15, 20 minutes and have a short conversation about cyber security or things that they you could be doing to better yourself to make yourself a strong candidate or thing that they would even recommend that maybe you want to give them a
resume, see if they'd review your resume and go from there. As I mentioned, not everyone wants to go out and be on a podcast or a YouTube or go shake everyone's hand at a convention, but it can get you some places, such as for myself, I went to Defcon this year for free. Now, Andy, how did I do that? I didn't social engineer a company. I didn't send out a fishing email. I didn't steal some creds and get myself a black badge. What I simply did is with my network and what I started doing with my YouTube channel in in Arizona is I started talking to people about breaking into cyber. And with that journey, I got
to meet Josh Mason over at Synak, who luckily enough for me this year submitted Noob Village, Noob Community. We're going to be a village next year. and I was asked to come actually work and help inside the village that year which got me a free badge to defcon. Now what that looked like was some meetings a few months before setting up uh volunteer pages, setting up sponsorships. We did a very noob friendly capture the flag. We had to find prizes and giveaways and how we were going to do it. So slightly some nonprofit work to kind of do that extra over and beyond to earn my ticket. I didn't just have to go there and go,
"All right, Josh, I'm going to head out to all the rooms and go to all these talks." I was inside New Village probably 90% of the time. Now, this was my third Defcon. So, I've been around Defcon. I know what it's about. So, if you haven't been to Defcon, it's a conference that's held in Las Vegas. It's right after uh Black Hat. But what we did at New Village is we helped kind of bridge the gap on breaking into cyber your first time at Defcon. What you should expect villages and rooms that were new friendly and also kind of just being able to let people network and talk about local K through2s and other things that they can do in their areas
to or local bides to come and even meet up. Um, other show of hands. Who here is currently in school or trying to get a job in cyber security? Awesome. I see some hands. So, quick question. I'm I'm assuming most of you guys are already inside building home labs or doing CTFs. Have you ever thought about reaching out to your local K- through2 schools in the community or maybe even talking to I don't know if you guys are going to churches or going to any other nonprofits, but offering those services and maybe linking up with any of those saying, "Hey, look, I'm a senior at X College. I'm graduating next year, but I specialize in doing web
application testing. I noticed that your nonprofit has a website. I'd love to offer you a free pentest or maybe if you currently already have a team doing that, would love to help give any assistance that you can. They're you're going to get one of two responses. One, thank you, but no thank you. We already have someone that does that. Or two, hey, you know what? We do have an organization or someone here inhouse that does that, but we'd love the free help. What does that do, Andy? Well, what that's doing is now giving you some one, networking abilities because you're now talking and working with local K through2s or churches or nonprofits, and two, those are some things you can put
on your resume for things that you've actually done outside of school or outside your own home lab. So, as I mentioned before, networking is amazing and it allows you to meet amazing people. Now, you may not know anyone on this page, maybe other than the very top left, top right of John Hammond for those that know John Hammond. That was my yearly photo with him. And uh but there's some folks in here that you may know. And by me simply networking and creating my YouTube channel and putting myself out there and talking to folks on LinkedIn and Discord communities, it allowed me to really build a strong foundation of self-branding. And I say self-branding because for those that are currently in
the work role, what happens if we lost our jobs tomorrow? Do we have a strong enough resume or a strong enough LinkedIn profile or a strong enough kind of work ethic to where if I were to throw out a a Hail Mary onto my LinkedIn community, would I just get crickets? I've I've slightly learned this last year, one, giving back to my community and allowing myself to mentor and let people share their journey of how they broke into cyber has opened up a lot of doors to me across mentorship from everyone from 12th grade up until even my seniors and folks just leaving college. because mentorship is sometimes hard to find. We don't have folks or
know who to find. We don't have outlets. We don't know the community. We're not part of Discord groups. And so, but by simply just being a little bit more uh flexible and willing to maybe talk to folks or go to your local meetups and break out of that comfort zone, it might open up some crazy doors. Like, I don't know, going to Defcon for free and getting the network and talk to a bunch of amazing cool hackers and blue teamers and compliance folks that are working in this industry that are hiring managers, directors, senior engineers, and analysts that you can talk with, bounce back ideas, and even maybe just work at their company. Next, now these next few slides for those who
are in cyber security or maybe are working into cyber security, these are going to be some outlets I think you should go to or that I would recommend being a part of. This is just a short short list of some of my top favorite Discord groups that I'm a part of. Um, obviously Ginger Hacker, new villager on there, they were just added. Anti-Chip training from Black Hills. Uh, you have Hacksmarter from Tyler Ramsby. He used to be with Rhino Security. He just broke away. Now is having his own uh pen testing company. Uh, you have simply cyber with Jared. Oh, don't let mess up your name, Jared. Jared Azure. It's like Azure, but Azure. I hope I said that
right. Don't kill me. Uh, try hackme. Uh, hack the box should be on there, but I don't know why I took it off. Uh, Ginger Hacker is my own Discord. I post job uh job recommendations and other resource pages as well, just like this. And then New Village, which is the new Discord that we just made because we made New Village for Defcon this last year and will be at Defcon for the foreseeable future from what we've been told. Then your foundation and hands-on skills. So obviously a lot of these are going to be very common knowledge. You maybe already are in these environments and already doing a lot of this training, but these are all still great
ones to kind of throw in and put into the uh the void of things that you should be doing if you're not. So obviously try Hackme. Try Hackme just got done doing their hack to win challenge here I think from September 1st to September 9th but this is a great way and there's a lot of friendly excuse me friendly beginner to intermediate rooms and challenges that you can do in here for free there is a payw wall to some aspects of some of the rooms so this is not just a completely free resource but if you are not in try hackme uh I I even when I was leaving law enforcement leveraged try hackme and
put my little top 2% in try hackme on my resume on other skills I was doing trying to get into the industry because this was my experience. My home lab messing around in try hackme and learning all the skills I could to make myself the best candidate. We are now graduating from try hackme to hack the box. I think hack the box oh loud. I think hack the box is a little bit more uh intermediate red team focused oriented. Um, but however, I've actually been navigating through there a lot more this last uh week and a half or two weeks after coming back from Defcon. And there's actually amazing rooms in there called Sherlock Rooms. And for
those that have not been in Hack the Box for blue team training, Sherlock Rooms or Blue Team oriented training that Hack the Box does. Now, they also have some great OCP prep, which is if you're looking into getting into pentesting, I would say is the pinnacle of right now of where you want to get for certifications. Um, but they have amazing, it's very much CTF style uh, rooms and trainings. There's obviously a lot of walkthroughs and other trainings that you can do with those as well, which I always explain to people that if you get into a room and you're not aware of it, don't be afraid to open up the walkthrough and go through the
walkthrough just step by step. You can always come back and revert the room and refresh it and then just close the walkthrough and then once you've gotten more comfortable with the commands, go through it again to build that repetition so you really understand how and what the box and what the training is trying to teach you to do. Blue team level one uh blue team labs online. So this company is based out of the UK. So one thing I think with a lot of certifications that folks are starting to realize is as much as Compia is uh well known the aspects of only having four simulations I'll say where it's still chooses the best bubble and
that might or a drop down box. uh not bashing on CompTIA, but with Blue Team Level One and some other ones even like such as SANS or try HackMe with their blue team level one certification, they're allowing more simulations where you're actually inside a lab environment and actually having to write up a report, go through logs and how that's more beneficial, I think, when it comes to certifications and training. you can then explain to a resume or during an interview saying, "Hey, like I understand I only have experience via through my home lab and schooling. But I've also done these certifications that actually had live environments where I was inside a sim inside a sore reviewing
spunk reviewing spunk logs uh to better myself and understand what and how these events were happening. Another one right here is just hacking training. So this one just came on the market this year with John Hammond. John Hammed here has tons of free practical labs pentesting recon osent uh malware analysis and he is collabing this with many many many different uh cyber security professionals across the industry. Uh Michelle Khan, Bailey Marshall, uh Tyler Ramsby uh all creating training and products putting into just hacking. Now there are some stuff in here that is free but as always we want to make sure we can pay the web app and developers. There are some trainings in here that you do need to
pay for as well to actually get the full content or training paths into just training or just hacking. We also have Pluralsight. Pluralsight I actually I leveraged uh to get all my CompTIA certifications when I was at the bank at Wells Fargo because we had access to Pluralsight. I also see someone in the crowd that used to be at Pluralsight. But they do amazing kind of video training learnings very much like Udeny uh which they're also going to be here on our slide deck here also going over before the difference with Pluralsight is is a there is no free leverage of this. You have to pay for the subscription to get access to all the training and the labs. I think
Pluralsight has uh Black Hills anti-cipyhip training. Um if you've never heard of anti-ciphon training before please please please take out your phones take a photo of this slide right now. The most amazing part about this is that this is the the part I like most about anti-cipyhip training is the way that they do some of their training certifications. They do a pay what you can model. So they will have five-day long live lab instructor labs with real people, not some automated recorded video you're watching with an instructor. And they will actually walk you through labs and training from point A to point B of setting up VMs, going through logs, going through Wireshark, how to respond
to uh maybe a or do conduct malware analysis. And the way the training works is they'll do a pay what you can model. So they have everything from $0 to like maybe $500. Not saying you have to drop $500. That's more or less for folks that can support those that maybe aren't able to pay for the training certification and kind of trying to pay it forward. But I've gone through several of their trainings and it's fantastic. It's great information. They you get GitHub repositories, access to their discord and actual live instructor uh questions as well if you get stuck on something and the training is actually very uh very beneficial and you get a lot out of
it. Uh Udommy is another great one. So Udommy is very similar I'd say to Pearl site. There's there's walkthroughs. This is where also other folks can actually build out training uh that they're maybe proficient in to uh learn and then share their skills across the environment. I've used this for uh Azure my Azure 900, some Microsoft certifications, Google certifications. I'm using Udemy right now for my CSSP studies as well as some other sites um and so much more. And there's hand-on labs in there and also guided paths. Uh and just another great resource that you can leverage and use. So in conclusion, so the point about breaking into cyber and whether you're transitioning from law enforcement as a
preacher, as a teacher, as a librarian, is to always kind of be curious and ask why. You're always going to be learning inside this field because every six months we have something new coming down the pipeline of new vulnerabilities, new tools, AI is being integrated into everything and definitely networking across your community. So, I've mentioned before that me getting the network this year took me to to Defcon for free. I think it was a great gift and a blessing and I got to leverage and talk to so many different cyber security professionals to also just grow my network and also just talk and talk to folks trying to break into cyber or even transition into cyber security to kind
of let them share their story with me or their journey to kind of get into this this next role. And I am definitely ahead of time. So, I will open up the floor to any questions as a short AMA. Ask me anything. So, what's an AMA, Andy? AMA is a no holds bar. You can ask me what my favorite color is, and as long as it's ethical, I will give you an answer. Um, does anyone have any questions in the crowd? >> Oh, good. Perfect hands. Go ahead.
So the question was what was the hardest thing I found transitioning from my law enforcement role to cyber. Uh the time commitment honestly I realized that when I decided it took me a year to do my transition into cyber. I know some folks think like oh I can go to this boot camp or I can go through a workshop and it says in six months I'll have my next job in cyber security making six figures. There's a 1% chance it happens. But I realized that there was such a knowledge gap that I was walking away from because I was with law enforcement for seven years before I I moved into the position. So I'm like,
okay, well, I need a knowledge foundation base. So I went back to school for my masters in cyber security. And as for my law enforcement folks, there's a joke saying that the gateway drug into drugs use is meantas. And so I always joke that the gateway into cyber security is security plus. So I went ahead and got my security plus and that opened up all the acronyms and the trainings and learnings and just like law enforcement or military there are acronyms for days. So learning what all the acronyms meant, why were they important, what processes and how how a website or a system needs to be secured is important was uh was kind of a
difficult piece for me. I I hated school growing up. But I realized when I got older in my years, I'm like, I need to go back to school and really understand this stuff so I can go into this next field and like be the best candidate. Uh, also just doing research in the the free time on my own. My my days were long days. I'd start my day at 6:00. I'd end my day at 11 p.m. and then repeat Monday through Friday. So, a lot of self-taught, a lot of learning, YouTube learning, try hackme to make sure I really solidified and stuck in my foundations and then just applying out. So, hopefully that answers the question.
saw another hand up. >> What's your favorite color? >> My favorite unethical color. >> Oh, man. I've never been asked that question. That's actually a weird question. Uh uh, pink, I guess. I don't know. I don't know. I don't know how to answer that. I won't lie. The question was, what was my most unethical my favorite unethical color? So, I don't know. You stumped me there. Good job. What skill set you learn in law enforcement that you have found different? >> So the question was is what skill set I find being in law enforcement made me stand out different from people in the industry. And I'd say that what I brought to the table when I got my job
with the state of Arizona was and I actually got this comment from my my state was Andy like we love you being here because cops make the best analysts. I'm like, "Well, that's really impressive to say, but you got to give me a little give me an explanation of why." And he's like, "Well, like you're standardized and systematic. You have to explain things to a judge and a jury of 12 that hold everything from a GED to a master's degree depending on who couldn't get out of jury duty that day. And you have to walk through an entire case to prove how and why something happened and why it was bad or malicious." Or switch that around and
maybe you're trying to expune something and show someone why it wasn't malicious. So taking my report writing skills and my kind of analytical mindset of collecting evidence such as a gun at a crime scene would then kind of correlate to now going through logs and finding maybe a malicious traffic that a user went to on their web browser. And taking those skills and kind of getting to mash them together where I'm like I'm really when I finally was able to solve my first kind of incident with my team where we were able to remove some malware inside of a library somewhere in Arizona. I won't tell you where. Uh, I realized cuz imposter syndrome is such a
real thing in this industry and I was there was some days where I didn't realize if I was making the right jump. I was obviously in law enforcement for seven years doing that career change. Some people don't do career changes till 10 12 years or they'll do it earlier. But I was like, should I just be staying a cop? Do I really belong here? But I realized once I got that comment from my my siso, I'm like, okay, this is I belong here. I understand what I'm doing and I just need to kind of continue to grow, ask questions, be willing to train and be take feedback in a positive way. Not every day is a good day. You're
going to miss things. Uh you might take down the DMV's Docu Sign because you blocked it on accident during a fishing email, but but it's okay. You're going to learn from those and you're going to bounce back and you're going to be a better analyst from it or whatever rule you kind of get into. I saw two other hands. Anyone else? >> Based on your experience, would you say there's any benefit towards trying to go into public versus private sectors? >> So the question was is with my if I'm saying this correctly, my experience of going from public to private sector, is it a pro or con to start with public or private sector first to public?
with differences between public sectors and private sectors and how they operate. Is there one that is there? >> I I'll answer what I think you're trying to ask and hopefully this will answer it for you. So, so if I had to go back in time and talk to Andy of how we should break into cyber security, I would honestly probably tell him to do the same thing I did and I'd look for my state and local government or my cities. Now, the reason why I say that is is because with private and government sectors, one positions were probably going to be available. But the reason why is because they don't really pay the big bucks. So, when I took my first job
leaving law enforcement into the state, I took a pay cut, but I knew that's what I wanted to do. And I knew by me getting into this position, I can level up and get myself into a better position from cyber security. And fighting people on the south side of Phoenix is kind of tiring and hurts your back. So it was just a little bit easier not to have to fight people and just fight the keyboard. And I was only at the state of Arizona for nine months. So I was there for six months as a senior information security analyst. After six months of working my butt off, learning the systems, understanding procedures, being a really go-getter initiator, they
promoted me to a senior engineer. And I tell this story, and my boss knows I tell this story because I he is an amazing boss. Adam Pena, he's our director at MCC in Arizona. On our Christmas party, I got head-h hunted to Wells Fargo to go join their cyber security team, which came with a title, a slight title increase and a very much larger pay increase. And I remember I told Adam, "Hey man, I need to talk to you real quick. Can I can I pull you aside?" He's like, "Yeah, man. Give me one second." And he walks away and comes back, hands me an envelope. He's like, "Yeah, I open the letter real quick."
Gave me a Christmas card saying, "Hey, so glad you're on the team. Uh, so excited to see the next year of what happens." I'm like, "Oh man, you should you should hold on to this card real quick." And uh I pretty much explain to him like, "Hey, I've I'm actually contemplating a new job with Wells Fargo." And I tell the story, and maybe this will make sense to you, but I I tell the story because then Adam then explained to me, he's like, "You need to take the job." And I'm like, "Well, I feel bad, Adam, because I'm leaving this team. I haven't even been here a year." And you'll know you're in a good place
with great management because any good manager rather than holding you back is going to promote you and push you forward. He's like, "Andy, all this shows me is that that our sock is pro is making such great cyber security engineers and analysts that I'm making you so competitive that someone else wants to wants you wants to take you away from my team." And I really appreciated that because I mean I'm I'm married. I have a wife and two kids. I got to make sure I'm providing for my family. And he he he kind of told me like, "Yeah, man. You need you need to take the position." And I left in great standings with the state. I still talk
to all my co-workers and everything there as well. But with current day and age of trying to break into the public se the private sector, I'm sorry, the public sector. So like your banks, Wells Fargo, Microsoft, Google, it is such a competitive world because one, the salaries are insanely high. The requirements are listed to find unicorns and if you find one, let me know, capture it. We need to study it, duplicate it, and share it to the world. But going private sector into your local, state, and governments is going to one get you a lot more experience, I think, with getting into all the systems and the knowledge and even communication skills. And then from there, that's
where you can grow in and go out to the the private sector and make the big bucks like everyone kind of wants to do when they're breaking into cyber security. >> All right, that drill got a little bit more time, but uh any other questions? I see you in the back. Go ahead. >> What made you sure you wanted to get cyber security? >> That's a good question. So, the question was is what really made sure that I wanted to get into cyber security? And if everyone remembers uh the years where we had the huge incident with George Floyd and was a horrible thing that happened, but law enforcement had such a negative target on their back. Anyone
with anyone with a badge or anyone that was with law enforcement, uh you could have been the best cop in the world, cop of the year, you could have saved 10,000 babies from a burning hospital and you were still just looked at as being worthless. And it put a lot a lot of targets on people's backs in law enforcement. And obviously being married with two kids and I my my wife's family has folks in law enforcement which I I applaud the job and I still tell anyone trying to get into law enforcement that it is a I would never change the career path I went through. I would still become a cop before getting into cyber
but it was a lot of stress for me and the family and it was getting taxing. I also worked very crazy hours. I was on call 28 days of the month. I was a drug recognition expert and a photonist with the city. So, I was constantly getting called out, going on scenes, and it was kind of just getting to become a lot, and it was just tiring. And I was I've been in the military for 17 years, and I'm part of a cyber protection team. And talking to a lot of my mentors within my unit, they said, "Andy, why don't you break into cyber security, man? You're a great analyst. You're a great threat to
Intel analyst. You be you could be making just as much, if not the same, doing some great work, just writing reports, but it's a lot more safe for you. It's more safe for your family." And when I I went on a deployment to Kuwait working with the 29th ID infantry division doing thread intel with their S2 with their information shop and that's where I got my SEC plus. I was working on my master's degree and when I started interviewing for all the applications I did what anyone kind of did initially when they started. I started tracking all my my failures. I was getting a hundred I did a 100 applications and got 101 rejection letters cuz someone sent it twice. And
uh yeah, you've been there. And initially I was just like okay well maybe this isn't the place for me. And but by networking in my my mentors, they introduced me to my team at the time at the state, they got me my initial interview to the state of Arizona. And after kind of explaining the same question of like, hey, why do you want to leave law enforcement and break into cyber, I explained my passion. I explained what I was doing on my own private time of building my own VMs, going through training on my own dime, paid for my own comps, I was paying for my own certifications. Uh that showed that drive and initial
push of what I really wanted to do. And like I'm a gamer, I'm a nerd, I already like doing cyber stuff anyway. So like it kind of just fit the bill. But um hopefully that answers your question. But yeah, it was just it was I think it was the right career change and move to do. So >> uh hand in the back.
>> What was something that was I thought would be difficult that then once I got into the field was not as difficult as I thought. Honestly, working cases. Like when I got my first job as a sock analyst, I'm like, man, this is gonna be so complex. I'm gonna be so confused. And once I got into the tools and I learned the tools, so I'll just give some examples of tools, not saying they're for any specific organization, but like so like for an EDR going through CrowdStrike and navigating through CrowdStrike to pull logs or to remote onto a remoting onto a host to pull a file to drop it into a a sandbox to deploy it to see what happens
when I run it and then just writing a synopsis of what I saw or going through policies and procedures for GRC for SOCK 2 compliance of like, hey, do we have this log ingestion implemented? If so, how and why? or how is it h why is this and how is this happening? Um I realized it was just doing more research and kind of making sure I knew how and what I was doing. I thought there'd be such a almost like learning a new language like going to Germany or Mexico the first time and not understand the language and you're just walking around like oh this is so cool but then you go try to order
like a soda and they give you a water. I'm like uh okay cool this will work I guess. So I think it's changed a little bit now because as many talks have said like AI is becoming such a big thing. It's being integrated into a lot of workspaces. It's I think helping out with a lot of analysts getting into the role. But I would definitely I argue the fact that I don't think AI is yet is at the point yet where it's going to take over some entry-level positions such as a sock because I can even talk at the federal level like we're not fully implementing AI to write reports. Like that still takes an analyst hands on
keyboard, eyes on screen to proofread, uh review, pull logs and kind of get those into an investigation. So great question. So with that, that's a little bit or any more questions, I guess, before I count. I got like five more minutes. Any more questions? >> What would you tell somebody who's considering? >> You need to just do it. And I that's such a play from Shilabuff. But if you're not sure, the one thing that I think the biggest issue that folks have when it comes into breaking into cyber, they don't know what they want to do. And they think there's only the three roles. pen tester, red team hacker, blue teamer or IT help desk. There's so many
different roles and things you can do to get into cyber security. You really need to find what your passion is. So whether that's app development, whether that's procurement, whether that's sales, whether that's project management, whether that's cyber marketing, uh there's so many different things that you'd be surprised on. Maybe your passion is building websites. Well, MSSPs and startups and nonprofits need to build websites, but keep in mind, we also need to make sure those websites are safe. Are you building the website safely? Are you using like bad code, bad practices where someone can go in there and deface it? So, there's a lot of different ways I think folks can break into cyber. And their journey is all
different. I've talked to folks, like I said, that are teachers, uh, preachers, cops, librarians that get into the get into cyber security and they love it. And burnout's a real thing. And you'll talk to folks that get extremely tired and they've been in cyber for 5, 10 years, but they look like they've been in it for 25. And it's there's long days out of it, but I think it's very beneficial and it's just finding what you enjoy and what you're passionate about. Great question. All right, everybody. Well, these are all my socials. Uh, if you go to the YouTube, there's a link tree pretty much that has everything. Uh, the YouTube was made off of Dare, so just bear with me
on the name, but it's Ginger Hacker. It's this logo right here. Um, I do an awesome series called Breaking into Cyber where I talk to everyone across the industry from interns to juniors and seniors in college of why they decided to go into cyber security to IT help desk to engineers, sled, GMs, state sisos, uh, you name it, I want to talk to them because everyone has a different journey of how they got here. And, uh, I'm excited to see how you all, if you're trying to break into cyber start your journey or get in. Um, and if you're currently on your journey, hopefully it's been a smooth one. And if you're transitioning to something else, I hope
it's just as smooth. And thank you guys so much for your time. And I will see you guys. I'll see if anyone has any questions. I'll be outside the room to take any. Thanks so much. [Applause]