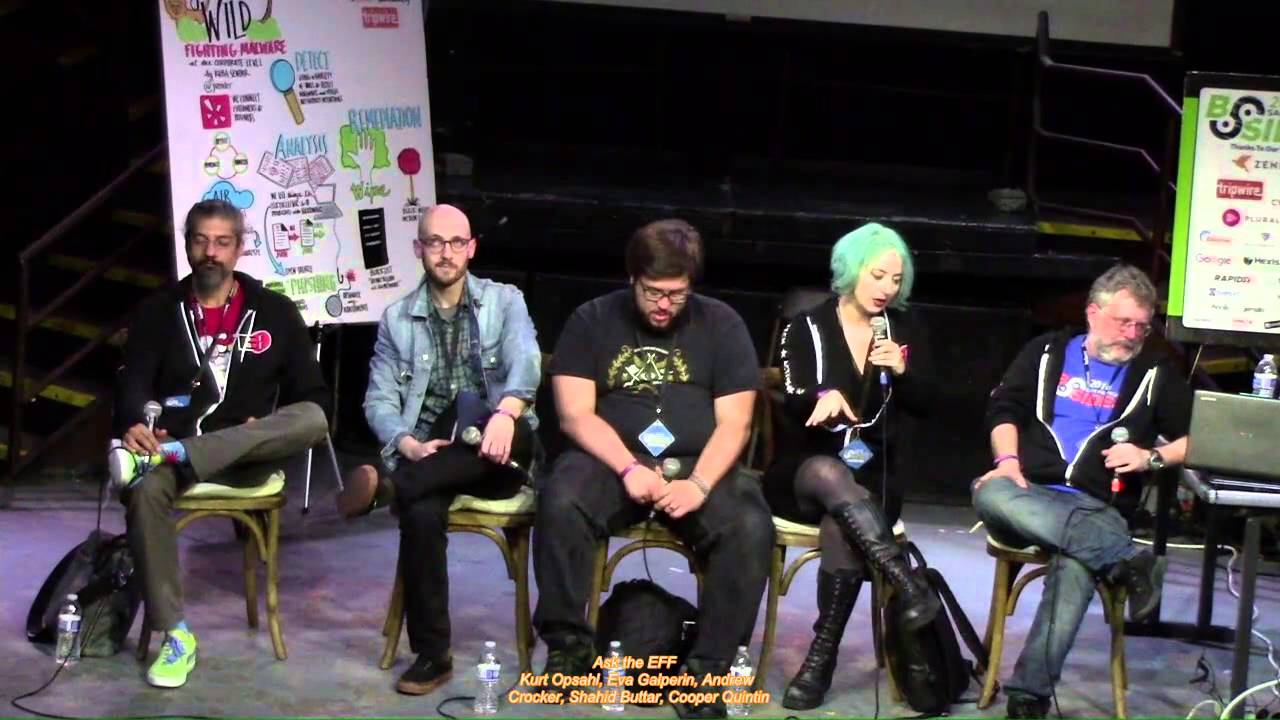
Ask the EFF

Show original YouTube description
Show transcript [en]
[Applause] all right welcome to the last talk of the day this is the EMF panel so as a recovering attorney myself it is my immense pleasure to bring to you Nate Kurt Jenni Jamie and Erika from the EFS
alright hello everybody great to be back here at DISA at San Francisco we've been here for many years been enjoying it all the time a lovely to to work with this community my name is Kurt Opsahl I'm the deputy executive director and general counsel with the Electronic Frontier Foundation well and thank you I take it many of you already know what what EF f is and we appreciate that for for the for the guy you know somebody out there who doesn't we are a non-profit civil liberties organization dedicated to defending your rights online and a particular for this community we work on the coders Rights Project where we help security researchers understand about the legal
issues surrounding their research and surrounding when they want to talk about their research and try and make sure that people can do the research they need to do and can talk about the results that they find so this is the the ask the e FF panel so this is where mostly it's going to be your questions after we give some brief introductions we're going to be looking for audience questions and I believe we'll have people line up over here by the corner of the stage and then Nate will use that mic to allow people to to ask their questions one one quick word is that while we do provide legal advice to people this is not the time for that if
you have a legal question about your personal circumstances that should be done in a confidential communication not on stage in front of a lot of people just in case there there are some things that you're going to want to remain confidential so so with that word of warning let me turn it will go down the line here with just a minute or two talking about the things that we have been up to over the last year and we'll turn to your questions so Erica
hi I am Erica Portnoy and I am an engineer on cert bot witches ef-s let's encrypt client let's encrypt is a free automated certificate authority that is bringing encryption to the web it's been a pretty exciting time for let's encrypt these last few months in September when I started working on surf up we had roughly eight million websites that we served depending how you count and lest I checked a couple days ago we were at twenty five million so it's exciting to see the impact that we've had and there's also of course tons of work to be done I personally work on the client where we're working on making sure that for the long tail of use cases we can
meet your needs and keep hitting all those tough to get configurations and also make sure that it's as stable as it as it can be for the people who already using it and we're pushing towards our 1.0 release [Applause] I'm Jenny Gebhardt I'm a researcher on EFS activism team my broad area of focus is researching consumer privacy and security looking a lot at different tech company policies and practices I also spend a lot of time working on open access working on zero-rating and net neutrality and working on censorship in her present States hello I'm Jamie Williams I am a lawyer on ESF civil liberties team so I focus mostly on free speech and privacy issues
I also do a lot involving the Computer Fraud and Abuse Act and state computer crime statutes we got a really good ruling out of Oregon last year on the state computer crime statute so that was good and then what else I've been doing some work on compelled decryption cases [Music] yeah yeah that's it I'm Nate Cardozo I'm a senior staff attorney on EFS digital civil liberties team I work on the coders Rights Project defending people like you against people like I work on our crypto policy I work on our who has your back report when we evaluate what companies are doing to protect users from the government I am suing the government of Ethiopia for
wiretapping an American that's a fun one I had an Ethiopian government spy up in my face taking pictures of me a week before last and I gave him my business card which is if you know me a serious insult if you so ask me for your business card later and that's the sort of stuff I do and on that note I'm gonna have the microphone I can have this microphone over here and we will answer any of the questions that you could possibly ask and if we don't know the answer we will tell you that we don't know the answer and refer it to one of our colleagues and on that note yeah let's let's get to your your questions
thank you so I am a director of technology for a school district here in the Bay Area and I spend a lot of time looking at fun things like SEPA and Coppa and FERPA and etc and I have concerns about what is going on with policy in schools with regards to it seems like the actual legal policy is more about like oh don't the babies see that as opposed to let's actually protect them from things like teachers being lacks with data etc and I'm wondering if you have any insights into where education policy is going with regards to privacy student privacy data privacy etc and what is someone in the education space should be doing to
try to advocate for my students great question thanks for that one of the big things are working on right now is a student privacy initiative and we're looking at having kind of a more in-depth white paper coming out relatively soon but as far as what people in the education space should be doing it's hard to give one-size-fits-all advice I think one of the things we're discovering in our research we did a survey of kind of a thousand people and change in student privacy space parents students teachers administrators I think like 600 different apps and services were reported to us it's like things in use at my school and that's 600 privacy policies or lack thereof we discovered
so it's hard to rely on the policies kind of privacy by policy I'll say not even as advice but one thing that we're seeing some sysadmin do and some administrators and teachers do is try as much as they can to rely on very like local privacy by practice like you know can we crank down the privacy settings on these Chromebooks or on the apps we're using can we find allies like librarians are kind of like the privacy ninjas in your schooling community and can we talk to people to get contract negotiations going to get people really looking at privacy policies in terms of service yeah I think Nate do you have anything to add yeah so one of the
things that we have and as part of our student privacy initiative is a set of guides for students parents and school administrators on how to lock down their settings only for one product for Google Apps for Education which is now called G suite for education I don't know why they change that name so we have we have a guide on iff taught org slash student privacy and also if I want if you see any terrible policies in your schools and your kid like your kids you can reach out to us we have helped parents talk to schools too and we've actually had progress the one policy we were working with in Tennessee had terrible policy on
1st and 4th Amendment issues and we got a little progress and getting them to make it better so yeah info at iff org and we're also happy to refer you to local attorneys in your district wherever that district happens to be hi everybody I just want to say first off thank you very much for keeping my dumb ass out of jail I'm a security researcher so keep doing that second of all um recently the EF F put out a notification about we should upgrade our threat model given the new administration coming in and one of the big things I think of in that is the idea of secure communication so how do I communicate details of different people
given the fact that there might be people trying to listen that have a lot of resources so given the recent issues with some of the major clients such a signal is what does the e FF recommend that I use to make sure that my communication is safe even if maybe even not from nation state but very powerful people so you mentioned recent problems with signal I'm not sure I know which ones via the whole idea that signal basically has a dependency on Google cloud services and that possibly leading to some okay so the nice thing about end-to-end encryption is that even if it has a reliance you still only get availability that you lose switches yeah
okay better than other things our cliched answer is you signal you store but I bet obviously isn't necessarily going to meet all of your specific needs so if you have specific ones I would have number one always say go to SSD EFS org that's our surveillance self-defense guide which has things for every possibility for messaging services you probably like end-to-end encryption is it does the trick it's what you want there the math will still work no matter what's going on underneath this is the ASCII FF panel come to me on this side of the stage if you need to ask a question right now there is no waiting at the SK FF panel I'll talk a little bit more about the
signal threat model so depending on whether your Apple or Android Google or Apple may know a little bit about how you use signal but they don't necessarily know who you're talking to and when they know when you're receiving a message and maybe from whom they might not know when you're sending it and they definitely they probably know to whom but anyway it's not the same threat it's a it's it's a lot less information that Google and Apple have if you're using signal than if you're using SMS or iMessage yeah I am so I'm not from the US I'm on a green car thing I'm very afraid of what we have now with the fact that when I cross the border I what
we're hearing now is that we have to give our phones but also give our passwords which to me sounds mmm it's not legal to do but I have no idea and that's why I first of all up really appreciate what you guys do we appreciate that you guys do this this panel and basically we want to know like I could understand that they can take my phone but did I force me to give them my credential it sounds really crazy so where are we are is the legal is there something that I can do is this really something that is not legal but I don't care you just don't coming if you don't like it because that really puts me in
an impossible situation right I will my career is here my life is here and I don't want to give my credentials yeah I think thank you for that I mean that this is this is something that we're looking at very closely you've been seeing more and more reports of people being asked to turn over their devices and their passwords at the border and it is pretty challenging I mean one of the things that's the most challenging about it is that for those who are here on a visa that they can be placed in the situation where they're asked for consent to turn this over and they can refuse to give that consent but they might not be allowed in the country
as a result and that puts a lot of pressure on on people and I till till recently what a differentiation between legal permanent residents green card holders and and visa holders but we have seen that the current administration is sort of moving the category of legal permanent residents closer to visa holders as opposed to closer to two citizenships so I'm I think that that is very troubling but it may in fact be happening what we have done at least right now is ask people to to come to us with their stories if this happens to them if you know someone who had this happen to them when they came to order please have them contact us info at EF f
dot org because we're trying to turn some of these anecdotal stories that we've been seeing on social media into a more concrete story as having direct communications of people and basically to see if there's something that we can do about this this situation for someone who does have a right to come back into the into the country we don't think that that can be conditioned turning over your your social media passwords but also keep in mind that if you want to stand up for that right at the border you may be hanging out at the border for some time so if you want to do that you probably should if you're considering doing that have a lawyer that you can
contact before you're hitting the border have them know when you're expected and be sort of prepared to deal with that you know there are there are other things that you might you might do you can you cannot have your you turn your phone off delete some apps on it before you cross the the border though they may notice that those are are deleted and that independently could cause your trouble at the border Nate did you want to add something yeah so there's a couple of things you can do as a non-citizen when you're coming back into the United States the biggest one is to have something called a g28 form already signed by you and your attorney we've
heard a lot of things that the Trump administration is preventing lawyers from seeing people in detention that only happens when they don't have a g28 already signed so if you have that pre executed when you're coming back into the country that it may well save you a lot of trouble for citizens for US citizens who are coming back into the United States there are two rules of thumb that you need to remember number one they cannot deny you entry . number two they can take your stuff and there's not much you can do about it you can get it back later probably but if they're if if they give you the choice between if they say enter your password right now
or you can't come into the country they are bluffing but when they say we're gonna take your stuff unless you enter your password they are not bluffing so do that calculus I just want to add we also just this is like brand-new we created a special email address for border story's borders a tff org so if you or anyone you know has heard encounter some searches at the border let us know and also to get that g28 form it's available online you can just do a search for GT 28 form G dash 28 and you should be able to find that right right quick yeah so the g28 form is a power of attorney form it says this is my
attorney for immigration purposes only it registers that attorney or it allows that attorney to represent that he or she represents you to the CBP or ice when you're coming back into the states all right thank you I think for this audience in particular some technical and legal advice has been flying around online I know wired released kind of a guide recently and just like a word of caution is we're all kind of learning more about this threat model vacuum we kind of face at the border there's a lot of technical advice that's really cool and really clever in high-speed and sounds really fun to implement but it could also be terrible legal advice like there's really cool stuff you could do
to obscure things on your device or like hide different environments from CBP but it can also land you into a lot of legal and kind of practical hot water so just kind of watch out for that as there's more more commentary on this could I just wanted to first of all think you guys are doing a great job you've put out a pretty good threat model guide online could you give us two things the average employee living in the United States potentially foreigner could do with their iPhone to you know improve their security model and prove this of privacy after you I do you mean like harden your settings on your iPhone that kind of thing yes I
just everyone sitting here today's what could we do like from the settings or always make sure you go in via VPN or you know do you go into your settings and stop - you're taking what's the two things everyone here could do today [Applause] there's many things that two big ones that immediately come to mind first of all regardless of your device do not have the fingerprint unlock thing don't do that that's not cool it seems cool it's not and one reason is that law enforcement or Border Patrol they can compel you to put your thumb on something like they can tell you to take a fingerprint they cannot can tell you to put in a password so get rid of the
fingerprint unlock thing have a code longer the better the second thing which applies I guess two things you might do on your iPhone or on any device two-factor authentication enable it for your various accounts using whatever makes the most sense for you often that's not that occator apps like Google Authenticator it could be SMS it could be a hardware token like you Baqi those are the first two things that come to my mind at least also remember that you can use end-to-end encryption all you want but if you're doing an unencrypted cloud backup then your antenna encryption is essentially useless whatsapp for instance prompts you repeatedly to backup your texts to Google or Apple cloud those backups are accessible to
the provider and to the government even if the message is in flight or not so think about your threat model if you're actually using sensitive communications if you actually need end to end encryption for the love of God turn off the cloud backup and tell your friends to turn them off too hi I was just wondering do you guys have any advice for Municipal Corporation's that provide Internet access or fiber optic services so like a municipal light plant where I come from different towns can start in ISP or they can sell fiber optic services you have any policies are resources to make sure that we're making this as open and Farish the public as possible I think the answer is yes none
of us here work on municipal Wi-Fi issues not for a while but there's something that we have definitely been looking at I mean there is a little bit of an irony is to say that the the answer is trying to get you better communications is to work with a government organization but municipalities are generally on the more popular responsive end of government organizations and have done in many cities have ones which are more privacy protective and also high speed and free or low cost versus the the other environments that are out there there's been a fair amount of pressure from some of the larger service providers to try and stop municipalities from competing with them and in some places they've
actually passed laws in which they say the municipalities of that state or jurisdiction can't offer something competitive with the existing commercial entities but nevertheless this is becoming more more of a thing I think the key the key issues are making sure that you are not sacrificing a lot of your privacy and autonomy by using a municipal service so that it needs to be transparent about what its practices are and that you can be using it without having additional tracking of what you're doing held by that government agency but by and large municipalities have been pretty cool with that though occasionally some have fallen victim to a provider that says we will we will do this for your town but
only if we get to track everybody in your town and what they're doing online and send them based on it so something worth looking at to see if that's right for your community okay no waiting if you want to ask a question come down on these on your left I have another boarding border-crossing question so as a rule I turn off all my devices crossing the border and I've noticed that the TSA if you're selected for like the four s as the special screening the TSA asks you to turn on your laptop to verify that it turns on and my question is is this a situation where I should have served my rights what are my rights in that
situation just don't do it if they ask you to turn on the device turn it on if they ask you to unlock a device if you're a US citizen hell no don't do it should be enough to show the unlock screen before you put the password to show that it's not actually a bomb but it is a functioning computer and so they shouldn't have to ask you to unlock it if if it's just a question of unlocking it sometimes people will have a guest account on their computer so you can login with the guest account to show that it's a viable you know functioning computer without giving access to the rest of your your machine but really all
they should be able to look at or should be looking at is that it is a computer and not something fast creating as a computer and you can show that by turning it on enough to get to the unlock screen so to my knowledge no court has ever addressed that question and like I actually read order search cases pretty regularly so that is actually an unanswered question at law so the answer we gave you is what we think the law probably will be if it is ever addressed by a court just turn it back off after great just turn it back off after any well owe you a question great come on up so as much
as I may love signal in which that everybody would switch over to it it seems like that's a really tall order for the world at large what is the F F doing or what can we do to try to encourage the service providers that already have well-established and adopted messaging platforms to get on to end-to-end encryption and other good practices so we have robust dialogues with a number of companies we have a call coming up next week with whatsapp for instance whatsapp does to end in an end-to-end encryption but they have some significant issues with the way they implemented that not in terms of the protocol but in terms of other things so we think that end-to-end encryption
should be ubiquitous iMessage what's a facebook messenger and alo did it in a way that we don't think is good at all but they're at least thinking about starting it I think on the topic of owl and facebook Messenger like that's where I mean facebook Messenger lease where a lot of people already are and it doesn't demand a lot of additional adoption the issue that we've had is that it's kind of optional encrypted and there's two reasons of that is a problem like I think the good thing that Nate covered is like there's thinking about it there are engineers there who are pushing this forward and that is I think a victory for kind of thinking about encryption
and making it more available to users the two big problems are one that it's confusing neither Facebook nor Google's a low call it and an encryption they call it like incognito or secret mode and then in the UI itself it's very easy to make a mistake to send something not intend encrypted that you meant to send in the darker encrypted mode so first it's confusing and users can make mistakes second it teaches although it may be increases awareness and adoption we're worried that it will teach the wrong lessons about encryption it'll teach you like Oh only use intend encryption when you want to do seek shady things and essentially raise a red flag in your communications like hey you
secret shady things right here so I think it's in some ways it's a step forward in some ways it's two steps back but yes the robust dialogues continue on that if you would like to make your voice heard to a particular messaging app that you regularly use a way to get people's attention is to go into an app store and leave a one-star review because once you get enough one-star reviews they become somebody's job to see why the ratings are falling and when they go and read the comments along with it make sure don't just like leave a one-star review leave a comment saying I would give this a higher rating but I have secure messaging needs and it is
not meeting my needs so I'm forced to give this a one-star review there is a human being whose job it is to read those reviews and they will see that okay thank you for your service this again is a border crossing question what about if the person coming back to the United States is an American citizen but they're underage as far as the right to print to not disclose their password on mobile devices the age of someone coming into the country shouldn't matter for these purposes the government cannot compel a US citizen to disclose their password whether there are over or under 18 absent some unusual circumstances that we were not going to get into here
but the eighth age shouldn't matter I mean to do there the possibility that their parents could consent on their behalf but hopefully their parents would have their their kids back on this and not give them up this doesn't relate to at the border but we actually last year filed an amicus brief with the ACLU in a case involving juveniles being four you force your kids on probation being forced to give over their social media passwords as a condition of probation which is insane so we hear interested check out check out our website or our the post is there and I mean and we argue it's basically the same as a wiretap that invasive obviously the
technical things are different but yeah what about creating a social media account the new one then the password is fu five times want me to repeat that password sure why not one of the things that happened I think it was about a year ago with Apple and the iPhone obligation to write software to crack I phones it's something that has gone sort of by the wayside we haven't I feel like this hasn't been addressed as far as I know so yeah what do you think the motivation was for them even bringing that up if they felt that they had kits to break out anyway and so two parts of the question is what was their motivation for that and are you
guys still responding to it or you consider it an issue that will just come up naturally in the future and rootkits for breaking phones or kits we could just plug in a phone and scrape all the data off it I mean that's under Fourth Amendment isn't it I mean why are we even having a debate that it seems like they could do that without yeah so your first question was white why did they bring that case if they could unlock the they could hack into the phone yeah okay so this comes up a lot it was a terrorism case they thought it was probably gonna be easy for them to get like good law allow forcing Apple to
unlock the phone and set great precedent that they could use in cases across the board I mean that's why they picked a terrorism case that's why a lot of bad law comes from terrorism and child pornography cases we work on a lot of those cases so trying to hold the Constitution for everybody in those cases where the judges are gonna be less sympathetic but yeah the public outcry was amazing in that case they didn't win they they backed away but I think it's not gone we're definitely gonna keep fighting this I think that the new administration has been busy with other things but there's definitely been terrible like what sessions has called for backdoors are he endorsed Doris
backdoors yeah so are our new attorney general Jefferson Beauregard sessions the third has called explicitly for backdoors in technology luckily the the House Judiciary Committee has the Republican House Judiciary Committee has rejected legislate backdoors so that's awesome Thank You representative good lad oh but who knows what's gonna happen in the next Oh God four years pay attention we need a fight ahead and just to add a little bit to it to Jamie's point there is at the same time as the Apple iPhone case there was another case involving an Apple iPhone the the there was a San Bernardino case involving terrorism and there's one out in Brooklyn that was involving a meth dealer and so that the
meth dealer case came first it was ongoing when they brought the San Bernardino case and I think they would have they preferred to have that issue decided when looking at something with other sort of higher stakes then then a local Brooklyn meth dealer but however they lost the the the meth dealer case that the judge ruled against them but they dropped the appeal of that and they they dropped the Santa Marino case so there is no binding nationwide precedent one way or the other so we're gonna be back there and dealing with this question I mean there's the question of backdoors as a good idea and there's sort of a separate but related question can you force coders to write code that
they don't want to write they don't believe in can you tell them what to say and we think this actually hits on some very important First Amendment issues code is speech and compelled speech is just as challenging as telling people what they can't say so if you go to a coder and say you got to rewrite your code to do something which is against your principles that independently is a problem but this issue will definitely come up again and it'll just be just be a matter of time thank you for your work we all appreciate it I have a question specifically about California in the sacrament so the legislature is working on approving speed cameras and
potential surveillance use and from talking to the san francisco MTA staff they've been working with you your group and a seal you among other stakeholders on what the privacy implications on that are is hoping you could speak to that a little bit I think that's probably our colleagues Jen and Dave neither of whom are here right now so we are monitoring those sorts of issues but none of the five of us know anything about it sorry we have a legislative team who focuses their efforts in Sacramento and in DC but yeah so obviously there's just like the general privacy implications there Jen our colleague works on license plate data and it's gonna be arguing that case soon a case challenging
collection oh and lack of transparency around those records okay I think this is probably our last question last question so are you checking on that a little bit so most of us here have a representative two senators a bunch of state people do you have some resource we can go to to tell them well first of all to know what questions even ask to have a policy on and second of all to sort of have a form letter to like say yeah we don't like backdoors etc is that is there a resource pelvis yes yeah exits in it right [Music] like I seriously like were you asking what questions tasks yeah what do you do
yeah so what action AFF torge act act act act the verb act AFF Torg that is where you can go for kind of depending on the campaign to email your representative to call them to tweet at them app you put in what your address or zip code it tells you exactly where you're gonna go there are templates there are forms that we make it as easy as possible and similarly for AFF issues and if you sign up on our mailing list we will email blasts when one of these actions is really urgent so like when sopa/pipa happened it was because 200,000 of you call to your representatives that SOPA PIPA didn't happen we also have an app which you can
also use to track those action opportunities and Android only so our uff Action Center app is Android only because the Apple App Store terms purport to limit what developers can say publicly any FF as a free speech organization would never agree to those terms so we don't have an iPhone app all right [Applause] thank you thank you everybody for coming we will be ending our our house the EMF panel but we will be around so if you want to find us the booth is on the second floor in the back corner there if you want to stop by and maybe become a member get some swag and you can also just find us around here and ask any
other questions you might have but the meantime thank you very much enjoy the rest of your b-sides and we'll see you around [Applause] so that concludes our last presentation today on behalf of b-sides and Fitbit I'm going to present each one of these freedom fighters with a brand-new Fitbit I also have two two announcements to make starting now nextdoor at buzz works is hacker jeopardy also hacker one would like to invite everyone to hack the bar tab up here at CTF thank you and have a good evening
[Music] [Applause]