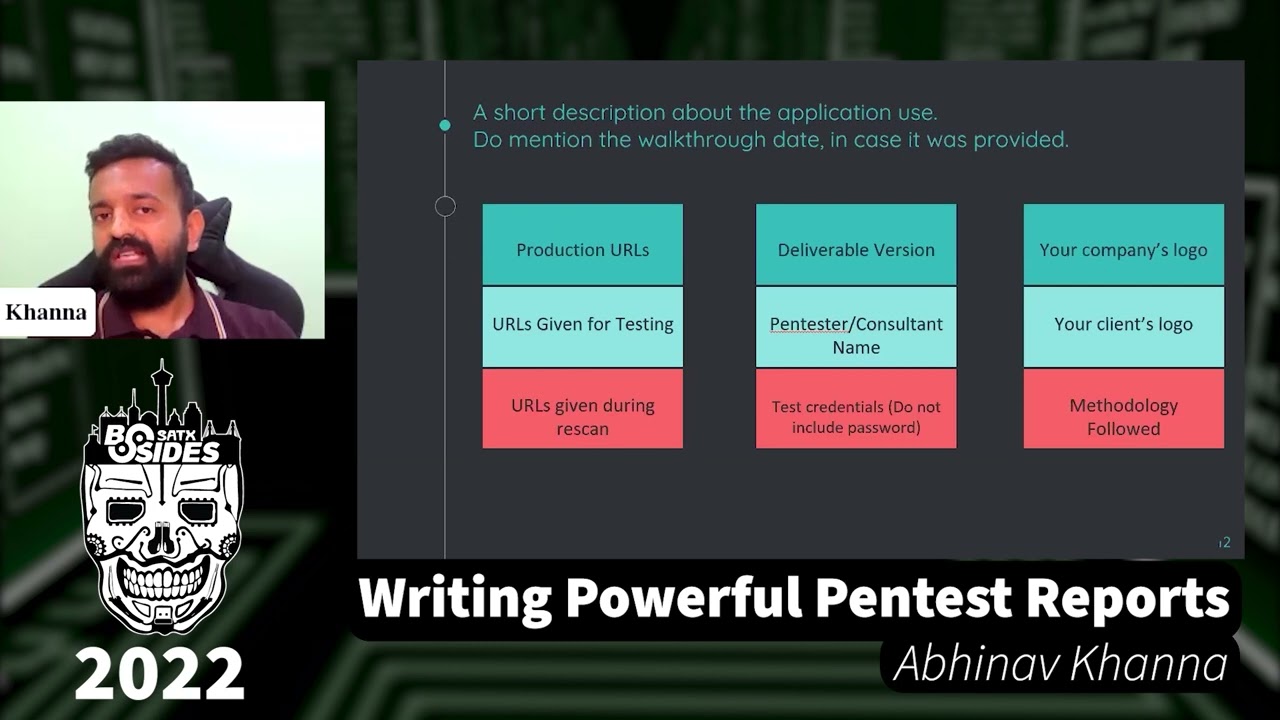
API Security From The Lens Of An AppSec Engineer by Abhinav Khanna
Show transcript [en]
thank you everyone so today i'll be talking about api security from the lens of an app second junior and uh you know just a little introduction about myself uh my name is abhinav and i'm currently working as an app second engineer for clarinet cyber security and i'm conducting my own security researches i'm into bug bounties and all those stuff uh okay before we get started just a little disclaimer that you know i'm going to talk about a few tools that we can use for api security but i'm not endorsing there are other tools available in the market i just uh i'll be talking about the tools that i know of okay so why is it important apis are used everywhere you see iot systems smart devices alexa and all those things api is everywhere and we need to take care that the apis we're using are well protected so our data breaches a minimum so that is something that we need to take care of when we talk about securing apis there are three things that we need to take care of knowing our data what data are we trying to protect is it credit card information or any other personal information the social security numbers things like that knowing our customers if it's a banking if it's a banking api so we need to know that okay the credit card informations the account numbers the balance and all those things we need to take care that they are well protected and you know no one is uh trying to get into or seeing seeing our personal information the tools there are tons of tools available and as a security guy you need to be you need to be aware that these are the tools that i can use to see what are the bad sides uh of the api okay so ovas has this top 10 list of the a api security and today we'll probably be covering um three of those one is mass assignment the other would be improper asset management and it would be excessive data exposure all right so when we want to start an api security assessment there are some things that we need to take care of one read the documentation that has been provided to us if it is not provided do ask your client or the developer business team whatever it is try to read the documentation and try to understand how the apis are working what is the exact business logic of the api second ask for the api collection which includes the positive response like if it's a get request and you want to know uh what is the data that the application is going to fetch we need the api response we need to know that what are the methods that we can use on the apis third so when we talk about api security assessments we do not uh we should not just stick to uh automatic tools uh the the scanners for for just you know just showing the results we actually need to do the manual assessments because they are going to give us the actual results so let's talk about the first finding which is mass assignment i've written a small line like let's lie and check if it get caught because what happens in mass assignment is that we are actually trying to tell the application that we are we are the admin of the application when in reality we are not and if there is no check the application would say that yes this guy is the admin and let's give him all the access that admin would have let's try to understand with it with this uh story suppose this is a restaurant if someone walks in and he just says that okay hey are you guys serving pets or not and the waiter comes and says yes we have a medium-sized pigs and it's for ten dollars okay now this guy says that okay i'm the owner's friend and he without verifying says that okay that's great you're the owner's friend let's give you the pizza for two dollars so straight away got the discount without any verification that is what happens uh in the mass assignment where we are lying to the application that okay i am this person or i have this discount code and they are not going to verify it they're just going to accept it and give you whatever discounts or the access you want let's just uh would it play sorry for the glitch there's guys so so we were talking about the uh demo of mass assignment all right so if we can see this is a login page and we go to the forget password page we enter the email yep we we have this link we'll open the password reset link that is shared to us and now if we analyze the request there's a parameter that that is going to says it admin false so we we just need to change it to true from false so without verifying the application is going to accept that okay this guy is actually the admin and when we log in with the new password we will have all the access that a normal admin would have so this is what mass assignment can do you're injecting something inside uh you're trying to get the access you're trying to get something for free those things can be accessed using this vulnerability all right so the next one that we're going to talking about is improper assets management now uh just a one liner here you made a very secure new version but did you forget to disable the previous one so for example let's say there's a new api that is called v2 and the entire data there is encrypted well encrypted but the developer forgot to disable the version one which is which has all the details like your credit card number or the cv details uh any other you know relevant personal information there in plain text that is a critical data and that can be used by anyone to access your information now let's understand this again with a story apologies for the pretty bad graphics there but yeah consider this an office and this is the next employee who resigned three months back but did not return his id card it's kind of like the physical talking physical security that you were talking about right so he still has his previous id card and he tries to enter the office the previous office and what you can see is he's able to get inside because that id card was not deactivated it was still activated because he was able to get in he might be able to pull off a lot of things like you know get access to things get data get some papers and all those stuff so that is why uh asset management is important be it physical or be digital they both are important let's just understand this now with a demo cool [Music] no actually we had a glitch so i switched it yep so we had we had the forget password page and we copy the email address all right so we receive a verification code that is 21222 cool so there's a v3 api this that is there in place it says that we are unauthorized to change someone's password and there are four attempts remaining before they block us it's it's uh preventing the brute force attack here so we'll again enter the same code and now instead of v2 we'll try with v uh v3 will try with v2 or v1 again unauthorized but this time it did not tell us that we are going to stop you from brute force attack so from v1 we are going to uh start a brute force brute force attack to get the verification token of the admin to get into the application so we run a python script here for brute forcing and we found out the correct verification code yep we were able to log in so by chaining two attacks in this improper asset management we were able to get inside the application when ideally we should not be able to do so all right so let's talk about the third finding which is excessive data exposure now exp exposing data more than required is is same same as disclosing your secrets to every person you meet and you do not want to do that and you don't do that right so it happens when the apis believe that the the end user is going to filter out the data and would only see what is required to him but in reality if someone sniffs the traffic he'll be able to see a lot more data let's just you know see an example now consider this a request of a dating application i suppose a lot of people use creating applications right this this is a get request which has an id one okay now when we're using the application on the mobile device the only things we see is probably the picture the age name or maybe the city you're from but when we analyze the request using a tool like burp suit we find out that this is your exact address this is your exact mobile number and this is your exact email address those things are not visible from the mobile interface so this can be very critical data if your business is uh you know something like a dating application so we need to take care of this and we need to avoid this kind of data being exposed now let's go through the uh demo okay so this is the application we again go to the forget password pager [Music] when we try to analyze the request we see that yep there's the username email the reset link all of these things are there is anyone a pen tester here doing application security assessments can you tell what is the flaw here i'll show you i'll just i'll just pause the request here and you can find out what is the flaw oops okay okay just give me a minute whoops not visible sorry now when i actually start this uh slideshow uh the crashes yep so i would have to go through it all right so so so that there was a reset uh token link that was going in the response so for example if if i enter your name for example your name is john and i say john gmail.com right so it would give me uh the recent link that is sent to your email right it would be there in response and i can change your password and i can get into the application using uh your credentials so so that is something that needs to be protected and those things should not be there in the response itself i have a few more things but again it's sorry okay so that's what i think i think that would be enough if there are any questions yep i would say just do a black box testing yep for it can be postman this it's a specific tool for apis then burp suit is always there burp suit for uh if you don't want to use postman there's something called as hopscotch you can use that as well if you're talking about xml apis there's a tool called soap soap api we can use that as well for fuzzing this something called as ff double fuf we can use that as well but then again there are a few automated tools but i would generally not recommend it it's more of a manual approach so yep um arjun would be a good tool if you want to do parameter discovery yep for the mass assignment kind of things or access control things arjun is a really good tool yeah that basically depends on the client right if he's trying to give you the documentation or not but yeah yep so uh someone would be you know just blindly starting the application assessment or the apprentice you would get the application intercept and you know start finding bugs my approach would be i would probably create a site map there's this tool called burp suit and it has a feature to create a site map by sitemap sitemap i would be able to figure out uh what are the pages that are there for the admin what are the pages that are there for the normal user so a map would be created and based on that i can try out all the attacks uh probably things like access control right for example if you are an admin and you have access to add users but i don't so i'll see okay if this is the api request that the admin is using and this is the one that i don't have access to i'll try to uh you know use it with my cookies or sessions and see if i can you know uh add an user using my account then there are a few above plugins as well bob suit the tool that i mentioned uh those are pretty handy again for finding a lot of bugs my approach is generally from bottom to top i mean i'll start with finding low issues bugs informational or low so that you know i can get used to the application i can see how it is exactly working and then gradually you know try to find the bugs like sqli or cross-site scripting and things like that no i'd get frustrated when i don't find bugs yeah thank you