2016 - Jerome Smith - From CSV to CMD to qwerty
About this talk
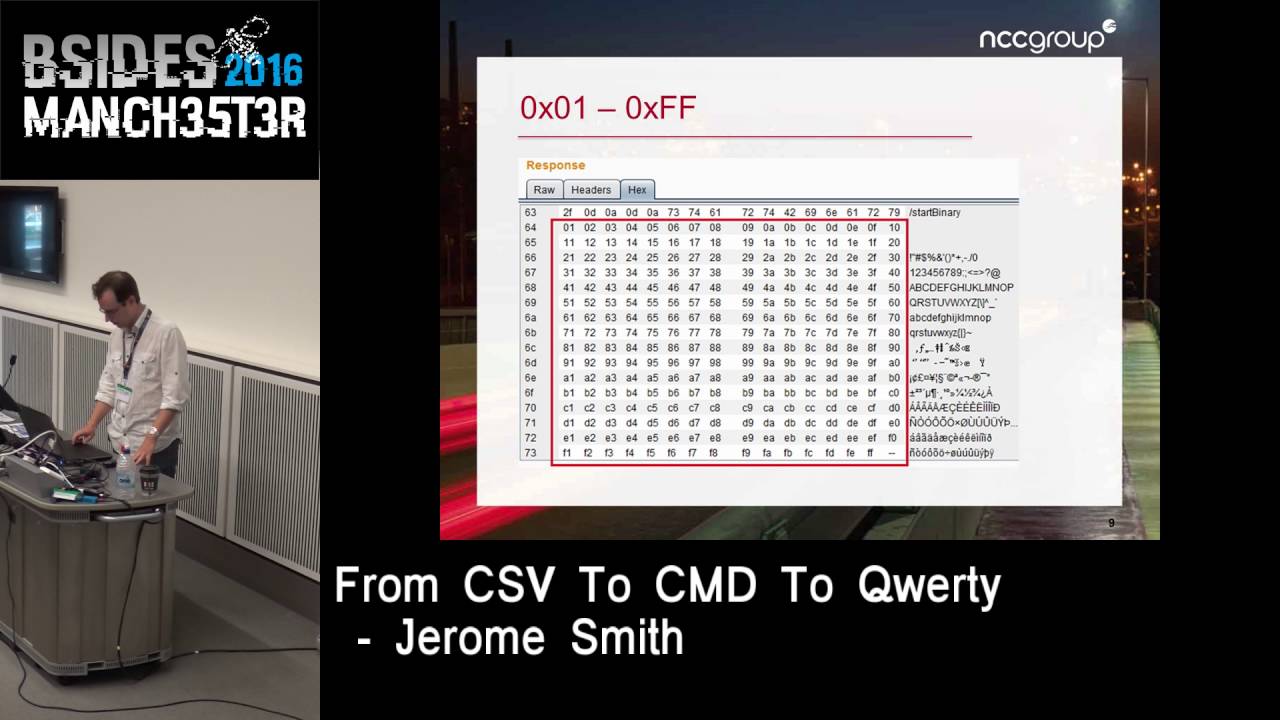
A pentesting war story from the front line…How many times have you seen a web application with an Excel export function? This presentation shows how you’ll more than likely be able to store a command execution payload against the users of the application. From there we’ll progress to an attack on their Windows credentials. With only Wireshark at our disposal, we’ll wrestle with the theory of the NTLMv2 exchange to pull out what we need to attempt a password crack. Swatting the bugs of Hashcat and grappling with the gotchas of John the Ripper, we’ll rejoice in the sight of a clear text password. We’ll finish with a script “catflap”, which amongst other things can generate arbitrary NTLMv2 test cases as a sanity check for Hashcat. Action, adventure and romance. These are things you get in the movies. This is computer security. Let’s not get carried away.





