Pip Vulnerability: Man-in-the-Middle Attack Explained #shorts
Show transcript [en]
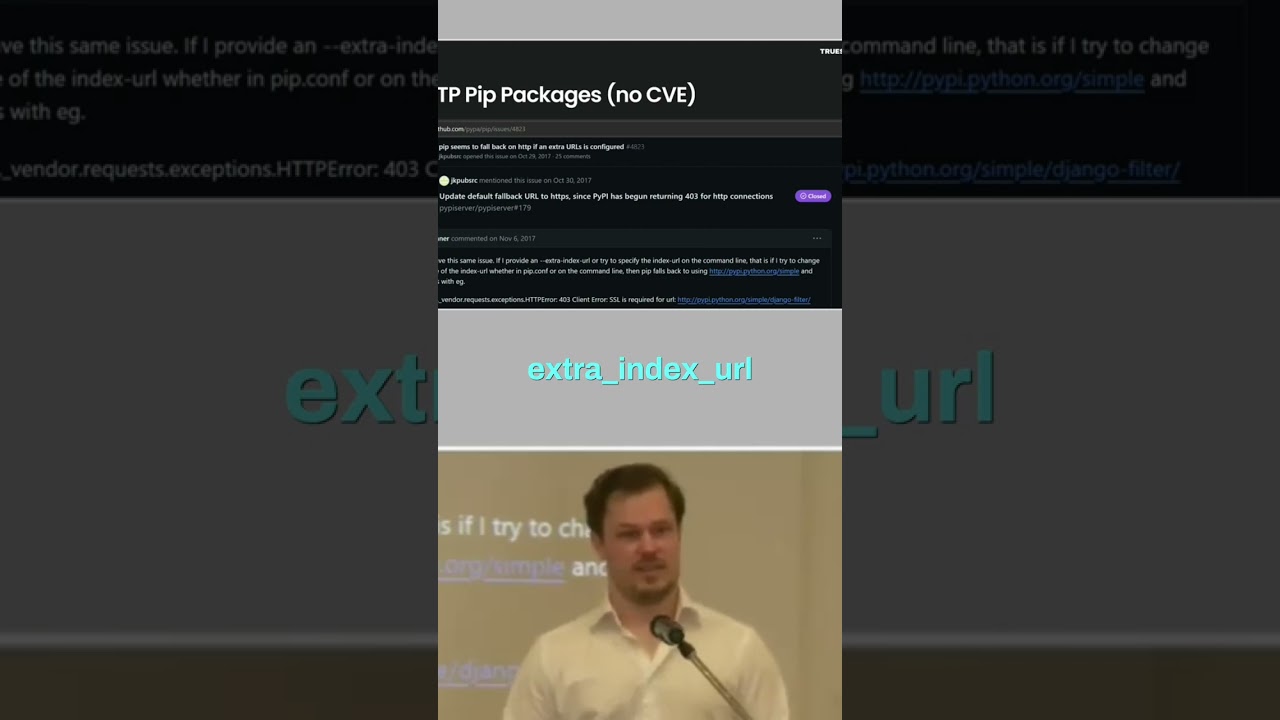
We're going to go through a few different techniques that I've seen to compromise that kind of container. And one of them we saw this weird log with an error in the pip file. So, we see that it downloaded version 9999999, which is a bit weird because this was an internal package for the customer. So, it's like company name internal something and version 999999. And when we looked in the official PyPI repos, we see that someone had registered the same name and put the version 999999. So, apparently, this is a won't fix vulnerability in PyPI because they say that the extra index URL, which you can use to point to an internal PyPI repo, um it's designed to be insecure. It will
check the official repo and it will check the internal repo and it will just get the newest version. So, if you want to be safe, you're going to need to use index URL, but then of course you need to sync the entire repo, right? Which is going to be, yeah, quite annoying to keep that up to date. So, no one uses that. Um this doesn't have any CVE because they just silently fixed this as a bug, but we actually saw a case where the problem is that if you have an extra index URL and it checks the official repos, it will start by doing a plain text request. And then it will get like, "No, no, no,
you can't talk as a non-SSL with me. Upgrade." And then it will upgrade to HTTPS. Problem is that we saw was that someone had compromised some infrastructure in the middle of everything. Which means that it checked the first package that it wanted to download and it says, "No, you need to upgrade. No, you need to upgrade the next one. No, you need to upgrade." And then all of a sudden it said, "Yeah, here's your package." So, basically what they're doing is doing a man in the middle of that first HTTP request and you basically have a remote code execution vulnerability in pip. Um this is a very old version. This was fixed in 2017, but since there's no CVE
for it and no one, you know, updates their Docker containers, if you look at Docker images, they are full with vulnerabilities, especially for uh like things that doesn't really have a CVE. So, it's not that uncommon that you still use this old pip version, right?





