Stick a Pin in Certificate Pinning: How to Inspect Mobile Traffic and Stop Data Exfiltration
Show transcript [en]
the End to End security is not just for one person right like the End security affects the entire spectrum of users of today's worldwide web so that that's a topic of the day and certificate pinning is one of the technology that's been used by most of the services and most of the applications today for providing NN security we just want to talk about what is certificate pinning why it has become so popular why n21 security has become a big topic of the day and we also want to talk about if you're a developer how do you enable uh certificate pinning in your apps and we also want to talk about what happens when you're an IT
administrator and the world becomes an end to unsecure world and you lose all the visibility of your network traffic that's the biggest issue that you the world like everybody is facing because Google and Facebook and all these other guys have moved towards End to End security what happens to the IT guy who Stuck in the Middle who cannot do anything right now because nothing is clear all he sees is opaque traffic packets going through his firewall and and just is sitting in a blind spot so the first thing we want to like the agenda for the meeting is we want to talk about what happened with this traditional SSL we all heard SSL is very
secure once you have SSL in your network you everything is happy you don't have to worry about malver snooping or anybody stealing your data even you see all the advertisements that say like look for the lock icon on your browser once you the the lock icon world is safe be happy you are completely foolproof right and that's not the case like the whole certificate model is been broken and it's been broken for quite some time and then how did certificate pinning arrive how did that become the DEA facto model for End to End security and then we want to talk about what happens now now like okay you've got n2n security what happens to the IT
guy what happens to the cios who are sitting there what happened to all the service providers were using the visibility in the traffic for Network optimization and all the other stuff and what do we do now right like this is what has happened what what next so that's the agenda for the day so where where did it start the first thing that started breaking the certificate r model is the certificate Authority is not one person right it's not RSA that's issuing all the certificates there's like so many sub authorities and end nodes and everyone there's a tree there's like 20 different certificate authorities that are issuing certificates you go to your web browser like Mozilla or something and you look
at the list of trusted Casa there's like hundreds of trusted CA if one trusted CA issues a malicious certificate or issues a certificate without validating The Entity or if they are hacked right that just opens up a can of warms so what happened like you've seen like um certificate authorities like bit9 and commodo they've been hacked and then they lost the root certificate and they never realize the fact they lost it and then for weeks and months and everything you see malare spreading across the board or traffic being hijacked without the users ever being aware because all the users care is do I see a lock icon on the browser I see a lock icon that
means it's SSL I'm good to go but they don't understand where this SSL is landing them to it's actually taking them to a pirate pirated website or something that's like injecting um malware traffic into their computer right just because you have a SSL traffic and encrypted traffic leaving your network or leaving your Endo it doesn't mean it's secure so that's the biggest problem that uh this the whole think of pkcs and CA that means once it's SSL once it's encrypted by SSL everything is good that is not the case and the other thing we have seen is uh several cases where Microsoft has several code signing certificates and root certificates where one or two certificates get stolen because they
have so many different Regional certificates one for China One for Asia one for Europe and everything if it leaks somewhere in one remote corner of the world and if somebody is able to use a certificate to like create malware and then install it on your PC we never realize it it always looks like it's a valid piece of software right the big problem with the certificate Authority right now is there is no complete loop back system of making sure every single certificate that is issued today is issued with a valid cost and the keys and the root certificate that are used for creating the certificates are foolproof and kept safe because once it's hacked you to wait for the
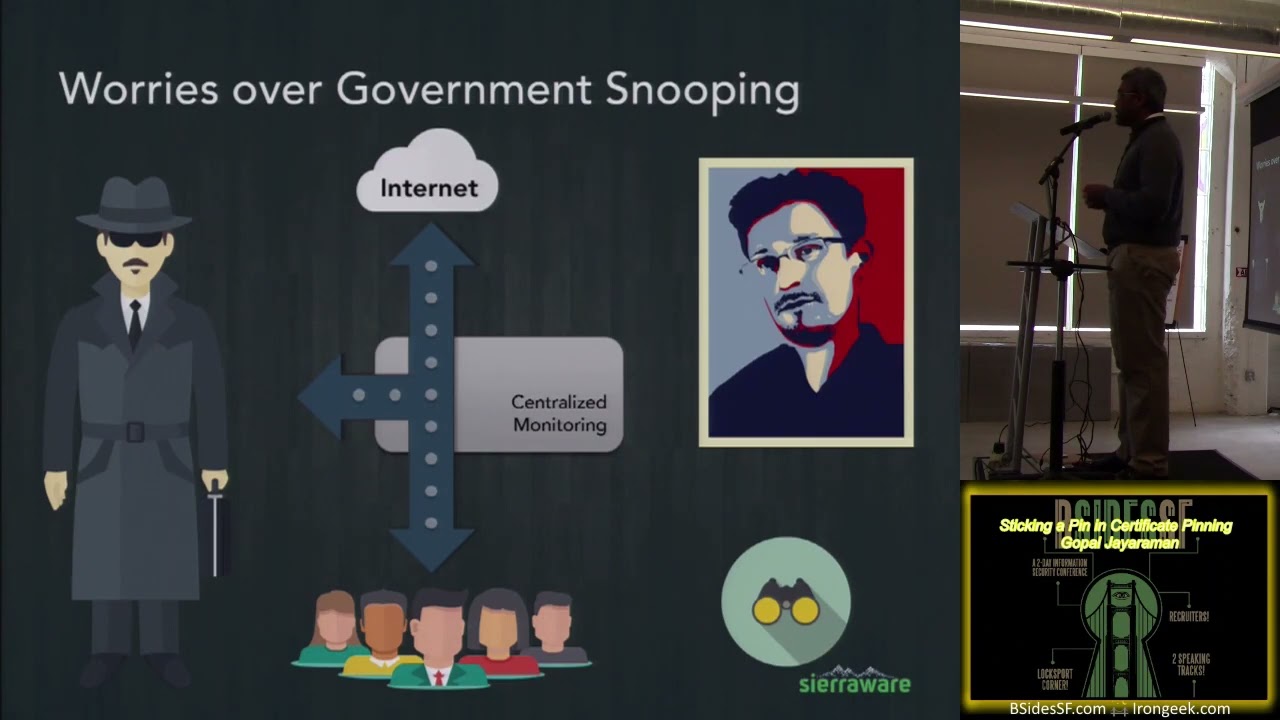
revocation of the certificates and the revocation could take a long time and that cycle between that period of time you could lose millions and millions of end points for malar and spers the next thing you probably have seen in the recent times in the recent year is the scare that is created by Snowden and other uh whistleblowers they've created this whole thing about whatever that goes through your network it doesn't matter it can be read by a central ized monitoring Authority right it it can be SSL it can be voice it can be anything that you send outside your endpoint it can be whatever it is right through your mobile network through your PC can be
monitored and which is proven true which is like there's so many um uh things that's been come like proven that like this is happening on a day-to-day basis a typical um NSA snooping happens they don't actually intercept the traffic they don't block the traffic all they do is they passively log most of the traffic they create a secondary bifurcation Channel they take a copy of the existing data they start archiving everything and then they do offline analysis right it's going to be a call from FBI saying like hey did you post a bomb thread it's not going to be like once you type bomb on Facebook it's going to block the traffic so basically most of the users never feel the
intrusiveness of FB NSA snooping because NSA does do inline snooping and ESS what they do is they work with isps and they work with uh providers to say give me a copy of all the network traffic let me do analysis they have their own algorithms they just don't go by simple keywords like bomb and other stuff but they do behavioral analysis and they figure out is this particular user Behavior request needs further analysis do we need to have FBI or local Authority come and talk to this guy and see what's happening so that's the um snooping model that's being followed by Western things like British and NSA snooping the other thing we hear is the
great firewall and the great Cannon most of you guys probably heard the great Cannon which was used for ding jit Hub few weeks back it's simple basically previously uh a year back if somebody said doas a lot of people thought it's the zombie pieces sitting across the internet and the malware can be activated for flooding traffic and that model has been deprecated for a long time you don't need zombie pces all you need is to be able to redirect traffic so all what great Canan did is they redirected all the traffic that goes to Bing and then they redirected half the traffic to jiub so whenever you see a web page today not the entire web page
comes from the same website right like you have advertisements you have several URLs that are like redirects where the you have Aggregates of data coming through and the final HTML is what you see so all you have to do is if you take a bing web page if you intercept the Bing web page and inject a small Javascript file saying go to the homepage of jiub that is enough to redirect billions and billions of connections to jiub which could just bring it down in NCS because jiub was never built to handle that much traffic so what the typical Chinese model is the have two ways whenever traffic leaves or enter one of this CH Chinese main
Network they have a great firewall which is doing inspection they do the other way of doing inline scanning compared to a typical NSA snooping which does offline storage and Analysis if you post a bomb threat in like in Facebook or some other website like in uh in China it can instantly block it they can say okay this particular traffic seems to be creating problems let's do a TCP deny so they do a inline inspection so they do archiving like NSA but they also do a inline inspection and block traffic if they decide you're not supposed to access this particular website like maybe Facebook or something else from China they can do an inline inspection and stop that's the great firewall and
they also can do uh JavaScript injection or HTML rewrite where they can use a current existing traffic going to a popular website and redirect it to some other website for dsing so all all of them are using encrypted traffic these are not traffic that are not encrypted so previously the expectation was if using clear traffic somebody could attack the traffic by snooping or redirecting traffic the whole man in the middle attack if you look at that if you read the description of SSL SSL simply says oh if you don't use SSL somebody could do man in the middle attack you don't need to worry about that even if you use SSL today it you can still do m
man in the middle attack almost 80% of the man- inth the- middle attack performed today are onsl traffic how do these guys do it right we heard it in textbooks we heard we read rfc's we read so many presentations and everything that says once you have once you have SSL you're good to go you see the lock icon on the browser world is safe your bank transactions are safe all your traffic is perfectly handled one Le person who can see the data traffic is the service provider so where it all fell apart where it fell apart is you got commodity Hardware that can decrypt at amazingly High rates you don't have to spend billions of dollars to decrypt
terabits of traffic today um you have very cost effective SSL interceptors using off the-shelf Hardware the other thing is a simple concept of uh doing um um mitm proxy what mitm proxy does is so basically they take advantage of the fact we have a whole bunch of CA that are trusted in our web browser you take a web browser we have uh service provider C that are being trusted so all a service provider has to do is let's say you are a PC that's trying to access google.com if you go to the lock icon on your browser and you click on that icon and look at the certificate it'll have two important Fields one is who is the
issuer of the certificate that's the guy who signed the certificate and who is the common name that means what are you trying to reach is it Google or mail. gooogle or whatever that thing is but when you have a mitm proxy in between if you check the certificate at that time the issuer will not be Google the issuer will be your service provider or your it administrator your corporate office certificate basically what they do is you first try to establish SSL connection to Google the mitm proxy in between determines that okay okay this is a new SSL connection it creates a fake Google certificate using its own CS certificate it signs itself and then it
establish SSL connection between the Gateway and the PC PC from end user the PC is very happy because he sees a lock icon he sees oh the data going out of my PC is encrypted using SSL but it's not encrypted all the way to Google it's only encrypted till the uh access point or the SSL Interceptor that's present in between and then then the SSL Interceptor gets a complete clear traffic and then it actually puts in a different tunnel and it goes out this is what happens today across the world this is how all the NSA snooping great firewall all of them work because we never realize where the traffic gets injector and all these other stuff this
is one other thing you hear like in UTM gateways from several vendors they say oh we do decrypt SSL traffic this is a simple thing basically what they do is when your endpoint comes into office or something they install a CS certificate on your browser and then your browser always trusts the your router gateway to be a CA this is one of the simplest way to do mitm hacks and everything so you've seen several problems right like SSL itself can be intercepted users are not smart enough to understand the traffic is not encrypted end to end you hear things like um NSA snooping you things like China Great firewall and all these other stuff now if you like Dropbox or
Facebook or Google you want your users to trust you you don't want them to feel oh if somebody comes and post something in my website it's going to be uh everybody's going to know what's happening like privacy issues and so many other things happen like a lot of people don't want to upload their entire backup to Dropbox right like that becomes a big problem because they know like whatever they upload a Dropbox is being seen by someone is being archived in some remote Warehouse somewhere right so that's a big concern so as a vendor as a business provider like Dropbox I want to make sure my users are happy so what do you do you work on certificate
pinning you make sure your connection is directly to the user and not with anybody else in between so the users trust you so that's that's how certificate pinning started basically all these vendors like Gmail even if you use PC if you use a Google Chrome Google Chrome does certificate ping it makes sure when you loog into Gmail or Google you're actually logging into Google it actually Val validates to make sure the issuer of the certificate is Google and not some in between CA so yes certificate pinning has happened all the users are very very happy now Google makes tons of money Facebook is making money nobody cares about everybody's happy that their privacy is taken care where does IT guy
stands now now right I am a IT guy I've installed it security I went and bought a data leak prevention I bought a deep packet inspections of firewall I bought a mail security I bought secure web Gateway I bought a IDs box I bought all sorts of stuff assuming all of them can see the traffic that's going through the firewall nothing is visible now you cannot decrypt the traffic all my IDs IPS box the green lights are not blinking just sitting there right like you spent millions and millions of dollars overnight the certificate pinning started happening they lost visibility on the traffic right like your signature B AV scans on the box they're not getting any traffic at all
from the firewall right like the typical architecture is you have a firewall that's analyzing the traffic and based on some patterns it redirect some traffic to DLP some pattern of traffic to um IDs all these other stuff nothing is hitting it because all it is is encrypted packets going in and out of the system what does IT guy do right like so just you're you're stuck in a limo you spent millions and millions of dollars you've created this beautiful Network architecture including video caching how do you offload basically when somebody's accessing video files from YouTube and everything frequently access YouTube files can be cached locally you've created this beautiful Network big corporate 500 company Fortune 500
company you've done this extensive work now you're stuck YouTube is inry Google is encrypted just basic stuff every single thing is now encrypted right you can't even cach image files so that's hello can you hear okay so that's the problem today so what has been what has helped some people what has helped some people are now impacting the other set of people which are the it
administrators yeah so what has helped the end users and the service providers are severely impacting it administrators so the other problem is previously you had this firewall and you had Salesforce and you had all this beautiful system for making sure nobody's copying data from Salesforce and uploading to Dropbox that model is completely broken you got a phone you got two apps you can copy data from Salesforce to Dropbox because the data that's going through Dropbox is just going to zip through your firewall with no visibility right all your data leak prevention schemes that you installed are worthless right now so that's a big problem lot of it administrators are facing today this is a very rapidly going problem with like
most of the things because all your analysis including IDs IPS DP everything is based on the fact you have some visibility on the traffic once you once you don't once you don't have any visibility on the traffic it's going to be very difficult to do any real useful analysis on the traffic that's going outside your network and who else has joined this party it's our Linux guys right today if you're a small app developer if you want to do certificate pinning or if you are like a big data center if you have like hundreds and hundreds of servers geographically spread across the world if you want to do certificate binning you need to buy certificates for every
individual server out there in the world right so the cost of making like creating certificates and paying RSA is just going to grow astronomically Also let's say if you move from Amazon to um some other AWS to something like azour your domain names are going to be different so you need to purchase a different certificate so all the cost of making certificates is is getting very very expensive right like so if I'm a very small app developer my whole budget was $100 that I paid for buying an i iOS Developer account and I'm just publishing a small app but I want to have certificate pinning I don't want to go through RSA validate that I'm a valid
business and make sure I have a certificate account there's two ends of the spectrum one is I'm a very lowend guy the other is I'm a big massive data center running 100 and thousands of servers across the world for both of them it becomes very cumbersome and costly to chase some certificate Authority buy certificates in bulk and make sure all of them are taken care right here's where Linux Foundation comes in they created this project which is which was there already but Linux Foundation adopted it which is called let's encrypt which is going to be a free ca for everyone it provides you revocation it provides you domain validation and it's it's a complete CS
service it's a automated CS service for everyone and this one is going to drive up certificate use everywhere like previously if you're it guy and if you wanted to have client certificates like thousands of client certificate for users it was com it was just astronomically expensive or if you are a big massive Data Center and if you want to have thousands of thousands of certificates and you want to change them you want to move from one geographical location to the other the costs were so expensive and you had to go through his budget approval and you have to go through planning right now nothing it's this free CA run by Linux foundation and it's being sponsored by all the big
vendors like Mozilla and Cisco they are all joining the party they want everything to be encrypted because more you encrypt more boxes they can sell on the other side for load balancers and all the other stuff right so they like the idea of everything being encrypted application developers like it to be encrypted and users like it to be encrypted there was in between CA that was just sitting there and saying I'm a gatekeeper you guys have to give me a whole bunch of money and that's where Linux Foundation coming into to democratize the whole CA system so now you've got a free certificate or you could just go to your typical cender got a certificate how do
you actually Implement certificate pinning right so a certificate pinning is on the app on the app that's on the IND user mobile device what you do is you take a copy of your certificate the certificate that you use for hosting your uh um applications on the web so you take the same uh certificate pass it on with your mobile application and the mobile application after the SSL connection is established can verify to make sure the certificat is exactly the same if you want to do like 100% bulletproof way of doing uh certificate check you check the actual certificate itself but the problem with that is let's say if you're Facebook your mobile users could be connecting to any
different kind of Facebook server right would be facebook. seattle.com or Facebook with located in San Francisco or Facebook Rector and so many other places so storing that many certificates inside an app for making sure certificate pinning Works going to get very very combersome Also let's say if you want to add a new geographical location or if you changed if you moved your server from Amazon to Google Cloud so your certificate pinning you have you have to you you have to create a new version of the app and you have to send with a a new patch of certificates so instead of that what the other thing people do is they just want to make sure the actual certificate is
signed by the person that Facebook users so Facebook or Google they act as their own certificate signing Authority so what they do is in the certificate uh pinning on the app all they do is to make sure the check whenever the connection is established the certificate is actually signed by Google not by in between mitm proxy the disadvantage with that is you need to store the keypad password on the app but that's the most common way of doing it because as you have a wide sprawl of servers spread across the world storing the entire list of certificates that this app could be connecting to becomes very expensive so as I was talking about if you are a developer which way do you go
do you want to go with the root key based certificate pinning or a certificate based certificate pinning is up to you if you are like a small guy all you have is one or two servers a simple certificate based spinning will be enough but if you're a massive data center with thousands of servers spread across the world you are better off with going with a root key based certificate winning so now we have free CS it's very easy to implement certificate pinning you just decide which way you want to go the root certificate way are the their way of doing individual site certificates right so what does it do it they have more and more people are using mobile apps like
what was PC based world that's now transforming into Mobile world and you lose lot of visibility when what's happening in the mobile world because every individual mobile world is an app right everything is now an app not a HTML page the traffic is all their own stuff the other thing is you have brought millions and millions of dollars of ips IDs web G and all these things expecting get some traffic from your inspection engine which is your firewall to identify the different kinds of traffic and then pass it along to IDs IPS boxes and they not getting any data right now right they are just sitting there idle not knowing what to do what do you do as it guy right we
hear from lot of big Fortune 500 companies or companies that are heavily invested in security simply saying turn off certificate ping traffic all they do is they go to their firewall box and say if you don't know what this traffic is just block it right which means you go inside the office you're not going to be able to access Verizon you're not going to be able to see your baby pictures and Dropbox or you're not going to do anything right like it's completely done you can't even use Google your Microsoft Office on your phone because Microsoft Office on your phone is using certificate pinning to store data back in the cloud so everything is off all
your phone is just used for nothing right like you just use your phone to pick up your phone call and there in a story that's one end of the spectrum the other end is to say just hope and pray nobody uploads all our company information to Dropbox and let them use dropbox so that we don't piss off all the users that's the one end right there's no easy middle way to come uh Fair where we are because there there's no way to encrypt see what's going on in that uh traffic either you let them just be a open blind Channel let trust your users and say hey don't do anything stupid just give them like a HR advice
or you just block all the traffic that's where most of the people are uh most of the it guys are faced with these two choices one is go to your HR and say please contact HR training to everyone saying don't upload don't download don't be you be I'm going to trust you but users can never be trusted that's the real world problem the next thing we see is it guys is getting completely desperate right their cios and csos all are screaming at them they're saying what is going on like you asked me for all this it budget I gave you all sorts of money you bought this beautiful fancy boxes and the fans are not even running in that room
everything is just happily sitting in power down mode what what's what went wrong right like what worked Year back they gave all this beautiful fancy charts and attack detection and Threat Vector and all these beautiful boardroom meetings are worthless right now so what does IT guy do you're desperate right you don't want to lose your job so what do they do they just go and install complete hacks on their endpoints they go and disable trust validation so let's say if you are an app that's expecting you expecting for SSL trust validation by checking the trust store if you disable the whole trust validation in the SSL stack of the endpoint yes beautiful you can be mitm
proxy in between you can do whatever you want to do the apps are going to think it's actually connecting the remote end node they're going to work but you're actually leaving the entire system vulnerable it's not even just your mitm proxy anybody else could hold mitm proxy at the remote side and hijack all your traffic right so being desperate and going crazy and then disabling the entire trust validation is not an option but a lot of people are doing it right now because there are so many op Source projects available like even you saw Lenovo installing superfish right that's the same thing superfish is even licensed by by several endpoint security vendors to act as a mitm proxy so that
you can inspect traffic and you saw what happened to Lenovo once it becomes a public once users are aware of the fact that their PCS are completely vulnerable and whatever they do can be seen remotely by a different user it's going to cause more problems right and also the problem is whenever the device leaves a managed node with all these hacks like superfish or Android SSL bypass install that device is completely completely vulnerable it doesn't take more than few seconds for the device to fall prey for a malware so please avoid it desperation but this is happening because they want a quick fix they want to see the data traffic going through the DLP box right they don't want the
DLP to sit empty so just come come back to the original thing if you have some developers here I I come from a developer background I like to see how things are written and everything if you and Android developer if you are iOS Developer how complex is it to implement certificate pinning it's not that complex we just want to give you an simple way it's very very simple if you look at Android right Android has gone a lot far to making sure you can Implement certificate pinning with just like maybe 30 lines of code if you look at Android it has classes you can go through the docs for Android you can look at these
classes for the trust manager the trust manager Factory that's the one it gives you you can take a current existing SSL session and using the trust manager and the trust manager Factory you can make sure that particular s is from a trusted CA of the list of C that like ca searchs that you provide and also you can make sure to compare your current search with SSL session session CT within like four lines of code it's so simple so that's one of the reason where you see more and more guys here's the thing right you have let's encrypt from Linux Foundation giving you free certificates Android making adding uh certificate validation like set pinning so simple all you have
to write is the 30 lines of code and the entire code is actually written for you in the trust manager Factory you just have to call few apis to make sure the remote endpoint is a valid one so that's one reason you see like more and more people are okay it's not that expensive for me I have aert I already have everything the apis are already there adding extra 30 lines of code let me just add it that's the reason you see like flurry and flurry of new apps every new apps that you see is now comes with certificate pinning even the simple things like Microsoft Office for Android and all these things come with
certificate pin uh SSL connections the other question if I'm an IT guy I can ask a simple question it's a nightmare I have certificate binning I cannot see the traffic all these guys are walking with their Android phones and iPhones and everything why do I even bother with BYOD let me just not say no to BYOD I give everyone a PC I disable the trust uh store in that PC or I won't let them use Google Chrome I'll say everybody has to use IE and then I I just be mitm proxy and continue to live where I am right that's one another option but that there's a between the fight between your CEOs and the C cios
and csos right the CEO wants to make more money he wants to improve productivity he wants a user to be available to do the work 20 4 by7 and he says figure out the security around what I want right you cannot restrict your corporate growth because it's not secure to do it that just doesn't work the other way you want it to be the other way you want to grow at you want to grow at like BL bling speed you want to just reach the Moon while you reach the moon you want your it guide to figure out how to make the path secure right it's his job to make the path secure it's your
job to trade Uncharted security like Pats right so that's the trade-off between your CEO and the CSO CIO in the company everybody's fighting for their own way this right now the IT guy has become the roadblock in your growth path of your company and you see more and more applications uh including like if you go to a retail store right now if you go to a doctor's office most of the doctors are now carrying an iPad right they don't want to have a old PC lugging it around and everything so everywhere including you probably heard things about like IBM working with Apple for providing an iPad for all the pilots so more and more devices like mobile
devices are being used for Enterprise applications the days when you have to go to a airport look at a air hosters waiting in front of a terminal to look for a schedule is gone right you want everybody to have an iPad in their hand find schedules you want to go if you go to a hospital you go to a uh optometrist everybody has an iPad they can just instantly scan your data and they can tell you where you are right they don't need to go through all the uh manually entering information calling the backend office and other stuff so saying no to BYOD is not an option so here so so far we just talked
about a generic issue of certificate pinning we talked about why all these providers like Google and Facebook were forced to use certificate pinning and as a developer how it is easy to implement certificate pinning what are the tools that are available for you you have very easy to use sdks from Android and iPhone you have free certificates from let's encrypt so as a developer you do that so that's the thing so what we discussed so far is just to summarize what we discussed is why do we need Inn security how do you do Implement in End security what are the tools available for you to implement n to End security and what are the problems the it guys are facing
everybody else is happy with n21 security except for the IT guy now right like that's the world has become all the guys have joined hands together the inducers the application providers all of them have joined hands they all become one side of the party they are all very happy the guy who is left alone is it guy who is like screwed he's like I don't know what to do now so the next thing we want to talk about is that one of the ways you can solve some of the problems is using virtual mobile infrastructure so just to give a but to give you what uh a disclosure of what we are is we are one
of the providers of virtual mobile infrastructure so it's not like unbiased pitch or anything but but what what we here to discuss is as it guy what are the options that are available for you for doing um to handle um encrypted pinned certificate pinned traffic just to give a brief overview of what VMI is I'm not going to go in several details of VMI VMI is similar to vdi most of you are aware of vdi which is like like hosted uh Windows services like RDP or uh full Windows desktop where you host a Windows desktop on a server and people access it remotely instead of Hosting Windows you host hand drve that's the difference between uh
vdi and VMI vdi is for desktops vmis for mobile there's few differences basically because it's Android you get better density you can do a little bit more uh like it's more touchbased and you can use your existing Android apps let's say if you're using drop Box for Android you don't need to ask Dropbox to develop a new app for Windows or other stuff you can just use existing apps as it is but it's hosted remotely so this is a typical architecture of VMI uh VMI apps are hosted in the centralized server and you can access them anywhere with no license restrictions because if you look at the typical Windows right Windows has license restrictions if you have a
Windows server with thousand users you need to buy th licenses Etc with Android there's no user restrictions so it's cost effective is cheaper higher density and also it's mobile friendly so end users can use what they use today without needing to learn a new interface or worry about Mouse pointer on a touch device so a typical uh way of doing VMI is two ways uh one is a mobile app virtualization which is similar to RDP how many of you are aware of rdss or RDP so RDP is basically you have one server you host multiple apps and the apps are only the apps are delivered uh to the remote client through a remote protocol and the uh vdi is hosting a
full user interface so REM mobile app virtualization is similar to RDP where you host multiple apps on Android runtime remotely and you deliver them remotely to the user so if you are a user if you a corporate guy using remote mobile app virtualization this is how my phone is going to look I have Facebook which is the directly running on my PC and Facebook which is hosted on VMI right the VMI apps are running on a remotely hosted box the box is hosted by the Enterprise which is your ID so using VMI how do you analyze encrypted data right like the data is going through your network how do you use VMI for analyzing data there are two
ways of doing it one you can do on the SSL stack itself the other thing you can do is on the container level the apps that are host remotely on the VMI are hosted in a container a secure container and the container acts as a OS abstraction layer between the apps and the operating system so it can intercept all the network traffic that is leaving and entering the app it can also understand all the file and the um content that has been passing through the app and you can also understand app behavior is the app supposed to do a particular kind of thing are they doing like downloading a lot of data or what kind of app Behavior the user is
performing right you can do app Behavior Analysis you can do Network scanning you can also scan all the other things like um you can also use for like recording your video session let's say if you find some malicious behavior you can use that to record the video session of the user and see whether and then you can do offline analysis so this is one method of doing uh if you're it guy instead of letting them for IOD instead of letting the apps be running natively on the device you host the device on your own uh managed centralized server which gives you better control better visibility so now you answer both the questions now you let your users to use Facebook Dropbox
whatnot also you have a way to inspect to make sure they are not uploading your corporate sensitive information to Dropbox so the other method is using a secure SSL prox see so previously I discussed right like one of the thing that it guys do is they get desperate they go completely disable the trust store or the trust mechanism in an operating system allowing them to run mitm proxy but the problem with the mitm proxies are both the the it guys are opening a big can of forms right once you allow an mitm proxy to be uh running on a network you could have a chain of mitm proxies once the data leaves your network there could be one more mitm
proxy see sitting up a higher up on the network that could be used to intercept traffic so what you want to make sure is as it guy you want to be able to inspect the traffic and you want to be the only guy who's able to inspect the traffic you don't want anybody else to sit between you and the actual business like Google or Dropbox to be able to drop and inspect the traffic so that's where we work with like uh the VMI and some of the vendors who provide um SSL proxies trusted SSL proxies they're coming up with a new protocol a new infrastructure called trust SSL proxy where basically only the Gateway that is approved by the it only one
particular box can act as a trusted SSL proxy and rest of the connection has to be directly secure so what they do is you have you saw some of the apis like the x509 trust store validation all the other stuff so for that what you need to do is you from the SSL State machine it there's a modification to the SSL State machine that is required what it does is today the SSL State machine all it does is it maintains the pr certificate what we do is we also maintain the tunnel certificate who is a actual next end point so the tunnel certificate will tell you where this from from the let's say if you the VMI
host the VMI host also knows the SSL certificate of the connection it also knows the certificate for the actual internal the internal certificate is what is the Google certificate right so both the certificates are passed to the state machine on the VMI host when the VMI apps that are calling when they try to validate the trust store they actually validate the tunnel certificate not the actual certificate that is used to connect to the V uh router Gateway so previously used to have only one certificate for the connection SSL connection right which is the certificate that is used for encrypting the traffic that left the endpoint now you are going to have two certificates one is your certificate
that's used to connect to the endpoint like for encrypting the traffic leaving the endpoint the other is a certificate that's used to Tunnel data between the SSL proxy and the server which is google.com or whatnot so and all the trust store validation and everything is all performed on the tnal certificate so for you you know you're going to trust your uh proxy and you also have a hold on the proxy right now to make sure the proxy is not allowing any more mitm proxies in between this and the tunnel so from the from the from the SSL proxy on the end node the tunnel is guaranteed to be a straight end to end tunnel so
you the it guys get the advantage of able to have see some visibility on the traffic the end user can have some peace of mind saying once the traffic leaves my um Network it's not being hijacked or it's not being profiled or it's not being snooped upon by anybody else it's a traffic that's going to the cloud so the tradeoff here is you are giving some front end key it's kind of like giving you a key of A a copy of a key to your or like a servant made or someone you know you you trust them you trust them to come in clean your house but you don't want anybody else to come into your house right that's the kind of
thing this is approach the approach is you let your it guy to see the traffic but nobody else can see the traffic so that's it's kind of giving a front end open key to your it guy and say yes I have to be part of the ecosystem you have I have to trust you to be able to inspect my traffic so I can access Dropbox inside office so there are three trade-offs you can do one is you can give a key to your it guy or you can you have your it guide block the entire traffic or you can have unsecured Network which most of the it guys are not willing to do right so this is one
of the thing The Trusted SSL proxy is going to start showing up in more and more boxes more and more vendors are working with like uh endpoints and uh VMI gateways to come up with this model because you need to have some in between uh way right you can simply say I'm going to allow you to use Dropbox with no visibility or you cannot simply say I'm not going to allow you to use dropbox inside my office there has be in between uh approach where users know that previously when you access Dropbox from your office it was intercepted it was analyzed right the forever that was the model and the certificate pinning that was mainly used for to circumvent
or avoid the problems of government snooping and other bigger problems now has broken the Enterprise it so this is one of the things that uh we being proposed by several vendors on the SSL proxy and the other areas to solve this issue the other thing that VMI can do is uh it can do complete monitoring because the entire app is running on a remote hosted Gateway uh you can do uh let's say if you're using messaging apps you can basically say okay if the message is being sent to a particular user or if the message being sent to a particular broadcast group or you can use any kind of ACLS to monitor the particular behavior of the user so you have you
have a lot more options for monitoring the user Behavior and the type of operation the user is performing so just to give a most of the discussion about certificate pinning is done I just want to give you like a final uh thing on like if I'm it guy yes VMI is helpful how does VMI help when the guy takes a cell phone out of my network manage Network right what am I going to do your Enterprise apps are still protected because your Enterprise apps are actually hosted in your own control managed Network right it's not hosted outside your network so even if you are even if the end user leaves a office your Enterprise apps are still protected you can still
make sure nobody can actually uh nobody can copy data steal data you can still make sure all your data leak prevention schemes are being enforce because the apps Enterprise apps are always hosted in your office through a VMI Gateway and the data traffic is always routed through your own manage Network and the other thing what we can do is uh because all the phones now use Arm based processors all of them have trust Zone based Hardware security with the trust Zone based Hardware security you can completely bypass Android and you can use uh the trust Zone based Hardware model for rendering the actual user interface and also accept user input so the Android if you let's say if somebody
brings in a phone which is rooted and they have the complete colel of the complete access to the kernel right most of the phones you buy today allow you to install signam mod or anything else which allows you to root the device instantly and you can install whatever root kits you want to install or install however you want to disable you can disable and do it right like you can disable MDM in 5 seconds so what we can do is when you use tress Zone based Hardware protection even if you have installed rootkits even if you have a rooted device you still cannot touch the thr Zone based thing because it's a hardware based protection
it's not a software protection so typical trust Zone based data path works like this uh data comes through the phone as a input streaming encoded like whatever that you see the remote screen right the remote screen is sent as a compressed video format and the compressed encrypted video is directly sent to the trust Zone world the trust Zone world has a complete own memory completely separate Hardware block and whatever that's running in the TruStone secure world can never be seen or access from normal world the normal world is what is running Linux Linux has zero visibility Linux thinks there is only like 0 to 3gb of ram after 3gb there is 64 MB of Ram or 128 MB of ram that's
being allocated to tr zone so today when you buy a phone they say oh we have 3 GB of RAM right there's always a hidden memory that's sitting behind used for trust zone for authentication and validation and everything and also trust Zone can process IO inputs and everything so when the when chip is in trust Zone lock down none of the normal World applications can read the memory can access IO blocks so the actual keyboard input that you're pressing from the touch screen which is I Square C is directly routed to tr Zone world and uh and so basically this is one of the things what we can do is on the endpoint to make sure your endpoint is completely
foolproof and secure irrespective of the fact what version of Android they run they could be running a rooted version of Android they could be running whichever thing is like they could be just installing their own they could just go to XDA Developers download the source code recompile boot their own phone it's totally fine because Hardware protection enables you to do certain things that Android doesn't do um that's pretty much the end of the presentation thanks for Patiently listening to the whole thing um if you guys have any questions feel
free
so the question is uh is it only for Android is it for operating system agnostic as far as the client is considered the client can be operating system Gnostic the VMI Gateway right now it's basically for Android because we want app developers the most important thing for the VMI Gateway is app developer if you use any other operating system educating the app developer or asking like guys like Dropbox and Facebook to write app for a new OS it's not going to happen right they've already written apps for Android we can get them from Google Play Store that's the reason we use Android but on the client device the end user device can be Windows Phone
Blackberry everything supported there's no issues on the end device because most of them are running on a similar architecture like a qualcom processor or the Samsung xnos they all use cortex a57 they are identical chips right this just have different s so ID but the actual chip architecture including trust Zone and everything are identical they use the same instruction for switching between normal and secure world it's the same arm processor same cortex
a57 hi hello uh thank you for the presentation I see the uh I see the clear benefits of the VMI approach for protecting the endpoint my question is and I'm sorry if I missed this it might be the audio uh how does the VMI approach handle the certificate pinning issue if if my application is checking for certificates how does the how do you block it or how do you allow it so um just to show you right when you host an app on a v my Gateway you can do two things one is you can actually when when an app is hosted on the VMI Gateway there's a container secure container that is residing between the VMI Gateway
and the application the secure container provides the entire operating system obstruction so every call of network traffic every time a packet is encrypted or decrypted the actual encryption decryption apis are through the container so at the application layer you got to complete complete visibility of the decrypted traffic right because the API that the app is calling let's say the app is calling um op SSL or like a Java API for decrypting the SSL call that container is the one that's providing the OS obstruction right so the entire decrypted traffic has to pass through the container to the application so the the container knows the complete decrypted traffic that is one approach the second approach is the secure
the second approach is the trusted SSL proxy which I was discussing it actually The Trusted SSL proxy what it does is it is very similar to the mitm proxy the one difference between mitm proxy and SSL proxy is trusted SSL proxy is the mitm proxy when you connect to it it's going to send you a certificate for the common name so the common name is google.com but the issuer will be the mitm proxy here the mitm proxy will not create create a fake certificate the mitm proxy will just create a normal s certificate and then connect to you but also it will pass you the tunal certificate back to you so you know where the mitm proxy is connecting
previously when you are working with mitm proxy you have no idea how many mitm proxies are in between the user and the google.com right there could be five mitm proxies 10 mitm proxies here you don't want when you connect to the mitm proxy you don't want to have any more in between mitm proxy you don't want to have NSA soping you don't want to have China wall you don't want anything so you trust your it mitm firewall and you want to make sure your it mitm firewall is directly connecting to Google so what you expect from basically The Trusted SSL proxy protocol what it does is it gives you the actual tunnel certificate back to you which you can use for
validating so you ask your mitm proxy or let's say if you're working for XYZ company the XYZ compan is hosting a SSL trusted SSL proxy you connect to it you ask the trust proxy and say who are you connecting to are you really connecting to google.com he says yes I'm connecting to google.com here is a proof of it you take that certificate and use that for validating certificate Penning instead of using the connection now previously what you do you use that certificate that's used for establishing a connection for for validating certificate right instead of that you use the T certificate for establishing for validating certificate Penning you get the point so basically you are letting your
mitm proxy in the it managed Network to inspect the traffic and you tell them I'm letting you under the under the Restriction that you're not going to let any more mitm proxies to come in between the way it's only you I'm letting you to the gatekeeper but once you analyze the traffic you better make sure the data directly goes to Google right so that's the secure mitm proxy these are the two ways you can help handle uh certificate equipment
propic so here hello all right uh okay there we go if you're um running in a man- in- the- middle proxy and you're trying to uh how are you actually verifying the Google search is the one that's pinned because the pinnings done on the application side right the like in this case for Google right now they're using uh Chrome has it pinned right but if you're running a man in the middle proxy you don't actually have that information right you can verify that it's signed by a quote valid CA but that could be
China yeah so uh his question was let's say if you're using Google Chrome Google Chrome could come with his own SSL stack same with Mozilla right Mozilla comes with his own SSL stack and it does all the work inside like there's no visibility for the operating system can we do anything about it no we cannot do anything about it we can do only things that are using the OS apis uh for doing all the work if they if you find an application like Google Chrome or if you're finding something that's very very heavy-handed and comes with its own SSL implementation and not willing to do anything else you are very very limited let's say Google Chrome even has an
option to have have its own secure sandbox right they even completely take all the visibility of the file operations or anything else out from the user it runs its own sandbox when you're running inside a Sandbox and coming with your own SSL stack it guy has to say sorry man I'm letting you use dropbox I can let you use certain things but if you're going to come back and say I want to use Chrome I'm going to say sorry that's that's where it is right now thanks for all your time and uh okay here's our timekeeper she's being so helpful she probably ran five like 5,000 laps today hello okay um here's this is kind of a
stupid question but this all appears to be designed for uh a phone connected to a Wi-Fi network suppose I'm trying to smuggle data out of a network or into it over The Cellular Connection or even on the internal flash memory this uh technology doesn't do anything to prevent that does
it so his question was what happens if the guy is uploading traffic to Dropbox via LTE so that's why we are telling if you just use the trusted SSL proxy it's not enough right using just a trusted SSL proxy and saying okay that's going to be the way I'm going to analyze um uh Dropbox traffic is not going to work when the traffic doesn't go through your own uh Wi-Fi network that's why we are telling host the actual app on the VMI Gateway
host so if you host the app on the V Mi Gateway the traffic always leaves through your corporate manage network if you just use the trusted SSL proxy what you're saying is perfectly true there is no way to inspect the traffic that's going through LTE right but if you host the actual app on the VMI Gateway so using the VMI Gateway you are hosting the app on your own server and the traffic leaves the server goes through your IB IDs IPS and all your inspection devices through the trusted SSL proxy so they have to work in conjunction the whole thing is you the main thing is if you're not hosting the apps on the VMI Gateway as you're saying um it's not
a completely secure thing or you have to do like signal Jammers and disable all the users from stop using LTE inside the office like use some kind of MDM or something like that and say nobody should use um LTE when you're inside the office what you're saying is 100% a valid question because there's no easy answer for that
thank you everyone thanks for your
time





