BSidesSF 2024 - Phish & Furious: Campaign Builder Vulnerabilities in a Blink &... (Raae Wolfram)
Show transcript [en]
so with that let's introduce our guest speaker uh Ray Wolfram with Microsoft and as you can see here talking about fishing and Furious fish and Furious this is going to be a great conversation I think you folks chose the right theater have a great time and take it away thank you so much Dana thanks to everyone for joining us here uh at our very first fast and furious uh fan club meeting in San Francisco who who am I uh I am a technology professional uh been in the space for more than a decade have taken an incredibly unconventional route here uh I've basically have done anything just to get to touch cyber security directly uh
we've been it system admin project manager and now I am a senior product manager at Microsoft and I work to help build our manag security services uh org so uh it's a it's a pretty accomplishment for me I am a a native New Yorker just a Puerto Rican kid from the Bronx so to be able to be here and represent is pretty extraordinary stuff I'm also a mom to a 5-year-old uh incredibly precocious but she keeps me spry I am a Star Trek fan I've had brain surgery uh and then radiation in 2022 so if anything sounds a little bit funky just blame it on the radiation and then I also don't drive which I think is hilarious considering
that fast and furious is uh framing the entire uh presentation so it's just for me and my reverent sense of humor and also Dana apparently but yes I love that um so what what are we doing here and what are we actually going to be talking about well we're going to be working uh to address uh the vulnerabilities that are inherent to campaign Builders email campaign Builders marketing platforms like MailChimp and discuss how they can be exploited for fishing attacks right uh we're going to address uh some of the aspects like trust manipulation as well as the scalability of these attacks and uh consideration for mitigating uh these uh exploits uh moving forward and then essentially uh
really want to focus on the Practical strategies uh to understand and combat uh evolving fishing threats but some of the most like essential basic um uh practices that we should be abiding by uh cyber security uh practitioners all right so as I said a little uh while earlier it is all about family right so we're going to start at the basics here CU when we talk about email security this is setting the foundation right so we have this Trio or or trifect or trivant if you will of uh uh email security protocols right and so uh we can tackle them independent ly and they can be considered as distinct uh protocols but really uh their power is
Unleashed uh when they are uh working together in concert in conjunction uh in all with all three being deployed in an environment and when we have this Trio uh in effect um we really are not just building uh our cyber security uh program and and bolstering its posture but we are um uh engineering it with a level again not just of fundamental security but of resilience as well and so we're we're going to tackle each one uh individually and we have SPF dkim and D mark and uh then we're going to discuss how uh important it is to to have them working in in unison with one another um so the first one that that is
the the ground floor here that is SPF which is the cender policy framework and again it's really helpful to understand conceptually uh the landscape that we're operating in because when we dig into how the uh email marketing campaign Builders are actually uh how they function and how we're able to leverage them for legitimate business purposes and how we're able to exploit them uh for uh malicious intent it helps to just have a uh the the fundamentals down here right and so SPF uh represents the sender policy framework and that's really going to validate whether uh an email server can send uh mail on behalf uh of a domain and an analogy that might be helpful here is to think of SPF like
an employee directory um essentially it's saying these individuals work within this organization and and we vouch for them and essentially how it functions in the security email security protocol world uh is when a mail server receives an email it checks against the record uh to verify if the the IP address matches the list right of of the specified IP addresses that are are um allowed or permitted to send email on behalf of the the server and so this is really going to be um protected against uh spoofing right so you know we we have a list it basically confirms who is able to send emails out uh and if it we have another entity that attempts to send an
email out that is not already specified on that list it's going to fail the check right so they they are are not allowed they're not on the RSVP uh uh invite list right but that's not going to address um the integ of the email content right so we first we want to validate the identity of the the sender and then we want to be able to confirm uh the integrity and so that's where dkim comes into play but just to to close the loop on SPF and and like what it represents there are two like options here two flavors of how to create or specify your SPF record uh essentially you can have a soft fail or you can have
a hard fail and the soft fail um is more permissive right and so if there's a email sent from a sender that's not explicitly listed not on the SPF record it the the network or the organization can still allow that email in and and it could specify how it handles it with Demar but if there's a hard rejection um setting enabled then it's going to drop the email and again there are different ways to handle it but by and large it's just not even going to hit uh the server and these are these are the basics these are the essentials here um so SPF covers the the validation of the identity of the sender and then we have
dkim and that's where we're going to get into validating the Integrity of the content to ensure that it hasn't been tampered with or it hasn't been compromised in in any way and so really these protocols build on each other right so we want SPF enabled to validate the identity and we also want dkim enabled to validate the Integrity of the email content and then Demar brings it all together um DeMark is going to basically outline what we're going to do so first it it's it's dependent on SPF uh and deim being um uh enabled and operational but essentially if there's an email uh that fails the check um we're going to be able to tell it what to do with that
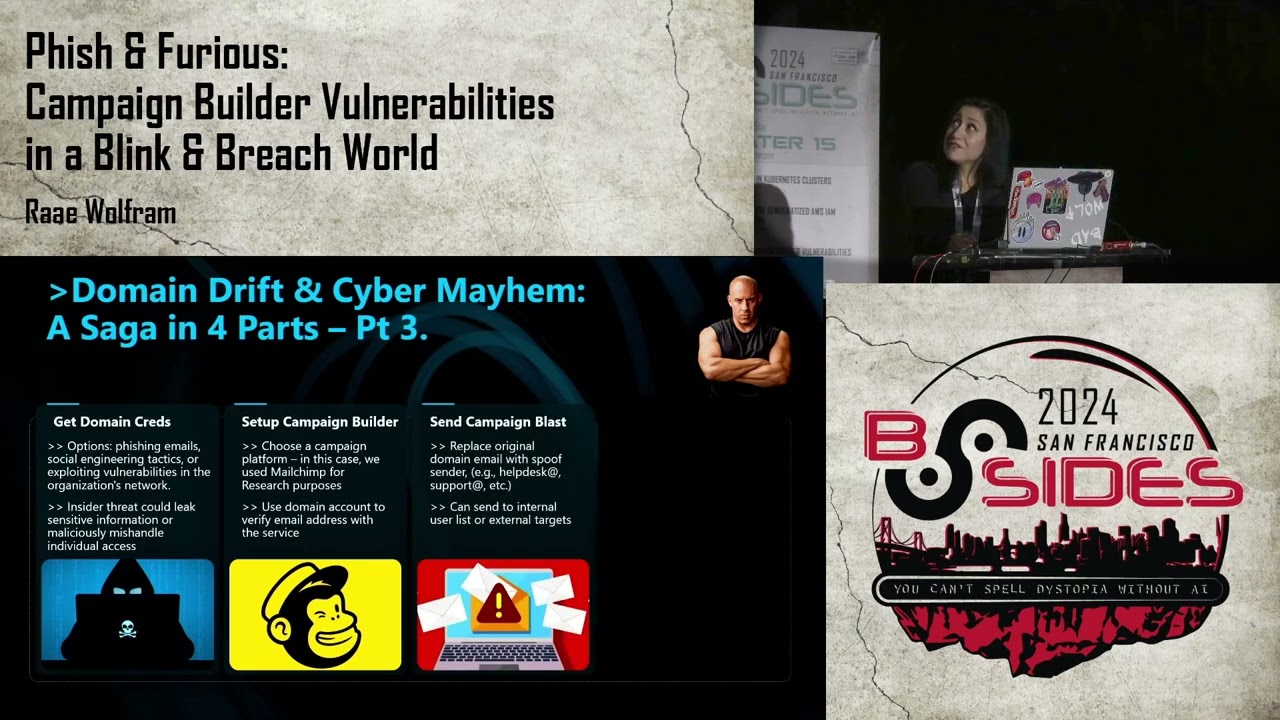
email and then we're going to have reporting auditing logs essentially of what's actually happening and that's going to be vital to you know your your stock uh and your internal organization to understand uh exactly all of the traffic and activity and and to be able to to get ahead of of threats so when we think about um how this ties into the picture of leveraging a tool like male chimp um it is a saga in four parts okay so MailChimp is a basically a glorified or not we're not there are email campaign building tools like MailChimp essentially a glorified content build Builder and you can blast emails at scale you can distribute them at scale um the the first step in this
attack essentially is to have domain credentials already right um and so that's um seemingly a non-trivial aspect of this but we can have Insider threats we can have Bad actors um we can have credentials that simply uh have not been expired because these organizations don't follow and the fundamentals of security operations here um so as long as you have access to an active uh account within that domain you are good to go so that's step one and then step two you're going to set up your campaign Builder account and that is pretty straightforward and you could be uh you can essentially load it with um uh fictitious information with the exception of validating your that uh
legitimate domain e email address and then you're going to craft your campaign or your email and then you're going to wreak havoc uh CA some Mayhem and you know this is scarily easy to do uh so again this is an attack in four parts uh in the in the first part um as long as you have access to an active uh email account within that domain you you you're Off to the Races all right so when I first uh put this uh presentation together first started working on the project uh I was using MailChimp and it was uh a lot more permissive uh I was able to build more elaborate HTML campaigns again using a outdated email
account for specific domain still had credentials that were in no way uh administrative I had no admin level privileges uh just an ordinary um essentially uh student account and uh I was able to to create really polished uh looking um fishing campaigns simulated fishing campaigns again there were no special privileges associated with this account uh and that uh so that was a great wonderful presentation uh concept and when I Revisited a few weeks later it looked like this um capability was uh um deprecated it was address um so MailChimp uh in response to an industry initiative uh led by Google and Yahoo that now requires uh services that send out um or organizations that sent out
emails uh at least 5,000 I believe uh a day or for some specific period it requires them to have Demar enabled again which requires in turn SPF to be enabled in the environment as well as uh deim enabled in the environment and so because of this Brave New World uh mailchip restricted the ability to uh basically uh arbitr set the sender um and you are you're no longer allowed or permitted within the system to send uh HTML campaigns because of this DeMark movement here which is pretty impressive um however we are still able to send uh emails again as long as you create the account in this uh campaign Builder with a validated legitimate email address
like you know uh John Smith at wherever. comom we can uh create uh a email that is PL text and list the sender legitimate sender quote unquote legitimate sender with help support at whatever.com or uh it system uh Team uh whatever or financial services at whatever uh.com so there's still a major Gap here and that's where we kind of dug in and and exploited and so um we we might be thinking huh how is this really effective right like HTML you know email seems a bit more compelling you know folks might be um more liable to click around or might be um more easily deceived with a A Polished HTML email but with plain text many organizations
use that to send broadcast messages critical alerts um uh important time sensitive information uh so this is still super relevant and it's still uh a vulnerability here and so what we're looking at uh on this slide uh is essentially setting up the the plain text uh fishing email um so I you know registered with essentially John Smith at school.edu and I'm able again you know so it's um we can change the name right like the plain text name and that's helpful right that adds to legitimacy and believability and we can instead of the name that you registered the account with we can alter that modify it to University help desk we can also modify it to to the burar we can
modify it and again this is sticking to the world of Education we can take a step back and literally select any industry we can uh select uh Health Care Hospital uh provider we can um select financial services so we can get uh pretty creative here uh and then when we uh alter the email address again the email address itself doesn't even have to be legitimate doesn't even have to exist um we were able to send successful messages with chaos uh at that university.edu so I mean the there are no limits to how creative you can get here and so what was even I think the the Pista resistance of putting together this um plain Tex campaign you have to
appreciate that when they appropriately properly addressed the HTML uh vulnerability I feel and they implemented that technical control where now you need to validate um the actual sender that you were specifying which is is amazing and impressive and that's totally what what should happen um when you set up or create a plain text email and you drop in a URL and the URL could be anything it could uh link to a Rick Rolling YouTube video let's say and the and the URL is plain text right you can shorten the URL it doesn't matter if you drop that into the the email itself as you're creating it within this platform the platform will alter it on
your behalf and it will prepend uh that domain that you listed the domain that you registered with it'll prepend that to the uh beginning of a uh a vanity URL so not only does the end user uh receive uh an email or a message from this entity that you are impersonating that you are spoofing you can also drop in links and regardless of how those links are constructed they will appear as they they are legitimate um and a part of that domain now uh for for this slide for for this uh screen capture this is a view uh where you see the email on desktop and so uh kind of appended uh to to the sender it has via
MailChimp or via the the campaign Builder now that's kind of a red flag that's kind of a signal um more Savvy end users might disregard it might report it hopefully they'll report it uh but it it's it's not as obvious right and it's especially not as obvious on mobile on mobile this is pristine this is seamless it comes through flawlessly uh we have the impersonated identity we have the modified kind of vanity uh title and the from name we have the uh transform or converted URL that in this case uh thankfully just links to Rick Rowling uh video but this uh appears to be part of an actual legitimate um domain sub page so the you
know this is the uh the exploit in the world of the the platform um this is what you can do leveraging that tool um again with plain text it is no longer uh a capability with the HTML uh module that they have because they implemented a technical control because of the Demar push and initiative earlier in 2024 and so we reached out to uh the service and let them know hey you know we uh recognize that you there used to be a way to exploit the the tool for HTML campaigns it's still active for uh plain text ple you know please create parody please address it uh and you know we we tried to raise it as a
vulnerability um it was closed because it was out of scope because it wasn't technical um in terms of the the code infrastructure for the platform uh and then we reached out to the service uh support folks and they share that this is uh a burden that lives uh upon the shoulders of the individual organization they addressed the uh HTML campaign Builder functionality because of the DeMark push uh but the plain text uh feature Falls outside of scope in some way and again is just the responsibility of the individual organization and so you know this this bring us to you asking more critical questions here U and thinking you know like we can appreciate that there are
some fundamentals and Basics to implement when it comes to email security right we just want to uh understand like do you have how conservative is your SPF record like what what configurations or what settings or controls are you um deploying to to that end and then are you actually leveraging Demar right um we you know I toally get that SPF is more straightforward right it's a modification of a text record whereas Demar first you have to have SPF in place then you have to have deim in place and not is a bit more Tech uh techn technologically um uh involved um but DeMark uh is really going to be um one of the the Hallmarks here of your
email security program and so these are they totally understand that that's on the the burden of the organization but when we look at um the example set forth by leaders in the space when we look at the actual impact uh where something like if Google and Yahoo say hey you can't use our services right unless you have Demar enabled in your environment I mean the businesses take notice of that they're they're going to um pay heed to it I mean um and obviously uh there are other considerations in place there but it ties into this aspect of just good upstanding cyber citizenship right there's a global community so if we go back to to Dom and uh the theme at hand
it's all about family and there's an aspect of shared responsibility right on the individual organizations but also the the services themselves so you know there are vendor uh solutions that could be leveraged uh but they leaders in the space and then the the vendors uh that leverage those Services I mean we work uh uh in unison with one another right and and so um just understanding and paying heed uh to that I think is incredibly important um and critical to keep top of mind um when we consider just how impactful uh something like um leveraging exploiting a legitimate tool such as MailChimp uh could go Ary right um so that's where we're at today um any questions uh feedback here we
actually do have a question yes uh one person asked do you see these dark patterns being used by semi-legitimate senders for example political campaigns and advertisers who don't want to respect email etiquette yeah I I think that that is actually a a serious concern um which is why we are doing the the good work um internally I I can speak to to my team leading the charge um again not in particular to the presentation here uh but what what what I just shared is it is an actual um Gap in something that you know organizations need to to think critically about um and so there are simple things that we can do um on the technical end I used to you
know work for smaller organization I understand the challenges and the bureaucracy and the burnout uh and having to wear many hats all at once uh and reconciling the business needs of uh leveraging um these email campaign Builders uh but also protecting your en users protecting your organization it sometimes requires some level of creativity um but but sometimes uh you know end user education can go a long way we can uh Implement um some Flags or banners as uh signals or cues to our end users to kind of mitigate uh the the threat uh and the risk there to a certain extent so to your question yes I think it's a legitimate cause for concern and there are ways that we can
be empowered and show up at the individual organ organizational level and also encourage service providers uh to to do their part as well thank you uh another person has asked if the sender does not exceed the 5,000 message quota can spoofed email be received in Google or Yahoo inboxes without requiring proper DeMark records yeah um that that is a great question um so I can't speak to the ins and outs of the Google and Yahoo um uh Service setup but uh with regards to MailChimp in particular they implemented a technical control so regardless of whether there's a DeMark set up uh you cannot send or exploit uh the HTML campaign uh functionality without validating first the sender that you are
specifying right so if you register your account with johnsmith whatever.com if you then attempt to send an email with not johnsmith whatever.com MailChimp is going to require you to say oh cool we you're not John Smith fantastic please confirm that right and M they're using multiactor authentication as well so it's pretty incredible that for one module one functionality one feature they have really they Shen up the the gaps there uh but for another uh functionality like plain text that's still uh uh the wild west essentially well let me take one last question for you um Sayan asks what are some theories as to why plain text is permitted but not HTML Rich email for the recent
DeMark requirements like fishing is still very possible yeah that's a great question I I imagine it's because um at first glance uh it may be because plain text is not as compelling right so it's not as sophisticated not as polished but many organizations for various reasons still rely on Plain text Communications and almost it's a a riskier um Vector because you're going to be leveraging it in the break CL glass scenarios in those edge cases in the hey this is time sensitive this is urgent you're going to want to leverage plain text over a glossy Banner uh multicolumn email content so I think it's it's a huge gap there needs to be addressed thank you uh folks give it up
for Ray thank you





