The Vulnerability in Your Pocket
Show transcript [en]
Thank you for coming. I'm Ben Aling the welcome to the vulnerability in your pocket. If you want to follow me on social media, I do not do Twitter, but you can find me on Masttodon infosc.exchange. Ben aling. Anything I say today, my opinion, nothing to do with my company. It's purely my opinion and does not represent the position of my employer. First, the bad news. Your phone is insecure. It's insecure not because of anything that's wrong with your phone, but because of the way telecommunication networks have evolved, you can't fix it. There are some things you can do to reduce your risk. There are also things you can do to increase your risk. This will not surprise you. Of
course, Telos talk to each other. They have to to get your phone calls through, to get your SMS through, to get your data through. But they don't just send user data. They also have a meta conversation about the user data. They need to say, "Does anybody have this user in their network? I've got this user. I've got a phone call for this user. I've got an SMS for this user. This is all signaling information without which you could not send SMSs to somebody on a different telco. You couldn't do roaming. Billing would have trouble. One of the main protocols used for doing this you may have heard of, you may not have heard of is SS7. It has
other names in other countries. SS7 signaling system number seven. It's old. Not quite as old as I am. Older than the internet, older than mobile phones. It was developed for landlines in an era where to make a phone call, you had to effectively reconfigure bits of the network to connect the two phones together. But it's evolved and it's been extended. And it now allows Telos to provide all of these features and and far more. SS7 was used in 2G was used still is still used in 2G still used in 3G. When 4G was developed, they knew there were a lot of problems with SS7 and they fixed some of them. They improved the encryption. It's still not
great, but 4G is like 3G only. 4 diameter is for 4G. What SS7 is for 3G. Some of you may be thinking, hey, I know the name diameter that's used for logging into computers. Yes, it is the same protocol. It does a lot more than most people [Music] realize. I mentioned roaming. You probably don't have to think about roaming to use it, but there's a lot happening under the covers. When you connect to a network that's not your normal network, it has to connect back to your network and say, "Hey, I've got your user over here. Is their credit good? Am I going to get paid if I put their phone calls through?" And then
your home network will say, "Yeah, it's fine." they can make a phone call, send it to me and I'll send it to the end destination. So if you're roaming in Australia and you call somebody in Australia, your phone call quite probably comes back to your home country and then goes all the way to Australia, which is one of the reasons Rome is expensive. But there's a lot of conversation between Telos behind the scenes to make this all happen. Let's go back insert wavy lines here. Before there was SS7, there was SS6. Before there was SS6, there was SS5. SS5 used what's called inband signaling. They actually played tones of a specific pitch in the audible
spectrum. And that worked well enough until people worked out they could play their own tones with the right equipment. If you had whistle out of a serial box, you could use that to persuade the exchange that your phone call had ended. So it would stop billing you while your phone call continued, which was very nice for you cuz you got free phone calls to anywhere in the world. This then evolved into blue boxes and all sorts of other freaking boxes. PHR and Steve Wnik and Apple were actually quite invested in this very early on but that's a long conversation. The problem was that users had access to signaling data. So SS7 moved the signaling data.
SS6 moved the signaling data onto a separate system. Users can't get to it. Everything's now happy. For a while, for a while, 1975, this was good enough. The only people who had access to the SS7 system were Telos. So, they didn't need encryption. Encryption was expensive then, too. Nobody would have even thought about doing it. diameter. They included encryption, but what they didn't fix was authentication. So, you still didn't really have a lot of control over where it was coming from. If you can get into the network, and it's not trivial to do it, but it's not impossible to do it. You can send SS7 messages. You can send diameter messages. Telos sell access to these
networks. Access gets stolen. Telos cooperate with the local authorities. If your government says, "Hey, we need you to send a couple of SS7 messages for us," your telco is probably going to cooperate because they have to. There are legitimate uses for this. If you get a two-factor authentication from an SMS, it's probably not because your bank has worked out which of the however many telos there are in the country. They will go through aggregators. So you can get two factbased SMSs. You can also get spam. Banks use this for fraud prevention. They will say where is this user and they can use this to diagnose impossible travel. If one minute you're in Gway and then the next minute you're
in Russia, something dodgyy's happen. They can also be used for all sorts of undesirable things. If your telco gets told, hey, my users in Russia, there's an SMS comes through, send it to me. probably be about six digits. Thank you for that. So, this is one way that cycriminals get around 2FA. Similar things can be used to intercept phone calls. It can even be done with SIM swapping and it can be done to locate people for espionage for sort of international stalking. Criminal groups have used this to work out where reporters are. There's almost certainly people being killed based on this sort of metadata and that sort of gloation is probably the most common abuse because
it's also one of the hardest to prevent. 5G these problems are now well known. So 5G comes in there's a lot of people working on security. It's got better encryption in more places. It's got mutual authentication. So when your phone connects to a visited network, the visited network says to the home network, I've got your user here and there's an exchange of information so that they really do know mutual authentication. Phone authenticates to the network, network authenticates to the phone. It's much harder. You, the visited network, can't say, "I've got your user here on my 5G network." If they don't, it also defeats im catching. Some of you may have heard of catching. Im catching is basically fake
base stations. Again, it has different names in different places. If you can get your fake base station so that it's got a stronger signal, it'll be preferred. Perhaps you might even do the real base station. It's it's probably most often used by law enforcement, sometimes with a warrant, sometimes without a warrant. Uh so tech companies don't like having their their users been compromised. So 5G because you've got the mutual authentication and you've also got concealed identifiers. So it's very hard to get information about using 5G because your identifier is concealed. That's not it's sent in any way which is easy to access and it changes. So you don't know whose phone is trying to connect to the fake base station.
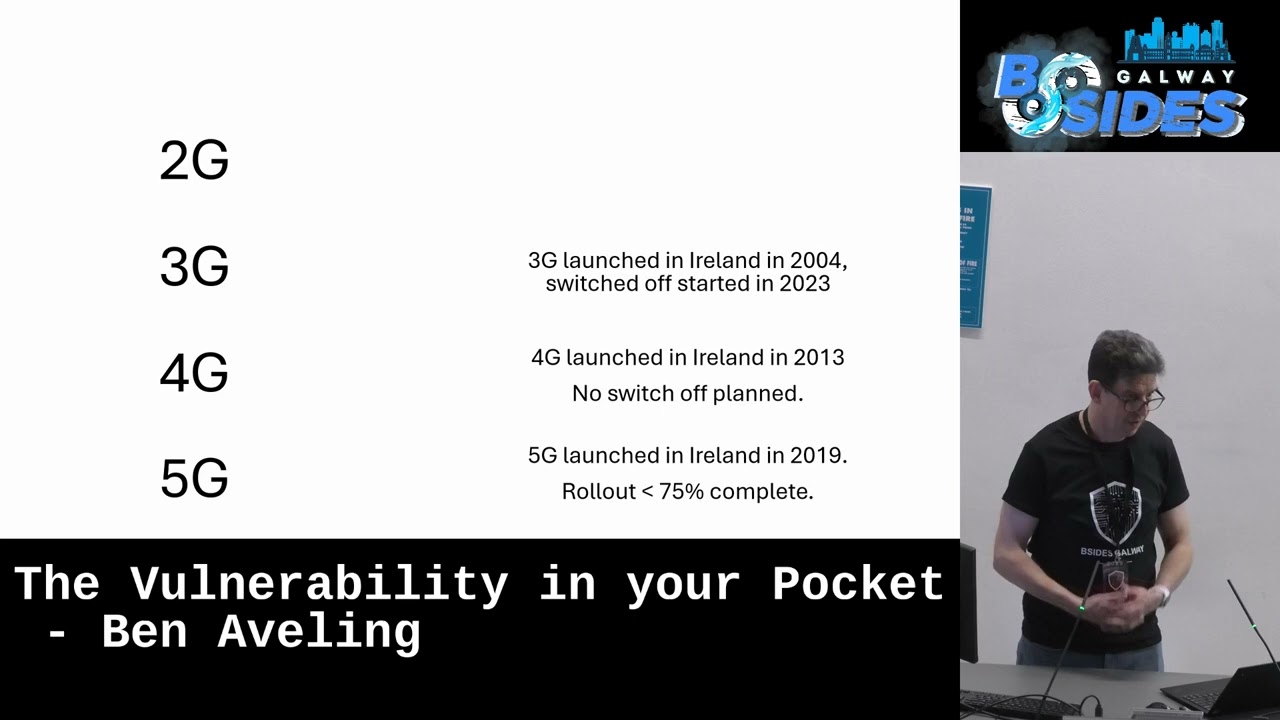
Happy days. Who's heard of downgrade attacks? If the fake base station says, "I only speak 4G." It's quite likely your phone go, "Oh, all right. I can use 4G." If the malicious visited network says, "Here's the user. Oh, they're not on my 5G network." then the home network's got no good way of knowing just from that information that the user is not in the visited network. So while we have 3G, while we have 4G, these attacks will continue to work. Simple. We just need to get rid of 3G and 4G, right? We're still using 2G. Russia stopped using 1G in 2017. 3G, the switch off has started. Some Irish Telos have switched off 3G, some haven't. Some countries have, most
haven't. 3G has been with us for 20 years. 4G could last 20 years, could last more. While these networks are still used, these downgrade attacks will still be possible. Everybody feeling cheerful yet? [Music] It's when a threat emerges, it becomes worth investing in defenses. Telos do have access to firewalls. They're called firewalls. They're more like proxies. It's not like they can block a particular port, but they will look at some of the different commands that are sent and try to work out, should I actually respond to this or is this suspicious? So, they can use improbable travel, they can use volume. And it's a continual game of leapfrog where the attackers try and find new ways to abuse
these protocols. And these are big and complicated protocols. Lots of messages in them. It's a little bit like trying to stop somebody ping using ping on a network. There's always another way to send a ping request. But there's this game of catch up and stay. So there's a limit on the scale of this, but it's never going to be completely eliminated using firewalls. Not all telos have firewalls. And if you're genuinely roaming or if your telco can't tell if you're roaming, then they sort of got to kind of trust what they're told. You can't completely protect yourself. The attack doesn't even have to arrive at your phone. You can say, "Okay, I'm not going to use SMS 2FA."
But if somebody's trying to break into your account, they're the ones that decide a 2FA message is going to be sent. So, it's not the message won't reach you, but you won't even know that that message has been sent. The criminal will just authenticate. Forgot my password. Send me a new one with 2FA. Happy day. Turning off your phone doesn't help. Your phone's not involved in this conversation. Turning off your phone just means that your telco has less ways of knowing where you are. I'm not saying they're going to use that information to protect you, but maybe they will. If you take it away, that's just one less defense. What you can do, all you can do
is reduce the attack factor. So, if you're in a position of saying, am I going to use SMS? Am I going to sign off the users SMS? And you don't have to, maybe you don't. Uh if you do get SMSs which you don't that is sus don't trust them. If you're communicating with somebody else and you want that conversation to stay private don't use SMS. Prefer an encrypted end to end messaging system. A lot of people recommend Signal. There's some other ones that are recommended too. A lot of people recommend telegraph because a lot of people have put a lot of effort into persuading people that telegraph is secure. Telegraph is not end to end encrypted.
It's not as good a choice as some people will tell you. There are things that you can do to make life better or worse just in general regardless of how the attack comes in. If you have an iPhone or a good quality Android, if then you'll be getting sent updates. If you have a cheap Android, you may never get a security update in the life of the phone, which means that all the vulnerabilities that are there when the phone was made will still be on the phone. Install those updates when they're offered. There is an operating system called Graphin OS. There's a couple of operating systems that are designed to be installed on Androids. It's not for the home user yet, but they
are there if you feel you have the need. People will tell you that iPhones are more secure than Androids, and that's debatable. But what's not up for debate is that there's a lot more malware on Androids than on iPhones. And the reason for that is sideloading. The app stores are pretty good. Apple is probably better than Google, but they're both it's like 99 98 and then side loading is down about 5%. Side loading is the fast track to getting malware. Don't root your phone because then it makes it so much easier to for malware to move sideways. Well, the protection on your the sandboxing on your phone is there to protect apps from each other.
If you root your phone, you bypass it. If you have a professional reason to root your phone, I remember the sort of room I'm in. Have two phones. Do not have your banking details on the phone that you've rooted. However good your reasons are for rooting it questions might anticipate WhatsApp it's with WhatsApp the user data is protected. WhatsApp cannot see the me see what's inside the messages you send. They cannot get at the conversations that you have, but they know who you're talking to. They know who you're sending messages to. As one of the Americans said, we kill people based on metadata. Metadata is enough to build a network of who your connections are. If
your connections are dodgy, then it's pretty easy to tell that you're dodgy. Now, this doesn't mean that you shouldn't use WhatsApp. It's all about knowing what information you're putting out there and accepting the risks that you're taking. VPNs, VPN into work makes perfect sense. Not as necessary as it used to be because a lot of the applications your work office will probably be secured anyway. FreeVPN is worse than noVPN. There's almost nothing on the web now that's not encrypted. Simply using VPN isn't a layer of encryption or encryption. It doesn't help, but it means that you're sending all of your meta data because VPN can't protect your metadata. You still need to know where the traffic is going from and
to. But it means it's just a single place where somebody out of the goodness of their heart is forwarding on your data. And why are they doing that? Well, who knows? Antivirus. It's probably a good idea on an Android. doesn't do much on an iPhone because sandboxing apps can't interfere with each other. So, and that's what antivirus does. It's one app checking on the other apps. Using a local SIM overseas, well, on the one hand, you're not roaming. On the other hand, you're now with a telco that you don't know and probably possibly may not have as much protection as you are as Telos do. Throwing your phone in the river won't work. It just
makes it harder for your own telco to know whether or not you're roaming. To recap, SS7 diameter 3G 4G, they are vulnerable for reasons that are not going to go away. Those proto those protocols are not going to go away either. 3G 4G will be with us for a long time yet. 5G is quite secure. Maybe tomorrow, maybe I'll walk out of here and I'll discover, oh yeah, somebody's broken 5G. That's always a danger, but so far it still seemed to be secure. There are things you can do to reduce your exposure even if you can't eliminate it. Telos do what they can. Most of them we hope companies I if you have the option to
not send SMS by SMS 2FA you should take it. A lot of companies don't have that option because not all of their users have smartphones. But as things evolve, we may get to a situation where that becomes more practical. And for some situations for your own company where you know people have smartphones, you should probably looking at Google authenticator, Microsoft authenticator and other solutions.
questions.
Yeah, call it out. Thank you very much for presentation especially for your iPhone 16 environmentally damaging too. Um do you see uh do you see any trends for by this several do you see the trends that this um mobile network specific attacks will be evolving as opposed to classic IP or application level and cheaper than do you see we will see 5G breaking everywhere has become So well do I do I see 5G becoming broken? Yes. I don't know. I don't know. There's been a lot of work go going into 5G to make it secure. They budgy relies on web services for its communications. So it's it's well tested. So the telecommunications industry everything used to be custom. The hardware was
custom, the software was custom. This gave a lot of security through obscurity, but it was all a bit roll your own crypto. These days, it's much more commodity based. It's Linux VMs. So, I have some faith in it. Um, somebody might want to ask about quantum and the answer is yes, quantum breaks everything. It it ever works. There are defenses against that too, but that's an entire talk in itself. In the slide, I saw that 2G is supposed to be introduced by 2023, but 3G is already used right now. Depends where you are. So 3G has been shut down in some countries. In Australia, in Ireland, the shutdown has started. Vodafone I believe have shut
down their 3G but three I believe don't have any plans to shut it down anytime soon. What's the reason like in some countries shut up? What's the reason? So there's lots of reasons. Um there's the cost of the equipment but also uh there's coverage. So there's parts of the parts of Ireland that really effectively only have 3G. So even on the train between here and Dublin, my phone was switching to 3G at points. So it's for rural communities. No telco has 5G to more than 3/4 of the Irish population yet. So because of the price, maybe the price of well it's it's price and its time. Uh 5G is much more energy efficient. 3G is very energy
inefficient, which is why people are keeping 2G and shutting down 3G. Also a lot of cheap equipment IoT devices rely on 2G rather than 3G and 4G but it differs from country to country but 1G 2017. So there will be countries using it and maybe Telos will have to say if you're roaming you must be on 5G but we're a long way from having coverage for 5G. So who was next? Just add that it's also down to lots use 3G for SOS I think is for certain applications because Australia had that problem of shutting down their 3G networks and just so the comment was that a lot of phones use 3G for SNS even though they're nominally 4G phones.
Yeah. Yes. So that's another reason that people don't want to move away from 3G because they need to upgrade their phones. But over time that will come less and less of an issue because that's just a limitation in the phone. So 3G 4G phones don't do proper 4G. But these phones are now 5 to 10 years old or more. Yeah, I just I'm just that but I have a question. It's also just in power 5G and power. Yeah. Um the question forms but I'm just wondering what your thoughts are. You were talking about 5G and the fact that it tends to web services more secure but if there is significant risk surface or surface in
the handoff between different delivery mechanisms. So handing over stations switching over to Wi-Fi delivery different frequency I'm just wondering how your thoughts are in that space.
So, one of the things you probably never noticed about mobile phones is that they keep working when you're moving around. You can move from one base station to another base station and the phone will be handed over. And with 5G, you can also move between Wi-Fi and an actual phone call and it will all continue. And the question was, does this introduce security risk? And I would have to say it increases the attack surface. uh how easy or hard that would be to exploit is a very interesting question and I don't know do we have time for one more I think that might be so so you were waiting for a while do you think because the
security that's why the connection So yeah, sorry I'm walking backwards and forwards. I'm half deaf. So the question was, is the security and 5G why we're seeing Chinese actors hacking American Telos? No, I think 5G is easy enough to get around with. What they're hacking them for is for records, billing records. So they can just just collect all the metadata. It's all in one place. They can get access to lawful intercept systems. They can see who the lawful intercept systems have been used against and they can use the lawful intercept systems themselves. So it's just Willie can't remember his surname said was asked why he robs banks and he said that's where the money is. Why a telos
broken into that's where the data is. [Music]