Conti Leaks and CARVER Analysis for Threat Intel Analysts

Show original YouTube description
Show transcript [en]
okay the title for the next talk is Cony leagues and car analysis for threat Andel analyst and um please welcome our speaker will baget over to you hey thank you for coming to the talk I appreciate it uh these talks are truncated from 55 minutes down to 20 so like Matt Foley I've been in my basement drinking three pots of coffee for the past few hours and I live in a van down by the river speed through this so compromise KY chats and Carver methodology first I'm will bagot uh CCE certified combat collection engineer for my V NATO soft days certified product examiner a whole bunch of digital forensics certifications started off working uh Financial technology was a coder
developer took that off my resume because open floor plans and coding don't work um went to CIA for 20 years did some stuff did some things met someone at another conference we're just talking about networking ended up getting a job for a couple years over in Belgium as NATO's cyber security instructor for the Special Operations troops there which ties into this uh worked digital forensics uh Insider threat for a large consulting firm with a company that may or may not have reduced vaccines I can't name them but you know who they are and from that I pivoted over to uh cyber threat intelligence where I am now and since they're not paying for the talk they're not paying for me to be
here I don't have to get legal involved so I'm not naming them so we're going to cover a few things we're going to talk about the KY ransomware group we're going to talk about the Carver methodology The Insider threat overview and then how well the Russia Ukraine situation some of the games they play with each other the slides are colorcoded a little bit if it's a red slide if I had a week long with you and this is a native classroom we had pivot we' do online training we'd actually get some handson the yellow slides are things that were discovered after the fact for this leak months or you know 18 months later which is relevant but it didn't impact what we
did when the leak came in so at besides you know you can have someone coming straight into cyber security who's never worked in the field they looking to transition out of what they're doing or you might have someone who's legendary like Jack Daniel who helped build the internet down to the ones in zeros for the routers everything so we'll start high level ransomware is basically malware that locks up your computer and for a very small fee of money with six figures seven figures they'll give you a data bat another variant of that that we've seen now the Russian conflict is wiper Weare for same methodology but instead of locking your data up it just wipes it it's like an
EMP electrom magntic pulse vehicle or bomb that wipes it out but it's a little more efficient a little clean it's cyber warfare it is what it is so K's a Russian ransomware group they're first spotted in May 2020 they'll do data extraction first exfiltration they'll name the company uh like I think it was Uber that was hit today by Klo and they'll shame oh they've been hit we have their data we can sell on the dark web if they don't pay us this amount of money to pressure the company to give up the information one of the things that came out out was they are a fundraising arm for the Russian government and it's not a small
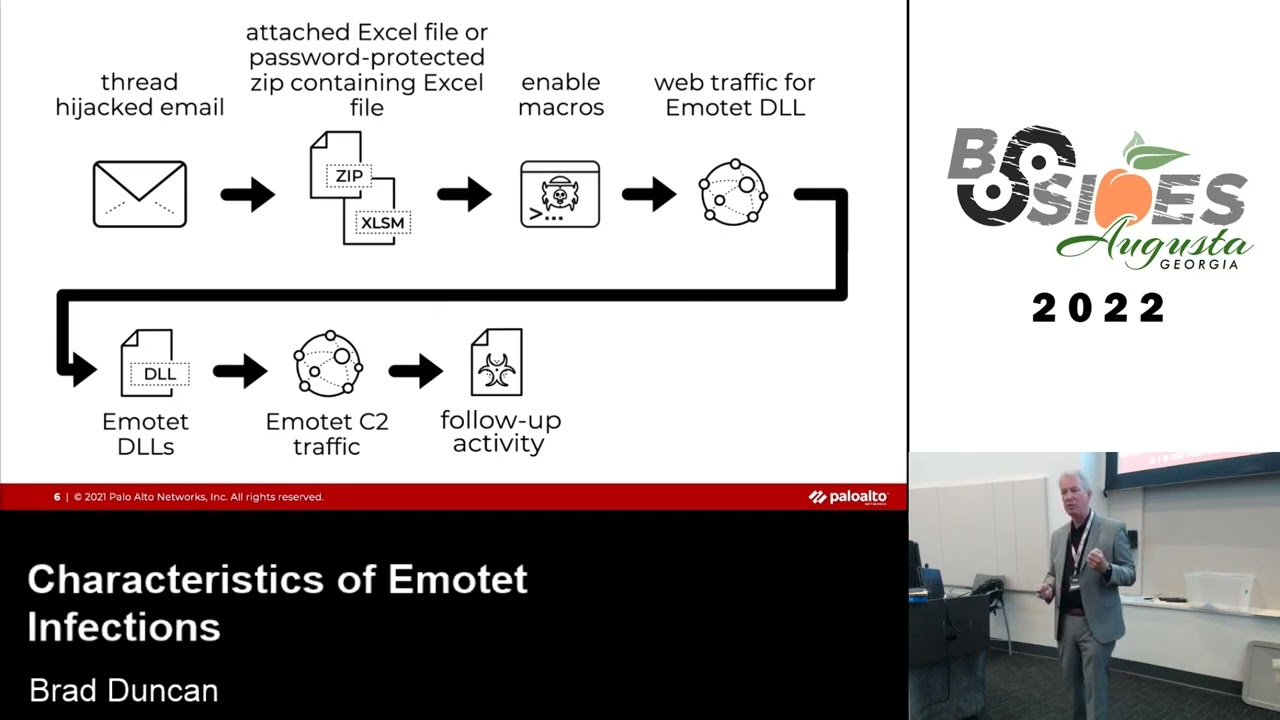
business Ki was was past tense the leader in ransomware $180 million in was it 2021 and that's not chump change for a criminal organization their standard methodology they'll te they'll Harvest credentials through spear fishing whatever else they'll get the credentials penetrate the organization make sure it's a valid account and then they'll Spearfish this is also mapped out very well by so many other researchers the malware comes in they get the back door they connect to their C2 command command and control server they exfill the data they give the command to lock it up once they're available they have Consultants to tell the company how much money they can possibly ask for for a ransom that's
reasonable and also they'll Target the insurance policy so if you have something like an Aon cyber insurance policy they've got the data they know for your policy limit is the last that top dollar policy limit just like a car mechanic oh your insurance is going to cover $50,000 for this repair to your Jeep the bill is $50,000 same thing but with ransomware all that said May 2021 the colonial pipeline leak any of the East Coast people in here impacted by that few people long story short and we don't need editorial they weren't hiring for their cyber open cyber security position i s they were hit by dark side with ransomware locked up the payment system
so Colonial pipeline went dark for about a week seriously impacted the East Coast all it took was just one fishing email to get past the defenses to load the malware all that said I know I'm going fast but we have a lot of material to cover couple of cool things that came out teaching over in NATO soft of for the troops and it's a whole Coalition which is bizarre to have the former Soviet lot troops in a skiff they're now our allies whereas before I couldn't talk to you socially but now you're one of us you're in the skip I'm teaching you it's bizarre so a couple of cool things that came out cool as in I respect the technique I
don't like the conflict but long story short Ukrainian troops landed in near the border Russia owned the cell tower whether they penetrated it where they owned it whether this fake fake cell phone tower like a stingray I don't know all the imy data was gathered the phones come up they hit the network the Russians collect the data they find out who you are who your family is they send a text to you that you're going to be shelled they send a text to your family your son or your daughter is going to be killed in the next 30 minutes if they don't move the parents call the kids they text the kids they geolocate where the troops are
it's electronic warfare it's seant it's psychological operations again no one was killed with it but it's an absolutely brilliant tactic in the 21st century so that was something Innovative the big takeaway there the tldr is don't take your personal cell phone into combat that's you'd be surprised uh there was another slide for cut for brevity Ukrainian researchers would have fake Tinder profiles to do social media elicitation on Russia to find out troop movements morale things like that and uh one of the things that led up to the conflict Ukraine released a list of roughly 600 KGB sfb or svr officers to the world here's their name phone number all the personal information of them whether or not
they're actually KGB I don't know they could actually be the third under Secretary of Commerce for Russia working in Kiev doing nothing with Espionage however they've been named in this so now your named the locals don't want to deal with you because you could be a hostile so this effectively neutralized is the Russian intelligence collection off over there I who's this from this is this is your comrade no D rinsky it's actually good okay so the red slides are where we would pivot and stop and do a couple hours of exercise we're not doing that here because we don't have the infrastructure Belling cat otheros researchers found where KGB officers would go to other countries execute dissidents murder them
return back and they would have oh it's on YouTube it was terrible trade craft they identified we could go through that leak and find who they were the soldiers would dig into this to find the operations that were leaked where it would Branch out find out who's going to Siberia for po tradecraft we don't have time for that here but that's where we would pivot go and a lot of ukrainians are saying I'm telling you right now that moscovite Foreign Service Officer he is not he is not real okay so I'm working now cyber threat intelligence large infrastructure provider you know who they are can't say them legally but we're concerned that if we're hit with this leadership's
concerned CE is concerned sa is concerned that if we're hit a lot of corporations are hit it's going to make majorly impact the US economy so CA likes to say we have our Shields up for this kti sends a message saying we are fully behind Russia we support Russia hund no cap for real for real yeah my son just cringed at that one and then well we don't really support Russia two hours later well we'll support ourselves they're backpedaling well that was kind of vague and unconvincing the internal researcher who's a Ukrainian working with Russia couple of days after that announcement sends out an email to bleeping computer if your cyber threat intelligence basically that's where all
your data comes from saying hey I'm going to leak all this data it's going to come out the next few days here's his unique file name it's going to come out and you're going to like it first and formost like Clint Eastwood said in the Good Bad and the Ugly if you're going to talk talk if you're going to shoot shoot you don't do do that so he leaked out 6 60,000 messages several gigabytes of data again we would pivot here and go from who's following this account who opened the account who's bookmarking this and who's quoting that's when to give a lot of information of cyber threat intelligence because the average person's not interested in
this the leaks start coming out and as you know this violates Twitter terms of contract or X's terms of contract of what data is actually available English version comes out I don't know how long it's going to be up we're doing shift rotations I'm former CSA uh CIA my manager is former NSA White House comms it's a heavily Military Intelligence group themed background group so we understand we've got to work shifts in this this isn't 9 to-5 day work for the first few months it was fun no it wasn't fun so all total this is what came out everything and when they said they weren't actually working with Russia the results determined that that was a lie there are links this came out
last oh wow times lies last month of what was actually there very quickly because we have about 9 minutes left The Insider threat usually if you think of the data Leak with a dam holding it down a breach is when the dam break sta comes forward it's usually an external actor something like a solar winds misconfiguration an Insider threat someone like Edward Snowden Robert Hansen giving leaking out sensitive data to hostile people nebula bringing the ship in from wherever Thanos was and people do use science fiction as a reference because that's not copyright it's not an NDA so we can go to that as a common ground so people don't expect this to leak when you've got a breach like Klo
and move it organizations are still being hit with this finding the weak is just like The Shield at Scarff was now your traditional motives for Espionage mice money IDE ideology conscience compromise or ego or excitement so this definitely hit ideology conscience and probably a little bit of ego if I leak this I can take down the Russian fundraising machine the is Rascals which is exactly what the email fishing does so we have an Insider threat this is a one-time event he's lost his access it's directly attributable to the only Ukrainian on there the damage is unquantifiable at least 180 a year they were up to 180 million a year before the leak again going back to the class
method we would discuss how they stage the data for exfiltration we look at how you could determine they us his corporate laptop does he get a corporate there's a lot of questions to answer but this is raw data that comes in from a battlefield even though it's not traditional finding USB drive in a sensitive side exploitation is still data from a conflict that leaked to the corporate world we have to determine if it's uh what the impact is if it's disinformation if it's manipulation or if it's actually true good data we can ingest so who was KY they're gone now we haven't seen anything on Cony they've been relabeled other things the methodology I I used once I had the
data was the Carver method it's from OSS office of special services in World War II it's what we taught the French how to identify the key points for subtle sabotage with the longer method I might be able longer time I could talk about some of that but given this is on YouTube and it's teaching people how to do sabotage probably not something I should teach out for the world but this is offense or defense to find the weak point so you got criticality accessibility recoverability vulnerability effect and recognizability but out of that you look for the key piece just like the meme of the One XL Spreadsheet supporting the world's Finance system this leaker knew exactly
the key thing to take out cont just like air conditioning runs besides and deathcon air conditioning goes out no one's sticking around to these talks same at Defcon God the smell but for our purposes with that methodology criticality and effect if these two things go down what would happen so just like the Battle of Scarff if the shield goes down they're not expecting the rebel Fleet to actually physically Ram something that's an out-of band technique that hadn't been done before per Star Wars lore that's the key weakness for the Empire so we've got a chart and we go through and rate what's the most important thing so the scale of 1 to five highest score is going to be
30 lowest score is going to be six most important is their source code their core designers and some of the infrastructure credentials are you know a dime a dozen the staff they can always get more staff but the core developers that's their weakness our weakness are crown jewels all the financial information that we hold the personal information the way we handle it our infrastructure the way we process what we do and our reputation if we lose our reputation it's a major part of the US economy and I think the kids would say it'd be shook but that's how we line it up but very quickly we knew this is what K is coming after email databases source
code in Insurance there's a screenshot given this is a lot of leaked personal information I share what I can they're going for the banking information how do we Define it as CIA it was foreign of Interest new clandestinely Acquired and authoritative in the Cyber threat intelligence Financial world is it hit financial industry is it of interest is it new is it copied and pasted from belief in computer and is authoritative so we've got to look at the security the time the imminent threat what happening with this data it's been leaked we have all these creds out there we're not going to go online and search because this is a traditional Honeypot you wouldn't put your
information in one of these you wouldn't search on the dark web this is a common methodology criminal actors use to get the core information of flots of interest you tell me what you're looking for I'll tell you if I've got it they it's never found but they're building that backend database so the core of it is are we targeted our core business functions the then there's leak creds and then the cdei CPS and out of that that comes down to this came out last week roughly 87% of ransomware attacks fishing attacks are because of compromised creds so using this method I know that if I can find going like goes after like if I can find
if my company's targeted our Core Business function is targeted first and foremost if we can find there's creds in there that are leaked then I know what to disable what to turn off and that's going to lower our risk Vector a lot of credentials out there I can show you this that's what it looks like it's redacted it's redacted there's a lot of strong passwords they hit password managers it's shared in clear text it's leas in clear text and just adding a one at the end still isn't secure so the conf the operator they work off fishing vulnerability sprads and spear fishing is an inside threat to get their C2 up there that's the methodology yes this is a diamond model
I freaking wanted use that s that you've drawn since elementary school for the first time in my career so there it is that's your diamond model so importing the data I didn't do this on my corporate Network because I like having a job I don't know what Ki has in their chat I can almost 100% guarantee it's going to get me fired if the right filter hit it I did it out of band made copies made backups sort through it to see if we were listed first and foremost all we hit reports go up saying we use this method we're not listed we're not hit here's the credentials the next key thing for the other 12% not only do they document the
vulnerabilities going back to 2015 they list this companies vulnerable to the cve here's exactly how to do it step by step so it's not a oh let's wait for vulnerability management to rep patch This months later this is okay a doesn't work they immediately pivot to B the speed of ransomware versus the speed of business now the tertiary analysis as we're starting to wrap up there's a lot of stuff we can find here the after action threats we can find how to reverse engineer this we can pivot on establish usernames for ENT look for the leak Bitcoin wallets using entf framework. comom some some links there but immediately is my organization at risk are we being hit and if I've got that
88% coverage 87% 89% coverage then the rest of it takes a a lot of the pressure off there's tertiary analysis that's great for incident response it's great for the tech teams how they launch their domain controllers but the immediate are we at risk this is great but if I don't have the door locked of managing my Elite credentials because that's the first thing I sorted through it doesn't matter you can see this came out last week they go for insurance programs for insurance coverage VX underground a year and a few months after the fact all this is out there it's fantastic but back in February of 2022 my concern for my organization is I've made sure this leak isn't Russia is
not targeting our financial infrastructure so the tldr secure your own organization first document everything as you find it just like everything else the carbon methodology it's not there is a software program but it's the mindset because tools break tools change prices you lose vendors look at at in case with digital forensics they used to be the king of forensics now they're gone so as we're wrapping up if KY can take care of their own ransomware operators take a vacation holiday for yourself then you need to take one for your pee and the next steps I'm going to go back to the room change clothes and start looking for is kti affecting the US election because no one else has done
this I'm not going to assume it's been covered I'll take care of this myself and and I think we're right on time so
caffeine I think we can do like one one or two
questions you you blitzed through that is there a longer version that's recorded somewhere that is posted because that's awesome but I would love love to sit through the 55 minute version of that it's that with more examples slower talking and I don't sound like the guy from the Micro Machines commercials from the 80s but is it posted somewhere is it what is it posted somewhere not yet the talks will be on YouTube and um yeah here we go my email is 10x engineer.com yeah like if you go to mail.com they got like 200 domains when you apply for a job it's something unique like at consult Instead at gmail you send it a little bit better and it's
free any other questions so is that data set available yes to everybody yeah and so you're you're sort of advocating like hey it's a good idea for you go check to see if you're on this list if you're would it hurt yeah thanks I was just kind of okay I mean I no no no I I I just want to like read the tea leaves a little bit Yeah Yeah know kind of over caffeinated this morning thinking I haven't searched that data set for the other thing I'm working on yeah no one else in this group has why not yeah excellent thanks for the help okay thank you thank you will that was great thank
you