Malvertising: Under The Hood
Show transcript [en]
she is thank you guess straight thing so if thanks for coming along so we I talked about a lot about malvit izing different forms of advertising the social engineering aspect of how people get adverts in front of you and everyone else and myself included and I thought it would be fun to talk about the ways that people get malvit izing out there are the kind of tricks that they use behind the scenes to infect as many computers as possible so I mean you know where does the word malvit isin come from it's combo obviously of malicious advertising malicious have the thousand views of online advertising to distribute malware or scams with little or no user interaction required so
that's what malvert isin is and in terms of you know the numbers the bums on seats that you can affect with one single outbreak of malicious advertising these are all websites that have been affected over the last year two years the big names on the MSN comm monthly traffic roughly 1.3 billion New York Times 300 million BBC AOL nfl.com these are huge numbers and a lot of the the attacks on these these websites these balls are very easy to pull off there's no real financial outlay on the side of the scammer and in terms of the companies the the you know promote advertising have their own advertising platforms it's give you an idea of the
kind of problems that they run into Google Adsense they put out some stats a year or so ago they haven't updated these at don't think so for now this is the best we have to go on so in 2005 Google chose the disabled 780 million ads that they thought were you know broke their Terms of Service were rogue malicious pushed bad things 60% increase through 2014 to the first half of 2015 and there's an awful lot of rogue ads floating around on mobile I think less than I had something like one in five mobile users now have an ad blocker installed on the the mobile device or their tablet so you know this stuff is
quite pervasive these are these are some stats give you an idea from last year in May 2016 the bulk of the the files that we would see pushed in an attack was ransomware files 61% of all the attacks that we would see in our our databases are telemetry and everything else you know you get some you get some generic malware backdoors and Trojans and all the rest of it but the bulk of it would always be ransomware and that's a trend that's carried through now to 2017 you know again you can see this is this from January through June of this year the bulk of this is ransom work the Greenville SC the yellowy orange bar at
the bottom the green is the the add fraud component there's a bit of a tail off in June for some weird reason but it's it's fairly consistent sort of the marriage usually rogue ads and ransomware most of the time and in terms of the old sliding control scale bit of a show of hands who feels that they're they're reasonably equipped either at home or in the office their network to deal with a malware or spyware outbreak you know would you say you're 90% sticky handle which you know you feel 90% comfortable that you would probably stop there okay Script blockers whoo-hoo everybody everybody put the handle script block isn't disabling page elements I mean how
many of you've got something in place to stop a rogue script on your desktop or you so there we go quite a lot of hands actually normally it goes the other way around normally everyone sticks the hands up for the Vav stuff and then it starts to go down exploits who's got like a dedicated tool in place to stop exploits there we go it's gone down again a bit and finally adverts who's got something on their browser their PC whatever to deal with adverts rogue ads there we go so quite a lot of hands see the the biggest two problems that we see with malvit izing are exploits and adverts and a lot of the time especially when I
want to do this when I go out and do talks talk to people the majority deal with the malware spyware quite a few of them have script blockers in place but the exploits in the adverts fall by the wayside unless they've got you know an Plus or something in the browser it's just it just sails right through and in terms of the basics this is what you standard desktop would look like in 2006 pop-ups and ads and you know you've installed django search tools and now here's 6000 adverts for you to get your teeth into and it was all about you know as much bang for the book as they could get they would Jam as many of these things on the
PC and as short a time as possible to make as much money as possible from the impressions occasionally you would get installs but more often than not it was just ads galore and there was no real salty to it and then as that as the years went by this is from 2008 where they started to realize that they could make more money if they tried to entice the end user with some joong rather than just jam it all down the throats at the same time so you would get things like this free online Batman game ed this is this is a Google and here it goes a Batman game dot info looks really cool it's really nice we're gonna play there
you download it and of course it's targeted to people on a video game comics website installer Xango ad were they start popping adverts and what you actually end up with is a demo version of a completely different Batman game it doesn't even look like that it's it's a game from you know a couple years earlier and this was the general bait and switch that you would see so they've become a little bit more subtle they start to rely on social engineering a lot more and then by 2007 you've just got these weird erroneous fake little ads floating on on you know msn.com or what have you it will be a completely fake ad it'll redirect if the sort of
junk another one you know it they're really moving off to the side lines they don't want to draw attention to themselves especially if they're not pushing Iran somewhere but something that you know they want to keep on your system for a while make as much money as they can before you finally clean off the PC so this is a fake used-car ad trying to launch an exploit attempt so this is this is the basic weather it little o really popular with malvit Isis for some reason so here's here's a fake one that was floating around in Germany if you fit the demographics for the kind of people that they would like to infect they would pop this it would redirect
you to the the gate the gate is normally all-important we'll talk about that a bit later but it's it's effectively the gate that decides whether you know you you get redirected to a nice safe web site because actually they don't think that your click is worth the cost to them to get you to the the exploit site or whether it sends you to a pile of garbage in the form of you know one of exploits they might be looking for a specific version of Flash it might be an IE exploit might be javascript silverlight or some other thing and then finally you get hit with a really horrible picture of a piece of malware never mind
apparently murdering MSN Messenger going so that is effectively how these drive buyers work but they normally hinge almost exclusively on the gate but the base that gives everything a big yes or no I don't really like lots of words on slides but these are kind of important so we'll go through them quickly just in case you know familiar with these terms the publisher is the website so if I've got a website and I want to put some ads up I'm effectively the publisher that's displaying these adverts the creative is the ad creative so I as the publisher I'm going to roll out some creatives video stats what people like these words the impression obviously if you've got a
website whatever you familiar with impression it's how many times this thing is viewed by one person the ad call the browser requests the triggers and impression fairly straightforward RTB networks these are real time bidding auctions for each impression so the way ads used to work is that you would have really elaborate drawn-out ways of purchasing ads and buying units and there were quite a few checks and things in place I used to work with a guy that worked behind the scenes a lot of ad networks and so of you know millions and millions of dollars getting shuffelin shuffelin around the place every day and it was you know there was some checks and balances in there but with real-time
bidding it's all pretty much instantaneous so it's it's more a thing to say I don't know stock trading markets things like their financial markets so you will throw all these bids in in real time and it can go down through and put somewhere to the nanosecond whoever gets the best bid and instantly displays their ads on the websites based on you know the the keywords that they've chose that demographics of the big drill down into which is great for the advertiser because you're really getting like a direct connection there with with you know the person that may or may not buy your stuff but it's also brilliant for scammers because it's all instant it's very difficult to control these
outbreaks when they happen it's very difficult a lot of the time for the the RT beat networks to work out who exactly is is pulling the strings you know are you a real ad agency or your scanner is this you know is this one big wine doctor to infect a bunch of computers and the CPM is the cost per thousand impressions usually so a scammer depending on the network a scammer can pay you know five dollars ten dollars and get maybe five six seven and thousand impressions for that one ad via one of these RTP networks so there's a tiny tiny outlay in terms of rolling these things out to victims and you know they're in ever the long haul we you
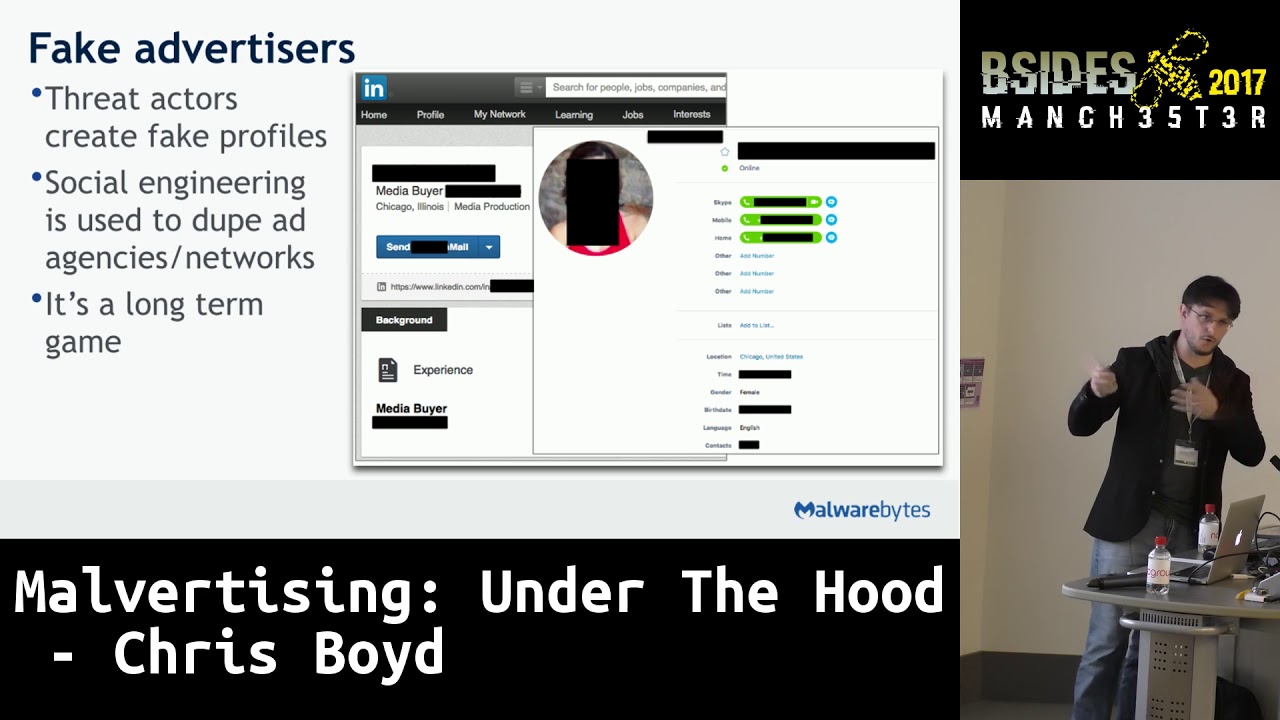
will see fake creative media buyer agencies on LinkedIn and other sites they will have a whole bunch of genuine looking Facebook Twitter profiles some of them will set up fake business entities they'll slowly but surely start to get in touch with the people of the known players in the ad space the ad industries and they just work in the way up to when they can actually get on some of these networks and push out some of these these fake ads to people and you know once once the objective is complete that they basically torched these these profiles at the ground and start again with the the fresh batch that they were cooking away in the background the whole
time so domain shadowing how many people familiar with domain shadowing there we go we got a couple domain shadowing is basically stolen identities so this this begins before the malvit izing before the dubious head low levels this is where I don't know you you you run a business you run an ad agency you might run a solicitor's firm it doesn't matter I'm gonna send you targeted fish campaign I'm gonna send you all sorts of dodgy links on skype I'll send you fake invoices I'll send you four Geling domain renewal notices they're quite popular with domain shadows and as soon as I've got the login for your account I'm not going to log you out I'm not
going to change it I'm not going to send it to anyone I'm basically just gonna start logging in on your web portal and create lots of dubious subdomains and then from there I'll host the the rogue advert I might host some of the malware files and I'll just collect hundreds of these things over time so again if needs be I can just burn them to the ground and start again meanwhile the poor person with the web site becomes on the you know comes under immediate suspicion they look like they were the one doing the scam it's always sort of morning meal for websites so you know they're very stealthy ver very quiet a lot of the time they favor HTTPS which
we'll go into and it's very very difficult to work out exactly who was behind this kind of scam and obviously the the legit business behind you know that's getting a chain yanked if you like is the fall guy and it's you know it's quite damaging to their brand reputation so a lot of these these guys they will go off and make their own creative ads you know they'll hire people in cottage industries to create really nice-looking fake ads they don't make them completely fake because a lot of the ad agencies out there will you know they'll they'll know if a if an image has been used for a scam they've got ways to track down the imaging
that's being used for this malware campaign will will cancel that so they will very subtly rework real ads so these are all real ads that they've gone off they've fiddled with they maybe move the logo around Thompson's is no longer in store and online its online and in store stuff like there and as a whole weird wacky ecosystem with people being paid small amounts of money to come up with these these fake ad banners we've seen thousands of these things and then once they've got those they then start rolling them out on the shadow domains so again this is this legal firm from earlier on legit website they even cannibalize the text on the site because
they're so lazy so the text that they will Jam into the fake ad banners they've just gone to lifted it from their website because why not they've a shadow of the domain using free SSL so again these websites and still just being a HTTP connection they're encrypted and we'll go into the reasons for that in a moment they've got a 1x1 pixel tracker behinds the fingerprinting code and then that chunk of code in the black box in the middle looks for certain security products and if that security product is on board again they feel that it's it's less trouble to just leave the PC and go and affect somebody else because they don't want to waste
the time the effort the cost per impression running into a roadblock because they have a sandbox on there what else have we got on Kaspersky and it's not just you know a viii tools like so folks whatever though they'll also look for things like Wireshark because they're not just looking out for regular home user with with an anti-virus installed they're looking for security researchers trying to shut them down here's another one here's here's a law firm that were they had this you know there's fake ad banner hosted you can see on the second one though it's it's checking for packet analyzers debug is pcap and so on you've got the angler exploit landing page again and at the
bottom note it's checking for a different set of security products BitDefender malwarebytes Avast and a couple of others and again they will just they do not want that traffic because it's it's wasting their morning effectively and we see a lot of domain imitators I've seen this print out so many ways I had AB Galasso since one called it ad ghoulish once which was a bit weird sounds tasty and they will they will specifically target these industries where it's very hard to pick them out so they a popular target are these essay writing websites so a lot of these you know the legit in the sense that it's not going to infect you will do weird things with your information
but they are sort of built in bulk a lot of them look the same a lot of them use the same branding and they're very cookie cutter so these guys will imitate these websites again you can see that they've they've set up a certificate issuer in this case let's encrypt and then they will they will push these websites wire adverts and they will they will try and redirect you here so that you can see a ghost down the side there eventually we head off with a streamer exploit Keith then the landing page and then they're trying to nail you with a flash exploit and again these are all from these these shadow domains these imitation web sites
really sophisticate the fingerprint and going on to make sure that they get the traffic that they want to infect and again cloned adverts you know I mean most I'm sure if you see most travel adverts and most travel websites they all look pretty much identical and you'd see something like this pop up this was a rogue ad flown from a legit site you would never know this was bogus and then the of course the iframe starts to work its magic and they try to go about with exploiting me the system that's landed on this advert so in terms of how they fly under the radar everybody's moving to HTTPS now which is great you know it's all a bit
more secure it's it's a bit more difficult for people to try and you know snoop your traffic and all the rest of it but what this this this means is this is an advert that is very commonly ad networks will just use HTTP although all the traffic is plain so it's great for us because you can see the RTP network you can see the DSP which is the demand side platform what that is is effectively a a type of tool that allows you to place your bets more easily on a real-time buying network you can see the marketplace involved the product the various websites a lot of the time you can see tracking code which leads back
to affiliate so you can get them shipped down everything is right there in plain view so of course then they do this and they move to HTTPS where and you can't see anything anymore it's very difficult to track it down you lose all those sorts of third-party tips because you do tend to get a lot of people who've been affected by one of these scams and they will get in touch with a security company say oh this happened I was on this website would you like some logs brilliant you know so it makes it very very difficult when all that metadata has vanished and that's why a lot of those sites are always trying to use the
the free certificate services they will pay for them if they have to but there's so many free service was out there now that it doesn't really make much sense for them to spend additional cash VPN traffic they hate VPNs so if you visit one of these ad networks again in the same way that they don't want you if you've got security tools installed they also do not want you if you've got VPN run and so this is you know you'll end on a website you should have seen an advert you're seeing this page because you're using an anonymous proxy in order to protect our advertisers we will not display real ads to the website owners
the real ads will be displayed to your regular traffic and will be paid brilliant great you know fantastic I'm not losing money on these ads so of course you visit the same website without the VPN and you immediately redirect it to a tech support scam so you know VPNs are in a really weird way to combat a lot of the more common malvit izing effects out there so they don't like those so for example magna gate this is an example of the way these gates fingerprint you so here we've got a website called roof Ted calm which was part of an outbreak not so long ago they issued these rogue and let's fire the XML page there you hit
the the Magna gate where it made a whole bunch of decisions about who you are where you're coming from really drills down into your browser operating system everything they can get their hands on to the side whether they're going to send you through the the magnitude site and envy you know the server waiting for you at the end so it's very very trivial as researchers to the spoof aspects of you system so a lot of researchers will for example you know they'll they'll try make the browser look like for example Internet Explorer or it might be in a VM it might be on a proper metal box whatever because they want to pop this this IX boy but I knows waiting at the
other end of a chain but with Magna gate they can look for example for the kind of fonts that you've got installed on the system so if it sees the eye on this person's got you know Mac fonts installed via they got Internet Explorer on they will just send you off into the void because they don't want to waste time because they know at that point but you're probably a researcher trying to trying to get them shield down so here we've got another Magna gaze check this has been around since about 2012 I think early 2013 and it's sort of developed as it's gone on so this one's a bit more straightforward they're looking for the
Kaspersky virtual keyboard so if you show up when you've got that room in which is obviously part of a security suite they will send you away they don't they don't want your business there it is there at the bottom can it run crisis they even check for the name of some video drivers this is a more more recent one this was one we found a check to your local IP and then started digging into your various video drivers and a couple of other things we're still not entirely sure why they were digging into this particular info on this this scam because it didn't ultimately seem to be rel to what they were doing hmm possible
it's possible there was none of that involved in the actual sort of junk that was deposited at the end or it is possible of a they you know they are trying bits and pieces of these these new Texas technique sales or unrelated scams and then you know they'll they'll wheel it out properly next time a lot of a lot of adware groups used to do that back in the day hmm yeah it's possible it's possible and I'll never know if this thing ran crisis but anyway and of course vm's you know there's so many security researchers will will fire off Windows XP in a VM and you know they ROM no malware and they're surprised when it
doesn't work because obviously so much malware now you've really got to throw it into a sandbox because it will be looking for things like VM Tools virtual machine files and folders some of it some of the pieces of malware out there will look for you know the default Windows XP background I mean who really know I leave it all because I like it but most people most people would get rid of it so they know if they hit it if they see someone running malware on an XP box would burst and there's you know nice green grass blue sky black background they know it's probably a research and they know someone's trying to run the malware and they'll do things
like check for you know mouse movement so they you know as the mouse just sort of not moving while they're off waiting for something to happen and stuff like that and by the same token some of the exploit kids some of the the malvit izing scams will check for XP and generally you know they don't want to know because they have a suspicion that it's probably someone with a VM or someone with a real box that's that's testing to see what's going on so generally don't bother with XP if you're gonna if you're gonna you know dig into malvit izing so to the to the pr 'mobile these these are grave these are fantastic because you know when
you're dealing with with malvit izing a lot of the time you bought heads with the ad agencies the advertisers and they're all very you know oh it wasn't as it was you know it wasn't a big deal it wasn't a problem everyone's at fault for running ad blocker you know that it's all on them see how this is great or small number of users were infected by malware this is this is one of the common things that you always see when there's an outbreak a silencer yeah I was only a small number I wasn't wasn't too many people well most of these ad networks have no idea what the scammers were up to which is
what enabled them to push this junk in the first place so this is this is one scam from couple years back where this guy was pushing all sorts of junk vile adware and adverts and things completely lost track of how many installs he had the ad had where a company that was supposed to be able to track and monitor how many installs have gone out they couldn't really give a proper figure and they've got actual systems in place supposedly to check for these things and you know if I go off and buy a bunch of rogue ads throw them out on a real-time bidding network and now a thousand PCs are parked they don't know they've got
no idea how many of these people are out there who are genuine who are fraudulent it's it's a nonsense for the most part only a few site visitors complained I love that walnut brilliant that's because their PC looks like this by the time they finished with it I mean I think they were expecting compose my smoke signal or carrier pigeon or poor after they've tanked a thing with ransomware and malware and all the other garbage they're probably not going to get many complaints from the people that were immediately affected because you always see they go for damage control they get the quotes out to the press and then they never comment on it again and
the quote goes out you know within six seven hours and then they just hope nothing else comes off afterwards and most people who would have been affected by this thing you know they just go off complain fix the PC roll back whatever and then you know it doesn't come up again and I'm sorry but this is what a lot of people's PCs look like I only I only stick with you know two or three browser windows at a time because this drives me nuts but you know lots of people do take advantage of all the RAM and everything else and you know this this is very valuable to some people so they do this and if you've got all of
these things sitting there on your desktop and one of those pages in the background have to load an ad or refreshed in the background and n load that a bad ad and you know this this is a slice of some browser history where this this person's gone through you know 12 13 websites in it in the space with ten minutes plus a bunch of Google searches you've got all of that info there you've got no chance being able to pinpoint which one of these sites did it so you can go off and complain especially when the mowers that they're doing this and waiting and waiting and waiting to pop because you know they don't always trigger instantly it's
normally beneficial to wait for a while and then pop on the system you know it always seems to surprise the ad networks on the ad organizations that they actually seem to know what they're doing and they don't actually want to be caught in the act so in the same way that you you'll stick a piece of malware in in a sandbox and the sandbox sort of distorts the malware's idea of time space and everything else so it thinks it's been in there for you know a couple of hours oh I better run now when actually it's being you know a couple of seconds it's the same with this you know if this stuff is designed not to not to be
tracked back to the source so of course these people don't have lots and lots of complaints coming through this is brilliant you know they're killing our lifeblood it's censorship well I think the the I think it was an Internet advertiser organization that represents the ad network so you know they're they're holding content hostage when they run these ad blockers it's disgraceful if they're thieves you know holding the content horses are they not holding the content hostage with ransomware the popped as a result of their terrible you know tracking abilities but they they you know you I'm sure you see in the news all the time these ad networks absolutely despise ad blockers which leads neatly onto
fighting back because most people generally now have an ad blocker there because they don't want to have to be dealing with all this mess from do you know the fallout from one single malvit izing attack so you know don't back to 2006 we used to get send letters from people like actual old-school handwritten letters incredible through the office and you try and read these things and we got one from one of the the so-called mom-and-pop stores in the you know middle of nowhere in rural America and it was this three-page tear-stained missive from this lady who was you know I've saw you guys talking about this stuff on the Internet my wit's end every time we try and sell
a product on our on our website we get these Xango pop-ups and these director revenue overlays and for a cheaper sale and we lose the sale and we're going out of business and what can you do and you it's not sitting there with these letters god what can you do and as with many things in tech over the years the the website pornography people sort of led to charge so this when when these ad where vendors started to get on the radar of the the the porno sites and start costing them sales they started to plunk some code on their web pages so you'd arrive on these websites with Xango installed and the same as the you
know the scammers not wanting the the the research or traffic they didn't want anyone hitting their site the heads angle and uninstall because ultimately it was costing them money so that you would get sent away to this page they would tell you the install zone alarm this stuff is rubbish we don't like it uninstall it then you can come back and see all the pornography you've ever wanted to and this you know these kinds of arguments raised back in the day they still do now and you know now in 2016 browsing is incredibly schizophrenic visitors from one website popping two messages simultaneously on the left the site saying you know nobody likes ads we know there's bought without ads we don't
we can't exist please pay as money so we can continue to give you content and then at the same time if you've got our block plus install they're telling you hi targeted messages this like to be known to show targeted messages if you have was installed do you want to hide the targeted message and you know it's this is very confusing to people just trying to go about the business browse on websites and not get infected with garbage so you know you get these these ad blocker blocker blockers I think that's correct so this is this as an extension that you know you you visit the website now and and it's you know you get the paywall or you get the
screen saying you know we need this money to survive please block your ads and then you can view the content so people start with this weird cottage industry of locker blockers so you would install this tool it was claimed that it would bypass the detection in place on the website and allow you to see the content without being hassled or blocked or anything else so of course a lot of these were actually rogue and installed malware themselves this one specifically we installed we you know we went to one of the websites that it was supposed to bypass and we got possibly the world's biggest you've got a ad blocker installed go away message I think I've
ever seen in my life so this one wasn't very functional and a lot of them actually were just designed to push malware ironically by some of the the malva ties and groups so there we go and in fact there was a there was a company the provided code to webmasters not so long ago where you know you could you could display these messages to people saying you know you've got an air block oh please switch it off and they were spear fished they were completely popped and then their code was altered and pushed out to all the people that were running the code to say you've got an ad blocker installed please turn it off - redirect
everybody - so a piece of malware so it's it's it's really quite bizarre with sort of returns that the the the great blocker Wars of 2016-17 I've taken quite frankly and you know malvit izing is is a bit of a weird one because you think back to the first slide we certain malware and scams because they're traditionally malvit izing is all about the malware but we're seeing quite a blurring of the lines in terms of what would be considered malvert izing we're going to look at some stuff now that I would consider malvit izing even if there's no you know malware specifically involved so directive it anyone familiar with director bill payments thank goodness okay so these are you know you you don't
know about you've got your phone you want to pay for something it might be a charity thing it might be tickets or something of any really but you don't want to mess around sticking in your car details on your phone because it's a pain you don't to fill in your home address and everything else because it's a nightmare how do you pay for stuff especially if you don't want to throw in your car details these director bill services allow our webmasters so they're the merchants effectively the set up your and then you can use this to pay for something online with your phone and the the the payment is taken directly from your mobile phone network
and they then pass the cost on to you so generally there are very rigorous checks and flows with these things because obviously it would be a scam fest so this is this is a good example of it so you know you have to physically enter in your mobile number hit by now you'll be sent a confirmation SMS and then you have to click the link to you know to confirm that yes I want to pay this morning and that's generally how these things operate or to be more precise that's how these things are supposed to operate because lots of these things we're getting jammed into rogue adverts in 2015 so actually I mean it's been going on for
years it's incredible you look on forums people complaining oh my money's being taken from me I don't know what happened and you you know you're sort of you see people are kind of look at these cases where they've posted on forms you know yeah pull the other one but now this actually happens scammers were able to bypass some of the less rigorous director bill services they were able to redirect you to blank pages on your mobile so you'd visit a a web forum completely legit web site you'd be redirected and you'd be expecting the usual pop-up or whatever and you know give us your email address sign up to this and yeah sure whatever close close
to have problem solve the test device we had was redirected to a completely blank web page no content no indication that anything had happened so it just looked like a dead advert redirect a couple of minutes later a text message through you know you've paid five power for one entry click here to view again no thank you and there's the 5-pound that was taken directly from the the mobile network they basically managed to leapfrog the whole checks and balance process and take the money I mean this is effectively apex malvit izing they says you know they've got rid of the gate they've got rid of the malware they've got rid of the lovely designed pictures
they've got rid of the the domain shadowing the phishing all of us just been thrown in the bin and they're just sending you to a blank page that immediately takes 5-pound from you and the only way to get their money back you have to contact the merchant who is the scammer give them your your name your age your address and a bunch of other stuff along with the mobile number they've already collected and hope that they will send you a check for five pound and not do horrible things with your information you know this this is amazing that this this this is able to happen it's incredible not quite as incredible as this stock photo which is
astonishing well this isn't actually far from the truth like I do a lot of work in virtual reality and augmented reality so virtual reality if you know for me is just you know plunk our headset on and it's lots of weird fake things augmented reality is is bolting things onto your field of vision so you know Terminator 2 and he sees all the the scans of all the people he's able to determine to pulp and all the rest of it but this this really isn't that far off from the truth virtual reality headset cell will flee 3 3 million ishik water not so much the HTC vibes and you know the oculus a lot of the cheaper ones that you see in
garages and everywhere else where it's just basically stick a phone in and then all of the the VR stuff is done through phone apps they're really popular bought wearable technology and augmented technology is 7/5 like 33 34 million units a quarter I've never actually run into any of these people but they're out there and they're buying this stuff and augmented reality is being jammed into all sorts of places that you wouldn't expect so you know there's already cars out there at the moment that have really basic so-called augmented reality and then you see these lovely mock-ups of you know you'll be driving along and there's overlays on you you know your windscreen of blue lines you know almost
like Google Maps has been jammed onto your windscreen and this is technology that's being played with rolled out now so this this is this is a sort of rough approximation yet to GPS but we'll just pretend it's it's you know it's it's a really basic form of AR on you you know you your dashboard boom as you've seen in the press and everyone else this stuff can be hacked they can be tempered where they can be played around with you can get ransomware and specific cases where people manage get ransomware running on their you know their internet connected car so what happens when these wonderful people pop back off on your dash and then what happens if you're
driving along with you know it might be an applet you've downloaded it might be and provided by the vehicle itself you know you've got the the the the lovely car overlay the directional stuff on your screen and then that happens what happened you know this it says humorous because it kind of is but then the actual reality of it is this because at some point someone is going to have a really bad time of it when someone has one of these AR things on the bird - something goes wrong with it and then you're left with this situation you know if you try to put yourself in a position of someone who investigates you know this guy's trashed his car exploded
all over the place how would you even begin to know that this guy was wearing say a wearable device what kind of wearable device was it was a glasses was a little thing that he bought from a third party and bolted onto his headset was something in the car would they even be aware of this you know was it an app that they downloaded what's thought that it come from was the app tempered or exploited in some way was a deliberate who was the ad network you know how do you even begin to work out what the supply chain is for guy driving in his car he's got a you know Google glass equivalent he's using a sort of
third-party google map style thing but you know it's not ads included anything oh well okay yeah ads or ads but didn't expect an answer pop while he's driving who was the ad network who was the support you know these are all things that they're not gonna have a clue about and you know there are very specific rules and regulations where real world advertising are concerned so you've got these really sophisticated malva tires and kits that are doing around you've got these really sophisticated barriers to the side if you go left or go right to the exploits you've got really clever sort of phishing campaigns that will they'll take weeks or months just to grab that one domain and then use it for
the sort of shadow domain scams you've got all of these networks moving to HTTPS which makes it more difficult for us to actually track these things down and then you've got these these wonderful mobile maybe not wonderful scams where they can literally take five to ten pounds out of your pocket at a time just by being reader to a website and as I'm sure you to where if you you know you do any browser on your phone for any length of time it's actually quite difficult to install or download and ad blocker it's actually quite tricky to prevent yourself being redirected to a pile of garbage on a phone and in terms of real-world laws
there was a case not so long ago where I went to a course in America because a national park went to impressed with all these people playing Pokemon go trampling all over the plants and flowers and fields and they tried to get a some sort of legal judgment where people could no longer play Pokemon go in Miss Park and there are lots and lots of laws for advertising in the real world surprisingly certain types of banners aren't allowed certain types of it the pay it's very dependent on location but in certain places you know you can't have specific types of flashing billboards or banners you can't have digital effects they have to be a specific size and shape so you know
you've got all those regulations for these real world ads but then you've got all these virtual ads coming down the pipeline you've got the augmented reality ads and everything else and a lot of AR and VR companies are investing heavily in advertising so HTC have got their vibe they've recently set up a really sophisticated advertising platform pipeline so you know you go there you sign off you get the dev kit you can make these virtual reality adverts adobe have invested in virtual advertising tech I believe and basically if someone's out there and they're making a headset of some description they're jumping on board the advert right now and a lot of tech and a lot of
cash is being thrown at these devices to surround you with adverts from the moment you stick the headset on to the moment you take off the you know the the Google glass so how do you actually regulate for these types of adverts that are just going to pop up out of the ground temporarily blind you and have you you know Jam your car in a ditch and then vanishes if it wasn't there so yeah there is a huge ramp up in leave these VR ad space technologies and it probably won't be too long before we see the malvit izing equivalent in the the virtual and AR space so that's that's that's all happening now and we expect the ants base in VR to
really take off sometime in the next six to twelve months so it's gonna be pretty interesting to see you know where that leads probably somewhere terrible but never mind so I mean thanks for listening and you know if you've got any questions about advertising VRA are those horrible phone things I mean feel feel free to fire away okay as a publisher what can we do to protect our users one of the things that we tend to see is either very unrealistic sort of game plan set out by the website so you know they have these huge screens on their website where you will never get affected by yours all our traffic is 100% legitimate we guarantee
you will not be infected that's okay nice try come on it's you we have to accept that there is always a possibility that this is going to take place and some of those sites theoretically open or to legal issues by making these weird guarantees but a lot of it is down to making sure that the ad network that you partner with has a good reputation and a lot of these things have you know you can google a lot of these ad networks a lot of them have been around for years and it's usually reasonably straightforward to find someone that can recommend or you know shoo you away from a network because so many of these malvit izing attacks
become big news a quick search for the company's name will vary you know quickly show you lots of blog entries about them on security slides lots of white papers lots of you know my god these guys did this all over the register and the BBC and everywhere else so in theory it's a lot more straightforward now to find out who these these dodgy ad networks are than it's ever been but there is always the possibility of an outbreak and there are some air platforms out there the they have you know clean ad sort of programs and they do a lot of intensive vetting and checking I think Google Google answer in the process of rolling
something out like that now the Internet Advertising Bureau the IAB that might not walk be IAB stands for what the IAB are doing something similar so if you are a publisher I would suggest you know plugin those sources and seeing what kinds of programs are actually being rolled out that will help to keep you know your your visitors save ultimately anyone else yeah I mean so basically how do we secure people and protect them from these things I mean obviously you know ad blockers are great but they're not so great to roll out within a corporate environment most I had blockers don't have a sort of central you know control panel where you can roll out ad block
plus to six hundred people and keep it all updated nor the rest of it and having said there I think Magna gates and a couple of others actively looked to bypass some of the the more popular ad block tools out there the the I think it was the the rough tab website that was part of a campaign that actively tried to bypass ad blockers and even though a lot of the more popular ways of avoiding malvit isin were deployed on test machines in those cases it's still always managed to either dial back home or pop an ad in those cases you'd be redirected to you know a nice edge rather than a horrible ad but generally it's with most things
you know a nice layered approach with all these various tools or an all-in-one if you can get it for the time being as is the best way to do it obviously with most of the junk being pushed by these things being ran somewhere but a good backup you know policy is is essential but a sensible backup policies in better because you've probably seen in the news there's been cases in the states where hospitals and police stations are being compromised and then you know they had backups but they had to pay the ransom because the backups were an absolute mess it was just hundreds of folders with files randomly placed all over the place and it was just it was a disaster it was
actually cheaper more cost-effective to pay the ransom so you know you're gonna have good backups I'm not just sort of rubbish backups anyone else okay brilliant well thanks for listening come over and ask me anything you want [Applause]





