Go Hack Yourself
Show transcript [en]
yeah we're going actually I don't know how to turn this one on or
off okay let's go started good morning and welcome to the size austa if you've been here in years past you know that this is more than double what we had last year which was already about double what we had the year before so in 3 years we've gone from about 170 people to probably about 600 right now have check so it's uh really we're really thrilled that you all were here uh really happy that you come supported us uh at B sites and thanks for joining us today I'm Phil PanAm I'll be hosting this track uh today so if you don't want to hear me anymore after this go to one of the other tracks that dou and marting
um I'm pleased uh that we have such a great lineup today so I'm to kind of step out of the way but I do want to give you just a little bit of administra first if you didn't catch it in the uh after the keynote because I understand there were some audio difficulties in some of the rooms during marks administ you have those red tickets uh if you still have two like two lines of red tickets then you can still go back over to the giveaway table and drop a ticket in it's chines auction style seeway got them right there seeing them up right here in the orange shirt so if you still have them you can run over to the
giveaway table the drawing will be at 11:15 you have to 1:00 to CLA your prize you actually have to either go back or we'll announce the numbers uh you can go back and find what the numbers are and find out what you want way Network pass a gr couple other really cool things Chris Sanders autographed a few of his books for us if you want to pick any of those up and I'm sure you can find CHR and get them to put some a special message uh the CTF is going now uh in a room I found uh down the hall here in Fr of next to the Chiron boot so if you want to participate in the CTF you can
uh you can do that starting now and finally I think Mark mentioned it and don't see that there's going to be an issue here today but what we've been telling everybody is uh you know just make sure you have your badge nearby we did have to as you guys probably know some of you know we actually had a long wait list we had a weight list about 100 people and we had to all we had to tell most of them no but thankfully this morning we didn't have to turn anybody away so that was all right so I'm pleased to announce that uh we have Jason Frank here with us Jason leads the Adaptive thre division at uh the be group and
he's going to uh to talk to all today here in blue team number two so please give a welcome to
BR thanks Phil and uh thanks to besides cre Mark and Philip and Lawrence a lot of the guys who put a lot of effort into growing this conference over the past couple years this is our second year actually attending the conference as speakers um it's great to see the growth um kind of taking off especially in this area today what I'm going to do is I'm going to talk to you um about some of the stories and some of um our approaches I am a pen tester by train I actually want run a group at this point of about 20 different testers the group based on the Northern Virginia area we have exposure into a lot of the civilian
government U uh agencies as well as a lot of Fortune 500 commercial companies as well so we see a lot of different network environments and what consistently um comes across is during the outre when you go you do the test you run around the network and then at the end of the test you're usually briefing uh your findings uh what consistently comes across uh is blue teamers The Defenders they're saying hey I didn't even know that this portion of the network exists or I didn't know that we had this this box here that was severely out of date or you know I didn't know these credentials were out there a lot of these things as
pen testers we be leverage in order to run through your network and hopefully obtain the data with the crown ruls that we're going after so what we done internally and a lot of this is for our our benefit is we've developed a bunch of um tools scripts that we on the red teaming side uh that we put out for free uh open source uh and our tget audience initially with other pesters however you do recognize that The Blue Team The Defenders also need some help and so we're I'm going to do for this talk is I'm going to show you some of the tactics uh that you can use as Defenders to help secure your network uh so that
the pentester that you bring in has a little bit harder re time once they get okay again a little bit about me on Twitter is Jason J Frank um I'm a black hat trainer teachs the ad of 10 testing course and probably have every single pen testing certification that's available some are certainly better than others um but but why this talk we we kind of covered that a little bit but what's also interesting is when we're doing our test a lot of times the Defenders a lot of times our customers want to sit with us because they want to learn they want to say okay you how do I get started P testing or how can I
leverage uh your your adversarial mindset helps proactively secure my network as opposed to leing this uh report and saying oh well I probably should have known about this PL for you told why don't blue seamers have black hat some do some some have the budget some some say okay well you know I'm coming at it u a couple different uh perspectives however some no some are just underwater their time has been split so many times that they cannot uh keep up with all the demand and everything that's going on with with everything so my go to you by the end of this this talk is I'm going to show you these tactics I'm going to
give you the tool sets and I'm going to make it easy for you uh to to execute these things we'll talk about that you ever looked at any of the uh to secure network usually first things first is you need to figure out what what you're looking at what do you need to secure what uh from a hardware standpoint when is sitting on my network the answer to be well good things change you know might a network or users and plugging in laptops unplugging laptops that of things or you might say okay well for this server on where all my critical data all my critical applications sit that should probably not change right but you need to know
what what is is normal um there's a lot of cost in politics involved um a lot of times when uh I talk to Defenders they say well Jason I want to be able to do better and I know that I can do better it's just I have heard from upper management that they will not allow me to do certain things whether it's political or or because they don't have a budget to do so as an attack what what I want to do is I I have to come in for a pen test and usually my pen test is going to be anywhere from one to two weeks and so with that time frame I have to drop in on Monday become
an expert on your network on Tuesday and then use that expertise to hopefully build in a attack chain and get the crown Jews by Friday so that's 5 days to completely understand digest that information and make it use um from that perspective and so you look at the Blue Team you say okay well you know this is your life this is your baby you know why do you not understand everything that's going on in it well you know that that was my first kind of approach to but but the reality of the situation is that there are a lot of factors on Defenders that don't allow them to do this usually what happens with my team
is uh they they have this uh adversity to doing anything that is tedious anything that uh clearly could be automated I I need the data there's a there's a nice little graet that represents this but from an offensive side the uh the lines of code that you have to write uh to be effective in your job is a lot less than the lines of code you have to write as Defenders because as Defenders you have to be right 100% of the time as hackers my job is easier because I have to be right 1% of the time so what happens is a lot of these tool sets that we write are are uh we put out there open source we put them
out there uh and the cost to the defender if they choose to use these tool sets is going to be their time so they are available for anybody to use regardless is pesing or I will say the other thing about these tools is that uh typically they are just doing calls uh Discovery calls that are normal and so they're not going to be disrupted uh and that's that's crucial because um as a Defender you don't want to do anything that oper operationally impact your network AR sets a lot of them focus on Windows and the reason for that is because um does anybody here know what the most common method for getting into an organization is
today I heard fishing that is correct so instead of you know Bing against your boundary most people 2015 most people discover what a Pall is fishing allows you to send an email in sometimes with an attachment sometimes with a link and compromise the leest link in the chain people right and so what we do is when we land our fishing attack we're usually Landing in a Windows Department why because Windows is typically what US resides in and windows also allows us uh to get the access we need uh to to the Nick side the databases that type of thing because typically those admins those database admins those SS likely have a Windows side that um or Windows
console that they have data on that so here's a t typical attack path we spear fish in escalate access we identify where we're going uh and sometimes this is based on the customer telling us sometimes we have to kind ofine it for them but then we'll use that access toiv databases stations a lot of a lot of our team has been doing a lot of research recently and a lot of schol Dev uh around po shell tools and um Howell informally has been named by us uh Microsoft post exploitation language because of how powerful it is in those environment the um inent testing pen testing a lot of it is just using build in functionality or admin bu in
functionality but in a different way or so you're leveraging a lot of the calls a lot of the tools that are that are there um to help you perform uh your actions and so uh this is great because uh it also allows for a level of um of of stealth because if you're using already uh built in API calls and windows it's not going to look abnormal necessarily if you're doing these types of calls Microsoft's really funny they tried to put in this execution restriction if you put a flag to do power when you launch power show and do Dash bypass all that stuff Falls away some ad thought that that was uh that because of that protection they
they were to execute custom scripts well what we're going to show you a couple custom scripts here that we're developing um in order to launch those you just that flag should be let's talk about some the tools we're going to cover um these are all free these are all open source and map eyewitness which will cover uh power split Power Up Power view and erress assess most of these tools um save n map and uh in and powerit uh have been developed internally by our guys um at the time here's our approach here's here are the 10 tactics that we're going to be discussing over the course of the next uh uh few moments we're going to talk
about asset Discovery we're going to talk about base image analysis we're going to talk about your file shares file Shar um as an attacker you know who are your admins where are your admins um how old are their passwords and that type of thing we'll go into a little bit more the goal of this though is as you're knocking these off and as you're checking these off as a Defender you're starting to build rapport within your your organization and so you build that report and hopefully by the end of it you demonstrated enough uh impact that you now have the political Capital to request the budget to get to further some uh that you need because and that's the biggest
thing when I said political reform when I said you know Defenders were being shut down because of politics that's the biggest thing they say well you know you're not doing anything with what you have now so why should I spent money on this well these are going to give me some quick okay talk about asset Discovery and this is asset discovery on the cheap there are all kinds of appliances that do this but if you do not have um the budget to do asset Discovery what you can do is you can schedule a Cron job with nmap to scan your environment every 25 hours why 25 hours well because what that will do is in about a course of a
month 45 days you will get a pretty good picture of what your environment looks like um throughout the day so you can start to create a baseline of what's going on the other thing you can do is once you do uh Port Discovery around your network uh you can use a tool called eyewitness a former employee of ours Chris trer actually wrote this what this does is it runs out and rapidly grabs the web applications the websites that reside in your environment as a pentester I am very very concerned about the web applications that you have because typically what happens is company buys waking box they put it in their data center the admin doesn't want
to run into the data center every time they want to admin the box and so there's a web interace involved a lot of these web or a lot of these web interfaces do not um conform to whatever security policy the company has and so they left unconfigured default credentials that type of thing at that point as a pentester I can now leverage that uh to do bad things within your network and so we inventory all the web sites uh to see potentially where um our first link in our so you're going to notice with some of these slides they tend to get a little bit long however the goal of this was and you don't have to write all the
stuff down now the slides are actually to be available afterwards they're up on slides here at the moment um but we want to give you the syntax that we use or that you can use and take back into your organization so you can just run these things we're going to show you expected output and then you can use that in your go what's going on here uh that first ount command is basically running around your network looking for for assets the reason we're checking for those ports 21 through 8443 um is because typically those ports are going to be 9 95% accurate as far as what's in your network if you just do a ping scan with NM that's typically not
going to work one because of firewalls two because of icmp if icmp is disabled um typically you're not find everything so we use this method to a little bit more comens again right here you're doing asset Discovery you're doing Hardware Discovery making sure that you know it's on your network once you get a pretty good list of what you think is on your network at that point you can go ahead and do a followup P scan just to see um what uh what's running and then once you do that you can take that list and pipe it into eyewitness highness does for you is it creates a little little HTML document that inventories all the different web
applications that are sitting in your network right you must found a uh we dropped into a network and they said well you can't thr any exploits you can't really do anything said oh well this going be short test then so we um we ran this we did our Discovery process and we ran our um r eye witness what came back to was something very interesting I didn't I've never seen this product before but what it did was it was an active directory management platform it was a web application um that cached it server side login for cash Ling server side so I didn't even have to have credentials I just hit the Ling button sure enough
I test so I always I always look at the the other thing that you want to do is you want to take a look at your base image how does it deploy their new assets well they probably have some Bas image that they spin up from new employees they give a laptop they have some sort of instruction here's here go down what that means is that Bas image is probably pretty standard across the organization and so if it is standard across the organization and you can land out a box and you can escalate and you you done passes and all that type of thing the misconfigurations on that image are probably consistent across the entire
organization okay so people say okay well you know I run I run nessus on these things that you know um I I don't come back with anything critical so I think we're okay so that's not always true um we'll show you an example here we wrote a tool called power up it's a Powershell script that automates a lot of the privilege escalation attacks uh against windows and these aren't new and ground breakings but what they are is a collection of privilege escalation techniques that have been publicly released but it's a quick way to check for a lot of the a lot of the checks in here include things like abusing window Services um abusing all kinds of
different misconfiguration that are are resonant on the system here's the syntax you download the script you import the modle invoke all checks what it comes back with is it runs through new checks and if if something pops this little plus comes up here and says oh there's a vulnerable service here now in a pentest this this is helpful to me because this is the weaponized Commandment that allows you to take advantage of this service however for you as a Defender you'll know that this one service has a problem typically I see um the last last one I I did Lotus Notes anybody still uses Lotus Notes good luck not poorly misconfigure allows you to escalate the system pretty quickly
just get rid of it it's a worthless product
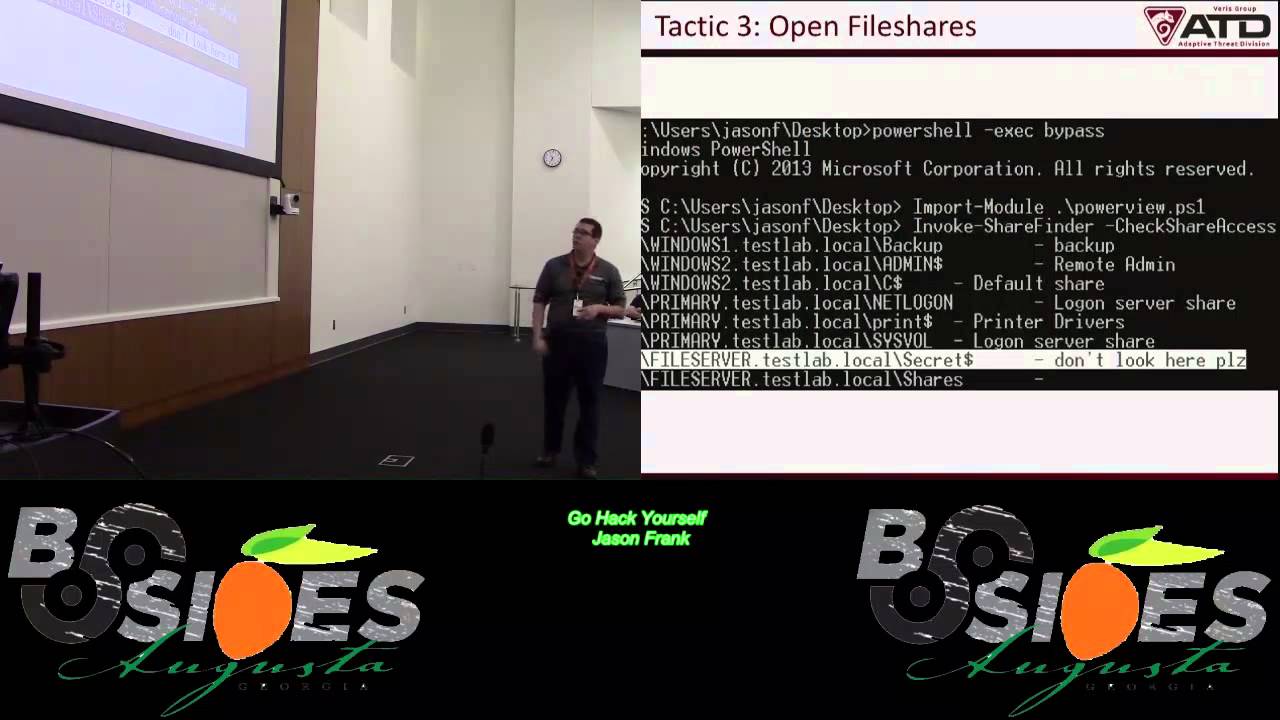
open file Shares are uh my favorite because um usually uh they're kind of our they're kind of a back pocket method we use as pesters I was in a banking Environ at one time and they they had everything pretty well locked down they were using aware th CLI system pering system the images were updated every every week and what happened there is they they actually had firewall rules set up that wouldn't allow the work stations to talk to each other which is great because if I can spear fish in I can't spread even if I find a misconfiguration on that box I can't spread lat laterally I may be able to spread through the servers but I can't
spread laterally so good on them for that however what I did find is I did find a um a file share it it was everybody's file share you know you drive you drive whatever it is everybody has chair you Traverse off that chair one and you see everybody else's stuff it was configured so you can jump into everybody else's stuff so this was a bank and we got in and um I got into the CEO uh file share and he had this nice little Excel document not encrypted name address account account balance social for everybody in the bank I looked into the out I said why are you doing this he said well there's some
regulation that basically says that you have to correlate the accounts with actual people okay why that he didn't have an answer open file a lot of times to you'll see um it shares that have some passwords and that type of thing that you could leverage uh to Mo around the network powerview has a function Power view is we talked about power up which is the privilege escalation piece Power view is a another script that we wrote um that uh allows you to run around the network essentially what it does is IT director where are all my objects and then let me query all those objects and see what shares you have available and so you throw this little
check share access flag on there and so if you run this as like a domain user somebody who has no privileges on the network and you run around and you collect everything that you have access to and it'll spit back this little list for you and say okay and some of these might be default some of these you know are are standard things that are here but then you'll you'll see a couple nuggets and obviously well sometimes they look like this but usually they don't um but there's there's usually always something that's going to allow you to you know maybe it's a complete file maybe there SSH keys that are leveraged uh that you can use to spread
in the network things like this are are R you want to figure out who your admins are if you're working in a large organization this might not be a very easy problem to answer reason being is because um you know say you're part of some large conl company this company is in the habit of buying other companies well what typically happens there is that you'll have all kinds of users coming in all these different groups that are created and if anybody's an active record you know they know that they can put groups within groups right so that things tend to get confusing as far as what permissions uh you have and so what we did with power VI is we
actually uh did this we put this thing in here where you can cry for anything of that admins right you do get that groups itry all groups but the admins or Star admin Stars just a qualifier and then you can figure out um the people within that group using get neck group this is just a pipe and then you can recurse what this will do is this will follow the chain all the way down if you're looking for domain admins and you may jump all the way down the chain and figure out who exactly your high value Target targets are going to be within your [Music] environment so that's one piece from a a perspective that's one
piece from a Defender perspective you want to know where these people are constantly loging in why because you may do some extra logging on their stuff you may pay attention to them a little bit more closely than somebody else or you may know that okay if one of these are compromised that's bad news right here's a quick example of output um you can see that you know there are multiple admins here we did a star admin star so not only are we getting back to main ads but also new exits and again that's one piece who who am I targeting the next piece is going to be where are these people so for almost every engagement as a
pentester we go we go hunting hunting versus at what that means is we we take a look um and see okay well if we can pivot around if we demonstrated that we can move around your network we're not just going to blanket spread across your network one because that's noisy two that lose a lot of artifacts um but what I want to do is I want to say okay if I'm at my box and I've escalated now where do I go well I'm going to go after the admins and so at that point what I'll do is I'll I'll go hunting so this is my favorite function within power VI it's invoking and if you add this little text
show all what this does is it shows you it goes out to active directory it says where are all my objects then it queries all those objects thatb and you remember you can do this without being an admin any domain user can do this okay where are all my objects I'm going to query all those objects over S&B who loog down to the Box currently if you run this during the day it's it's helpful who loog down to the Box current so you know um not only where your admins are sitting but you also know where everybody else typically sits it kind of helps you build this dat repository of what's going on sign what
I so this is what you get back you say okay well this person's loged here here here um a lot of times you'll see sessions that file servers from other people as well yeah uh nice little list for you again and you guys might be saying okay well there are appliances that do this yes that's true but but this is this is kind of free and on the je sale password reuse the reason this is a problem from a pen testing perspective is typically uh these appliances that come in and are supposed to do maintenance in your network will introduce um a service account into infrastructure these service account typically don't change passwords because well that would cause too much work so
those service accounts by designer are supposed to run around your network and perform maintenance on these infs so you have elevated accounts running around doing maintenance on inflence and so what you can do is you can say okay in powerview get that user and I want you to filter don't don't memorize this syntax again be avable but and any account that has not changed uh their password within 12 months your password policy might be 3 months right but are there any accounts out there that have not changed their password within 12 months sometimes uh what you'll do here is you'll catch admins who got lazy and they're just like I don't feel like changing my
password this time around I'm just going to set fire so this is what we'll see we'll see service accounts and that thing I talk about a little bit about before you know companies buying companies well in an active directory infrastructure typically what happens is you take this Behemoth of a domain over here this other domain and you put together and it's a you create what's called a trust and you can do very interesting things with trust and yes there's different settings you can do one way two way trans trans um however uh if if you can leverage trusts as a pentester um to uh compromise other companies so we're actually doing an assessment as we speak right now it's an
international assessment where they bought this company and they are trying to Leverage The Domain trust to jump into the mhip we did we we got like two days ago I think so we were successful able to do that uh here's a syntax in cor Power view and then you can map your domain trust what's interesting with this one is you can output it to a CSD and then you can use y head I'll show this to you too you can use this to kind of map out your network all you have to do is import the CSD this is what it will um this is what it will do so if you start say you into
corporate over here and your crown jewels are down here you can go up down cross into the other company and then move your way through until you get to the crown TOS this is something that we will very regularly execute in a period of about 2 to 3 weeks ass trust Miss misconfigured you can add in your DCS uh obviously domain and administrators um obviously Enterprise admins but there also can be other admins of your DC so if you can compromise a DC you have the domain um I'll show you this in a second but get domain controllers and then get net local group um what this will do is it will return output to you you'll see
things that you would expect like the administrator there might be a local administrator EA da but sometimes admins will go ahead and just add themselves as the buil-in administrator uh Group which allows them to log directly in the through policy preferences are fun uh typically what this does is it allows um Defenders to admin their their their inlo what's interesting though is the gpp it actually puts out these these XML files that are available on the DCS and there they there are encrypted credentials in those files those XL modes both usernames and passwords problem with that is that Microsoft in its Infinite Wisdom publish the key to decry these things so you to do is you
have to go find them and then decrypt them and then all of a sudden you have local admin passwords for across the network as Defenders again if this is something you're in your network uh get rid of it there are patches available and there write ups on how to how to roll that so uh again power power is different than power up and Power view this one was not written by us if you get gpp passwords it's going to hit all the DCS and collect these files and decrypt them and voil out you have usernames and passwords for across the network these are simple things and you you'll notice too that most of everything that I showed you up until
now has just been quaring information and then correlating right it's nonintrusive these tool are free right and a lot of these things a lot of these can be done in the background while you're while you're at your day job the last thing I want to show you is a little bit beyond that it's looking at order excuse me um we go to a lot of companies and we've actually got a lot of uh attention recently from some healthare companies because of the Anem but what they want to know is are we going to be the next anthem and um so what we've done is we've uh one of our guys at the time he wrote A Tool uh was called e SSS and
what this will do is um when we get to the point in the engagement where we know that we have the data we're not going to sit there and actually xill your data across your boundary to somewhere that you don't control because customers typically get a little upset about that so what we will do is we will generate data that looks like that data and then we'll attempt to erress that out and what we're looking forward seeing if your DP Solutions are actually do what they say they do what you pay do I actually had an example one time where we were expelling social security members and they had a DP solution in place so they were uh actually pretty
audacious about like oh yeah I don't catch it well sure enough we uh we had gigs of Social Security members come out of their Network UND detected and when asking him about it they said well it wasn't proceeded by SSN colon I said well that's a simple red ja better go back to the drawing board so but at the end of the day there are these DLP Solutions out there and there are blind spots that often exist um so you want to make sure that you do that ESS is out there uh it works on a client and server model and so if you get like a DPS like on Amazon or wherever you can set up a server out
there listening and then on the client now what you can do is you can generate data and then upload the data it has the ability to do credit cards socials it has the ability to put together a full profile name address that and these are all R it's all R data and then xill that out and see if your DP Solutions cat you has the ability to do multiple protocols HTP FTP SMB a few other ones too can't see this really well but this is hopefully what you should be seeing is you should see an alert sensitive data coming out over wire and the your data contents one you're testing the fact that your technical capability can see this stuff
and then to your your testing that you have a process in place to respond to this type of thing so just to kind of wrap it up I have given you uh these 10 different uh tactics that uh from a pesting standpoint can easily be translated into the blue side you'll notice that a lot of this is uh Recon and Discovery and so by having that information uh and knowing what you can protect protect is going to allow you to do a lot better of a job and hopefully make the pin tester's life a little harder once once they get into your network they're repeatable you can schedule them to run consistently and you can run in
the background so you don't necessarily have to be there monitoring most of these things um and these are free everything I've showed you is free because we know budg is a concern and we know Defenders um we know Defenders are operating on a budget and finally again these are going to give you a lot of quick WIS so that you can start getting that report together so you can actually make some impact Chang so I'll take questions I don't know how much time that we have but my contact information is there um our website be.com uh resources we have all all these tools here um and write up some things like that and I'll show you real
quick under our
resources I've been told I have to give up under our our site we have all these available for download you can just go here you can get them on GitHub directly or you can just download them some of the vogs and like that so with that I'll open it up to a couple questions I think we have a couple minutes for those um you have tools or any advice for Mac Centric environments Mac Centric environments a lot of times so the question was do you have any tools for Mac Centric environments a lot of times what I will see on the Mac side is they will somehow be link into the active directory side so there is some profit
over there um we as pin testers we in most corporate environments we have't come across too many Mac uh full Mac environments we have there sorry any other [Applause] questions yes you said ACC that did I not put them up there're also going to we're also going to post all the talks on YouTube So This Is The Blue Team handbook in respon any other questions see everybody to ask questions like oh
thereis yeah talked at one point about being noisy so test are you usually given direction to not be noisy or is the user population notifi thaty we're having a p test so the question was um we talked about being noisy is your goal uh to not be noisy or are users notifi it it depends on the case uh typically when we um perform pen tests they're a week or two long and so they're what we call Smash and grab tests and what we tell people is we say okay well we're eled here for that week and so we need to be we can't worry about being stealthy necessarily because the Packers are going to have a long period of time to
do what they need to do we do offer um a r team service that does incorporate things like staying in memory staying off disc and doing everything to kind of evade some of the the things that are so that we we kind of term pen testing and R teing as separate services this is a um this is an alpha card sponsored by alha we're doing some good stuff how would you harden around power show
how would you poers shell um again me being a pester I'm not an expert in this but I've been told that if even roll power shell in and it makes things a lot harder you got time I one more this gentleman had his hand up right here was um for for those that may have admin access or admin rights to do to do [Music] all this can be done standard standard that however you guys have the authority obviously to be able to do some of these things because it is to create nwork traffic but these queries and everything can be run as a standard user active director designed that way okay thank you very much everybody I
appreciate it