Let Me In!!! An Overview of RFID Badge Systems and Attacks
Show transcript [en]
So go by TechEmily, Pitbull, depends on who you ask. We're gonna go over RFID badge technology today that's currently existing in the wild and how to exploit those systems. And of course, gotta get in, let me in. So again, my name is Emily. I am a information security analyst on the blue team side. I'm also a physical penetration tester. And I am a DEF CON goon for speaker operations, so I'm sure whenever you've been hungover at 9 in the morning and someone's yelled at you through the speaker, that might have been me. I'm also a 2X dog mom, so these are my babies. I keep my heart full. So I have a few goals that I want to accomplish in this talk. First
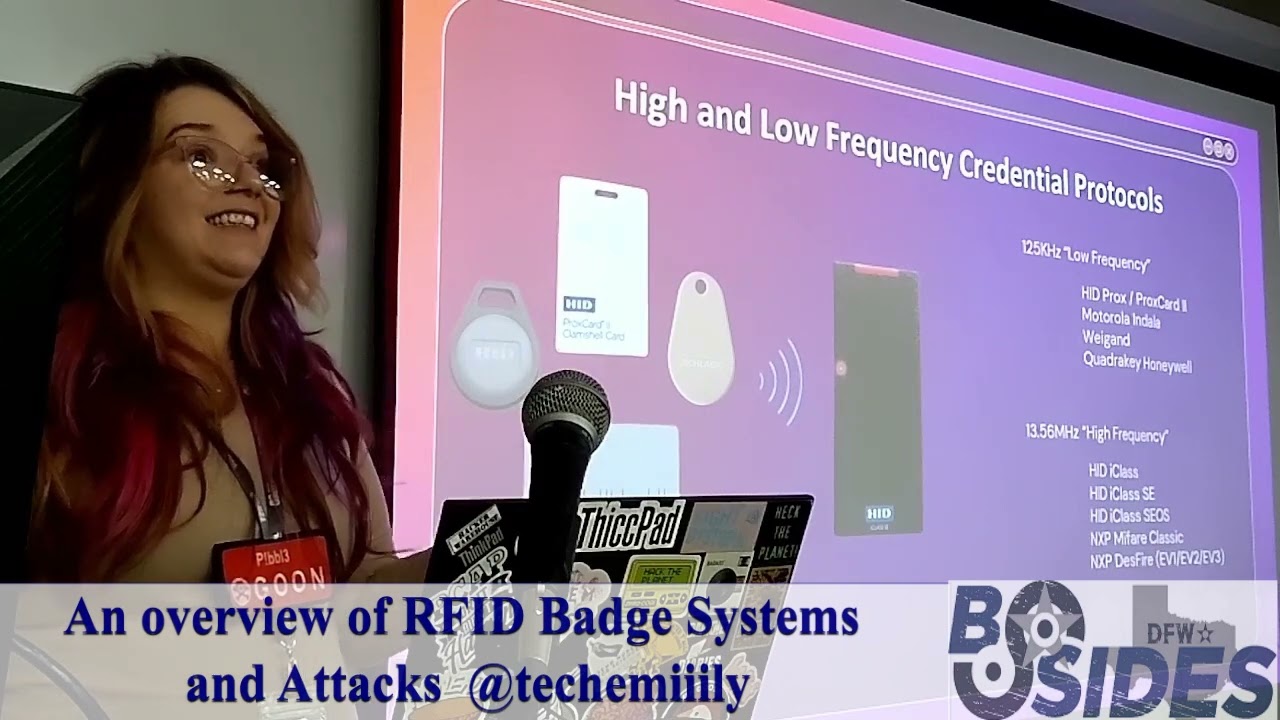
off, we're going to give a comprehensive overview of physical access control systems and its underlining components. the basics of RID badge technology and from presentation of credential until the door becomes unlocked when you can access the facility. We're gonna go over common exploits, the weaknesses in the systems and how to attack them and tools because you want to get something to use all of this information you're about to learn so you can go do some of this stuff. But again, systems that you even
of yay, more acronyms. When one thinks of badge technology and physical access control, usually what one thinks is this.
degree.
really really down into the computer engineering level so that's very crazy that he was able to make this discovery without any assistive technology and that's where his time at Juilliard comes
and of course, physical access control systems. This is the wire. I'm not gonna go super in depth into it, but basically it had a special design where there was an outer cord and inner cord. The outer core is hard, the inner core is soft. When the outer core becomes fully magnetized, then it can start sending magnetization to the inner core,
of sensing and motion applications. So that's revolutionary at the time because the only current credentialing technology that was being used before WIGAND was MagStripe. And I'm sure you've put your phone next to a MagStripe card and then it got wiped. That was a very big issue at the time and they were trying to find different ways to have data
is a zero and a one. These two on the end, actually I'll show you in the bitmap, are for parity and then the inside of those wires is the facility code. So it's just literally all the byte information translated onto these wires based off of this position. So like I brought up earlier, 26 wires, 26 bits. So the Wiegand format consists of 26 bits,
was the original iteration. Low frequency cards usually are between 26 to like, I've seen up to like 42 bit configurations.
it.
So yes, my fair, DES Fire and the newest iteration, which is DES Fire EV3 came out in 2020, which those EV2 and EV3 are two of the most secure protocols that currently exist. So like they always say, we're all the same on the inside and the same is true for modern card credentials. So modern RFID card technology is just different ways to hold the same WGAN format data we were discussing earlier. these different types of credentials to the reader.
human error and improper installation of hardware. Patching these systems is difficult and usually requires replacement of components and or moving of sensors. To truly patch configuration issues with these systems is going to require collaboration between the maintenance teams of a facility and the access control employees, which usually the maintenance people and the access control people are two totally different vendors and most of the time they also
as soon as I get
party.
to find the
that's why you can save it. Because you know the encryption schema that the device is expecting. With RelayAttack, you're just kind of holding the credential in a suspended state.
like your server
secondary
Team Tools has a lot of more specialized stuff, but you kind of, you know, this community gets built by people like us, people giving back to the community, presenting their research. This is my first talk at any of these conferences. So
sharing this and collaborating and giving back to the community is how we get cool stuff like this. It's how we get cool little toys that you can buy and then start turning off TVs and opening Tesla charger ports. Like,
is not good enough. Share it. Share it with anyone. I honestly, I was expecting one of you to raise your hand today and tell me the difference between one to one.





