Using and Mis-using Kubernetes Dynamic Admission Control
Show transcript [en]
all right good afternoon we are back in business so uh my name is Richard tweet I am a senior cyber liability engineer my Thought Machine they make um core banking software um some Payment Systems I've worked with kubernetes since fin B 1.6 1.8 so approximately five or six years at this point I've worked with um s GK what the ones called open PR them all I'm here to talk to you about but before I get into it just to help me level the talk um who here knows what L says please okay good containers uh kubernetes dyamic ignition control or ignition controlers brilliant right we yes right so that's what I'm going to talk about
folks are here and I'm going to be talking about using them misusing them just to check am I audible over the Ango and all the brilliant uh I do have a strong abent I'm aware of this if I'm unintelligible um if I'm writing complete cish or uh you want to clarify something it's a cozy CME just shy ey interrup me PR questions and things I'm very happy to especially few people so uh here is what you're going to learn these are the key takeways you're going to learn how you use here you just read it t this is how you justify your that you showed up tday right so you know what kubernetes is so I'm going in first to process a
API request kuet go ignore this B I sjs so um whenever you need any API request kubernetes star um you so say want part it will first move you to the API server and will go through authentication authorization if check is this a valid request like does it the scha etc etc it will go through the entire points of this ST which I'll talk about a moment and then after all of that um the request be alone or rejected it will be AED and then you'll get your response so your Cod command x z or
whatever this is unreadable and that's fine it's more to just give an idea of when things happen so um so there's a difference between Dynamic and and static I'll talk about first static is the things built into C itself this is well the API sches are actually static Mission Control also things like um uh you can schedule stuff on to the master not all of that is like you buil in static this compares to Dynamic which is I bring my own logic um and that's what we're going to be talk about today bring in L so what is the [Music] so there are two related things I'll talk about the first one here which is
AD mission for anyone who's not sure what the webook is uh kubernetes will send you an H you ask request you do some stuff return something to the control and [Music] return and just to repeat the dynamic part is the you bring your own l bring your own plugin components I can do some stuff so first in this chion are mutating webs these requests and choose whether to change them or not and whether to alow them or not so um an example of using this is um say you run the same works on multiple clusters on multiple time Meers and for whatever reason you can't s the registry at build time you could have a mutating
web on the cluster that goes ah this should be the gcp registry this should be the AWS registry um another example say have a multi-end cluster you're running cluster you have different teams um multiple reot time you could um add anotations to the workload based on the name space so like this has building a building C this is by te and you can do all of that see so the thing that's called after that is called validating Mission policy are as of 128 and um the whole point of these is that you don't need an https server anymore you can just put in some logic kubernetes will use the common EV language which is the awful thing that
they use for conditions on gcp I so if it feels familiar it's because it is it's this it's okay it's this weird mle language for doing stop uh SL logic uh I'll show an example in a little bit but what you can do here is yes or no is on but you can only do yes or no and this runs inside the control so here is an example of one so because what we're actually showing here and this is the only piece of this that matters that isn't Dil is that um if I'm creating or upating a deployment then the replicant must be less five so I'm saying you can have as many replic as you the less
five right um um again the only pieces of this that matter are you say what things this deployments and then changing what and you many or as few kubernetes API objects as you want here you can even have star like if you want something that happens anytime in API that's so here's a more realistic uh scenario so on the left I have a policy and again the only piece is at the bottom what I'm saying is in the production name space you have to use a Harden class because your stuff is so spicy it needs to be really well isolated really well controlled um on the right is an example pod that you can put in space so in the working case you
said your run time class be G visor so it's nice secure that l in and in the cas uncommented it will fail and you just get a refuse it will tell you no you'll get to do this this is created [Music] byy he's going to keep trying to H part it's just not going to succeed um which is wonderful happy answer so last but not least are validating webs so in this case you have to have your own https server it has have a HPS and again will send you requests configuration and you get to decide whether PES or P it's or it's not and that's next um the main difference between the valid missiones which is
what I was just talking about and this is you have to bring own um workload of the project and this work could make it own API you could have it to do some other logic um as an example uh you could have some cost management system and whenever somebody tries to spin up a workload you go and check whether they have any left whatever that means and then if they do they get started otherwise yeah so responsible is some third party let's say yeah it's only yes or no or you can yeah soe for the recording so the question was when you have a validating web and they contacting third parties does the response from the third parties have to
be yes or no the answer is it doesn't matter the only thing that this is your own custom code it could do whatever's nonsense you want it can talk all the do in your house you wanted it to if you're backod uh the only thing that matters is that you send back to kubernetes yes or no whatever you make to get there so in terms of ordering with these things are called first come the mutating web codes these are all called and you can think of it as all being called at once if any of them M the object it will get resent to all the other ones that then can decide whether they want to M or possibly including
itself so your stuff has to be or else you keep getting you keep editing stuff keep getting you Ed stuff um so this will happen and eventually hopefully finish no more changes um if any of them rejected at all that's it it just gets straight up rejected um but if allting webs Alli then it goes on to the next stage which is the Val policies the new St this is some C control plan and in this case they're all executed if any of in fil rejected otherwise who's on the stage then same thing send to everything and then passes and every you can choose uh [Music] where so this is the J BL that cuber
to I'm not ugly
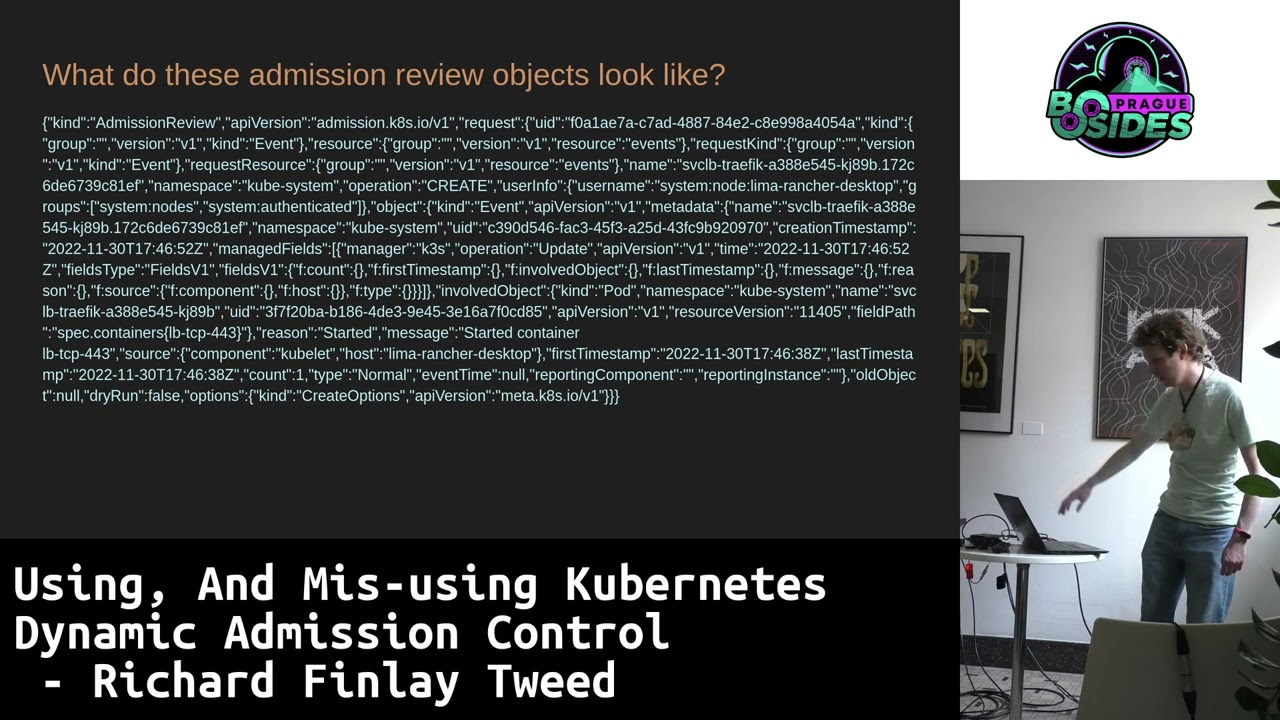
so we don't get get video excellent so uh I have PRI the it might even choose loc this wi-fi it but the the key from this is you get sent this object which is an admission review object it contains the original object and metadata by what API was made and it um I would point to this but I can't actually get over there recording but what you would have seen is it tells you what groups the API user is in what the user wants things like this plus the original object of the API so you go some quite nice
there right so now we see what [Music] Wii hat me I was going to show the specific pieces but essentially what you can choose is for example this group can only do these things or this if this group does something outside of business owns fire an alert over to your seene for example you can do that you can do that sort of advanced logic based on so uh what are the limitations at every single stage of these you can choose whether it feels open or closed so you can feel the request but still have't happen I show up in the audit so this is useful if you want to you can use that kind of like a a
drawing run or n right you can turn it on but tell it kubernetes toore what you return and then you can see is this going to cause me anointed so that be n but um the other flip side of this is if you have shoes Ste clo and your code is a bu or your dependency if you're calling off to something else isn't working your cluster is Seal right like those API Cod will all get blocked into your service there are cases where this maybe appropriate but this is a real like watch out for this you can really have a bad time they also take time to proess which again is on the API coming in so you can things the
minimum time you can tell kubernetes when it's calling you is 1 second one whole second is the minimum time this Stu I I I'm not very happy with this that's the choice m in web HS will be send requests they already mutated or at least they can do so you need to make sure that whatever you're doing is it like really that's the key thing you have to be item put to um also none of these resources can act on themselves to stop you Lo like soft hardlock Sy noting web validating act it which again is there for safy an if you want to some so can you use these so I'm going some proper uses for
this so you could use valid to check whether you have enough say you're running a GD for your team like processes they had I don't know 4,000 hour week or something really have concept of that so you could build that in here as you can use a m to best so if your users in a multi cluster don't set a user run you for to be something else um so you know they run us nobody or user something just princip you could also choose to set living conventions on this stuff um it again it's just an example um but it may be necessary in some multi situations like it has to be Department te work or
some you can force that to happen so fun new misses um you can just build me binary after some time for some K Eng this this is a thing you can do not shoot to be clear you could do it um you could have a guard web that just set secret off to some
server you could listen to every mutation or creation that happens um then use this to create a aned log um I see the project want AR rest and that's literally how this works if you just want mutations or Creations you're happy to leave the side you don't have to pay [Music] certain you could also register a validated webook that sends a request the Cofe machine if somebody employs the critical Surface after you should you're good all right so he takeways again if you hav't interested in this here's some useful resources the diagram that I showed that I'm currently trying to get kubernetes official documentation hopefully it'll be there in say a week or two and you'll
be able to see it there uh that's the talk any questions yes uh hi it seems to me that this is quite similar to the open policy agent do experience with it or how would you compare the solutions so open policy agent is one of these it's just the language that they use is open policy sorry I'll get to the recording uh they're asking why does this differ from open policy agent or trto uh open policy agent andto are ad missing controll one of these Dynamics probably validating but I don't M and all they do is allow you to bring your own budget and then it will execute for you so it's just a fancy
[Music] htps controllers to I'm wondering there is this of
does it all the Stu yes of course so uh the question was um there are various things to use this for security purposes um I also make sure yes so they all get calls on all matching API calls and numerical order the only cop I would say is that there is no guarantee your thing will be first or last so the that's one of the limitations of rest I don't know I wouldn't be able to know that the request I audited actually happened or not because other web post could have rejected after I saw it um it's a limitation but again it's something you can use so yeah canere contr not interfere by the way the only way they interfere with one
another is if they both are mated so one thing changes something and another one changes back and then you end up for the valida webs they all run um it's only any of them rejected but if any of them projected rejected so he want to have like four different ones that verify four different things you can do that and you'll get a guarantee that if any of them it it will be any other questions if anybody DED by this St and thinks it's really complicated orig version of rest was 60 lines of go and that ran production for a while um these are all you need to do which was why I'm really this I'm going to try it
again anyway while I attempt to have
this okay anyway it's all loing but um the response the minimum from is which the the request and the equivalent of a lie true or a lie false that's it like there's no it's not some crazy API you genuinely just need to put it in U and yes no um so I wouldn't be DED by these you do not have to this you genuinely can just have this tiny pie of right any further questions okay we'll still recording there if anyone does think of anything I'm going be here all day I'll still be in bright green t-shirts just wonder and ask me stuff thank you very much





