James Habben - Assessing Weaponized USB Devices

Show transcript [en]
every bus how many of you right now would take a thumb drive from me and plug it into your computers Yolo right
so fortunately I'm not a a red teamer I am focused on on blue team defense I work for Verizon formerly known as risk where digital forensics Incident Response consulting firm much like mandiant or straws or a crowd strike or you name them that's my intro so I found that's a that's a default animation in keynote by the way I just found that today I was like oh that's perfect so the agenda for today I'm gonna go over a couple of things real quick on significance things that we as Verizon see in mirrors cases that I've seen in my consulting work with customers with malicious USB devices they are out there as Joe indicated and as apparently the last
talk whence went on I didn't get a chance to see that one so I'll go over one of the scenarios I'm normally I've given this in a few other places and it's normally about an hour talk so I got a I got a push through on this and and make sure but I'll be outside if you want to talk about anything else definitely so DHS study back in 2011 they dropped a bunch of thumb drives out and out in the parking lots yeah you can see there the 60% of them got plugged in and the ones with logos on them I think they they indicated that their government logos of some sort so you know very trustworthy face right ninety
percent of those got plugged in kind of a kind of a bad statistic any red teamers in here you've taken notes right put put government logos on your USB sticks okay so five years later you think you'd get better it did come on give us some credit forty eight percent got plugged in there's actually a great blog on this from from some of the guys that did the study there's a link in the the link down here at the bottom Joe or you guys showing shank slides through the through the conference somewhere I'm happy to give a PDF with the slides there's a bunch of links and stuff in here so I'll figure out some way to get that out some
of those thumb drives went in within minutes as in like first thing as they're getting in the door right forget that email that's that's been waiting all weekend long I gotta find out what's on this thumb drive because there could be something good I might need to tweet about it you guys almost Stuxnet right okay so USB was used in there it wasn't a USB exploit so to say but there was a link file exploit in there that exploited how Microsoft Windows interprets the icons as they're referenced you can exploit you can execute code by way of referencing an export through a dll that's included on your thumb drive that's that's been patched since there was another one that
was similar after that but that was conducted through a USB medium because they were trying to get into that air gap network so we've got nation-states using this and we've got studies showing that it's effective we've got can't say if they're nation states always but we've got other attackers using them as well so the scenarios well first off the the significance I'm Verizon right the DB IR report I'd get fired if I didn't at least mention it so this is one of the the stats that we have in there this is the the targets of compromises targets of the breaches credentials right so I categorize USB attacks like this as phishing attacks same same category you
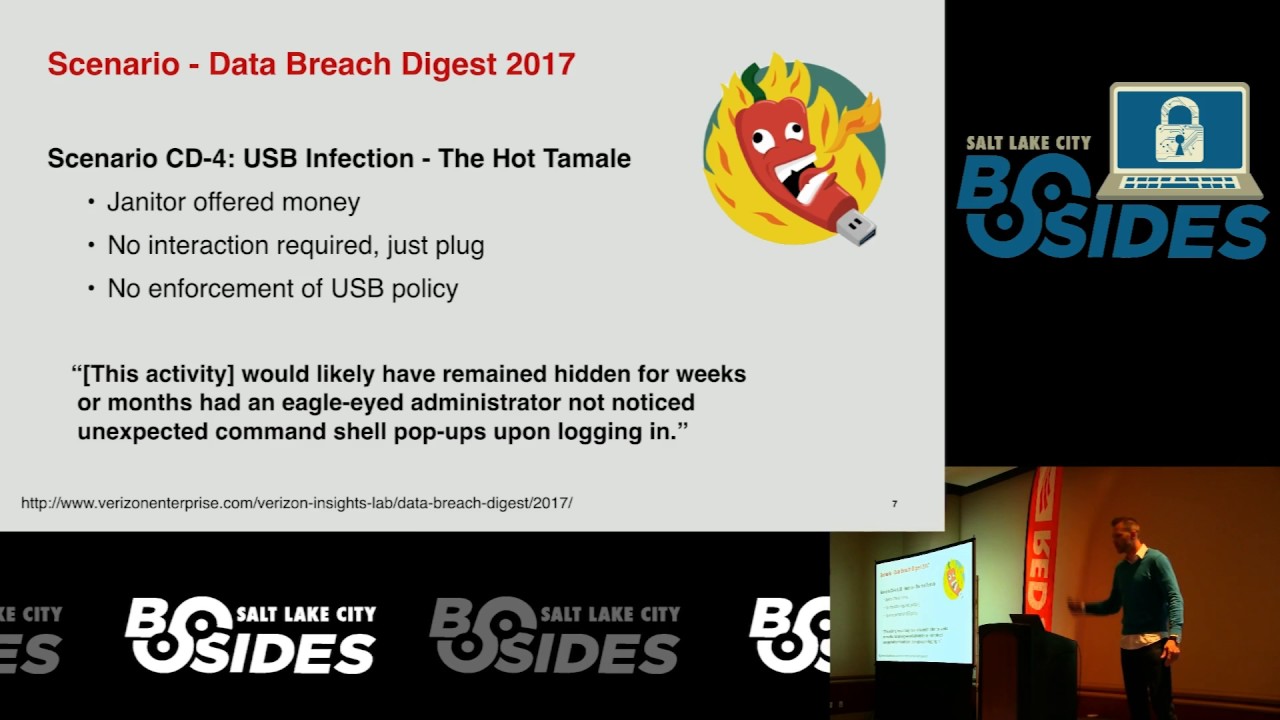
can put them in emails or you can put them on a thumb drive you're convincing someone to run or open or something that that that piece of something that will get something running on your computer so credentials are the major source can you get credentials with you we drive yeah absolutely so here's a here's a scenario you can read more about this this is another Verizon publication called the data breach digest that talks more in depth about the that some of the cases that we actually work rather than the DB IR which is which is more anonymized from lots of people in short here because I'm a little shorter on time a janitor at a
company was offered money to plug USB drives into computers while going about everyday business and it was effective so the yet the the way this was a case that we personally I didn't personally work but Verizon handled the case for a customer the the way they detected this is the administrator logged on to one of the infected machines and noticed an extra command prompt you know the login scripts that you do when you your domain policies and all that kind of stuff he noticed an extra one right how how observant is that so that's that's how they caught that this scenario was an entertainment industry company which was a lot more elaborate of a set up here
they they were at a conference they targeted an executive for the company they had a booth they talked to the executive they followed up with the executive with letterhead sent him a thumb drive plugged in and got a matter Pradesh L back out and the quote down here once the reverse shell had been established it didn't take long for the threat actor to start exfiltrating gigabytes of data including an unreleased movie it's a very serious threat that's that's what I'm trying to convey across it have I been successful okay so those of you that raised your hand would you take a thumb drive from you now
yes it's only a 512 Meg though no all right so the attacks that can be conducted with a USB there's the very simple and and most likely the the most known to you guys right now is what I call file based or or logical attacks and those are what we do commonly see in phishing emails via PDF files via office documents or via the the linked file exploits or some other zero-day or one two three four five day whatever it is at the time that is is not patched up on that system so the the PDF files they run they run scripts they allow for event triggering all kinds of crazy things just like the the office
documents they can they can do all kinds of nasty stuff for some weird reason they think that's a good idea but anyways we're all very familiar with those through the phishing emails so I don't want to concentrate too much on that because those are those are fairly easy to address you throw throw them in a sandbox throw them at antivirus throw them into your your PDF or your word or whatever analyzers you can inspect those pretty well what I find most most people don't have a real grasp on is the hardware attacks that can be conducted with USB some of you are probably familiar some some devices out there anyone the names rubber ducky is is like the number one
most well-known device it was one of the earlier devices another one Bosch yeah bash bunny I heard some more USB armory Raspberry Pi they have a zero Raspberry Pi zero it's called so all all can be used to conduct USB based attacks did they talk about some of those in the last talk those of you are there some of those devices not so much other other USB stuff okay what's that the face no okay I'm not if I'm not familiar with that one gotcha okay I'll have to check that out then the the physical attacks that that can be conducted pretty easily by these tools some of the ones that were mentioned here and by many others that
that have been custom designed a USB device can a thumb drive looking thing can emulate a keyboard and what's scary about that is you think about how how do you run your highly privileged scripts how do you run your highly privileged programs and all those sorts of things you type in right you type or you use the mouse that's your interface that's the human interface into your computer so if a USB device can can take the form of your keyboard and your mouse and it can be scripted that's pretty pretty serious right it now has taken over the same privileges the same permissions that you have as your user the fingers that you're typing with it can do anything that you're
doing so you're logged in to your domain I'm an admin account it's got the world right it's it's a very very serious threat and the thing that makes it worse there is no admin privileges required to enable these things when's the last time you plugged in an external keyboard or plugged in an external mouse and it said hey are you sure you want to use this device yeah never right none of the OS is unless you anyone use cute was it cubes yeah does it I think it does that doesn't it yeah I remember seeing Joanna talk something about that I haven't played much with that but a little better okay cool so cubes check
that out it's a it's like a virtualizing app type of operating system Linux ish based type of thing helps to protect about against these things the cd-rom is a serious threat in this because windows back in in XP timeframe allowed for what we call auto run yeah you know I'll remember that some of the the viruses spread through that some of the virus spreading things using USB did that way they blocked it I believe it happened in XP at one of the patched levels that they blocked the odd run it turned it off by default as a Vista you can't actually turn that on for USB storage right mass storage so disk drives and thumb drives that you
plug in CD ROMs however still have auto run available so you can turn those on and USB devices can emulate CD ROMs you the I think of sand disks that made the U 3 USB devices those are all run on cd-rom type of things so if you can get a little menu thing with portable apps loaded you think you could get something else loaded oh yeah anything you want and then the the last one is a little more recent development in in the last year so it's been developed a little bit more started by mu bik's maybe making that real popular he inserted through through one of those USB devices an Ethernet adapter it sounds silly it
sounds innocuous right if you plug in an Ethernet adapter but you don't have a cable going to it what could it do what's the worst that can happen so one of the things that mu bik's made popular is he found that if you plug in an Ethernet adapter with a ridiculously high speed rate as the operating system sees it and then you emulate that it's actually plugged in it's not going anywhere right it's a virtual adapter it doesn't even matter the operating sees that super high-speed rate as the priority device regardless of routing tables so when you go and authenticate all of your things it loops through that emulated USB Ethernet device and then that device sends it back out to the
real network so you know nothing different so when's the last time you got prompted for that USB Ethernet device that you plugged into you are you sure you want to use this never right I'm hoping that changes in Windows or something but anyways what I'm presenting to you is a methodology if you have a piece of hardware in your hand that you feel might be malicious I've got a methodology that we use in in our labs to assess these devices to make sure we're not plugging volatile and and well malicious items into our sacred systems all right if you take some thumb drive that comes to you if you're in a forensics role and you take that and
plug it into your forensics machine you are exposing your forensics machine to the malicious threat if you don't do the right things you are doing that now if you are placing things in now so what I want you to get out of this is a comfort level that if someone hands you a USB device and you don't know that person or you don't know that device you can walk away and say hey big deal I'll run through this methodology and I'll know is it malicious or is it not and I'll know that in the process of doing that I haven't compromised anything on my systems so it's it's a little a little bit of a lengthy process and it requires
some setup but you can't be too safe right so the first step we want to preserve anything that was on that disk if this if these devices can be scripted they can be scripted to go and wipe data so what I want to do first is prevent the scripts from actually running I want to collect the data as much as I can off of the the data portion of that device so you need a physical machine I run a Mac you can well you can't really see it it's behind the podium here I use fusion I don't do I don't have any problems with it I always use fusion for Windows I don't even boot
into boot camp I don't ever have to do that this is one thing well I don't use my Mac for this but throw away laptop you need a physical machine use a Linux boot CD to make it easy I use Linux just cuz it's quick and easy to get the data off you don't have to worry about booting windows and all that kind of stuff we're gonna use a hardware write blocker this is an example of a hardware write blocker right here it's an inline write blocker it uses power from the host computer and it powers up the device and it just prevents writes going there that's the whole forensic methodology I recommend though you get
something like the tableau right blocker because it's got its own power source you guys heard of that USB thing that has the capacitors in it that can suck up juice and then blamo it goes and fries your computer well if you haven't you have now so you don't want to plug that into your $10,000 forensics system now plug that into your tableau and let that be a fuse replace your $200 right block or rather than your $10,000 forensics machine so then your standard collection of whatever tool you use to do that next step physical machine again this time we want to run the maliciousness we want to find out what it's trying to do so the
biggest target is Windows so that's that's what we use and my recommendations on here and are in the the commas afterwards use a small hard drive because the goal is you're gonna acquire this drive actually twice so get yourself a little 64 gig solid-state something like that make it fast make it small and then forensic wipe it out first because that compresses a whole lot better lessons learned through the process use a software write blocker this time the reason why the tableau hardware or any of the hardware write blockers are meant to talk USB mass-storage they don't know how to talk hid the human interface they don't know how to talk CD ROMs they don't know how
to talk USB Ethernet they don't know how to talk any of that they are purely designed for USB mass-storage and only to allow reads so it shelters all of that other potential maliciousness out you just get the logical data here we want it so I want a software write blocker you can use that registry hack that's out there just google that registry hack USB write block or something like that you'll find it in case has a write blocker built into it if you have that it doesn't require a dongle so you can use that without the dongle we want the stuff to run but we still use a write blocker because you know forensics and stuff collect a
before image of your disk and your RAM and then prep any of your collection tools this is kind of like malware sandboxing but you're doing it on a actual hardware system so if you've got any system any scripts or frameworks or anything like that that you like to use for doing malware sandboxing put them all on and then the other thing i'm gonna present to you along with this methodology is number six a PowerShell script that is going to make assessing the hardware maliciousness of these devices incredibly easy once you start up all that stuff insert your USB let it recognize the drivers run through all that give it a minute two minutes something along those lines and then
stop the the PowerShell script finish your volatile collection tools and then do another hard drive collection and your memory collection because you're going to do a differential of the clean versus the dirty and of the disk and of the memory and then from there you're just gonna do your standard find evil with your the file contents of your the acquisition from the disk look for any of the files in there running through your AV scans that's a it's a low effort to result ratio right you can click a button or something like that five minutes to kick off an AV scan let it go in the background doesn't cost you any more time you surprise it here
consultants say that we don't build for machine time so it makes the job cheap if that doesn't come up with anything then you can run through io c-- searches or then dig into your PDF or office document specific tools to analyze some maliciousness of those files if you don't find anything there get into the the disk of your sacrificial system look at the disk images compare them compare the memory images compare your volatile tools see what might have gotten started for processes what files got created what registry entries all that standard stuff when you're looking for evil on a system and also review the output from the PowerShell the the last thing here collects firmware
this is the this is the really really super deep that that I'm not very good at myself but I have people for that and probably the guys that we're talking before me are one of those people not not not my people but but they're probably the type of people you want to make friends with if you need to start doing this type of thing there are thumb drive controllers the the USB controllers out there the most well-known is fives on pH ISO n there is a talk about this at shmoocon in 2015 about how you can reprogramming these controllers in the field to become cd-roms to become HIDs and then you can rewrite the firmware on there to include
scripts and in fact there's actually a tool now that'll take the rubber ducky scripts and compile them into firmware that can get loaded on to a files on controller thumb drive that costs like five dollars on Amazon the challenge is just finding one of those that has the flies on it's not used across the board so you might have to buy a few dozen and hope for hope for one of them being being it so if you if you can't find bad and anything else and you're still convinced that there's a problem on this thing then you can go after the firmware the easiest way to do this is a program there called chip easy be very careful
where you get this from I've got a slide in a few that that gives you the URL don't get it from anywhere else it's a sketchy looking URL give you that the one that I'm gonna show you but there's worse so the chip easy I've got a picture of it too it tells you the the controller that's on there it tells you the size it tells you all kinds of good stuff about that it gives you URLs to the tools that will allow you to dump the firmware out there for analysis and then the easiest part number four just re the firmware okay so before I get into the PowerShell some of the PDF file
tools that you can use if you're not familiar with analyzing PDF files didier Stevens actually has a quite a few blog posts on it he's got a lot of information on all that so it's a great site to use my favorite is this pppp PDF I always have trouble saying this p:p PDF whatever peep-peep II okay now on video saying that so that's my that's my favorite he does a lot of cool stuff in that there's an interactive shell it's it's a real real fun one to work with for office files my favorite again up here is the Des Lodge allayed tools he's he's got his he was on that bitbucket before but he's modernized and
now on on github any bitbucket fins in here didier again has some tools down here that will allow you to dump some of those things out this talk isn't on that I don't have enough time for that but those are really good tools to use so here's a picture of the chip easy only get chip easy from that site I told you it looks sketchy right dot see see where is that from China yeah it looks sketchy is all hell but that's actually the legit site you'll you'll find a ton of downloads offered from dot are use and diet who knows what so yeah only get it from there but you can see here some of the stuff and for
example right here so it tells you the Phi's on controller can everyone see that in the back is that big enough this this program was actually designed because there are people that will get thumb drives and reprogram the firmware to let's say it's a physically a one gig thumb drive they'll go and reprogram it to represent a 64 gig and then they'll sell it sell it on eBay as a 64 gig for a lot more money so this this tool is used by a lot of people to check those things out and yeah it obviously gives you the tools to do that so the the URL down here it goes to the same site usually where they have the
they host up the the firmware tools in order to download and reprogram the firmware here is the PowerShell script you can find it on my my github gist page it's a really stupidly simple PowerShell it's got about three lines of function but another like 20 or 30 lines of making things pretty you guys know how that goes I get a list of the plug in play devices PNP right plug and play devices that's all USB thinks I get a list before you plug it in I pause you plug it in give it a give it a minute right it recognizes all those things I go once you continue I get another list of all this plug and play devices and
then there's even a function in PowerShell that says get me a differential between these two variables like I said three lines of code it's it's nothing amazing but it makes this process incredibly fast so it dumps out a quick list of the differences and then it gives you the full properties everything that's stored inside the the plug-and-play properties so here's an example of that output you can see some things like the USB store up there's for those of you familiar with forensic artifacts for every USB store there's also a corresponding USB nan store okay and then you've got the the W pad Enuma all that kind of stuff so this is the the quick list on the top you can see
over there it says DIF list and then long list down here it'll scroll for a few pages with the full long list of all the properties for each of those devices so let me just pop through here real quick you can see on this one you've got just a USB and an HID there's no USB store on there at all so if you're plugging in a thumb drive and you don't see a USB store but instead you see an HID and this is just a USB so it's just a logical oh right down here so that's a USB USB Ethernet that's plugged in there so now the the slides for what happens when you plug in some
of these devices the USB rubber ducky in default configuration you can you can program a lot of those things and change if it's got storage or if it's not or whatever else so over there you can see there's a mass storage there's an input there's a keyboard there's a disk drive there's a volume there's ducky storage clue right and then there's a composite device one of the other devices the USB the land turtle from hack five by default it gives you in a nice a tap and then also a Realtek Ethernet controller again thumb drive Ethernet controller hmm clue and then this is the USB armory with the with the Ethernet enabled for the 4mu bik's attack he ran this for me
on his devices because I don't have all of those things and then I had some one so I think someone gave me I didn't get that slide in here the the most put together attack using this method all this mechanism is poison tap a guy by the name of Sammy well known in the in the industry here he put together a framework that basically you install you run an installer and you get it installed on this device and it will install poisoned cache in your JavaScript history for the the top million Alexa sites and so you've basically got a JavaScript rat and running now in your in your victims web cache anytime they start up and go to
basically any site either ever write the top million sites so then just show and tell about some of these devices what they look like that's the armory and then the files on controller and that's all the time I have but happy to take questions out in the hall or you
you