Azure Enterprise App Takeover: Privilege Escalation Explained #shorts
Show transcript [en]
In Azure, you have enterprise applications, right? Uh they are used to do a bunch of different stuff. This is one example of a application, which is like a backup application. That application is able to do quite a lot, like read all the SharePoint and read a bunch of I mean, it needs to do backups, right? So, it needs to be able to access a lot of things. Um in particular, one interesting permission that it has is that it's able to read and write directory data. So, let's think about this. The account that they stole on that server is able to take ownership of applications. Those applications are able to do a bunch of very interesting
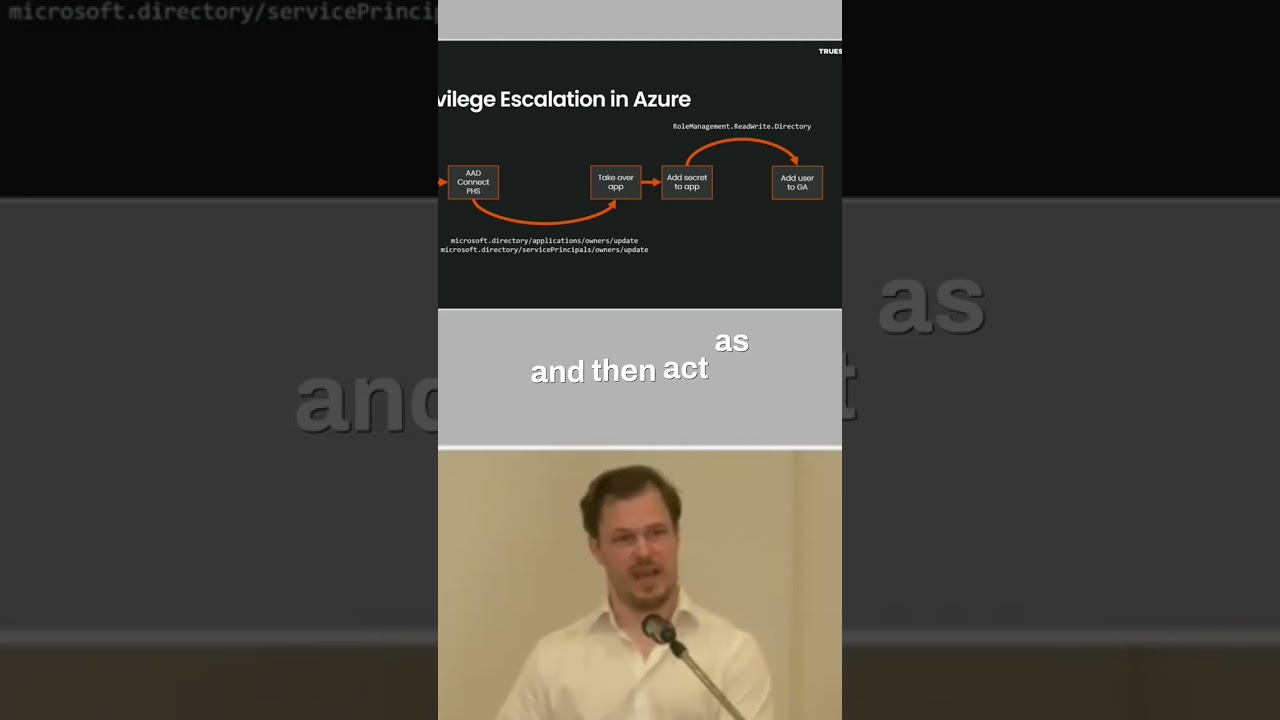
stuff, which the original account didn't have. So, basically, they used that update owner to be able to escalate the privileges and then act as the application. So, abusing applications like this is a very interesting way that we see uh threat actors escalate privileges in Azure, basically. So, they take over the app, they generate an app secret, and then they use that to create their own user, which they can with the original permissions, and then they just make themselves uh global admin because they're able to read and write the directory. So, the service principal credentials is interesting in itself. I mean, what what it does is that you generate these credentials and then you act as the
enterprise application in Azure. Um that's interesting for uh privilege escalation, but it's also interesting for persistence, right? Because many companies that investigate uh breaches, they will look for newly registered applications. But if someone takes over an existing application or like it generates credentials for an existing application, that won't really show up anywhere.





