Scott Arciszewski - Application Security Beyond Compliance - BsidesOrlando 2015
Show transcript [en]
boy yeah I remember I just didn't trust hey just we have that is like we had a better building like
because the dinner etiquette I think for the saturated because our PC
I just need to be on me into right-center co-host thank you
um
muted
yeah my clicker thing or uncheck these people
stop
all right field test
is this work hey
afternoon everybody welcome to app sec beyond compliance aight i let subtitle that your guide to not so good compliance you'll see why when i get to it later slide we're quickly show of hands who here is actually done a security audit before PCI HIPAA oh I'm actually substantial have you okay raise your hands higher if you like auditing and you think compliance actually make security better yeah I didn't think so mmm so we're going to talk about why compliant sucks we're gonna talk a little bit out the ol boss top 10 because that's everyone's go-to checklist for is my web owner bowl and it doesn't get enough job there we're gonna talk about good enough security
and what that means and what it means for business people and what it means for security engineers not really the same thing I'm going to mention a I'm gonna introduce a taxonomy of vulnerability um that will make sense probably in a later slide how to build secure and maintainable applications and how to protect developers from their own bad habits so if you're um if you've done compliance auditing this problem will be new to you but there are different types of audits depending on the industry you're working in e-commerce if you're done with credit card numbers you have PCI payment card industry data security standards sarbanes-oxley if you're do anything with a corporation that's publicly traded this is popular in financial
institutions HIPAA dealing with financial information this is what I'm currently dealing with it um my previous employer and phipps for non-military government sometimes you might run into all of them sometimes you might run into none of them and you're working for a company that doesn't really care about security so if you had like an online traded or publicly traded corporation that published an online app for veterans you'd probably have to comply with all four which as of last time I had to do a PCI audit was not really possible because the requirements for SSL for phipps and the requirements for PCI contradicted each other so have fun alright so one of the reasons why compliance sucks is it's time consuming
you have to take time away from building stuff that creates obvious value to your business um which in turn raises costs it's also invisible unless you're actively being attacked like NSA KGB or even you know underground groups anonymous hack the planet you're not probably going to see a lot of return on investment it's insufficient if you're doing compliance usually you're following a checklist and if you need everything on the checklist do you think okay i'm done i stopped here into the line when attackers are actually far more creative than that and they're also responsible for a lot of complacency and negligence a lot of business owners assume okay well I'm PCI compliance I don't need to keep up to date on
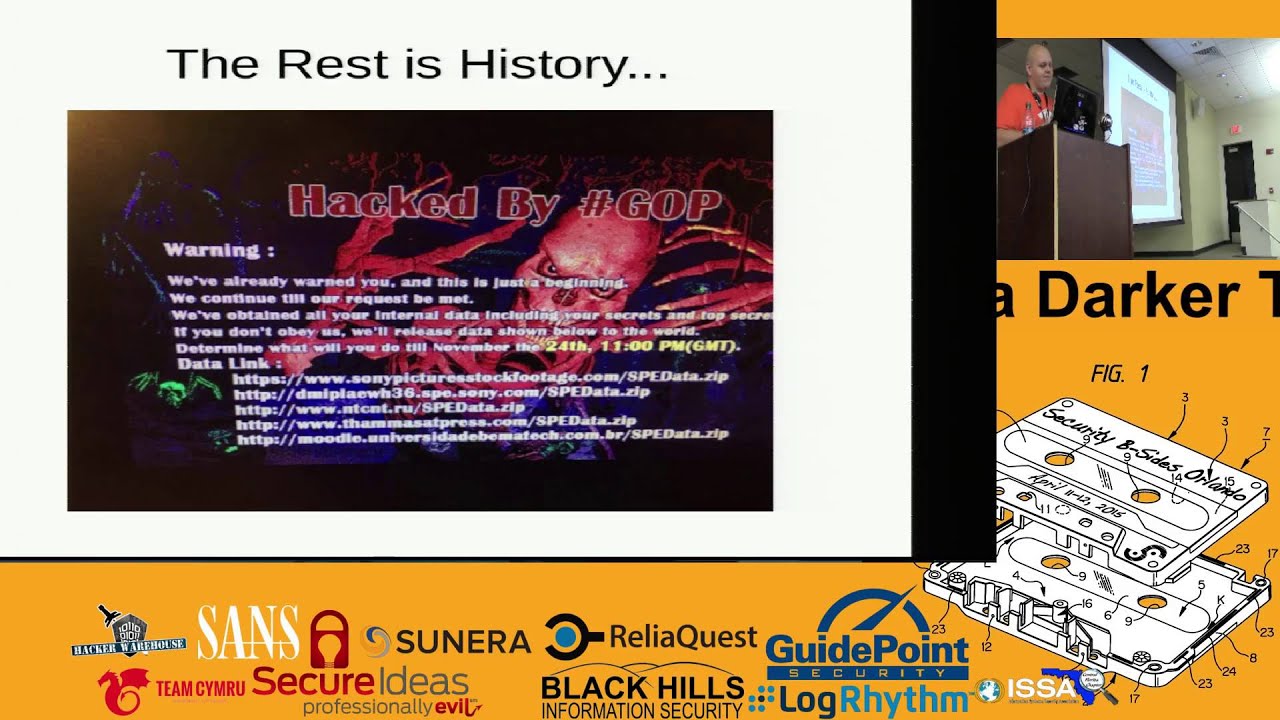
everything because we're compliant and unfortunately that's a fallacy and it ends up costing consumers more than anyone else so I'd like to propose the compliance of in diagram and it kind of looks like this so in theory the way security compliance supposed to work you have school security practitioners who regularly test your network for risks um on except the ones reported fixed addressed and maintained you know it in it everything's you know maintained reasonably quickly and responsibly and this will keep your company security robust and you won't have anything happen like what happened with Sony or with push last week and everything will be great unfortunately in practice since the company's dictate what the scope is
they typically select things they know are hard targets then they are another problem is you have auditors who just literally fire up automated tools running on your application go oh we didn't find anything that's as far as we're going to Delft McAfee did that for one of the applications I built while I was working at UCF some of them will actually have people actually test your application manually these are one of the more legitimate companies on completion and checklist is completed and you're certified yay and usually they check for the things on this top ten list you know injection both sequel and ldap cross-site scripting etc etc if you're familiar with owasp none of this
is new to you they haven't published another list of top ten but it probably won't be too different so as I said before compliance sucks but non-compliance is so much worse than compliance let's take a look at that olas top 10 lists if you notice something interesting about it is that the same vulnerability was the number one for both 2010 and 2013 three years of research three years of security patching people were still following create a sequel injection this is what non-compliance means you don't comply with the bare minimum and of course Bobby tables approves of on compiling compliance and it's basically negligence by any other name so real quick this was a quote extracted from an article from a
magazine about that interview cios does anybody know who this is that said this line okay yes exactly so it was James Paul trow the executive director of information security for Sony back in 2007 and you give me the interview at this bitly link I provided here um so what happens when you say I will not invest this much you know resources to predictive projected to be minimal amount of damage that's what happens so when is good good enough well unfortunately to be sympathetic towards the Sony guy there is a tough cost-benefit trade-off you have to make you can't sit there and hire two thousand auditors and engineers to rebuild every little micro application if you're building like a two page app
on WordPress or a simple Android app you probably don't need that much investment but what I don't think his arguments captured is that not all dollars and hours are spent the same you can waste time and money on developers who don't know security you can waste time on these auditors who will literally just rubber-stamp anything you put in front of them because they get paid for you know X amount of money for approving a checklist so no so exploitation takes place at the application layer um system all vulnerability still do exist and they still do matter but most of what you see that actually gets into your network is going to be um like sequel
injection oh we hired an auditing company or we hired a development company that didn't know if they were doing somebody got lfi access into our system they dumped our hashes and they figured out a root password that's typically the most common way things go or the simpler route they literally sequel I into a reverse shell so if you want to make your company more secure if you want to make the world more secure it makes sense to focus on developing more secure software so how do we do that it's easier said than done a lot of people on Twitter a lot of specially cryptographers will tell you don't even try it's a lost cause I don't really
agree with that philosophy I believe there's three things we can do simple strategies that will make software better and more secure in general across the board so first things first we need to provide developers with a secure environment if you have a compromised system and you try to build safe software the people who compromise your system are going to be able to make it say whatever they want and unless you're diligent and paranoid you probably won't even notice and you'll just commit the changes in your next you know push to get teach developers about security this is what a lost focus is on um this is actually one of the most effective strategies for securing everything because people who
know something can share it with others education is actually the one security strategy that has the highest ROI because when you train somebody when you teach somebody they can go on and pass it on to somebody else who doesn't know and you actually make less people right crappy code and then the next thing you can do is provide tools that are secured by default so I don't know if anybody is familiar with me me or any of my research that I do as a hobby I go around on github and I'll you know bitbucket and I find application frameworks and published vulnerabilities in them slim cake PHP codeigniter really none of them have been safe so far
Symphony had a really weird one but it was really edge case so I don't to call that a vulnerability if you want you can come talk to me after the talk and I'll probably talk your ear off about it for hours so let's focus on the OWASP approach teaching developers about security as I said at leads to better at option of better security practices if your employer and you're considering hiring a developer or training an existing developer in security would you rather train somebody who leaves and goes on to your competitors or would you rather have somebody remain ignorant and remain with your company the more developers no security the more hands our debt are on deck to find a fix bugs
I mean that's kind of obvious there's a famous quote that everyone likes to make fun of with enough eyeballs all bugs are shallow and then you have something like the openssl bug last year heartbleed or any other subsequent ones apparently there aren't enough eyeballs on open source projects so challenges to teaching people security is that this curriculum expands every year new vulnerabilities are published and it's just a complicated topic and some of the old vulnerabilities re-emerge new year you know in new areas a friend of mine is actually publishing a paper and doing a talk in August about what's called a flush and reload attack it's basically a timing attack on your l3 cache on your processor and you can
use this to you know side channel cryptographic applications well he found out you can actually use this to also spy on other processes including like firefox or google chrome and unfortunately there's a limited pool of talented researchers who can actually mentor people and it kind of creates this whole situation where the people who can do security don't bother teaching the people who teach don't really know it that well um Tony Turner of us being one of the exceptions because he's actually you know really what knowledgeable on that as a result it got drives costs up and it reduces the amount of information that's shared this is what the old hacker underground feared from the security movement so
let's talk about complexity let's certain securities complex we can kind of abstract a lot of the details out of it um yeah there's different kinds of attacks and vulnerabilities but let's focus on the broad category is not the little granular details so we're going to think in terms of Kingdom not really species so kingdom would be like you know animal or I think that's animal vegetable mineral whatever so I've taken a lot of the vulnerabilities you'll find in actual real-world applications and split them up into three categories i think is a nice model for teaching people how to approach security who have never done it for the first time so the first one is application logic you know
what is your appt doing the segment one is the one that most people focus on is the separation between data and instructions and the third one is your operating environment okay these are application vulnerabilities there's obviously Network ones there's physical ones and operation environment kind of touches on all of those but let's talk about application logic I don't know how well you can read that I feel pretty clear so this is an all comic about people who try to use like venom miracle occurs in scientific papers this is kind of what people do in their online applications for example a shopping cart where you can skip the payment process and go directly to entering your shipping
information that's actually a vulnerability unless you actually take the time to look for that you probably won't find it just looking through the code for can I inject a comma here and or ' here and get code execution there easy for humans to find surprisingly it's a little bit harder for automated scanners because you're not just looking for patterns and code the impact varies it's kind of bias horse alone in this spectrum if somebody goes on your shopping cart and manages to order a hundred dollars worth of I don't know fancy slippers and you go hey wait a minute I never receive payment for that you can just cancel the order your application was vulnerable but you can
probably mitigate it very easily and careful planning can avoid most of the problems without with application logic so I mean I forgot to break that slide up so data is instruction this is kind of the thing you run into when you're doing security research the most buffer overflows and see programs for mashing vulnerabilities those are two of the most famous ones um but in web world we have sequel injection on cross-site scripting and the goal is usually to take over the target machine hmm so how do you stop you know so we go back a crook so a sequel injection what you do is you send a parameter to a query and because of the way you write
your data it will actually change the instructions following that bit of information so you actually manage to say um like in the Bobby tables example like 30 or 40 slides ago Bobby drop table students it deleted the students table most vulnerabilities that result in exploitation our form of data and instruction confusion I believe that's one of the fundamentals problems of security so if you're using buffers you know use functions safely distrust input don't do like heartbleed and say I'm going to give you 65 kilobytes of data if you give me if you're asking for one operating systems mitigate this with different attacks or different techniques you know writer right or and or executed right exclusive or executed
cetera for mastering vulnerabilities are almost extinct but just don't use them badly don't printf user variable that that's bad with sequel and this has actually been a recurring question on Stack Overflow used for amortized queries prepared statements you know behind your parameters whatever you want to call it you separate them in cinnamon separate packets it's you're not going to jump out of it unless you're using an old version of PHP that emulates prepared statements and doesn't actually send a packet separately cross-site scripting honestly it there aren't any really good solutions if your template engine escapes your parameters for you you should probably use that if you're going to use something like a manual escaping process you know make sure you
keep character encoding in mind that can really bite you if your PHP developer twig is wonderful they now auto escape by default unless you tell them not to so operating environment this covers a lot of ground um a lot of stuff and every detail matters and unfortunately there's it's so wide and not really that deep and related application security is I'm not going to get into into too much detail um you know is who hosts it who has access to it are you up to date is it well designed you know permissions issues how are you connecting all these issues or operating environment issues um if you use third-party components that's also an operating environment issue because
you didn't write that code someone else did and since you're depending on that that's part of your environment so let's take a look at how developers acquire third-party libraries so when I went back here let's go back to this one I focus on point2 for a reason because I think these two points 1 and 3 the secure environment and tools that are secured by default are kind of the same point in a specific way so lists mmm best way to illustrate this is through example how do PHP developers install composer does anybody know does anybody know where on leading with this already the instructions look kind of like this so what they're doing is they're taking
data pulling it off the internet with curl without doing anything else with it immediately executing it we have more examples on curl pipe shi tumblr com I don't maintain that by the way it should go without saying this is a bad idea don't type to your shell just don't there's two things can go wrong one if you're in point gets compromised and somebody puts a Trojan horse on there guess what your computer's owned you know GG play again um the other thing that can go wrong is if you're running a if you're running to come in like REM RF at it the l a-- folder whether it's absolute path and it cuts off I think
they're just more of a double you get specific one but still running untrusted et untrusted code you can actually get Tory will delete every file on your system that user has access to because it cuts off and still runs it so yeah it's just a bad idea all around don't pipe to your shell so let's talk about secure code delivery so most people when you download software I know if you try to download something like tor or tails they published a pgp signature----- of their software and that does help a lot but securecode delivery itself is actually a surprisingly non-trivial security problem there's actually three nuances to actually make something secure the first one is cryptographic signatures is
it signed by the person who is authorized to release it you know and this doesn't mean an md5 hash by the way this means something like our essay or fdsa something with asymmetric cryptography so that way you have a private key that only you can sign the key then you publish it and everyone's can verify it md5 hashes shot you hashes it doesn't matter if somebody can hack your server they can replace it with another hash but if you use something like PGP organ EPG you can actually you know download the public key in your trust store and then you're secure going future they're going into the future so long as you actually you know have the
key on your system it also makes it very difficult to forge a signature the next one is reproducible builds a lot of Debian projects are actually moving towards this mmm basically if you build it from the source you should get the same thing as they're providing with you you know providing you with sometimes you'll have things that differ like build timestamps you really can't help that but in general the fewest things that differ the easier it is to trust the code or trust the deliverable because you can look at the code and see what it does and then you can look at the deliverable and say okay it does the same thing and so this is the more
interesting one here user base consistency verification making sure that every user gets the same thing in a way that's mathematically provable um this actually isn't that trivial to solve so the reason this is considered part of the triangle securecode delivery is that if the NSA were to hack let's say get composer org and say if your IP address comes from Saudi Arabia we're going to give you a different payload they could do targeted attacks but if you have a way to verify that everybody has the same exact piece of code that they're getting you suddenly took that equation out you took that out of the equation and at that point good luck at hacking it if you have cryptographic
signatures your bill is reproducible your source is open that's kind of implied by recruit reproducible builds and you can verify everybody's getting the same package in order to attack anybody you have to attack everybody and retort order to attack everybody you have to announce your presence it becomes very hard to would do a stealth attack with that and if you have somebody who's doing a signing that has discipline that air gaps their machines properly and doesn't you know just i'm going to use PGP for win I don't see how you would actually be able to trivially get into a system like that so these three properties in mind can we build a system that offers secure code delivery
um spoiler I did so I'm introducing a project utility I built called Asgard it securely allows you to securely acquire an update your packages uses cryptographic signature is to verify the integrity uses the distributed ledger a blockchain for any Bitcoin enthusiasts to keep us honest and prevent target attacks and we verify the reproducibility of builds when we publish our published ifs and everything we actually insert our signatures in the blockchain and in case you're wondering about the capitalization of the name it actually stands for authentic software guard so it's going to be free um software it's licensed under both the canoe public license and the Berkeley system distribution license to Clause by the way um we use live sodium if anybody
has never heard of it it's a portable version of dan Bernstein's oz nacl library oh it does all of our low-level cryptography are at DSA our curve 250 why 19 um II seedhe and it's maintained by Frank Dennis it's modern cryptography it's actually tomorrow scripto the IETF is discussing taking of these primitives that are used in life sodium and making that the next version of transport layer security and another thing is that everybody anybody who had who uses Asgard to run their own that notary server so each block is signed with a well each leaf in a tree is signed by a private key that we maintain on each block is a miracle tree based on the
blake to be hash everything we publishes in the distributed ledger private packages are available if you have a company and you want a private package what will do is that will give you a license key which is actually a curve to 5519 key pair and will actually encrypt it with your public key and send it to use only you can decrypt it and publish it in the ledger so you get the same consistency verification but nobody knows the details your privacy software notaries must agree before anything is installed that's just a fail-safe so that we don't have people thrown in a bunch of civil attacks oh we have 51 person to the network we can attack it
and convince people that you know this is wrong um every notary has its own signing key using a head to 5519 its time box do you have 120 seconds otherwise the signature expires so replay attacks don't work and the key is pinned so when you add a notary it actually pins it to where no one else can use that or nobody can just substitute it like if you had you know like a ssl certificate when we add a package to Asgard we give it a detailed audit the first time through we look for any obvious vulnerabilities we look for anything that jumps out at us we go through with a fine-tooth comb essentially anything we find is of course we maintain to the
vulnerability or to the maintainer because we don't hoard zero days um both the initial ease and every update will be looked over by us before we sign off on anything if we think the originals pretty swell then the subsequent ones won't be looked at to carefully but if we see anything that's obviously okay somebody put a back door in here we're not going to prove it one of the things we're going to looking for is reproducible builds because as I mentioned if you can reproduce the software from the source code you can guarantee that you're getting the right thing if the build script is different we market is it produces a zero byte if we market it executable if there's
anything wrong even a time stamp by even a second we mark it as non reproducible and we also will make comments about it so I'm going to show you real quick Asgard in motion along
so can anybody see that let me see if I can increase the font size your book where's my mouse
well ok there's
we're small size
channel oh there we go sorry it's really hard to see if the single that better yeah cool so I'm just going to get composure so what assuming this it's actually synchronizing from Allah notary did I have set up hoping the internet doesn't kill this
maybe you did
so dr. Palmer oh there we go okay so
mmm so I probably shouldn't show you the director for hand but if you look at the timestamp it grabbed composer verified it did all the stuff in the background this is just it in motion it's really hard to show you right now what it actually does under the hood without creping through a sequel light database but that's the project in essence now let me see where it was in the slideshow
oh there we go alright so let's look at a comparison on how to attack these two co delivery methods with composure compromise gift composer org replace the installer with malware you're done with us you need to compromise our air gap machine that we sign our packages on steal our signing key publish a bogus package compromises our server to actually upload it I hope nobody notices it from the distributed ledger given the limited and short payoff that you're going to get we don't see a lot of people considering it worth attacking our system some will try and whilst okay that sounds very good we'll try to stop them best we can so Asgard is offered as a subscription service
we're going to make a lot of packages available for free any package we make available for free will never be revoked in that status composers one of those more information is available at get Asgard calm arco de zones will be on github i actually forgot to make it public last night i'll do that when i get home tonight if you want any questions you can check out our project website and if you give us a gpg key when you sign up will encrypt your welcome email with your license key so with that said that's all I got if anybody has any questions you Oh
dynamic slamming no less um so is it a waste of your time hard to say the attacks I'm talking about are mostly in the theoretical realm there's something you'd expect to the national security agent she'd be capable of or any of their you know other partners in mass internet exploitation if your threat models script kiddies that download you know backtrack or kalyan to their laptop you're probably fine I haven't actually had a lot of people exploit these kind of attacks there was a that was an exception there was a company called push the got hacked recently and they actually used their auto update mechanism to push out an hour I don't know if you guys heard the
story about that but that's the kind of attack that our software actually prevents because if you try to just a few hack our server and distribute bad packages it's not signed by us and that signature verification is going to fail and if any of the ledgers try to lie about it it just locks up and screams bloody murder until we identify and fix it so to answer your question I don't think you're wasting your time but there's probably things that can be done better so is that everything okay my contact informations up here the company behind asghar does Paragon initiative enterprises we do software consulting application development we do security um give us a shout out if you have any
questions my pgp fingerprints are right here my personal one and my business one um little bit more about me and enjoy the recipe sides





