Attacking .NET Web Services
Show transcript [en]
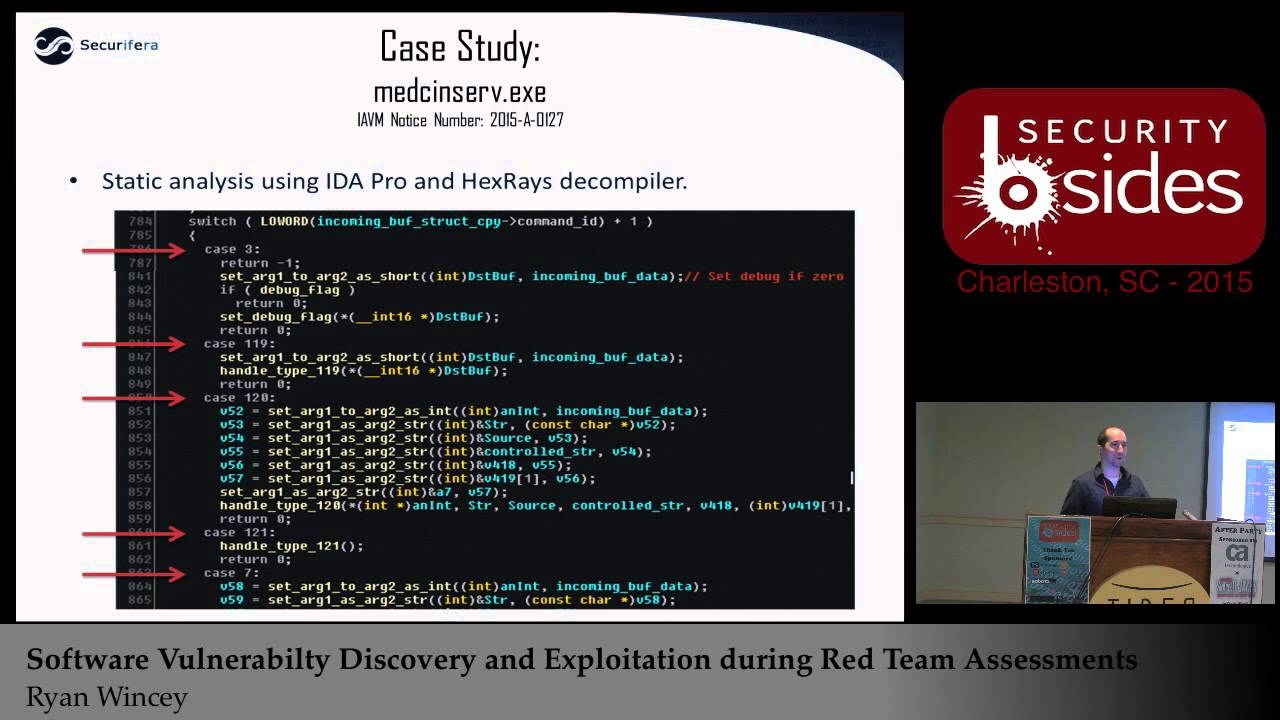
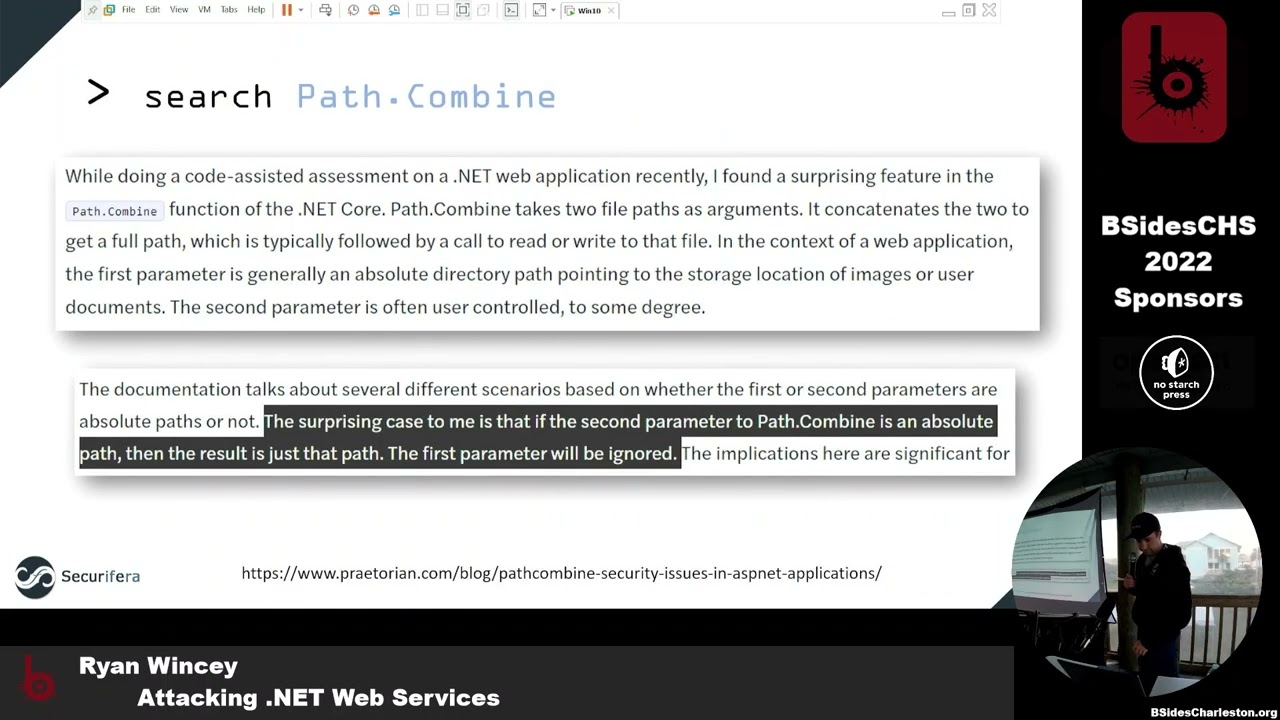
all right so can everybody hear me all right good so I'm gonna do a talk on uh attacking uh.net web services uh this is more of a talk kind of uh about my general process on how you know I kind of go through some of these things uh as she said I am Ryan winsey I work for Spira uh I do a lot of uh bug hunting uh where we do primarily red team work for the Navy um I have uh my history here some some advisories that I found some of the cves I've gotten when I've looked for certain types of bugs as well as a link here to the last talk I gave uh that's kind of similar to this uh here at besides in 2015. uh it was a similar kind of walkthrough but more for memory corruption type bugs uh where this one's going to be more uh web services kind of the newer type things that are out uh since memory corruption seems to be kind of going away in a certain regard thank you all right so kind of to go through what I I mentioned a second ago so this this talk is going to be um kind of more process related uh in regards to you know hey I had a Target that we got assigned to uh we're gonna be doing a kind of white box code review uh of the the software here um our customer kind of gave us a couple weeks they said hey we want you to find some vulnerabilities we want you to prove impact uh tell us why we care um so as we walk through this you know that's kind of the the goals here we're going to be looking for vulnerabilities uh interesting things um as well as kind of displaying some of the tools that we had to do or to use to do so um and then at the end of it I'm going to show okay based on some of these bugs it might have found uh here's some of the ways that you would exploit them uh to kind of show impact yeah a few of the tools that I've note that I'll go through here um moans mostly for reversing uh and debugging as well as kind of the exploit phase uh we got dnspy and Dot Peak uh they're gonna be primarily for the.net reversing as well as the debugging uh and then the last of course is burp Suite that's going to help us kind of walk through some of the the web exploits and sending those packets to make sure that uh we can actually see some effects foreign so our Target here uh this is a a piece of software that's put out by uh Siemens health and ears it's called Cinco Dynamics uh we had this on a customer Target uh it's used primarily for doing kind of cardiovascular Imaging but when you look behind the scenes it's really just kind of a thin wrapper around a whole bunch of net web services um so that's kind of the basis of this whole talk we're going to be using it as kind of our example on what you would look at if you uh were trying to do something similar all right all right so again kind of giving context here um you know if you were given this task one of the the primary things you're gonna have to do first is kind of get access to the software um so in our example you know we were kind of given um you know access to these systems that has the software installed um so one of the things we like to do is try to model this environment uh outside of the system so one of the things you would do in this scenario if you couldn't get access to the software is grab what you can off of that Target try to get it over to your environment uh try to model it yourself on a similar you know VM or something of the like make sure you try to get it configured and that sort of thing so some of the details you'll see later on here is kind of going through that process of here's what it would be like if you were able to actually get the software and how to try to get it up running yourself uh so you can go through and actually try to look for vulnerabilities and debug through it so one of the first things when you're looking at say you know a.net web application uh unlike you know a regular service binary application where it's super simple and you're like hey here's this application that's running I know where the code is um you start reversing it with web services it's not as clear-cut first you kind of have to find it so one of the easier places to kind of start that that path there where to look as you start looking in the configuration files for IIs one of the first places to look here is your inet server config as you can see here it's going to start telling you where on disk some of these things are installed to start prodding further that leads you to your web configs for the particular application so you see here in the bottom right when you start looking there it starts kind of giving you ideas of here's the particular classes Here's the the the different paths they're going to be mapped to to kind of give you a better idea of hey this is where I need to start looking these are the places I need to start investigating to see if I can track down where the code is for this web application so if you follow those through and you start looking on disk where you know the config files are pointing uh we take example one right here is called data transfer services you're gonna find a whole bunch of these files in a SVC um so sorry starting sound like web services um you open one up and you start seeing some definitions here that say simply and it has you know pretty generic names like okay data transfer services but it doesn't look like a particular file so you you're getting a little closer but you're still not kind of exactly you know what this file is or where it is but you're on the right track so in that config file and reference something called an assembly so if you look at what assemblies are in.net here's a quick kind of explanation for Microsoft tells you assemblies are typically you know an exe or a dll um it's going to be in your your.net application so you're in that directory that we saw earlier so you start poking around see if you can actually find any dlls or executables in that same directory structure so you'll see here I just brought up search in that same directory that had all the service files and just start looking for dlls and executables they're in that actual directory structure there and you'll see pretty quickly uh the name of that service that we looked for in the config file there's a dll that's named the same thing so there's a good chance this is exactly the file we're looking for so at this point you kind of want to crack that open you want to start looking at you know what's in this dll is this actually the the uh the code for the web service that I'm looking for and what's that going to look like so one of the first tools that we're going to show here is uh jetbrains dot Peak um dot Peak is you know something you can load a dll into with this uh you know.net and they will actually reverse that for you it'll show you all the code that you need and you can actually start looking at it uh one of the nice things about um jet brands that makes it a little bit different than some of his um other Alternatives is it also allows you to generate pdbs um this is something that will come in handy later when we start talking about debugging um could be useful something we might have to have uh going forward as I mentioned one of the main Alternatives a lot of other folks use is called the inspy it looks almost identical uh the developer I assume just kind of used jetbrains probably as a you know a template for what they wanted to look like this is open source um last similar functionality the big difference between this and jetbrains is this allows you actually do debugging which is going to be very useful when you get to the part where you actually want to run your code and see what you can do with it um but yeah otherwise you can see you know it's almost identical um in this particular example we're looking at our data transfer services uh that we were looking for earlier uh this is a class here um and one of the interesting things to note I have brought up here is there's something called contracts when it comes to these web services and if you're very familiar with coding in general and the idea of things like interfaces um a contract is kind of a similar idea where it says okay here's the functions that a service would actually expose think of it as the different things that you could call through your web service so this is going to be very important to us when we start trying to actually utilize our web service and the different you know entry points that we're going to start looking at when we start reverse engineering so again you know we got a handful here and at this point we're going to start kind of digging deeper and pick a couple out and start seeing how would you actually look at the code where do you go after you you have a contract or an interface uh to actually start doing something useful all right so we have uh dot P but D and spy does the same thing they have all the same functionality so if you were to click on one of your contracts here let's ride on over to get go to implementation foreign this particular example um you start seeing some useful things has has to do with files which is one of the key indications of things I like to look for uh when you're looking for web services uh some of your common vulnerabilities are like file uploads file rights those types of things so already this kind of jumps out to me as something that could be interesting to look into thank you uh this is the later part of that same function super small um as you can see here it opens up a file it actually reads it and then it just passes it straight back so this is already kind of sounding interesting this might be a possible you know local file read uh just straight from you know remote procedure call which is one of your your entry points into this web service so another thing I meant to point out here uh that also it was interesting that I wasn't super familiar with at the time so you start actually looking through some of this code uh the one of the things that looks interesting is that one of the arguments that you have here is this dysfunction our file name that we actually control is passed into this function called path combined it takes in you know what looks to be some kind of configuration path to the root and then our file name creates you know a combination of that through path combined and then it passes it on to actually be red so at first glance you probably think okay well that sounds normal right like you're going to have one argument that you don't control one that you do they're going to safely combine those together no big deal how's any kind of vulnerabilities here but we skip forward here and you actually look at this article that Pretoria put out a year or two ago uh they found a very interesting effect here which was passing behind actually will take both of those parameters and if you have one to say absolute path it will just ignore the other one so super interesting because now we always have the equivalent of a you know direct Universal or something similar where we can arbitrarily control the path um to whatever this argument that comes in so we got lucky here and that we have what we thought this is a local filing thing so pretty interesting right get all excited and you're like okay this could be interesting all right so if we skip back to our services here uh when we're looking for the code earlier you know usually once I get to this point where I'm like okay there could be an interesting finding I really want to see if this is real you know now you actually want to start constructing some kind of POC some kind of payload so you can actually confirm your findings right so how do we get to the point where I'm looking at code in this weird you know web services.net stuff how do I convert this on over so that I can start sending packets because at this point I have no clue how to put that together so all I see is service contracts I don't know what that is how that works so if we take a look at some of these you know naming uh you know terminologies or whatever think of it here as our WWE root and then of course into our directory here that in this example it's data transfer services um our WWE that's going to be just like regular website right starting there at root everything behind it to you know your url so if we're gonna just guess and say okay how could I get to one of these Services I'm probably just going to type in data transfer services and I'm going to pick one of these these SVC files to see if I can get there so here's an example we picked commonservices.scc within our data transfer services we're going to put it in our browser and just see what what comes up what's the service look like with.net so this is probably going to be your most common example of what that would look like it's going to say service it's gonna not tell you much else it's going to say your metadata is disabled and you're like okay well that doesn't tell me much how do I actually use any of these functions that we're looking at how do I send a packet to this I don't understand so the cool thing about this is it actually kind of tells you the answer says okay well if you actually want to enable metadata AKA get more information about what's going on here go into the config file you put in this new configuration point and it's going to start showing you more information so we're going to navigate over to that same directory we're in as our SVC so we're going to open up the web config we're going to turn on the metadata here and see it's highlighted we do it for both HTTP HPS it's enabled now we're going to see what happens all right so if we go back now we get this new thing okay so it's changed still not super interesting I don't know what a whizzle is I don't know how to get a request out of this but Something's Happened something's changed and hopefully you can start getting more information on our next step so if you click on that link it shows a wisdle you'll see here we have some kind of protocol specification kind of shows okay these are all the things that this particular service exposes and all the different ways that you can interact with it it's all on XML most of us can't read this I don't know what this means so I mean we want to figure out how can I convert this into something useful because I want to start creating web requests I want to actually send something to these endpoints I want to see if I can read a file luckily burp has a nice big plug in here called Whistler you download this through extender you can pass over any of these XML whistles and they'll actually parse it for us just like so and it'll start showing okay so we we go to that page it's gonna show it here in our history and then if we parcel it over to Wizard and say parse wisdle then it's going to bring up this other page under the extension it's going to show us all the different operations here that we can use and then very conveniently below it it actually gives us a template here a little example request on how to actually get to it so super nice you'll see here we have one highlighted here that download patch update now I have a really simple way of actually just going in here and I can pass this straight to repeater and I have an example for how to send this request foreign you're actually seeing the name of our function there uh it looks very similar kind of the contract that we were looking at earlier it takes this update ID it takes the file name and that's it so super straightforward it's got everything done for us so let's just go straight straight to it and actually just pass in a full path and see if what we want actually works so sure enough let's see over here on the right I passed the path to Nancy host on Windows and we actually get Etsy host super interesting this seems like a big deal all right so a lot of times at this point you know we've actually you know done something interesting but I also kind of want to get to the point where let's say it didn't work first time or we actually get to these other functions that we actually want to start digging into right or let's say I didn't know what that first argument was and if you know I needed something specific to it you know I actually want to figure that out so at this point I'm kind of going to dive into the next piece of let's say we actually needed to debug it right so it didn't work the first time I actually need to see in code why it broke and how to go further so we're actually going to start trying to figure out how to debug all right so now if we switch over to the inspy we've got jetbrains you know dot peak's big brother or little brother it's a brother whatever right you go they have a debug menu here uh inside it actually has the ability to attach to a process so if we bring that up you can see listed here any of the IAS processes uh that are running currently if you don't see one you can send a request and it'll pop up one of the interesting things to point out here at the bottom here it kind of gives you a little hint if you don't see anything after you sent that request it wants to remind you there is a chance that you could have architecture issues right so like if you have inside IIs you know this is a 32-bit application and you're running 64-bit D and spy you're not going to see anything and so you have to make sure that you know exactly what architecture your is running at so kind of give you a little help there if you ever end up there because I did in this particular uh scenario you can go to your application pools uh configuration for IAS you click through advanced settings here and you'll have this nice little figuration Point they'll tell you whether or not you want to enable 32-bit or not if you do you can click on that uh and kind of Define how that particular application is running and then run it with the appropriate architecture all right so now we've got debugger running and so you're like all right so I'm about to start seeing some you know ability to step through my code and uh unfortunately you see this error so typically when you have a debugger running and you put a break point in the far left there that'll turn into a little solid red dot if it doesn't and it gives you that little you know sign that says there's a problem you load over it basically it's telling you hey yeah I'd love to debug for you but I don't have any symbols so this is where we were talking about earlier the differences between the Inspire and uh dot Peak so luckily with DOT Peak you can then go and generate those those symbols it'll create a pdb and then you can actually take that file and you can drop it in to wherever your service is and then it'll have its symbols and you actually start debugging here's a slide that kind of uh goes through that process so open up dot Peak go to the top of your project here generate your pdb drop it in and you should be good to go all right so now we were to step through the exact same function as before and we're trying to debug through it you'll see here we're actually stopped here at our particular line where it's taking in our path combined it's taking in the parameter we control along with what should be the right directory and we can verify right now down here the line is following it it's going to check whether or not my file exists but we can see in our debugger it is actually our full path rather than the right one so this kind of gives us more granularity again so like if we really want to dig into something else being able to have the debugger handy on an application that's already running that we don't have source code for uh these tools make it very simple to make it seem like we do and we're actually the developer even though we're not for fun here I've kind of highlighted the little bud there for you know both of the examples here where it's taking a path combined and using that in a way it shouldn't all right so we've verified our bug we stepped through our bug what's kind of the next steps here