Malware, Cats and Cryptography - Zhassulan Zhussupov
Show transcript [en]
so hello cyber security Community everyone who interesting on uh cyber security entry level Specialists professionals students and everyone who came to this interesting conference so today I will talk about the role of cryptography in malware development and uh considering uh results of an unusual research I conducted during the last one year so little bit introduce me it's not me it's me yes uh so I'm a Mal analyst and thread Hunter and Mal researcher cyber security Enthusiast also contributing some projects like Mal pedia and sharing my knowledge during the years via my books so let's start today uh first of all I will talk about uh Mal protection a little bit introduce some techniques and tricks
which Mal authors used for protecting their applications then I will consider about Mal and how you can use uh cryptography for hiding malicious actions malicious payloads from uh Security Solutions and finally I just share my um last research about uh simulating ransomware and trying to decrypt some victims of ransomware uh like black cat ransomware Hello Kitty ransomware so uh cats are more than only uh not not only CS in cyber security and also ransomware today uh first of all okay defensive cryptography yes uh traditionally cryptography used for secur your information your data or privacy uh from unauthorized individuals and uh many of us used cryptography for uh protecting um uh communication also for encrypting uh for
example communication with between servers between uh infrastructure protecting and encrypting data and and other Solutions like uh pgp um mail and something else so uh defensive cryptography traditional is like balance between what's possible and uh what's acceptable because you cannot Crypt cannot encrypt everything everything cannot secure everything um but uh bad news is uh today nowadays uh cryptography also us it as offensive instrument uh not only red teeam operations not only festing also used for developing malware and using adversaries for protecting and hiding their payloads and assembly code okay uh m m uh M outs uh try to create full undetectable Mal uh antivirus Solutions easily to bypass and you can easily bypass uh Security Solutions EDR it's uh
some sentences when you can hear every day uh if you interested on M research and Antivirus researching so uh I also ask myself uh Hey really is it really too easy to bypass antiviruses and edrs or some other Security Solutions and uh I just uh concluded that um the classic tricks is divided to main these two three uh Concepts three main basic concepts to hiding your mother from uh uh Security Solutions in your red team operations spin testing or some another educational and research purpose of course only the first one is time Distortion tricks it's simple just uh trying to avade some uh virtual machines and boxes like using sleep a get count and trying to Distortion time
timing uh when you run uh your mother the second one is wi API application and hiding uh what's what does it mean it's application wi API functions and hashing using some CIS calls using hiding your uh calling V AP functions from import other table and the last one is of course encrypting and encoding payloads and assembly code uh so for example what does it mean uh when we say hashing API calls uh sometimes uh Mal good Mal analyst good security engineers and reverse Engineers can uh detect any malicious actions from uh by analyzing uh import address table of your M for example uh just in case in this example you can show that uh you can see that
message box is detected from from uh import address table of user 32 dll uh what the problem the problem is uh you uh security analyst also can found another actions and uh can detect malare capabilities from import address table for example if you found something like um Rec open KX uh you can uh uh you you know that your Mal uh have capability for working with reg Windows registry and try to manage registry try to create new case and another one is uh for example if you found something like vs2 32.dll and your import address table and found some functions like uh uh like sleep like uh virtual alloc for allocating uh locating memory for your
payloads uh it's yes it's a problem but uh what's the solution the solution is calling wi API by hashing when you uh use some hashing algorithm for example something simple or maybe something complex like B 64 or something like more more for example more more is also used for in real life M and real life runw like Cony like blackhe and finally just hiding this from import address table as you can see we cannot see uh user 32 D from address table in this case and of course just hiding function names also for you can't found message box from by hex dump or something like strings also uh what about pilot encryption in this case
um the main concept is the same uh the only difference you uh try to hide your payload your uh assembly code uh for example let's uh uh let's say we have something like this any any payot any msf Venom or another pilot maybe in in this case it's just message box pilot and just in case it's uh let's say it's malicious okay uh for protecting this from uh static analysis uh we can just encrypt it via something like XR or maybe rc4 or maybe Advanced encryption standard or any anything else uh which US it by U malare actors and malare outs and also these algorithms used uh in real life Mal nowadays like ransomware or also um
droppers and MERS and uh K loggers also uh what's the trick just dynamically decrypt it decrypted in just in case in this cases or uh I just show only the exr algorithm but in your case you can use any any of them so finally just run decrypted pilot as a result it's worked and uh in me in most cases uh this one is uh this trick is bypass many Security Solutions like uh Windows Defender kasperski uh of course uh in most case it's not bulletproof uh trick and bulletproof technique for by fully bypass security solution adrs for example if you have uh some theistic analysis or behavioral analysis or maybe uh other types of uh
deep analysis like sandboxes or manual analysis by good reverse engineer or good M analyst but in most case it easily bypass static analysis and uh signature based detections like uh ra rules Sigma rules and anything else so but uh of course there is a c about shenon entropy what's the Chanel entropy in in this case Chanel entropy is a quantity of the information included in data in information and mathematical Theory information Theory uh entropy is measure of the unpredictability of your data it's also sh entropy is name it after the famous mathematician Shannon clo uh of course note that that uh if you have height entropy Shanel entropy it's uh having a file with a height
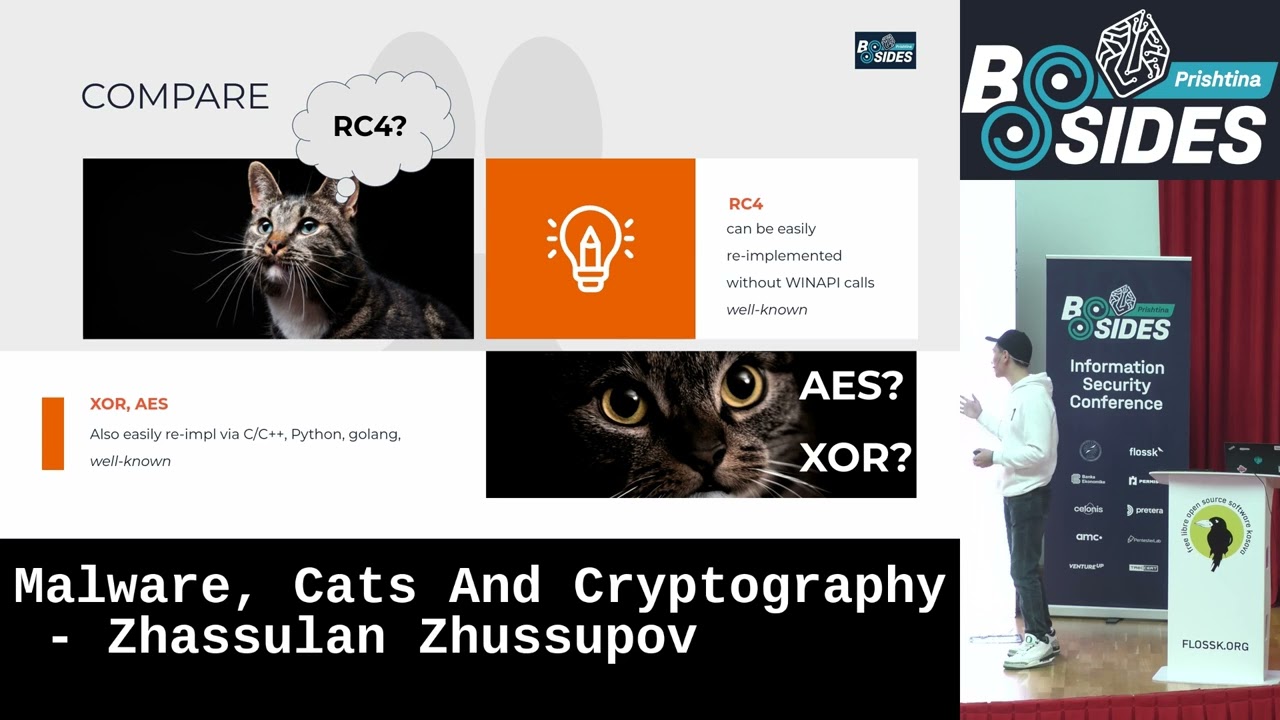
entropic score can cause Security Solutions to flag the file at least or at the very least consider it suspicious and uh Place additional screening of course uh sh entropy also the simplest uh formula is this one and uh you can easily create something simple in Python for example for just analysis and just for creating uh for doing some research for example in this case I just create a simple python script as you can see it's same as uh virus total uh SC wirus total calculating enthropy okay uh how is going uh what what about comparing um classic algorithms which I uh showed before for example rc4 or maybe XR uh first of all for example rc4 can
be easily detected and easily reimplemented and easily uh use it by without using win API calls for example you you not need to uh use Crypt encrypt API or something like big RI up API uh you know not need to call any suspicious V API so you not need to hide v i calls by uh via Aus skating it Aus skating your calls for function names you just need to hide your pad but the problem is this algorithm of course is easy and well known so nowadays it's easily detected by Security Solutions of course any antivirus or ADR easily detect this algorithm um but what about exr or a advaned encryption standard uh this algorithm also easily
implemented uh in C in C++ in Python and Goan uh many many open source libraries from GitHub you can use it for encrypting anything any data even payload even some malicious actions or your file but the problem is the same this algorithms well known and uh uh more complex Security Solutions and more complex and more um clever security analysts like reverse Engineers are easily detect these algorithms so I just ask myself okay uh well-known algorithms is not good for encrypting your pad today but what about uh classic algorithms it's which is not well known it's not famous like rc4 it's not famous like is or uh I just trying to get some encryption algorithms from
applied cryptography book by Bruce schne cryptograph um for example some algorithms like madri skipjack T encryption algorithm ex encryption algorithm and another algorithms from 17s and 19s uh but what is the main goal of This research uh how does this using this algorithms cryptography algorithms is the effect in shanon entropy it's increased or decreased and what about uh virus total score what about uh what about um shanon entropy and what about um virus total score okay the first one is uh to encryption algorithm this algorithm is uh block Cipher which use uh 64bit blocks for encryption uh algorithm and use 28 KS SI for encrypt so you need to divide your P lot uh to uh blocks uh for
encryption for using this encryption of course uh in this implementation you see by me I use just K size in 60 and round 32 rounds rounds for encrypt my payload as a result as you can see the shanon entropy is not so hyp uh what does it mean 6. uh 28 if your Shanel entropy is uh greater than seven it's detect as malicious as immediately by some Security Solutions like Windows Defender or something else uh but uh in this scenario and another scenarios also I use the most easy scenario just encrypt pad not using any anti-vm or anti- disassembling techniques or anti some anti reverse engineering techniques in in these cases so but uh even we have
a good virus total increasing uh uh decreasing score for example from 32 to to 84 it's not not bad for and uh it's that's concluded that uh T encryption algorithm is also used as starting point for your uh by for bypassing Security Solutions the next one is uh madri algorithm in 1984 uh which will was shared um and uh also used as advanced encryption standard in USA but uh after founding some issues and some back sec bux in this algorithm it's retired but uh why we cannot uh use it for encrypting or pelot in this case I just use uh 16 rounds and using this case just using this Delta of course uh you can you can ask it's
easily detected by Something Like aara rules or something another security solutions by just founding this data of course but even as you can see it's also good uh result for shenon entropy not so highight and virus total score also decreas it from 31 to 17 uh it's also good result and also you use as starting point for encrypting and uh adding uh another features like ant VM anti- disassembling anti reverse engineering tricks and features the next one is skipjack algorithm which will uh which was released by National Security Agency in USA it's also us it uh uh in the uh competition for uh using as advanced encryption standard and uh for standard encryption tool encryption algorithm in
USA but retired and uh many years ago it also not it's not um patent as open source or some open algorithm it's uh a closed uh algorithm but also retired and unclassified by National Security algorithm in 1998 as say know uh so also reverse engineered by pauletta and and I just reimplement it with some different some simple additions uh adding some uh modifications but basically it's a p uh modification optimize it by P implementation and of course as you can see in this case also good result for shanon entropy you can use it uh you can use it uh for uh as starting point for for encrypting your pad uh the next one is rc6 algorithm it's um it's one more C in
this case uh as you as you as you can see we use just p and Q prime numbers constants for this algorithm but uh if you try to use different constants and different rounds as you can see scalen and bit uh uh how many rounds you can use if you use more rounds more than 20 it's Chanel entropy uh highly increas it in this case and easily detected immediately but uh if you use uh this uh this implementation with these case uh these constants it's also can use for as uh starting point for encrypting your pilot and malicious activity uh the next one is the final one uh the interesting case in this here because this encryption it's not used
for protecting just data on U machines or technial it's just using for encrypting GSM it's a GSM standard or using uh encrypting your communication between base stations and your mobile phone so but we can why we cannot use it for encrypting our P lot of course in this case also uh as you can see I also use simplest case and simplest implementation with round case 0000 and channel entropy is not so high and it's good it's good for us uh if let's say we are try to uh security solution and virus total score is also good showing good result and decrease it and uh I just in this case I just try to uh Deep dive into
this algorithm and deep dive to protecting my Mal sample and as result by pass this algorithm also bypass uh kasperski antivirus and some Security Solutions like Windows Defender in real in the real case and uh it's really used in our pent test one of the our red team operations so uh in practice these algorithms also use it in real in real pentest and real red team oper operations but of course as I as I said before you need to not only encrypt it uh with algorithm you also use uh ANTM and different other different um protecting uh tricks like using timing time Distortion using upating V API strings and functions adding some tricks like uh try to evade virtual machine and
sand boxes what about full undetectable malas the main question is is it really to create ass say the previous slide uh yes you can you can do it by these algorithms any of this from during my research any of these four five uh classic algorithms uh the main the main reason I think uh using this it's they are not not so popular so uh for fall undetectably uh you need to use legit C2 uh INF structure like telegram API it's also I I have a practical case used with slack API and Discord API for stealing for communicating for sending commands of course everything will uh need to enry encrypt it and alcate it at least
base 64 or base 58 also for example uh of course you need to divide P lot it also a good trick uh because sometimes if you use standard reverse uh reverse reverse shell payloads from something like Ms venome from metas spit in your red team operations it's easily detect if you not divide it to blocks but it's also good for encryption because as I said before uh some algorithms for example ten encryption algorithm is a block algorithm block cfer so you need to divide your payload to blocks and then encrypt it of course and use NVM and anti debugging Tech like uh founding easy debugger present flag uh anti- Global flag um uh something like
uh is being the vaget flag also from parsing P files passing your M and uh also uh good uh good thing is hunting persistence mechanism of course because uh it's good if you was in my uh Workshop yesterday I just showing some tricks onti uh bypassing Security Solutions like encryption persistence and so on and uh what about uh okay let's for example let's see that a full undetectable malare in this case but what about ransomware okay we can encrypt payloads we can encrypt strings we can encrypt everything in Mal but what about ransomware can can we use uh these uh strange algorithms and classic uh encrypting for simulating ransomware attacks in Real uh but of course uh
during my research I also so trying to decrypt Black Cat and hello kitan wees and because these encryptions are little bit um uh use same tricks uh not using V API not using uh malicious suspicious strings also use same tricks as you as I said before so try to simulate uh different ransomwares and reimplement it from County Lake and copy kittens and black Trans okay encryption uh in case of Hello Kitty Hello Kitty use U encrypt algorithm it's just name of the library from GitHub they used this strange library with various encryption algorithms and encryption reimplementation and see in um assembly of course and uh this one is same little bit same modifications of advanced encryption
standard but as I said before Advanced encryption standard is well now so easily detected sometimes and they just little bit modification modificated for encrypting their victims and another case is black cat ransomware is is also used wellknown algorithm uh chaa 20 it's uh also us it by uh M actors and M authors in their malicious actions but it's also use same algorithm like as the only difference is they just replace V API it's it's the same like is encryption and like chaa hting uh hashing and um you also use more more hash more more hash to a modification uh and uh when you replace V API functions uh it's uh uh really decrease your detection score really DET
really decrease your entropy sometimes and really when I try to research these cases in my in during my career the next one of course um what about Effectiveness and problems when we try to prevent this preventing and hacking ransomware algorithms it's not so easily easy think and ransomware threats using different uh another different tricks like uh Deep dive into anti- debugging and some anti- reverse engineering tricks uh so I try to help victims and decrypt F files is it really easy or not uh and there has been minimal research unfortunately um in the GitHub in academic research I just uh try to hunt new research about uh how we can use uh some uh results from academic
uh professors and mathematicians and cryptographers uh how we can uh try to decrypt file but unfortunately so there has been minimal research in in the world in this case for these cases okay I just uh during new research okay what is the methodology of the research it's a simple just using virtual machines like Windows 11 or 10 or Windows 7 uh maybe I just uh using Linux in my future uh my future research during these uh interesting cases uh of course that me this uh V virtual machine with different files just in case something like doix Excel Microsoft uh PDF files zip files MP4 CSV files full them full them this virtual machines and try to encrypt it by
ransomware uh of course disable just in case for research purpose of course disable any Security Solutions like edrs and of course use legitimate C2 like telegram IPI as as I said before and compare and finally compare it with no more Ransom uh site I try to decrypt decrypt some files from these cases what's the results results everything is very bad but very bad but there is a trick I just show later uh of course the first issue is the heart not decryption because it's pointless and labor intensive because sometimes if you use all superc computers of around the world for decrypting some algorithms it's not not good idea course because you you need to 1 million years for this um of
course better results in best result is in best scenario is also less than 50% maybe less than 30% it's so bad and of course uh we need to do a lot of work uh we will need to research any new cases and more complex algorithms of course need to be tested as this methodology maybe you need to another methodologies uh like um combining some sandboxing and manual decrypting and some reverse engineering and trying to using some forensic tools like volatility and and so on uh as I said uh there is a trick uh what's the main idea of this trick let's say we try to decrypt yes no it's bad idea so we try to find the vulnerability in the
ransomware what does it mean I just uh want to say instead of decrypting uh to hard mathematical DEC algorithms and try to decrypting some in some case is so impossible with your resources so try to find vulnerability in ransomware architecture and because ransomware is also application as any application is wrot by people and wrot by stupid hackers sometimes so try to find this and uh in this case we are doing research in with my R&D uh in the web SEC company so I think uh we try to more complex algorithms and uh in some cases we will find some uh vulnerabilities in Ransom Wares and after finished our research we it will be public paper I
think I I hope it will be help for decrypting any uh Ransom Wares in the future so thank you it's the finish and if you have any questions you are
welcome thank
you thank you Jan uh okay I think we have a question there let me just pass the mic there
so I was just interested um how important or like how much would one you specifically suggest uh honing one's mathematical skills and reading on actual theory on cryptography and and and and and I know encryption uh to to like being a good like a ethical hacker or there is there some sort of work around that you don't need to know this whole bulk of theory and you simply get to use the tools that some other people have written what is like the the middle line between this do you do do have you for example had to read on on Theory before or or have you gone gotten around it just just sharing your knowledge just
sharing your any research by uh doing some good things you know uh traditionally M analysts use only reverse engineering and not try to reimplement some tricks as really hacker because sometimes it's really helping when you let's say you are blue team for example in my case I I'm not I'm not offensive security specialist I uh I just mathematician and uh traditionally I try to use uh reverse engineering skills my reverse engineering skills to beating Ms and combating mods but uh in my case I also have some soft engineering uh experience more than 10 years so it's helping for re Implement some things interesting things and try to to analyze it try to research it so I I hope it
will be helpful for any who need to analyze smaller and try to decrypt Ransom Wares maybe thanks thank you any other question no ran thanks so much that was very insightful presentation h





