“If Only They Would Take Us Seriously” : Christina Lekati
Show transcript [en]
hello everyone and welcome i'm very happy to be here again at another german besides event and this time talking about the behavioral science influencing your cybersecurity culture but before we delve into the science let's start with the story the story was described in the book how to win friends and influence people by dale carnegie it is the story of mr johnston a security and safety manager who was working for a big manufacturing company of the time so one of his responsibilities was to check out the employees and make sure that they are wearing their safety helmets however the employees didn't want to and they weren't really wearing them strategy was to walk down the manufacturing floor every so often
see the who is not working their helmet go to them tell them to wear the helmet point out the regulation cite the policy and basically not leave until they put their helmets back on and then go to someone else you could do that two or three times per day but of course once he was leaving the floor the manufacturing floor the employees were just taking their helmets back off and mr johnson knew that he knew that and he kind of hated it then and it was a main reason of frustration in his working life he would go back to his office and as you can imagine he would think why are they just not wearing the helmet i didn't ask them
to solve advanced algebra i didn't ask them to build a spaceship all i ask them to do is to wear the safety helmet and they just won't do it what is wrong with them and the months were passing by his frustration was growing but at some point his way of thinking started to change he thought okay they are just not doing it what can i do different how can i approach them differently and as he was building his thoughts he eventually he decided to go back at the manufacturing floor and talk with them and ask them why they are not wearing the helmets and what is wrong with the whole process are they uncomfortable are they too tight are they too hard on
the head do they sweat too much what's wrong and he would get feedback that was actually very valuable later on and that he would apply but in addition to asking why they are not wearing the helmets and what he can do to improve this process for them he also started discussing with them and educating them a little bit on the whole topic of safety helmets and basically telling them that there isn't this policy is there it's for their own safety and it is for their own security and it is so that they can stay healthy and avoid trouble once they hit their door if an accident happens they need to stay alive and they need to
stay well and with the conversation and the relationship building that happened through it employees started seeing the topic a little bit differently they started connecting with mr johnson they started understanding comfortable the helmets became more comfortable they started wearing them more often but in addition with increased compliance because they did start complying a lot more with the safety measures the resentment towards anything that was related to security also decreased significantly and this way eventually mr johnstone and the employees started collaborating a little better on the whole security issue in fact a lot better and we have a lot to learn from this story but before we do so let me introduce myself and tell you who am i
to talk about these things my name is cristina licati i am a psychologist and a social engineer i am a trainer and consultant for cyberesque in behalf on the human element of security most of the time i deliver social engineering and security awareness trainings to all levels of employees as well as security teams or i conduct corporate or high value target vulnerability assessments based on open source intelligence as of this year i'm also very happy to announce that i'm a board member of the awesome curious project which is always a lot of fun and i'm really thankful for now let's start a little bit with a whole topic of cyber security and why humans play such a big role in it
especially in the in recent years so yes cyber security used to be by definition a very technical discipline it was all about securing the integrity of devices networks and data from unauthorized access or damage but as a threat actor started started evolving as we all know by now they started targeting humans and cyber security started including an element of information security or a big element of information security now information security involves the protection of sensitive data and information from unauthorized access this means in any form in print in electronic format but also in the spoken word so if employees go about and discuss a sensitive matters or confidential information this is again a matter of information
security and they should know not to do it basically cyber security today is not only a technical challenge but it is also a behavioral one and why that's because as long as managers and employees can provide access to systems and high value information they also become targets and they may intentionally inside their threads or unintentionally cause security incidents or breaches basically cyber security today is a shared responsibility and it depends on all employees of an organization too don't take my word for it again but take a look at the data breach investigations reports and this one is the one from verizon so verizon measured the regularity of cyber incidents and breaches of last year as of every year but last year he found
they found out once again that 22 ended in 22 percent of breaches the tactics that were utilizing involved social attacks which means attacks to humans the human perimeter that we were talking about and not only 22 involved social attacks but 30 of the breaches that happened last year involved internal actors this includes either social engineering attacks or internal doctors that acted willfully which means they were inside their threats but in any case a good percentage involves employees and it will keep involving employees because right now it is one of the weakest points that we need to work better with and develop but we talked a lot about this security culture and i'm sure you have heard the
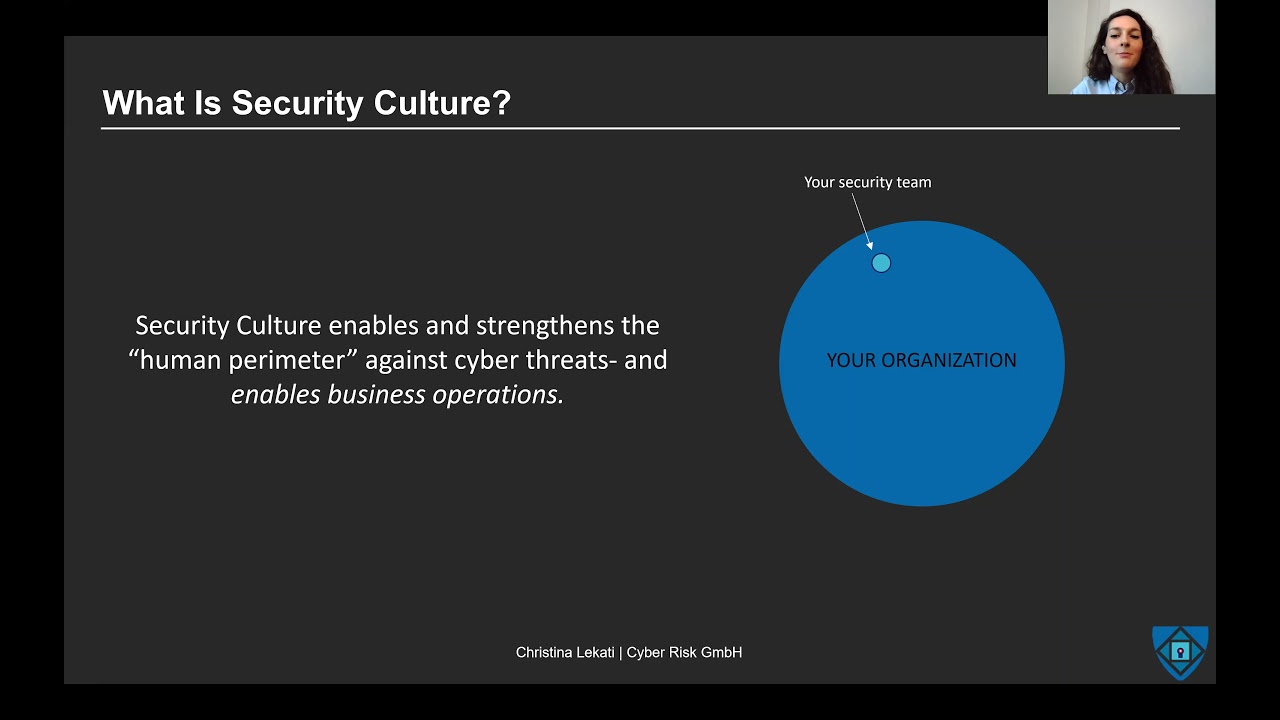
term as well but what is security culture after all by definition it is the ideas customs and social behavior of a particular people or society in our case the employees of an organization that allow them to be free from danger or threats and in effect protect their organization as well in other words it is the way things are done around here you enter an environment and you can pretty quickly tell how things are done around there and let's be honest between us you start following the norms of your environment we all do that so it plays a huge role and it is very very very significant however as good as it is it comes with a
challenge with a few challenges yes security culture enables and strengthens the human perimeter against cyber threats and it does enable business operations it does keep the organization more secure but on the other hand your organization is like this big black circle that you see on your screens and you and your security team are only a small part of it you're the small dot in this bigger circle in this bigger interaction of departments so suddenly we have one department our security department having to influence all the other departments and the way they interrelate with one another and it is a big task however it is doable as long as you adjust a few a few elements in the approach like mr
johnson did and it is necessary what are the challenges one of the main challenges is the employee competing priorities we will talk about it a little bit later in more detail but basically it means what are the norms of the organization in terms of priorities is it security or is it productivity for example what would come first if they if somebody had to choose between the two second it's i'm sorry to say the inappropriate security awareness trainings that create desensitization that create the mentality of it will never happen to us this is not relevant it's not going to happen here this type of mentality or very well so much that simply create security fatigue this usually happens when uh trainings
that when information security awareness trainings are very generic they feel like they do not apply to their realities and their lives and the corporate culture of that specific organization and therefore people just look at a series of um some of them are random some relevant videos about securities do's and don'ts and in the end they just decide to dismiss it all because it doesn't feel like it relates to them or they just get too tired or they get the third bullet point the mentality of inevitability they come in contact with so many different threats that they think it's inevitable i cannot do anything about it even if i try and put all this effort into
learning how to apply best practices there are just so many things that can happen that i have just play a very small role in it and i better look at how i can do my work faster and better than i start bothering with security at all and of course last is the whole factor around cov819 this pandemic that influenced the the cyber security culture and mainly the whole organizational culture because you simply just cannot do too much if you do not come in contact with people anymore if you do not see them if you don't talk to them and yeah and you have to stay stuck with zoom meetings but we really hope that this situation will change soon and we
will be able to again have organizations that intentionally are able to build their cultures in a better and more effective way now we have the challenges but we also have some support from behavioral science in terms of how to change the behaviors of people and here comes the theory of planned behavior that basically says that the behavioral behavioral decision making is based on how beneficial a certain action would be to me so really we all think okay if i do this what's my benefit what am i getting out of it if i put the effort what do i win out of putting this effort so if we think that something is positive and beneficial to us we are
more likely to do it and even more so if you think that our if we think that our significant others and especially our peer group our co-workers our teams and leaders are also in favor of us performing this behavior they will support it they will like it and it will be viewed in a positive way so as long as we have these two factors together our intention to do something or in other words our motivation will also be higher and the likelihood of performing this behavior will increase as well so very well a theory of planned behavior but there is another factor the person needs to feel capable of performing this behavior the role of self-efficacy okay i want to
do it i i want to be viewed in a positive light by others by doing it but can i or is it too complicated am i able to perform this action and follow the steps or not really is it too complicated too hard too many obstacles i don't know too little training so other behavioral models agree for example folks very well known behavior model which states that if the motivation is high it's good but it's not enough because people also need to have the ability to perform the desired behavior and then of course the triggers leading to it which are in our case us and the security professionals so three factors so far let's see what
we have okay we have the factor of uh viewing something in a positive life when right we understand that it is good for us to perform an action good we have social proof we have others agreement in doing so and the others doing that action as well we have the ability to do it perfect and all these things lead to the intention to comply perfect all these things are there but there is again something missing which is actually very important and in my opinion it comes first does this action conflict with other organizational values yes i want to apply more cyber security measures i want to take time to learn and be better but does it conflict
with other things basically what happens here is that we all before we do something we do a small cost benefit analysis we assess the cost of the behavior the risks but also the rewards of it so we know that complying with cybersecurity consumes certain resources especially in the beginning when it's not an automated action it will take time it will take some effort and it will temporarily possibly hinder productivity employees fear that the consequences of not being productive enough are higher and worse than the consequences of causing or being part of the reason why a cyber security incident happened and unfortunately it is this way they most of them do not view cyber security as a likely event or
if something that will happen and um yeah and they just prefer to stay productive because it is just having less consequences less severe consequences for them this is the whole point of competing priorities if the organizational leadership prioritizes productivity over security then you will have a very hard time because non-compliance will be frowned upon if you don't apply security behaviors yeah okay it's bad but if you reduce productivity could have worse consequences for example losing a bonus decreased bonuses or even unemployment and that's pretty bad in comparison of course on top of it comes the whole issue of inadequate awareness training the one that makes you believe that i cannot do anything against cyber security my role is not big enough
we have technology and that's all we need and the whole it will never happen to us mentality yeah they all play a role into skewing the the way towards choosing productivity over security and really in our heads there is always when we make these decisions should they take a little bit more time to apply proper best practices um in our heads there is this little voice that says how bad would it be if i skip a couple of best practices for the sake of convenience and speed how bad could it be could it be bad as a stop eating a cookie yeah i know it's not the best but nothing serious happens out of it
or is it really bad like smoking 15 packets of cigarettes every day for years and if they think that not complying with cyber security this is okay it's a little bad but necessary in order to yeah to serve this other priority and if they do decide to just keep a couple of good practices when it comes to security for the sake of efficiency and it works once they will think it can work again because this is how reinforcement works like so they will do it again and again and they will look that nothing terrible happens out of it and it will they will do it again and again until a very costly incident occurs and this is the dynamic of cyber
security incidences you have to keep your eyes open and be careful all the time but the incident will happen once every so often so if you just decide to skip on it and say that nothing but comes out of it without thinking that at some point it will and then yeah sure people will be tempted to skip a couple of best practices there many people know about this competing priority strike it was introduced uh through project management and basically it was saying you have these three elements that are all very important but you can only choose two and the same happens with security the the triangle that applies to project management is on the left
the one that applies security the adapted one is in the middle so what this means is practically that if you want more speed and productivity you probably have to sacrifice a little bit of security on the other hand if you want a more productive more security you potentially need to sacrifice some time potentially need to delay uh delivering some files until you find yourself in a more secure network if you're traveling etc etc you can only pick two and this is why it is very important within an organization to be very clear about what is a priority and to be very clear about communicating what is a priority and of course my organizational leadership and buying from the leadership
definitely comes in with it because it's not just you as a security professional that needs to push this agenda but especially the leadership needs to be able to push this agenda and evaluate based on it we will get into it so to end the challenges what does drive non-compliant behavior everything the circumstances surrounding security behavior impacts the security compliance and the culture basically three main reasons there is no clear reason why you should comply the cost of compliance is too high and there is an inability to comply maintainability comes in in place when there is an excessive workload and people cannot think clearly or they do not have the time to think about it when the complexity of security
mechanism is just very high which comes back to the inability to comply and when there is a productivity interference the whole competing priorities issue or other priority that your organization might have all these things will conflict with the agenda that we are trying to push of being more security aware and applying better habits but what can we do in the end to develop the cybersecurity culture so by definition to change the behavior and really by the way we are all wired to change the behavior you first have to change the attitudes thoughts and feelings associated with it why because first it needs to be in our heads it needs to be a thought it needs
to be an intention it needs to be a positive feeling and then it will translate into an action as they say it starts from the head until it moves all the way down to the hands starts from a thought before it translates into an action and all of our decisions in life work like this by the way how do we do that first of all by implementing not just convenient cyber security training but excellent cyber security training and what does that mean no generic and technically focused security awareness trainings that are full of lists of do's and don'ts but relatable relevant and enjoyable and interesting and personal cyber security trainings people don't want to see just a set of
videos that have some relevance to them but maybe not they want to see training they want it's much more effective and they enjoy it more training that is relevant to their reality to how their organization works with their industry and this is why it is so important to invest at least a little bit in a tailored cyber security awareness program one that can bring example from from examples from the industry and from the reality second utilize the psychology of groups use the principle of social influence to your advantage people tend to model the behavior of other people belonging to their group it is one of our basic try by instincts like we said before the thing
the way things are done around here is a really important factor but for that you will need leadership buying like we said before because again like children look up to their parents and then pick up behaviors and copy them this is an instinct that we carry throughout our whole lives and we basically even when we are in an organization look at the leadership to see what they do and we will do not what they say but what they do as well or at least we will tend to want to do that more so leadership buying and starting from the top implementing different priorities and the most important of them all or at least the really
really important one is improved communication the reality today is that caesars and security teams often struggle to relate to other stakeholders and they rely on a one-way communication they enter meetings and they say this is what needs to be done i i am the one responsible for this domain the domain of security and i know that this needs to be done and obviously it is a complex topic and you cannot explain everything and the wise you can explain it to a degree but usually the approach is a one-way communication to abc and this is why scissors often don't feel understood by the organizational leaders but also organizational leaders on the other hand don't feel like scissors and security
teams understand their business goals and that they offer solutions that are in collaboration with those business goals and in alignment with them and generally buying from other executives and team leaders better communication collaboration and trust needs to be in place and for that you need to speak in terms of the business goals and the calls of other departments what does that mean adjust the communication the way you communicate to others to the priorities and needs of other departments for example you have to speak with a marketing department and security teams often have a huge conflict with the marketing department tell them that by promoting cyber security you are actually helping build trust and brand loyalty and you add to the reputation of
the organization speak to them in those terms again if you have to speak with business leaders uh speak about cyber security in terms of an enabler in terms of enabling more business security initiatives are beneficial for the organization they are not just a necessary evil but they also will help you in the long road um open up into new new horizons make sure that everyone understands that their individual security responsibilities are theirs as well they have to know and they have to follow them because of all the um yeah because of all the ways that this will help the organization at large and their own work as well and make sure to be visible and approachable for example i know of
some managers that very regularly i roam around the offices and speak with the employees and ask them about some security initiatives and they also yeah and they say what they can do better they get feedback do they follow every opinion they hear no but they are able to have some quality time to discuss and push this agenda forward and they definitely do this with the leaders and the managers as well but it is always a two-way street you have to listen you have to accept them you have to adjust your message to other people's priorities as well it's just the way it is now there are three caveats behavior change takes time it has its benefits however it will take
time but the workforce will develop into an active human firewall and it will accumulate such a good set of cybersecurity habits that at some point they will they will not need much thinking to perform better habits but they will have become just automated actions and reactions so also if they see a perceived threat they will just immediately know how to react because they would have practiced and learned enough or heard it enough times from you it's pretty much like driving and following the rules the driving rules and the signs of the road in the beginning you kind of have to look at them and think what does that mean but eventually it just becomes an
automated habit and you do not need to waste any brain power on it second behavior change will happen if the secure behavior is achievable within everyday activities it is what we said about making it the whole thing creating the ability within the employees making the whole thing easy to apply and realistically and third the cybersecurity team needs to have better soft skills and trust and yeah develop some trust within the other departments and between the individual people so you need to talk with them you need to listen and communication skills are an amazing enabler for your job and you will see how it could change your whole working life in fact and before i close this presentation i
have two recommendations that i highly highly highly urge you to go through the first one is they are both books the first one is the psychology of information security and that discusses exactly the whole topic of creating policies and applying them in a way that acts as a business enabler and also communicating them in a very good way and many more topics please take a look at it you will love it and the second one is transformational security awareness by perry carpenter uh it focuses on what neuroscientists storytellers and marketers teach us about driving secure behaviors and it has to do with communication and how you promote the whole message of cyber security so that you can in the end build your cyber
security culture time is never enough i hope you have questions and i hope that you ask them please reach out to me and please contact me on linkedin or twitter i will be very happy to discuss with you and i was really really happy to be with you today and hopefully we will meet in person next year thank you all very much for being here and see you soon bye